AWS Security Blog
Category: Technical How-to
How to detect suspicious activity in your AWS account by using private decoy resources
As customers mature their security posture on Amazon Web Services (AWS), they are adopting multiple ways to detect suspicious behavior and notify response teams or workflows to take action. One example is using Amazon GuardDuty to monitor AWS accounts and workloads for malicious activity and deliver detailed security findings for visibility and remediation. Another tactic […]
How to incorporate ACM PCA into your existing Windows Active Directory Certificate Services
Using certificates to authenticate and encrypt data is vital to any enterprise security. For example, companies rely on certificates to provide TLS encryption for web applications so that client data is protected. However, not all certificates need to be issued from a publicly trusted certificate authority (CA). A privately trusted CA can be leveraged to […]
Introducing a new AWS whitepaper: Does data localization cause more problems than it solves?
Spanish version Amazon Web Services (AWS) recently released a new whitepaper, Does data localization cause more problems than it solves?, as part of the AWS Innovating Securely briefing series. The whitepaper draws on research from Emily Wu’s paper Sovereignty and Data Localization, published by Harvard University’s Belfer Center, and describes how countries can realize similar […]
Extend your pre-commit hooks with AWS CloudFormation Guard
Git hooks are scripts that extend Git functionality when certain events and actions occur during code development. Developer teams often use Git hooks to perform quality checks before they commit their code changes. For example, see the blog post Use Git pre-commit hooks to avoid AWS CloudFormation errors for a description of how the AWS […]
How to protect HMACs inside AWS KMS
April 20, 2022: In the section “Use the HMAC key to encode a signed JWT,” we fixed an error in the code sample. Today AWS Key Management Service (AWS KMS) is introducing new APIs to generate and verify hash-based message authentication codes (HMACs) using the Federal Information Processing Standard (FIPS) 140-2 validated hardware security modules […]
How to set up IAM federation using Google Workspace
August 10, 2022: This blog post has been updated to reflect the new name of AWS Single Sign-On (SSO) – AWS IAM Identity Center. Read more about the name change here. March 16, 2022: The title and the opening section of this blog post has been updated. Federating your external identity provider (IdP) to AWS […]
How to deploy AWS Network Firewall to help protect your network from malware
April 25, 2023: We’ve updated this blog post to include more security learning resources. Protecting your network and computers from security events requires multi-level strategies, and you can use network level traffic filtration as one level of defense. Users need access to the internet for business reasons, but they can inadvertently download malware, which can […]
How to use tokenization to improve data security and reduce audit scope
April 25, 2023: We’ve updated this blog post to include more security learning resources. Tokenization of sensitive data elements is a hot topic, but you may not know what to tokenize, or even how to determine if tokenization is right for your organization’s business needs. Industries subject to financial, data security, regulatory, or privacy compliance […]
Continuous compliance monitoring using custom audit controls and frameworks with AWS Audit Manager
French version For most customers today, security compliance auditing can be a very cumbersome and costly process. This activity within a security program often comes with a dependency on third party audit firms and robust security teams, to periodically assess risk and raise compliance gaps aligned with applicable industry requirements. Due to the nature of […]
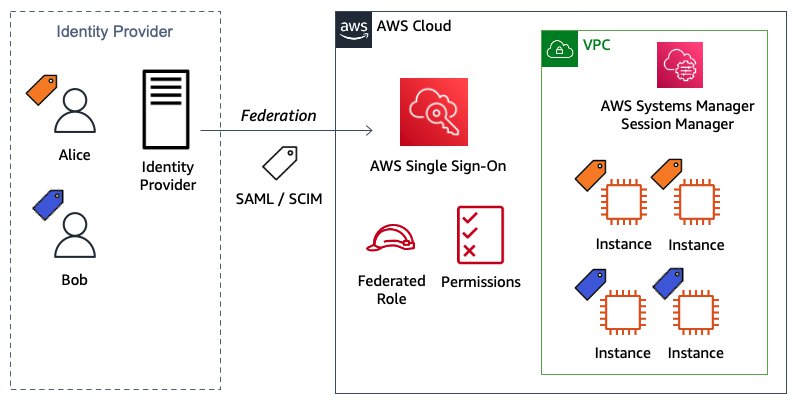
Configure AWS IAM Identity Center ABAC for EC2 instances and Systems Manager Session Manager
September 12, 2022: This blog post has been updated to reflect the new name of AWS Single Sign-On (SSO) – AWS IAM Identity Center. Read more about the name change here. In this blog post, I show you how to configure AWS IAM Identity Center to define attribute-based access control (ABAC) permissions to manage Amazon […]