AWS Security Blog
Tag: AWS IAM
How to use the PassRole permission with IAM roles
iam:PassRole is an AWS Identity and Access Management (IAM) permission that allows an IAM principal to delegate or pass permissions to an AWS service by configuring a resource such as an Amazon Elastic Compute Cloud (Amazon EC2) instance or AWS Lambda function with an IAM role. The service then uses that role to interact with […]
Refine permissions for externally accessible roles using IAM Access Analyzer and IAM action last accessed
When you build on Amazon Web Services (AWS) across accounts, you might use an AWS Identity and Access Management (IAM) role to allow an authenticated identity from outside your account—such as an IAM entity or a user from an external identity provider—to access the resources in your account. IAM roles have two types of policies […]
Secure by Design: AWS to enhance MFA requirements in 2024
November 17, 2025: The MFA Security Key program, which provided eligible customers with free MFA devices, has been discontinued effective November 6th, 2025. While existing devices will continue to function normally, no new orders for MFA security keys will be accepted after the program closure date. Security is our top priority at Amazon Web Services […]
Validate IAM policies by using IAM Policy Validator for AWS CloudFormation and GitHub Actions
April 15, 2024: AWS has launched two new GitHub Actions that can be used to simplify some of the steps covered in this blog post. Click here to learn more abbot the new GitHub actions for AWS CloudFormation and HashiCorp’s Terraform. In this blog post, I’ll show you how to automate the validation of AWS […]
Temporary elevated access management with IAM Identity Center
AWS recommends using automation where possible to keep people away from systems—yet not every action can be automated in practice, and some operations might require access by human users. Depending on their scope and potential impact, some human operations might require special treatment. One such treatment is temporary elevated access, also known as just-in-time access. […]
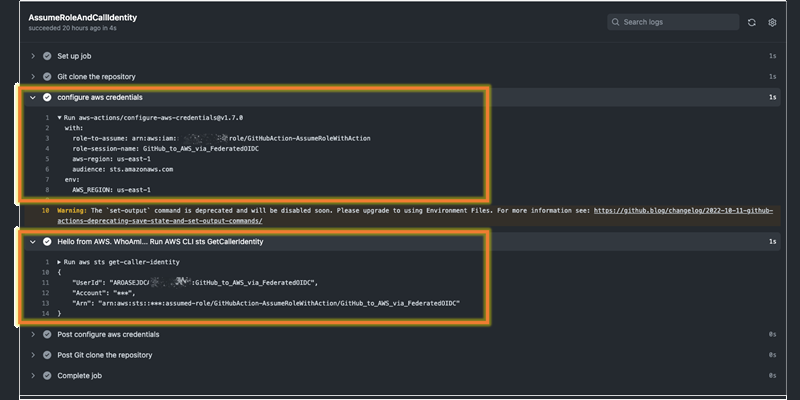
Use IAM roles to connect GitHub Actions to actions in AWS
May 22, 2023: We updated the post to reflect case sensitivity in the IDP entered: https://token.actions.githubusercontent.com. The IDP created in this post should be entered in lowercase through the post. Have you ever wanted to initiate change in an Amazon Web Services (AWS) account after you update a GitHub repository, or deploy updates in an […]
How to prioritize IAM Access Analyzer findings
AWS Identity and Access Management (IAM) Access Analyzer is an important tool in your journey towards least privilege access. You can use IAM Access Analyzer access previews to preview and validate public and cross-account access before deploying permissions changes in your environment. For the permissions already in place, one of IAM Access Analyzer’s capabilities is that […]
How to use Google Workspace as an external identity provider for AWS IAM Identity Center
January 25, 2024: This post is no longer current. Please see this tutorial for the updated info. March 21, 2023: We modified the description of a permission set in the Introduction. March 8, 2023: We updated the post to reflect some name changes (G Suite is now Google Workspace; AWS Single Sign-On is now AWS […]
How to visualize IAM Access Analyzer policy validation findings with QuickSight
In this blog post, we show you how to create an Amazon QuickSight dashboard to visualize the policy validation findings from AWS Identity and Access Management (IAM) Access Analyzer. You can use this dashboard to better understand your policies and how to achieve least privilege by periodically validating your IAM roles against IAM best practices. […]
How to use trust policies with IAM roles
June 20 2023: The wording in this post has been updated to avoid confusion around the use of wildcards in the principal element of an AWS Identity and Access Management (IAM) trust policy statement. November 3, 2022: We updated this post to fix some syntax errors in the policy statements and to add additional use […]