AWS Cloud Operations Blog
Tag: Synthetics
Using environment variables with Amazon CloudWatch Synthetics
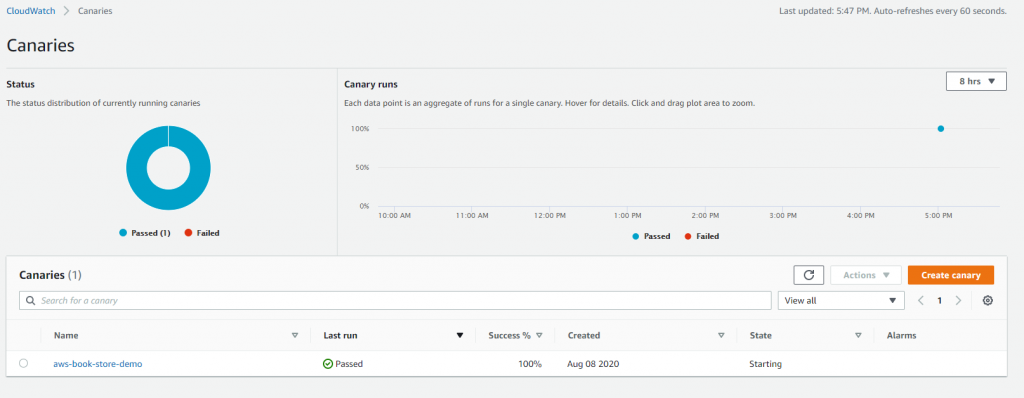
With the increase in online traffic, organizations have prioritized the continuous monitoring of their applications so that they can detect issues before they cause widespread problems. Canaries emulate a user flow, making it possible for organizations to proactively catch errors thereby ensuring a good customer experience. Amazon CloudWatch Synthetics allows you to create canaries to […]
Cross-Region application monitoring using Amazon CloudWatch Synthetics and AWS CloudFormation
Customers need a way to find problems with their application before the real end users encounter them. They need to predict how their application will perform in supported geographies and isolate the root cause of any detected bottlenecks. Synthetic monitoring allows customers to emulate business processes or user transactions from different geographies and monitor their […]
Secure monitoring of user workflow experience using Amazon CloudWatch Synthetics and AWS Secrets Manager
Customers often need an easy way to monitor the URLs, API endpoints, and critical GUI workflows of their web applications in a secure fashion. Monitoring helps keep the service available by detecting performance bottlenecks and operational issues as soon as they arise. Customers also want to be alerted when availability and latency issues occur so […]
Monitor your private internal endpoints 24×7 using CloudWatch Synthetics
Introduction Since Amazon CloudWatch Synthetics launched in 2019, Synthetics canaries have become the first line of defense to reliably alert developers if their public endpoints, including REST APIs and URLs, show unexpected latencies or availability drops. In addition, Synthetics canaries can also monitor for broken links, or unauthorized content changes resulting from phishing, code injection, […]