AWS Open Source Blog
Prometheus 2.26.0 adds AWS Signature Version 4 support
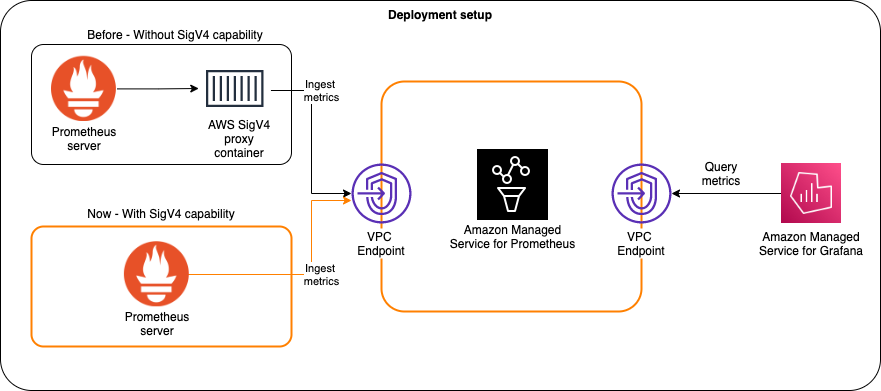
The latest release of Prometheus (v2.26.0), an open source systems monitoring and alerting toolkit, rolled out native AWS Signature Version 4 authentication support. With this new feature, the Prometheus server is able to directly make remote-write API calls to send metrics to the Amazon Managed Service for Prometheus (AMP) without having to rely on a proxy sidecar container, such as the AWS SigV4 container. The GitHub pull request PR 8509 that adds this feature is the original AWS Signature Version 4 authentication code in the Grafana Cloud Agent. This uses the AWS SDK for Go to enable this feature.
What is AWS Signature Version 4?
AWS Signature Version 4 is a process to add authentication information to requests made to AWS APIs using HTTP. The AWS Command Line Interface (AWS CLI) and the AWS SDKs already use this protocol to make calls to the AWS APIs. Review the AWS Signature Version 4 docs to learn about how the Signature Version 4 signing process works.
How Signature Version 4 works with AMP
This feature uses the SDK for Go, as seen in the sigv4.go file in the repo. As mentioned, AWS SDKs use the Signature Version 4 authentication protocol natively to make calls to AWS APIs. As a result, the metric ingestion calls made to the remote write API endpoints from the Prometheus server to the AMP workspace are made using the Signature Version 4 protocol.
The following diagram shows how this changes.
Read the updated getting started blog post to understand how to start using this setup.
Conclusion
Learn more about the Amazon Managed Service for Prometheus (AMP) by reading the user guide. If you are using a standalone Prometheus server, you can download the latest release from the Prometheus site. Read the full release notes for version 2.26.0 to learn more.
Let us know if your configuration doesn’t work or if you have any feedback on how the user experience can be further simplified. Please file an issue with your question, or if you want to report a bug or suggest an enhancement.