AWS Cloud Operations Blog
Using Amazon CloudWatch metric filters and alarms to monitor logs on SonicWall Firewall
In this guest post, Marcin Gornik – Director of IT at Tommy John Inc discusses how they used CloudWatch Metric Filters to monitor their SonicWall Firewall system to better secure their infrastructure.
TommyJohn, a clothing design and manufacturer company, uses Amazon CloudWatch to monitor their SonicWall firewall devices. This blog discusses why CloudWatch was selected as a monitoring solution and information detailing how it was configured.
Overview
TommyJohn uses SonicWall Firewall software to secure their network from external security threats. Continuously monitoring and managing the firewall devices on a regular basis is a critical daily task for the company’s security engineers. Also important is the task of analyzing the logs generated and performance characteristics, in order to identify potential gaps in the setup. The team wanted to identify a solution that is concise, meets technical and business needs, simple to set up and easier to maintain.
After assessing various options, the IT team at TommyJohn decided to use CloudWatch, because it met the business and technical requirements, including:
- Near real-time log monitoring
- Notifications
- The ability to further automate actions based on monitoring events
These benefits improve visibility into the functioning of SonicWall Firewall software, and help the organization protect its assets from unwanted harm. In the era of data privacy, regulations, and compliance, maintaining data security and integrity in an organization is key. Both large and small organizations employ various security measures, including deploying firewall software inside their networks, to enforce network security policies and manage network traffic. Network administrators who manage firewall software must be well equipped with advanced monitoring tools to ensure that the firewall rules are working as intended.
Solution
This section demonstrates how we at TommyJohn set up SonicWall Firewall log ingestion to CloudWatch Logs.
The assumption is that:
- You are already aware of the basics of Amazon CloudWatch and IAM roles and policies.
- You are using SonicWall Firewall OS 6.5 or higher.
- Your firmware version is 6.5.4.4 or higher.
Create a Cloudwatch LogGroup and LogStream
First, we created a new LogGroup and a LogStream for SonicWall Firewall Logs to ingest into CloudWatch. It is a good idea to group relevant LogStreams into LogGroups for better organization and querying logs effectively. To accomplish this, we followed the below steps:
- Log in to the AWS management console and navigate to CloudWatch Logs.
- Select Create log group under the Action drop-down menu.
- Give the log group a name, such as
SonicWall-Logs. - In the newly created log group, create a new log stream and give it a name, such as
SonicWall-Logstream.
Create or set up IAM User and Permissions
We decided to create new IAM User that can be used in SonicWall FireWall software to send logs to AWS. To more easily manage user permissions, we created an IAM Group instead of assigning permissions directly to an IAM User. We assigned necessary permissions to the Group and then assigned the IAM User to the Group. This allows us to modify permissions for a set of users at a time. The following steps show how we accomplished that.
Create IAM group
- On the IAM console, under Groups, we selected Create New Group.
- We named the group as
SonicWall-Agentsand then attached theCloudWatchLogsFullAccessIAM policy to it. - After clicking Next Step, our Review screen looked like the one below. We checked the Group Name and the Policies sections to make sure they are right.
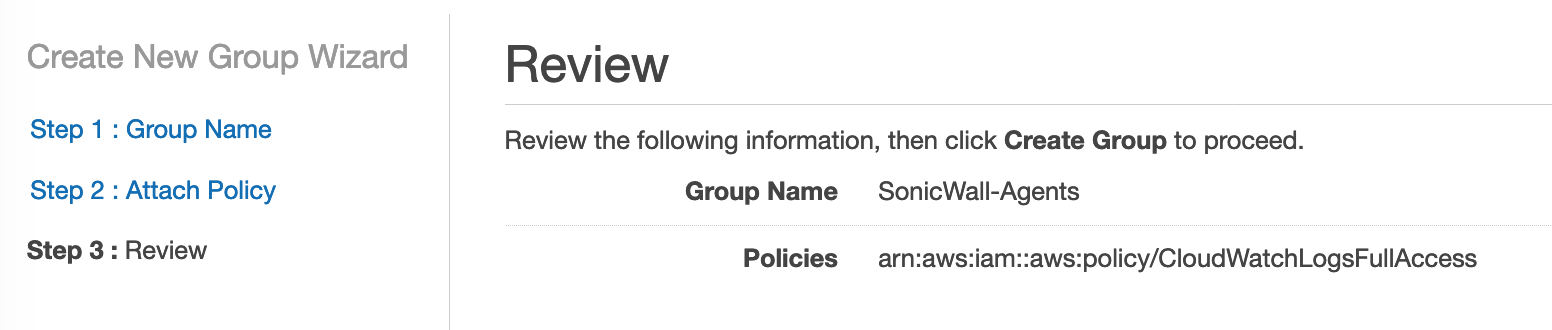
- Created the IAM user group by selecting Create Group.
Now that the IAM user group has been created successfully, we then proceeded to create the IAM User. The following steps demonstrate how we achieved that.
Create IAM User
- On the IAM console under Users, we selected Add User and provided the user name as
SonicWall-user1. - In order to allow this user to make API calls, we checked the Programmatic access checkbox under Access type and proceeded to select Permissions.
- Under Add user to group, we checked SonicWall-Agents group which we created earlier. This allows the user to have the policies that the user group contains. (You can also directly add the required permissions to the user.) We then proceed to select Tag and then select Review.
- Clicking on Create user results in creating a new IAM User.

- We then downloaded the CSV file. Since it contains IDs for Access Key and Secret Key, we kept it in a safe, admin-only location.
Configure IAM permissions in SonicWall
Now that we have both the IAM User group and IAM user created, we then proceed to set up the SonicWall Firewall software. In this section, you can find details about how we set up the AWS account on SonicWall FireWall software so the firewall software has the necessary permissions to send logs into CloudWatch.
- We logged into the SonicWall management console, and selected Manage, then System, then Setup, then Network, and then AWS Configuration.
- We then pasted the Access Key from the CSV file into the Access Key ID text box . (We downloaded this the previous section as part of creating the IAM User.)
- We pasted the Secret Key from the same CSV file into the Secret Access Key and Confirm Key text boxes, as shown in the following screenshot. We select the Mask Key check box on SonicWall which masks the secret key and provides an additional level of security.
- Once we ensured the selected AWS Region was correct, we selected Test Connection to test the connection settings.

Enable AWS logs in your SonicWall log settings
In this section, we configure our SonicWall Firewall to send logs to the desired CloudWatch LogGroup and LogStream. To accomplish this, we followed these steps.
- On the SonicWall AWS Management Console, under Manage, we selected Log Settings and then AWS Logs.
- After ensuring the selected AWS Region is correct, we entered the Log Group and Log Stream names. (We created these earlier in the Amazon CloudWatch console.) The screenshot below shows what this step looks like.
- The Synchronization Interval filed on SonicWall FireWall allows you set the frequency duration at which you want the logs to be sent to CloudWatch. We decided to use 900 seconds, which is the maximum duration. When you perform this step, assess this variable carefully and set a frequency that gives you the right balance between performance and cost.
- We selected Accept to finish the setup.

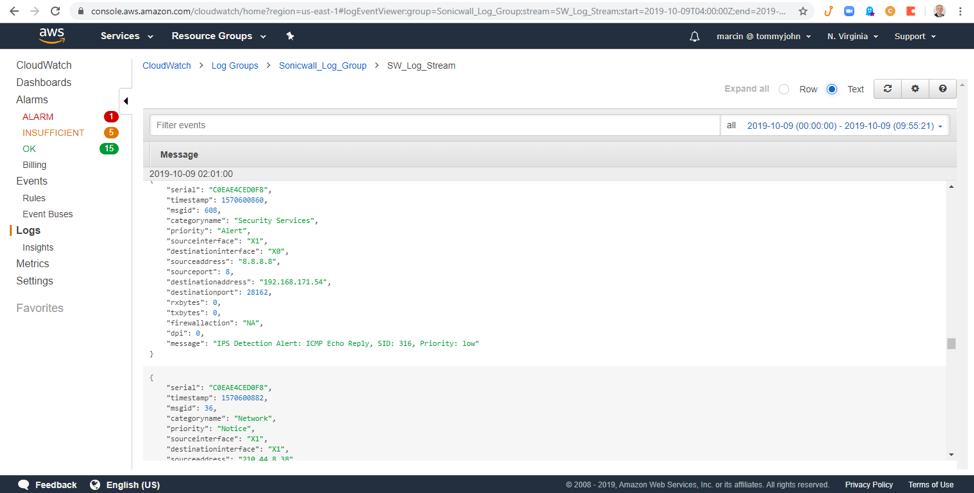
Check syncing
To ensure the setup is working as expected, we log on to the CloudWatch console and check that the logs are syncing to the LogStream we created earlier. The following screenshot shows that the logs are getting ingested properly into CloudWatch.
Create a CloudWatch metric filter on the logs from SonicWall
Along with querying the logs using Logs Insights feature on CloudWatch, we also wanted to get notified when something specific happened so we can quickly take respective action. We decided to use the CloudWatch Metric Filter functionality that allows us to filter out a part of the log data using a Filter Pattern. This filtered message can be stored as a CloudWatch metric that can be used to create alarms.
We followed the below steps to create the Metric Filter.
- On CloudWatch Logs page, we selected the SonicWall_Log_Group log group we created earlier and selected Add Metric Filter.
- We entered the filter pattern string in the Filter Pattern textbox and selected Assign Metric, as shown in the following screenshot.

- After providing a name in the Filter Name box, a namespace name in the Metric Namespace textbox and a Metric Name in the Metric Name textbox we selected Save Filter to save the Metric Filter. This is shown in the following screenshot.

Create an alarm on the metric filter
As mentioned earlier, it is possible to create alarms on Metric Filters. This is as straight forward as creating an alarm on a regular CloudWatch metric. The following steps showcase how we created the alarm.
- On the CloudWatch LogGroup we created, under Metric Filters we selected Create Alarm, as shown in the following screenshot.

- We selected Static under Threshold type, and Greater under Whenever the ErrorCount is…. and entered 5 in the textbox and select Next.
- Because we already had an SNS topic that we wanted to use, we chose Select an existing SNS topic. If you don’t have an SNS topic created, create a new one by selecting Create new topic and following the steps and click Next.
- We provided a unique name to the alarm and selected Next. Once we reviewed the inputs in the Review screen, we created a new alarm by selecting Create alarm.
Testing the alarm
In order to ensure the alarm worked the way we wanted, we tested it with by creating some actions on our enterprise environment that would create the logs which would match the Metric filter. After we did that we went to CloudWatch Alarms section to check if the alarms are firing as expected. The following screenshot shows a historical graph of the alarm firing over a period of time.

The following screenshot shows a sample email notification triggered through CloudWatch alarm notifications.

Conclusion
This post demonstrated how we set up CloudWatch Alarms on logs ingested from SonicWall Firewall in our on-premises data center. Now our IT operations teams can be notified of specific security incidents to help them respond to such incidents quickly. As a result, our team’s Mean Time To Resolution improved considerably, allowing the team to focus on business-critical functions. To learn more about CloudWatch Logs and Metric Filters from our documentation here and here respectively.
The content and opinions in this post are those of the third-party author and AWS is not responsible for the content or accuracy of this post.
About the Author
 Marcin Gornik is a Director of IT at Tommy John Inc. He has a strong networking, networking security, and system administrative background. He is passionate about IT and networking security and is excited to talk about new emerging threats. In his spare time, he is a huge advocate for clean and renewable energies and solutions. Marcin believes we are all never-ending students where there is no end to personal growth and improvement.
Marcin Gornik is a Director of IT at Tommy John Inc. He has a strong networking, networking security, and system administrative background. He is passionate about IT and networking security and is excited to talk about new emerging threats. In his spare time, he is a huge advocate for clean and renewable energies and solutions. Marcin believes we are all never-ending students where there is no end to personal growth and improvement.