AWS Security Blog
How to use Amazon GuardDuty and AWS Web Application Firewall to automatically block suspicious hosts
April 25, 2023: We’ve updated this blog post to include more security learning resources.
When you’re implementing security measures across your AWS resources, you should use a holistic approach that incorporates controls across multiple areas. In the Cloud Adoption Framework (CAF) Security perspective whitepaper, we define these controls across four categories.
- Directive controls. Establish the governance, risk, and compliance models the environment will operate within.
- Preventive controls. Protect your workloads and mitigate threats and vulnerabilities.
- Detective controls. Provide full visibility and transparency over the operation of your deployments in AWS.
- Responsive controls. Drive remediation of potential deviations from your security baselines.
The use of security automation is also a key principle outlined in the whitepaper. It helps reduce operational overhead and create repeatable, predictable approaches to monitoring and responding to events. You can take advantage of AWS services to build powerful solutions for the automated detection and remediation of threats against your AWS environments. For example, you can configure Amazon CloudWatch Events to invoke a Lambda action in response to suspicious or unexpected behavior in your AWS environment detected by Amazon GuardDuty. You can configure automated flows that use both detective and responsive controls and might also feed into preventative controls to help mitigate the threat in the future. Depending on the type of source event, you can automatically invoke specific actions, such as modifying access controls, terminating instances, or revoking credentials.
In this blog post, we’ll show you how to use Amazon GuardDuty to automatically update the AWS Web Application Firewall Web Access Control Lists (WebACLs) and VPC Network Access Control Lists (NACLs) in response to GuardDuty findings. After GuardDuty detects a suspicious activity, the solution updates these resources to block communication from the suspicious host while you perform additional investigation and remediation. Once communication has been blocked, further occurrences of a finding are reduced, allowing security and operations teams to focus more on higher priority tasks.
Amazon GuardDuty is a continuous security monitoring and threat detection service that incorporates threat intelligence, anomaly detection, and machine learning to help protect your AWS resources, including your AWS accounts. Amazon CloudWatch Events delivers a near-real-time stream of system events that describe changes in AWS resources. Amazon GuardDuty sends notifications based on Amazon CloudWatch Events when any change in the findings takes place. In the context of GuardDuty, such changes include newly generated findings and all subsequent occurrences of these existing findings. Using rules that you can quickly set up, you can match CloudWatch events and route them to one or more target actions. This solution routes matched events to AWS Lambda, which then performs updates to AWS Web Application Firewall (WAF) and VPC NACLs. AWS WAF is a web application firewall that helps protect your web applications from common web exploits that could affect application availability, compromise security, or consume excessive resources. It supports both managed rules as well as a powerful rule language for custom rules. A Network Access Control List (NACL) is an optional layer of security for your Amazon Virtual Private Cloud (VPC) that acts as a firewall for controlling traffic in and out of one or more subnets.
Solution overview
The solution assumes that Amazon GuardDuty is enabled in your AWS account. If it isn’t enabled, you can find more info about the free trial and pricing here, and you can follow the steps in the GuardDuty documentation to set up the service and start monitoring your account.
Figure 1 shows how the CloudFormation template creates the sample solution:
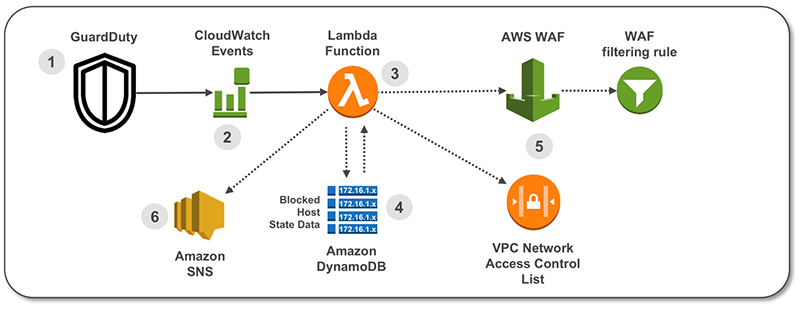
Figure 1: How the CloudFormation template works
Here’s how the solution works, as shown in the diagram:
- A GuardDuty finding is raised with suspected malicious activity.
- A CloudWatch Event is configured to filter for GuardDuty Finding type.
- A Lambda function is invoked by the CloudWatch Event and parses the GuardDuty finding.
- State data for blocked hosts is stored in Amazon DynamoDB table. The Lambda function checks the state table for existing host entry.
- The Lambda function creates a Rule inside AWS WAF and in a VPC NACL.
- A notification email is sent via Amazon Simple Notification Service (SNS).
A second Lambda function runs on a 5-minute recurring schedule and removes entries that are past the configurable retention period from WAF IPSets (which is a list that contains the blacklisted IPs or CIDRs), VPC NACLs, and the Dynamo DB table.
GuardDuty findings referenced in this solution
This solution’s CloudWatch Event Rule pattern is configured to match the following GuardDuty Finding types:
- UnauthorizedAccess:EC2/SSHBruteForce
This finding informs you that an EC2 instance in your AWS environment was involved in a brute force attack aimed at obtaining passwords to SSH services on Linux-based systems. - UnauthorizedAccess:EC2/RDPBruteForce
This finding informs you that an EC2 instance in your AWS environment was involved in a brute force attack aimed at obtaining passwords to RDP services on Windows-based systems. - Recon:EC2/PortProbeUnprotectedPort
This finding informs you that a port on an EC2 instance in your AWS environment isn’t blocked by a security group, access control list (ACL), or an on-host firewall (for example, Linux IPChains), and known scanners on the internet are actively probing it. - Trojan:EC2/BlackholeTraffic
This finding informs you that an EC2 instance in your AWS environment might be compromised because it’s trying to communicate with an IP address of a black hole. Black holes refer to places in the network where incoming or outgoing traffic is silently discarded without informing the source that the data didn’t reach its intended recipient. - Backdoor:EC2/XORDDOS
This finding informs you that an EC2 instance in your AWS environment is attempting to communicate with an IP address that’s associated with XOR DDoS malware. XOR DDoS is Trojan malware that hijacks Linux systems. - UnauthorizedAccess:EC2/TorIPCaller
This finding informs you that an EC2 instance in your AWS environment is receiving inbound connections from a Tor exit node. Tor is software for enabling anonymous communication. It encrypts and randomly bounces communications through relays between a series of network nodes. - Trojan:EC2/DropPoint
This finding informs you that an EC2 instance in your AWS environment is trying to communicate with an IP address of a remote host that’s known to hold credentials and other stolen data captured by malware.
When one of these GuardDuty finding types is matched by the CloudWatch Event Rule, an entry is created in the target ACLs to deny the suspicious host, and then a notification is sent to an email address by this solution’s Lambda. Blocking traffic from the suspicious host helps to mitigate the threat while you perform additional investigation and remediation. For more information, see Remediating a Compromised EC2 Instance.
Solution deployment
This sample solution includes 6 main steps:
- Deploy the CloudFormation template.
- Create and run a Lambda GuardDuty finding test event.
- Confirm the entry in the VPC Network ACL.
- Confirm the entry in the AWS WAF IPSets.
- Confirm the SNS notification subscription.
- Apply the WAF Web ACLs to resources.
Step 1: Deploy the CloudFormation template
For this next step, make sure you deploy the template within the AWS account and region where you want to monitor GuardDuty findings.
- Select this link to launch a CloudFormation stack in your account.
Note: The stack will launch in the N. Virginia (us-east-1) region. It takes approximately 15 minutes for the CloudFormation stack to complete. To deploy this solution into other AWS regions, first upload the solution’s Lambda deployment packages (zip files with code) to an S3 bucket in the selected region. Once you have uploaded the zip files in the target region, update the CloudFormation ArtifactsBucket and ArticaftsPrefix parameters referenced in step 3 below.
- In the CloudFormation console, select the Select Template form, and then select Next.
- On the Specify Details page, provide the following input parameters. You can modify the default values to customize the solution for your environment.
Input parameter Input parameter description AdminEmail Email address to receive notifications. Must be a valid email address. Retention How long to retain IP addresses in the blacklist (in minutes). Default is 12 hours. CloudFrontIPSetId ID for existing WAF IPSet on CloudFront. Enter the ID here if there’s an existing WAF IPSet on CloudFront you want to use. Leave set to the default value of False if you want to create a new WebACL and IPSet. ALBIPSetId ID for existing WAF IPSet on ALB. Enter if there is an existing WAF IPSet on ALB. Leave set to False for creation of new WebACL and IPSet. ArtifactsBucket S3 bucket with artifact files (Lambda functions, templates, html files, etc.). Leave set to the default value for deployment into N. Virginia region. ArtifactsPrefix Path in the S3 bucket containing artifact files. Leave set to the default value for deployment into N. Virginia region. Note: AWS WAF is not currently available in all regions. For more information about where it’s available, refer to this page.
Figure 2 shows an example of values entered on this screen:

Figure 2: CloudFormation parameters on the “Specify Details” page
- Enter values for all of the input parameters, and then select Next.
- On the Options page, accept the defaults, and then select Next.
- On the Review page, confirm the details, and then select Create.
- While the stack is being created, check the email inbox for the value you gave for the AdminEmail address parameter. Look for an email message with the subject “AWS Notification – Subscription Confirmation”. Select the link to confirm the subscription to the SNS topic. You should see a message similar to this:

Figure 3: Subscription confirmation
Once the Status field for the CloudFormation stack changes to CREATE_COMPLETE, the solution is implemented and is ready for testing.
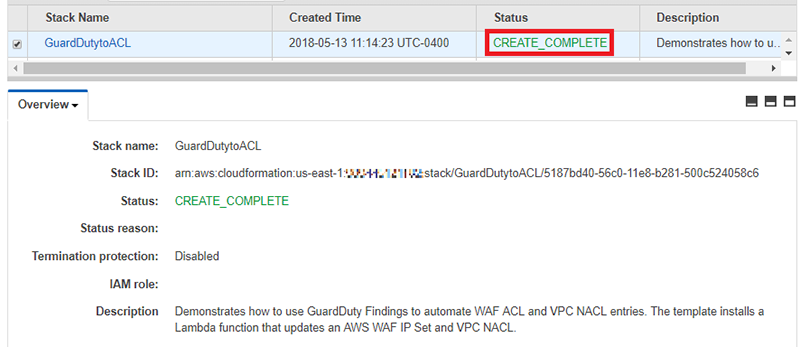
Figure 4: The “Status” displays “CREATE_COMPLETE”
Step 2: Create and run a Lambda GuardDuty finding test event
Once the CloudFormation stack has completed deployment, you can test the functionality using a Lambda test event.
- In the console, select Services > VPC > Subnets and locate a subnet suitable for testing the solution. On the Summary tab, copy the Subnet ID to the clipboard or to a text editor.

Figure 5: The “Subnet ID” value on the “Summary” tab
- In the console, select Services > CloudFormation > GuardDutytoACL stack. In the stack Outputs tab, look for the GuardDutytoACLLambda entry, similar to Figure 6 below:

Figure 6: The “GuardDutytoACLLambda” entry on the “Outputs” tab
- 3. Select the link and you’ll be redirected to the Lambda console, with the Lambda function already open, similar to Figure 7:

Figure 7: The Lambda function open in the Lambda console
- In the top right, select the Select a test event… drop-down list, and then select Configure test events.

Figure 8: Select “Configure test events” from the drop-down list
- To facilitate testing, a test event file has been provided. On the Configure test event page, provide a name for Event name, and then paste the provided test event JSON in the body of the event.
- Update the value of subnetId key (line 34) to the value of your Subnet ID from step 2.1, and then select Create.

Figure 9: Update the value of the “subnetId” key
- Select Test to invoke the Lambda with the test event. You should see a message “Execution result: succeeded” similar to below:

Figure 10: The “Test” button and the “succeeded” message
Step 3: Confirm the entry in the VPC Network ACL (NACL)
In this step, you’ll confirm the DENY entry was created in the NACL. This solution is configured to create up to 10 entries in an ACL ranging between rule numbers 71 and 80. Since NACL rules are processed in order, it’s important that the DENY rule is placed before the ALLOW rule.
- In the console, select Services > VPC > Subnets and locate the subnet you provided for the test event.
- Select the Network ACL tab and confirm the new entry generated from the test event.

Figure 11: Check the entry from the test event on the “Network” tab
Note that VPC NACL entries are created in the rule number range between 71 and 80. Older entries are aged out to create a “sliding window” of blocked hosts.
Step 4: Confirm the entry in the AWS WAF IPSets
In this step, you’ll verify that the entry was added to the CloudFront WAF IPSet and to the ALB WAF IPSet.
- In the console, select Services > WAF & Shield, and then select IP addresses.
- For Filter, select Global (CloudFront), and then select the IPSet named GD2ACL CloudFront IPSet for Blacklisted IP addresses.

Figure 12: Filter the list and then select “GD2ACL CloudFront IPSet for Blacklisted IP addresses”
- Confirm the IP address that was added to the list in the IPSet:

Figure 13: Confirm the IP address was added
- In the console, select Services > WAF & Shield, and then select IP addresses.
- For Filter, select US East (N. Virginia)–or another region in which you deployed this solution–and then select the IPSet named GD2ACL ALB IPSet for blacklisted IP addresses.
- Confirm the IP address added to the ALB IPSet:

Figure 14: Make sure the IP address was added
There might be specific host addresses that you want to prevent from being added to the blacklist. You can do this within GuardDuty by using a trusted IP list. Trusted IP lists consist of IP addresses that you have whitelisted for secure communication with your AWS infrastructure and applications. GuardDuty doesn’t generate findings for IP addresses on trusted IP lists. For additional information, see Working with Trusted IP Lists and Threat Lists.
Step 5: Confirm the SNS notification subscription
In this step, you’ll view the SNS notification that was sent to the email address you set up.
-
- Review the email inbox for the value you provided for the AdminEmail parameter and look for a message with the subject line “AWS GD2ACL Alert.”The contents of the message from SNS should be similar to this:

Figure 15: SNS message example
- Review the email inbox for the value you provided for the AdminEmail parameter and look for a message with the subject line “AWS GD2ACL Alert.”The contents of the message from SNS should be similar to this:
Step 6: Apply the WAF Web ACLs to resources
The final task is to associate the Web ACL with the CloudFront Distributions and Application Load Balancers that you want to automatically update with this solution. To learn how to do this, see Associating or Disassociating a Web ACL with a CloudFront Distribution or an Application Load Balancer.
You can also use AWS Firewall Manger to associate the Web ACLs. AWS Firewall Manager simplifies your AWS WAF administration and maintenance tasks across multiple accounts and resources. With Firewall Manager, you set up your firewall rules just once. The service automatically applies your rules across your accounts and resources, even as you add new resources.
Summary
You’ve learned how to use Amazon GuardDuty to automatically update AWS Web Application Firewall (AWS WAF) and VPC Network Access Control Lists (ACLs) in response to GuardDuty findings. With just a few steps, you can use this sample solution to help mitigate threats by blocking communication with suspicious hosts. You can explore additional solutions possible using GuardDuty Finding types and CloudWatch Events target actions. This solution’s code is available on GitHub. Feel free to play around with the code to add more GuardDuty findings to this solution and also to build bigger and better solutions!
If you have comments about this blog post, submit them in the Comments section below. If you have questions about using this solution, start a thread in the GuardDuty, WAF, or CloudWatch forums, or contact AWS Support.