AWS Open Source Blog
Using Steampipe Relationship Graphs to Navigate Cloud Resources on AWS
Relationship graphs in Steampipe are helpful visualizations to provide quick context of your cloud environments which highlight important information about your resources.
In our last posts we showed how the open source Steampipe tool can be used to query AWS with SQL with the Steampipe AWS plugin. You can also use Steampipe to run compliance benchmarks with the Steampipe AWS Compliance mod and leverage dashboards-as-code with AWS Insights mod to gain insights on your AWS inventory across regions and accounts.
In today’s post we’ll show you how you can navigate between resources using the new relationship graph capabilities added to Steampipe AWS Insights dashboards. These new graphs help:
- Understand relationships and dependencies at a glance: What services log to this Amazon Simple Storage Service (Amazon S3) bucket? What instances are targeted by this load balancer? What identity access management (IAM) role is used by this Lambda function? Does this Amazon Virtual Private Cloud (Amazon VPC) use peering?
- Review architecture and topology: What is the network structure of this VPC? Is this application balanced across availability zones? Is my Amazon Relational Database Service (Amazon RDS) instance in the database subnet?
- Identity and permissions: What users are in this group? What resources use this IAM role? What permissions are granted by this principal?
To get started and to see your own AWS accounts in these dashboards, here are the prerequisites:
Here’s the setup:
git clone https://github.com/turbot/steampipe-mod-aws-insights.git
cd steampipe-mod-aws-insights
steampipe dashboard
Now visit localhost:9194 in your browser to view and interact with the dashboards, as shown here.

Let’s take a closer look at some dashboard examples of how Steampipe relationship graphs can help you navigate and manage your AWS infrastructure across accounts.
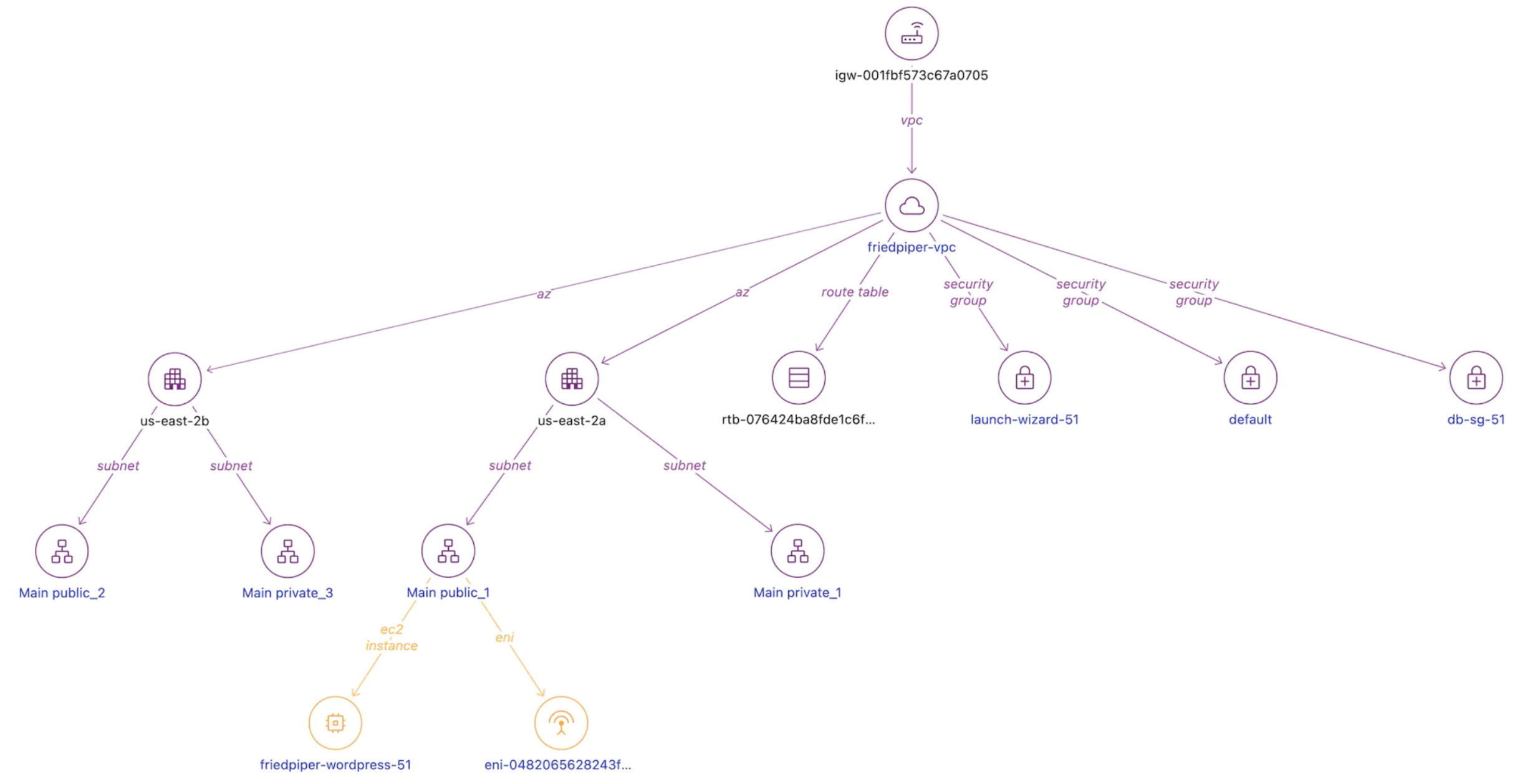
VPC Dashboard
We can start with the VPC Detailed Report. In this environment, we see the four subnets and the availability zones. For example, in the public_1 subnet, we find an Amazon Elastic Compute Cloud (Amazon EC2) Instance and its associated network interface. You can also navigate the Security Groups created in this VPC.
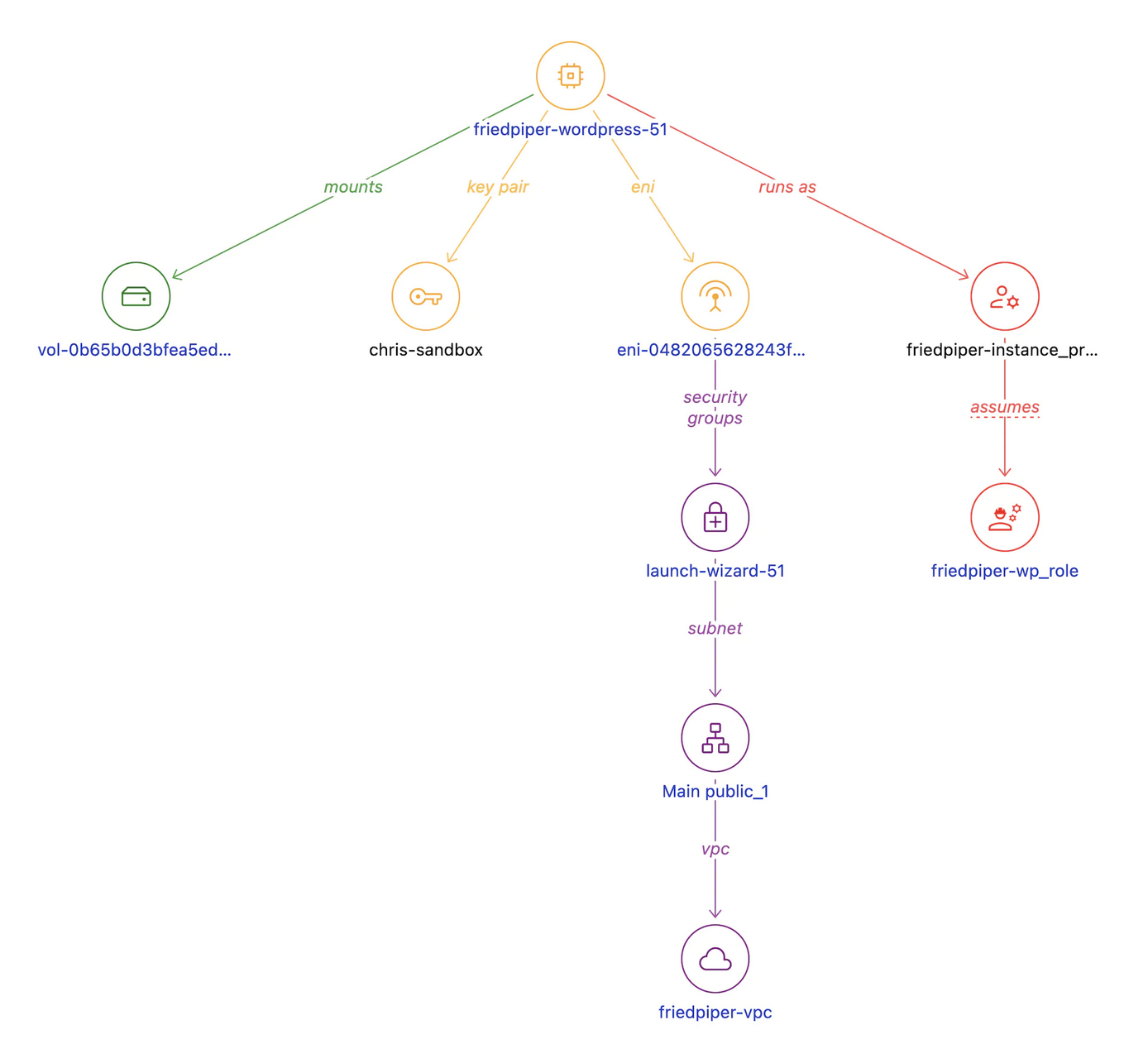
Amazon EC2 Instance
We can click on the WordPress instance to see more details about it. Here we see the WordPress instance has a disk and a network interface. In addition, we can see the instance role. The SSH keys are often a way to see who created a machine.
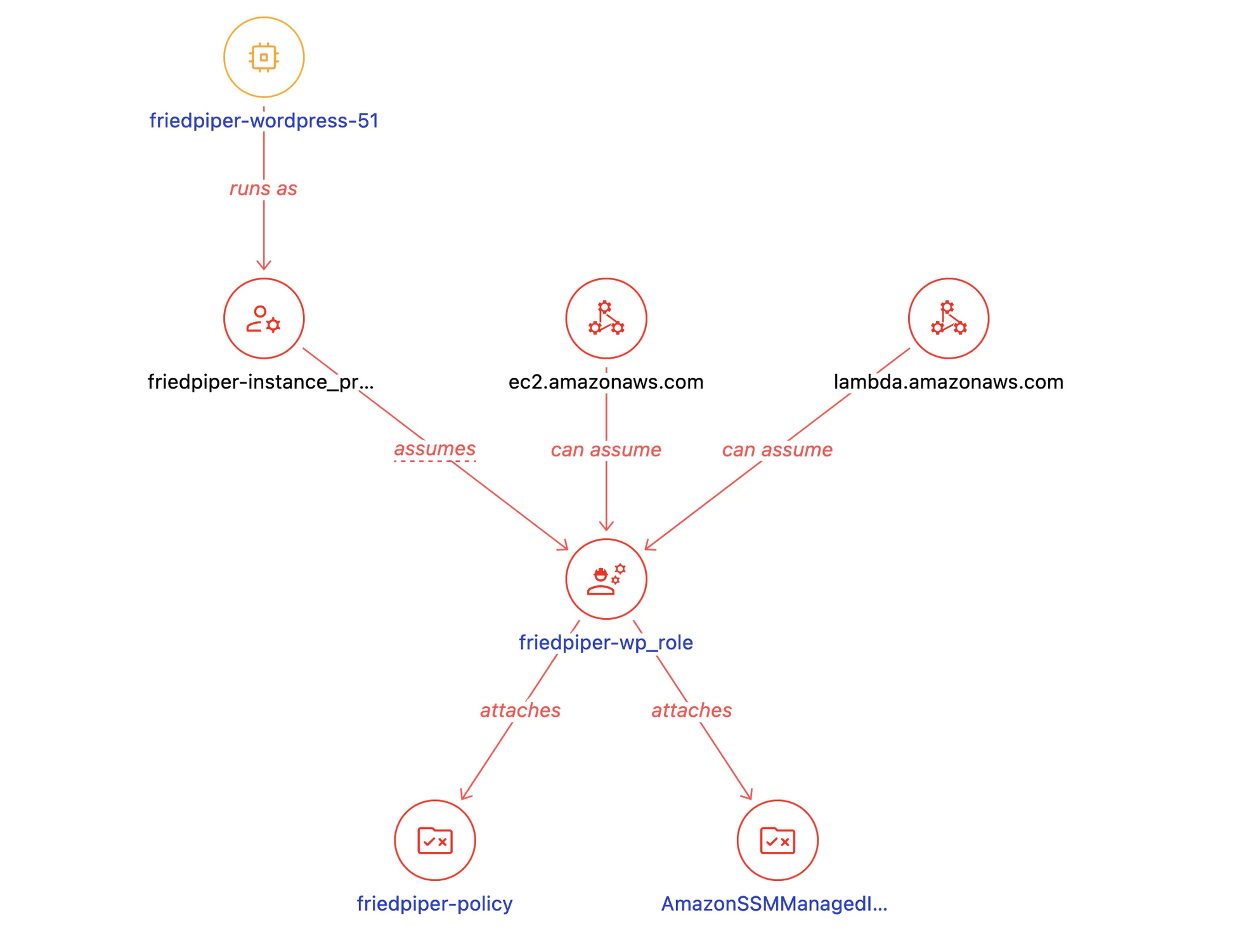
IAM Role
The IAM Role allows us to see what permissions the WordPress instance has. The instance has the AmazonSSMManagedInstanceCore role.
Additionally, both the Amazon EC2 instance and the AWS Lambda services can assume this IAM role, as shown in the diagram. As this role is for Amazon EC2, that is something a DevOps engineer should investigate.
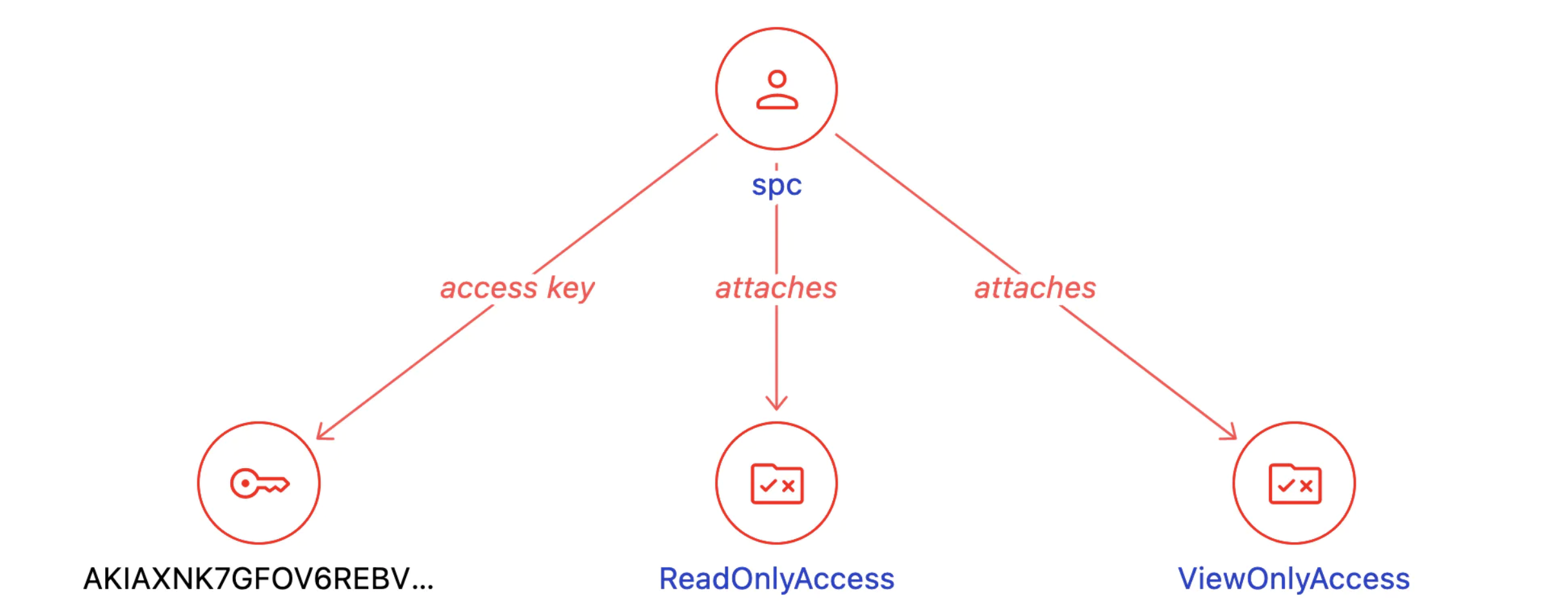
User Detail
The IAM User Detail dashboard shows the relationship between a user, their access keys, and the attached policies. For example, this diagram shows what the Steampipe Cloud IAM user looks like. The spc user has an access key and attaches ReadOnlyAccess and ViewOnlyAccess.
Uncover hidden details in your AWS footprint
These graphs work hand-in-hand with their dashboards’ infocards, charts, and tables to help you understand your AWS cloud in a whole new way. Which of these seem most useful to you? What other kinds of relationships will help you understand your cloud environments and manage them more effectively?
We’re excited to learn more about your experience using the AWS Insights Mod. Our Slack community is a great place to share your feedback and connect with other AWS users.