AWS Storage Blog
Audit your backup RPOs with AWS Backup Audit Manager
When designing a backup and recovery strategy, one important factor is aligning your application’s recovery point objectives (RPO) with your business continuity goals. The ability to continuously detect drifts in your RPOs, due to backup plan misconfigurations or job failures, and identifying non-compliant resources is a critical need for customers.
In August 2021, AWS Backup announced AWS Backup Audit Manager, which helps you monitor and evaluate the compliance status of your backups to meet business and regulatory requirements, and enables you to generate reports that help demonstrate compliance to auditors and regulators.
We are excited to announce a new control in AWS Backup Audit Manager – Last recovery point control created, that allows customers to identify and report the latest available backup recovery point to verify compliance with organizational recovery point objective (RPO) requirements. This new control extends the visibility, ongoing compliance monitoring and reporting that AWS Backup Audit Manager provides to allow you to easily validate compliance across multiple resources.
Walkthrough
Let’s review the new control in more detail. If you are already using AWS Backup Audit Manager and are using either the recommended AWS Backup Audit Manager framework or a custom one, this new control will not be enabled automatically. To enable it, select your framework under the Frameworks section of Backup Audit Manager section. Then, select Edit. The following diagram shows these details.
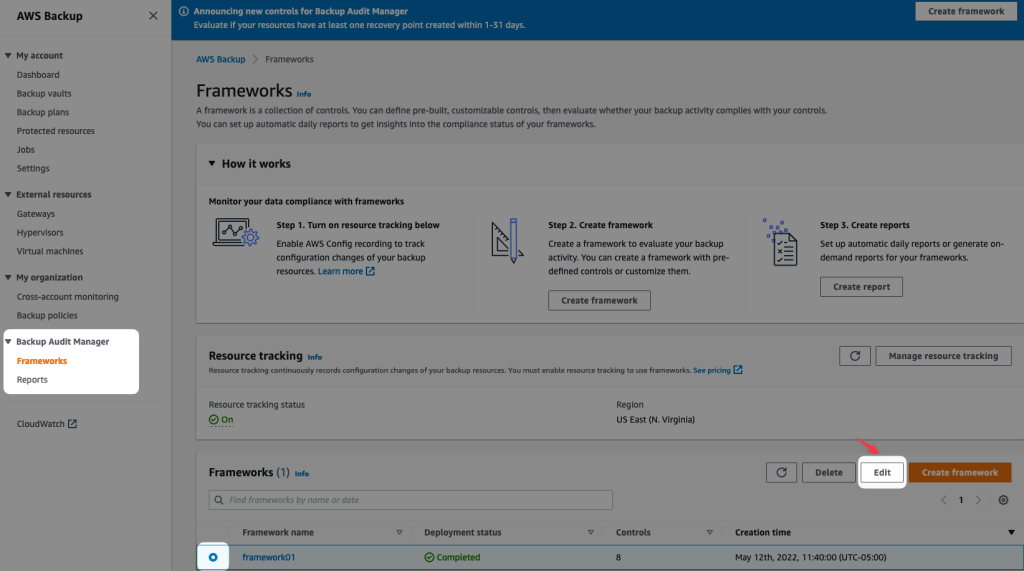
Figure 1: AWS Backup Console – Backup Audit Manager Frameworks
Scroll down to see the new control:
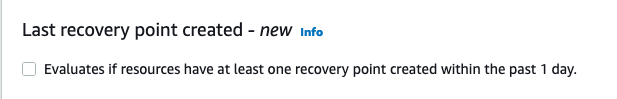
After the control is active, configuration options are set, which include, defining the period we want our framework to check to make sure we have an available recovery point within the specified timeframe. For hours, select a value between 1 to 744 hours. For days, select a value between from 1 to 31 days. Once the frequency is selected, we need to determine if we want to evaluate all or some resources.
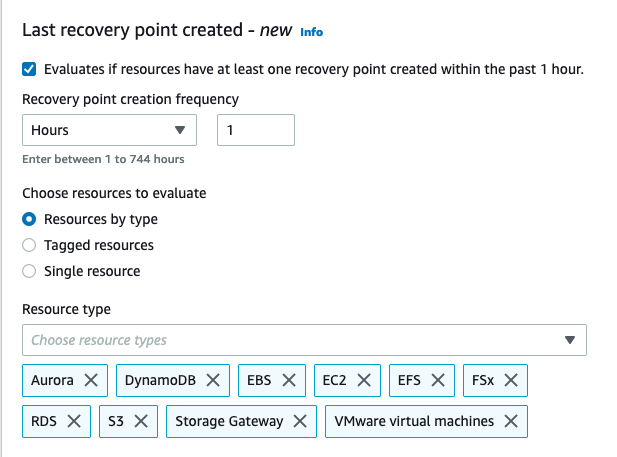
Figure 2: Last Recovery Point Control configuration options
Once you define the settings based on your requirements, select Save changes. After that, your existing framework will be re-deployed and re-evaluated with the new control in place. Afterward, this framework will re-run every 24 hours.
Depending on the number of resources in your account, this process could take from a few minutes to a couple hours. On my side, I have configured the new control to check if I am compliant across all supported resources with a 1-hour backup frequency.
It seems I have some homework to do, because only I see one compliant resource (Amazon EFS)! According to the control, my other resources aren’t in compliance. Therefore, I know I can’t meet my RPO objectives across all my resources, which is shown in the following diagram.
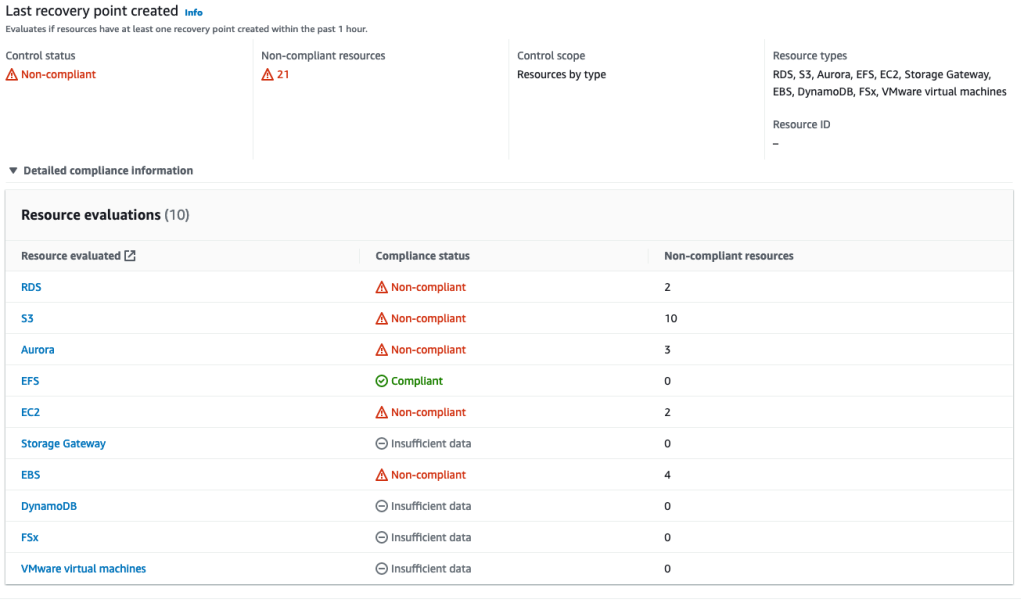
Figure 3: AWS Backup Audit Manager Resource Evaluations
Let’s click on Amazon EBS to find out which volumes are not compliant. This takes me to the AWS Config dashboard where I can see all the non-compliant Amazon EBS volumes, as well as the evaluation parameters.

Figure 4: Resources in scope
Lastly, the information of this new control will be included in the next compliance reports that are created by AWS Backup Audit Manager. Here is an example of how it looks on my end:

Figure 5: AWS Backup Audit Manager Compliance Report Example
Cleaning up
If you created and scheduled an AWS Backup Audit Manager framework for testing purposes to assess your environment, please remember to delete the framework to avoid incurring future charges.
Conclusion
In this blog post we’ve shown you how to apply the RPO controls in AWS Backup Audit Manager so you can meet your RPO requirements across multiple protected resources. We hope you’ve enjoyed this brief walkthrough of the newest control available in AWS Backup Audit Manager.
For more information about AWS Backup Audit Manager, refer to this section on audit backups and creation of reports in the AWS Backup Developer Guide. To get started, visit the AWS Backup console.
Thanks for reading this blog post! If you have any questions or feedback about this post, leave a comment in the comments section.