AWS Security Blog
AWS FedRAMP-Trusted Internet Connection (TIC) Overlay Pilot Program
I’m pleased to announce a newly created resource for usage of the Federal Cloud—after successfully completing the testing phase of the FedRAMP-Trusted Internet Connection (TIC) Overlay pilot program, we’ve developed Guidance for TIC Readiness on AWS. This new way of architecting cloud solutions that address TIC capabilities (in a FedRAMP moderate baseline) comes as the result of our relationships with the FedRAMP Program Management Office (PMO), Department of Homeland Security (DHS) TIC PMO, GSA 18F, and FedRAMP third-party assessment organization (3PAO), Veris Group. Ultimately, this approach will provide US Government agencies and contractors with information assisting in the development of “TIC Ready” architectures on AWS.
Background on TIC
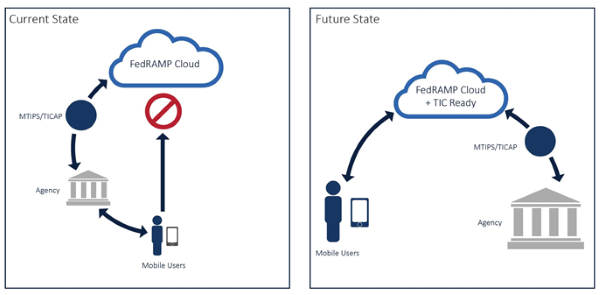
In November 2007, the Office of Management & Budget (OMB) mandated that government users could only access their cloud provider through an agency connection, either a TIC Access Provider (TICAP) or Managed Trusted Internet Protocol Service (MTIPS). These agency connections can be slow and cause additional constraints on a government network or infrastructure. In today’s “anytime, anywhere” world, it’s important for government users to access their cloud-based data from any device with speed and agility.
In May 2015, the FedRAMP PMO and DHS TIC PMO invited AWS to participate in the FedRAMP-TIC Overlay pilot program to develop an approach that balances the need for speed and security, while also removing the frustrations and headaches caused by slow connectivity and suboptimal network routing. The goal of the pilot was to help develop and test a new way of architecting access to cloud-based services with TIC capabilities that would maintain a high level of security—mapped to FedRAMP security controls—and still provide a friendly and accessible government user experience. The following figure shows the current state, with cloud services accessible through an agency TIC, and the proposed future state, with mobile user access directly to cloud services.
AWS pilot results
The pilot was conducted in collaboration with DHS and FedRAMP. As an initial analysis, we leveraged a TIC-capabilities-to-FedRAMP-Moderate controls mapping table provided for the pilot. Our 3PAO determined that 80% of the TIC capabilities were covered within AWS’s existing FedRAMP Agency Authority to Operate. During the course of the pilot, in collaboration with DHS and FedRAMP, 17 of the TIC capabilities were removed from the pilot as either not relevant—and therefore excluded—or not appropriate to a cloud service provider (CSP)—and therefore deferred to the agency. Of the remaining 57 TIC candidate capabilities, we determined that responsibilities would be allocated as follows:
- Shared between AWS and the customer (36).
- Solely the responsibility of the customer (16).
- Solely the responsibility of AWS (5).
Through the pilot activities, we worked with GSA 18F and our 3PAO to identify and demonstrate implementation of the required capabilities through a combination of native AWS services and the use of technologies available from the AWS Marketplace.
Take advantage of TIC connectivity on AWS today
Our government customers interested in following GSA 18F’s lead now have the capability to deploy and test their own TIC capabilities on AWS. While the FedRAMP-TIC Overlay is being finalized, customers can use the evidence resulting from our TIC Mobile assessment to implement the TIC capabilities as part of their virtual perimeter protection solution using functionality provided by AWS and our ecosystem partners. With a clear definition of the customer responsibility for implementation of the additional TIC capabilities, our government customers can architect for TIC readiness on AWS.
Take a look at our TIC readiness whitepaper, which provides an overview of the FedRAMP-TIC Overlay pilot and its goals, guidance about how customers can implement TIC, and appendices that provide detailed mappings of customer responsibility for the TIC capabilities.
If you’d like to learn more about AWS’ FedRAMP program, please visit our FAQ page, or, for general compliance information, please see our Cloud Compliance page.
Want more AWS Security how-to content, news, and feature announcements? Follow us on Twitter.