Networking & Content Delivery
Hybrid Networking using VPC Endpoints (AWS PrivateLink) and Amazon CloudWatch for Financial Services
Amazon CloudWatch offers a centralized service to collect monitoring and operational data in the form of logs, metrics, and events. This provides a unified view of AWS resources, applications, and services that run on AWS and on-premises servers. When you have Amazon CloudWatch agents running on-premises, the default behavior is to export the collected metrics to CloudWatch public endpoints which can be reached over the internet or Direct Connect Public VIF. This presents a challenge to many enterprises who are bound by their compliance policies to have private connectivity to AWS services. This is especially critical to customers in the financial services industry who hold sensitive data. With AWS PrivateLink, you can prevent your sensitive data from traversing the Internet and maintain compliance with regulations such as HIPAA, EU/US Privacy Shield, and PCI. You can leverage VPC Interface endpoints, powered by AWS PrivateLink, to extend the private connectivity all the way to your on-premises network using Direct Connect Private VIF or VPN. Your traffic is not exposed to the internet, eliminating important threat vectors.
This blog post demonstrates how you can use VPC Endpoint to export metrics from CloudWatch agents running on on-premises servers to Amazon CloudWatch via a private connection. We’ll also secure the endpoint using security-groups and endpoint policy. Let’s get started…
Prerequisites
- An AWS account
- Private connectivity through Direct Connect and/or Site-to-Site VPN to on-premises/DC
- Setup of CloudWatch agent with respect to system-level metrics on your on-premises servers
Solution Overview

Walkthrough
To Implement the solution, you need to complete the following steps for which I have provided step-by-step guidance below:
- Create CloudWatch Interface endpoint from AWS VPC console in us-east-1 region
- Verify private network connectivity between AWS and on-premises using DX/VPN
- Setup Route53 resolver inbound endpoints to resolve DNS queries from on-premises
- Set VPC Interface endpoint with endpoint policies, security group, and network ACL on endpoint ENI
- Verify system-level metrics being delivered to CloudWatch using VPC endpoint
Create VPC Interface Endpoint for CloudWatch Monitoring service
Open Amazon VPC console and navigate to Endpoints and create an Endpoint.
Select AWS services and search for “com.amazonaws.us-east-1.monitoring”
Select the VPC in which you want to create the endpoint and optionally you can also configure tags.
Once you select the VPC, go ahead and select the subnets where you want the endpoint ENIs to be created. As a best practice, you should always select multiple subnets for high availability. 
Select the check box for ‘Enable DNS name’. This feature associates a private hosted zone with the VPC that contains a record set. This enables you to leverage Amazon’s private network connectivity to reach the service. You can do so while making requests to the service’s default public endpoint DNS name.

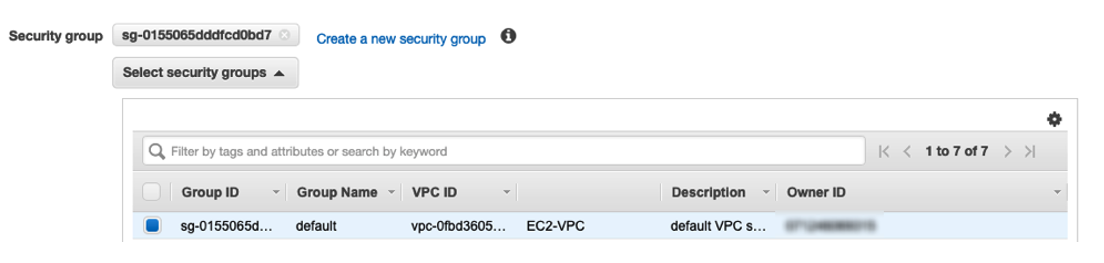
Finally, attach a security-group to the endpoint ENIs. You can also create new security-group to restrict access based on your requirements. Later in the blog, I will customize the security group to allow access from on-premises subnet.
Check and verify the DNS entries and ENIs that were created for the endpoint. As I had selected the ‘Enable DNS name’ during endpoint creation, it created and associated a private hosted zone with the specified VPC. You can find out the DNS entries for your endpoint interface by either selecting VPC endpoint in the VPC console or using the below cli command. After this you can simply run nslookup on monitoring.us-east-1.amazonaws.com or custom DNS entry for endpoint from an ec2 instance.
Note the private DNS name (monitoring.us-east-1.amazonaws.com) which is listed in the above command. You will need this when you setup conditional forwarding on your on-premises DNS resolver. It is always a best practice to be very specific with conditional forwarding as you may want other AWS services over public access.
If you wish to setup the CloudWatch VPC endpoint using CloudFormation for automation purposes, you can also leverage the CloudFormation template below. The CloudFormation template creates a CloudWatch Monitoring VPC endpoint and sets up security-groups on endpoint ENIs. This restricts usage to network subnets you specify and applies an endpoint policy which further restricts the endpoint usage to a specified VPC.
Connectivity between On-Premises and AWS VPC
In this blog we are not going into detail about how to set up Private VIF over Direct Connect or VPN. If you need assistance with DX and VPN setup, please follow our documentations on creating VIFs over DX and setting up VPN. Once you have connectivity up and running, make sure you can communicate with resources in your VPC. For this demo, I tested the connectivity from my on-premises router to an EC2 instance running in the VPC in which the CloudWatch VPC endpoint is deployed.
Setting up Route53 Resolver Inbound Endpoint
Now that you have CloudWatch VPC endpoint setup in your VPC, you will still need a way to communicate with it from your on-premises network. This is where we need to setup Route53 inbound resolver so that DNS queries for private hosted zones forwarded by on-premises DNS resolver can be resolved. You will need to setup conditional forwarding on your on-premises DNS resolver to forward all queries for amazonaws.com to Route53 inbound endpoint IPs. In the following section, I’ll show you how to set up the Route53 endpoint.
- Navigate to the Route53 console and to the Resolver section then select inbound endpoints.
- When you create the resolver endpoint, select the VPC you used when creating CloudWatch VPC endpoint.
- During the resolver endpoint creation, you will need to provide 2 AZs/Subnets so that Route53 can assign 1 IP for each subnet for high availability.

As you already have routing setup between your VPC and on-premises network, you should be able to reach Route53 resolver endpoint’s IPs. You can verify this by running a quick dig command. If you need further assistance, you can also follow our support blog which provides step by step instructions on setting up Route 53 inbound resolvers and testing your configuration.
Dig (Domain Information Groper) is a command line utility that performs DNS lookup by querying name servers and displaying the result to you.
Secure your VPC Endpoint
To secure the endpoint, use the endpoint policy. I used the below policy to restrict access to the VPC which has DX and VPN deployed. Please note: You can also restrict access to an AWS account ID. For more information on endpoint policies, please check out: Controlling access to services with VPC endpoints
To further restrict access to your on-premises network you can use security-groups, which is applied to the endpoint ENI. With this, you can ensure that networks and resources that are allowed to access endpoint are able to. In this demo, I have only allowed access to 10.200.2.0/24, which is my on-premises subnet.

Verify that On-Premises Server Metrics Show-up in CloudWatch
Before checking the CloudWatch metric console, I quickly ran a tcpdump on one of my on-premises servers to verify that the CloudWatch agent was sending the metric data to the CloudWatch VPC endpoint. From the tcpdump snippet, you can see that server is querying Route53 resolver endpoint (10.100.1.77) for monitoring.us-east-1.amazonaws.com. Route53 resolver responds back with ‘A’ records (A 10.100.5.39, A 10.100.3.194, A 10.100.4.146, A 10.100.0.101, A 10.100.2.241, A 10.100.1.6) for CloudWatch VPC endpoint. Once the DNS resolution is complete, CloudWatch agent forwards the metric data to the CloudWatch VPC endpoint private IPs.
Finally, we can check in the CloudWatch Console for on-premises server metrics, under the Custom Namespaces section. You can view it by navigating to CloudWatch console -> Metrics -> All Metrics.

Conclusion
This blog post illustrated how you can privately send CloudWatch metrics from your on-premises network to CloudWatch, using VPC endpoint. It explained how customers (especially in the financial services industry) with critical data can secure their VPC endpoint by using endpoint policy and then further restrict the access to on-premises networks using security-groups applied to endpoint ENIs. AWS PrivateLink provides you with granular control over how your applications connect to AWS services without needing to establish connectivity over the public internet and thus complying with your company’s compliance and security policies. You can leverage this architecture for other AWS Services that integrate with AWS PrivateLink as well. The core building blocks of the solution remain the same.
You can learn more about AWS PrivateLink in our service page here.
