AWS Cloud Operations Blog
Improve your security posture with AWS Control Tower and AWS Security Hub integration
We are excited to announce the general availability (GA) of the integration between AWS Control Tower and AWS Security Hub. With this GA release, AWS Control Tower can detect control operations performed on the Security Hub detective controls from the Security Hub service. This includes the ability to detect if Security Hub controls enabled via AWS Control Tower are disabled directly from Security Hub. When AWS Control Tower detects a control that has been disabled in Security Hub, the deployment state of each impacted control will show as ‘Drifted’. Previously, you had to navigate to the individual AWS Control Tower managed accounts’ Security Hub service to check the state of these controls. This created an extra step and a risk of an unintentional disabling of the control. With the introduction of this drift detection capability, you can now monitor the deployment state of your controls. You can then take appropriate actions to manage the security posture of your AWS Control Tower environment from within the AWS Control Tower service.
AWS Control Tower controls, including Security Hub owned controls, are mapped to related control objectives in the AWS Control Tower controls library. This provides you with a view of the controls required to meet a specific control objective. For example, the control objective Enforce least privilege is currently mapped to 63 controls, out of which 30 are Security Hub owned controls. For more information on AWS Control Tower control objectives, you can review the list of control objectives. Combining over 170 detective controls from Security Hub with AWS Control Tower’s multi-account environments automation, you now have a baseline for governance as you scale.
In this post, we will set up the integration between AWS Control Tower and Security Hub to demonstrate drift detection. This will include enabling Security Hub detective controls from AWS Control Tower. You will then be able to view the compliance status of the controls for all findings in Security Hub.
Overview of the integration
To integrate Security Hub with AWS Control Tower, you begin by enabling a Security Hub owned detective control in AWS Control Tower. When you first enable the controls in an organizational unit (OU) managed by AWS Control Tower, a new Security Hub Service-Managed Standard is created. This is applied in all the accounts governed by this OU. Subsequently, any Security Hub owned controls that you enable from AWS Control Tower in this OU, will be managed in this standard. Thereafter, AWS recommends that you enable or disable these controls from AWS Control Tower. If you disable a control in this standard directly from Security Hub, AWS Control Tower will detect this and set it as a ‘Drifted’ state. To remediate detected drift, you must either re-register the OU with AWS Control Tower, or disable and enable the control from the OU.
Integration Flow
The following Figure 1 shows the integration workflow between AWS Control Tower and Security Hub.
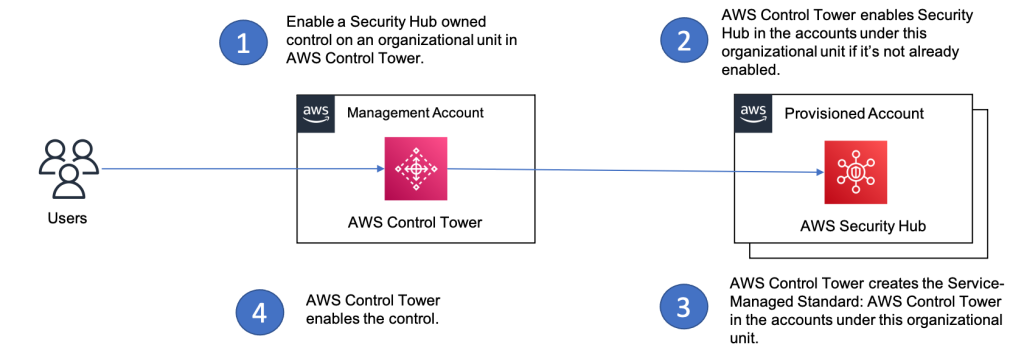
Figure 1. Integration workflow between AWS Control Tower and Security Hub
Drift detection flow
The following Figure 2 shows the drift detection workflow. This example considers drift when you disable a control from Security Hub, which was originally enabled from AWS Control Tower.
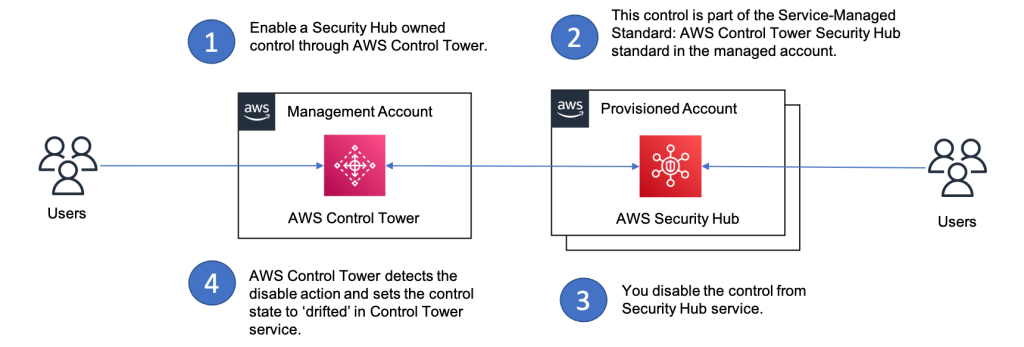
Figure 2. Drift detection workflow between AWS Control Tower and Security Hub.
Steps
Pre-requisites:
- Update AWS Control Tower landing zone version to 3.2 for the drift detection capability. See Update your Landing Zone for more information.
Steps to integrate AWS Control Tower and Security Hub
The following steps integrate Security Hub with AWS Control Tower.
-
- Go to the AWS Control Tower console, click All Controls in the left-hand pane.
- Choose any Security Hub owned controls. For this example, we chose [SH.APIGateway.5] API Gateway REST API cache data should be encrypted at rest.
- Click the Enable control button.
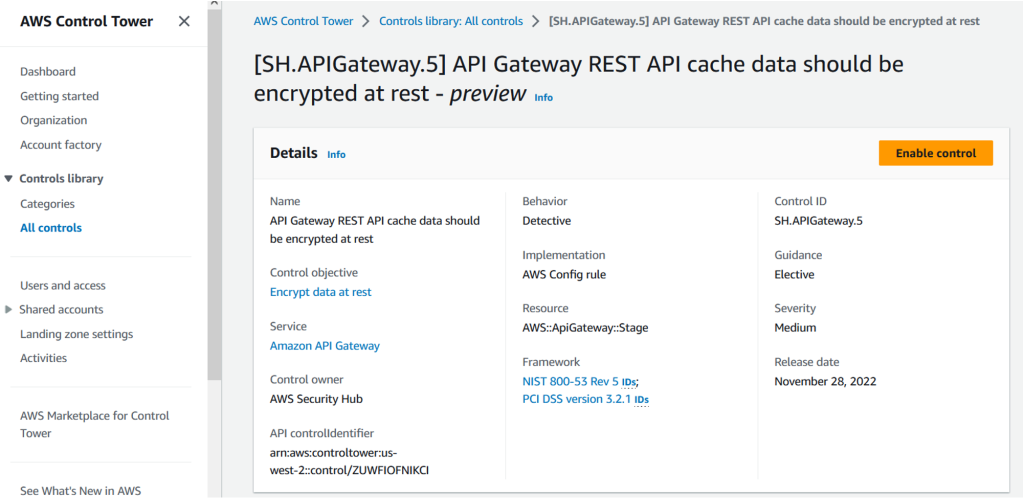
Figure 3. Screenshot of a Security Hub control detail page
-
- Select the OU for which you want to enable this control. For example, we chose the Custom OU.
- Click Enable control on OU.
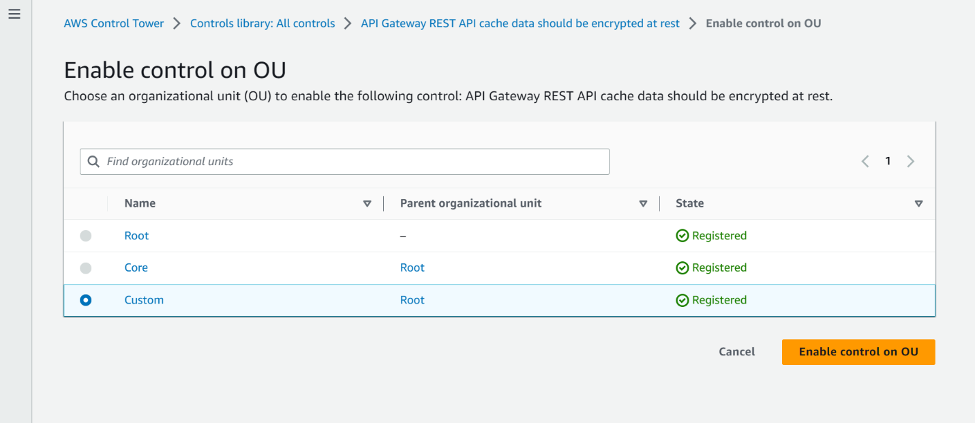
Figure 4. Screenshot of an organizational unit selection page for control enablement
-
- Log in to an account that is managed under the OU you selected in step 4.
- Navigate to the Security Hub console and click on Security standards in the left-hand pane. Click on the Service-Managed Standard: AWS Control Tower to see the control you enabled in step 2.
- In figure 5 below, we will see the AWS Control Tower managed standard in Security Hub and the control we enabled is a part of this standard.


Figure 5. Screenshots of the security standard in Security Hub that is managed by AWS Control Tower
The preceding steps show you how to enable Security Hub controls through AWS Control Tower console. You can also enable these controls with AWS CLI or AWS Control Tower control API operations.
You can use this AWS CLI command to enable the control:
import json import boto3 ct = boto3.client( 'controltower', region_name='<region>') try: response = ct.enable_control(controlIdentifier=<ARN_of_the_control>, targetIdentifier=<ARN_of_the_OU>) print("Response: " + response['operationIdentifier']) except Exception as e: print(e) raise eAt this point, you have enabled the integration between AWS Control Tower and Security Hub successfully. In the next section, we will show you how the drift detection capability of AWS Control Tower works for Security Hub owned controls. We will use the same control that we enabled in the previous steps.
Steps to test the drift detection workflow
- Log in to the member account from in the preceding section that has the control enabled.
- Navigate to Security Hub console and select Security standards from left hand pane.
- Click on Service-Managed Standard: AWS Control Tower, which will show you the control you enabled in the previous section.
- Click on the control and click Disable Control. The following Figure 6 shows how you can disable this control.

Figure 6. Screenshot of the control in AWS Control Tower managed security standard with the Disable Control option
-
- Choose any one of the reasons from the dropdown list and click Disable. This action will set the control to ‘Drifted’ state in AWS Control Tower.
- To see the ‘Drifted’ state, go to the AWS Control Tower console in the management account and select All Controls in the left pane. Search for the control SH.APIGateway.5 and click on the OUs enabled tab. You should see the Control State on OU as Drifted as shown in the following Figure 7.
-

Figure 7. Screenshot of the control in Drifted state in AWS Control Tower console
Cleanup
To delete the Service-Managed Standard: AWS Control Tower from the accounts you enabled the Security Hub owned controls, you must disable these controls from AWS Control Tower. This will apply to all the accounts under this organizational unit. Deleting the standard does not deactivate Security Hub for your account.
Using Security Hub to view the compliance of detective controls
After setting up your detective controls via AWS Control Tower, you can use Security Hub to detect the existing mis-configurations in your accounts. Currently, you cannot view the compliance status of the Security Hub detective controls in AWS Control Tower. In Security Hub, you can view those findings and compliance state both on an individual account and an organizational level.
To view findings for a specific control that was activated by AWS Control Tower via the Security Hub console:
- Navigate to the Standards page.
- Access the “Service-managed standard: AWS Control Tower” standard.
- Access the control whose findings you’d like to view.
- The list of findings will then be shown at the bottom of the page.

Figure 8. Screenshot of a Security Hub findings page for AWS Control Tower controls
Alternatively, you can use the GetFindings command via the API or CLI.
To view all findings in a single Region, you can set cross-Region aggregation in Security Hub. Now you can view all findings at the same time without switching between Regions. For additional information, see the Security Hub documentation.
Conclusion
In this post, we showed you how to integrate, enable, and manage Security Hub controls with AWS Control Tower. We demonstrated AWS Control Tower drift detection for Security Hub owned controls. We showed how to leverage Security Hub to view the findings for these controls across your AWS organization. With this generally available feature, you can use Security Hub as a single place to detect misconfigurations while governing your AWS Control Tower environments at scale.
If you have any questions about this post, start a thread on the re:Post forum.
About the authors: