AWS Security Blog
Tag: IAM roles
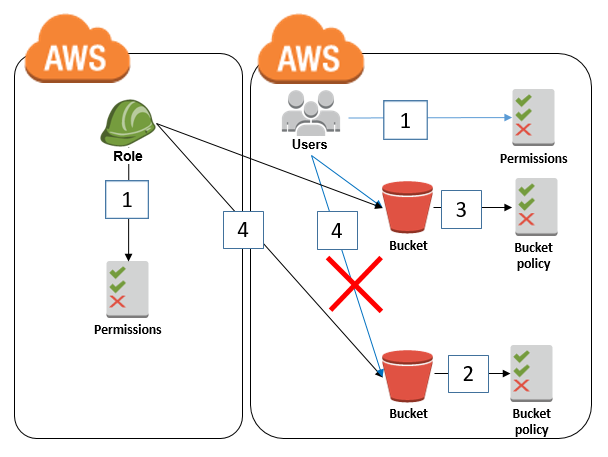
How to restrict Amazon S3 bucket access to a specific IAM role
February 14, 2025: This post was updated with the recommendation to restrict S3 bucket access to an IAM role by using the aws:PrincipalArn condition key instead of the aws:userid condition key. April 2, 2021: In the section “Granting cross-account bucket access to a specific IAM role,” we updated the second policy to fix an error. […]
How to use the PassRole permission with IAM roles
iam:PassRole is an AWS Identity and Access Management (IAM) permission that allows an IAM principal to delegate or pass permissions to an AWS service by configuring a resource such as an Amazon Elastic Compute Cloud (Amazon EC2) instance or AWS Lambda function with an IAM role. The service then uses that role to interact with […]
Refine permissions for externally accessible roles using IAM Access Analyzer and IAM action last accessed
When you build on Amazon Web Services (AWS) across accounts, you might use an AWS Identity and Access Management (IAM) role to allow an authenticated identity from outside your account—such as an IAM entity or a user from an external identity provider—to access the resources in your account. IAM roles have two types of policies […]
Using ACM Private Certificate Authority in a multi-account environment by using IAM roles
In this post, we show you how you can use AWS Certificate Manager (ACM) Private Certificate Authority (CA) to request or issue private certificates across a multi-account environment by using IAM roles. This solution allows you to centralize your ACM Private CA inside your AWS Organization, which reduces the complexity and the cost of having […]
Simplify granting access to your AWS resources by using tags on AWS IAM users and roles
Recently, AWS enabled tags on IAM principals (users and roles). The main benefit of this new feature is that you’ll be able to author a single policy to grant access to individual resources and you’ll no longer need to update your policies for each new resource that you add. In other words, you can now […]
Add Tags to Manage Your AWS IAM Users and Roles
We made it easier for you to manage your AWS Identity and Access Management (IAM) resources by enabling you to add tags to your IAM users and roles (also known as IAM principals). Tags enable you to add customizable key-value pairs to resources, and many AWS services support tagging of AWS resources. Now, you can […]
Enable Federated API Access to your AWS Resources for up to 12 hours Using IAM Roles
Now, your applications and federated users can complete longer running workloads in a single session by increasing the maximum session duration up to 12 hours for an IAM role. Users and applications still retrieve temporary credentials by assuming roles using AWS Security Token Service (AWS STS), but these credentials can now be valid for up […]
The Top 20 Most Viewed AWS IAM Documentation Pages in 2017
The following 20 pages were the most viewed AWS Identity and Access Management (IAM) documentation pages in 2017. I have included a brief description with each link to explain what each page covers. Use this list to see what other AWS customers have been viewing and perhaps to pique your own interest in a topic you’ve […]
Join Us for AWS IAM Day on Monday, October 9, in San Francisco
Join us in San Francisco at the AWS Pop-up Loft for AWS IAM Day on Monday, October 9, from 9:30 A.M.–4:15 P.M. Pacific Time. At this free technical event, you will learn AWS Identity and Access Management (IAM) concepts from IAM product managers, as well as tools and strategies you can use for controlling access to your AWS […]
Now Create and Manage AWS IAM Roles More Easily with the Updated IAM Console
Today, we updated the AWS Identity and Access Management (IAM) console to make it easier for you to create, manage, and understand IAM roles. We made improvements that include an updated role-creation workflow that better guides you through the process of creating trust relationships (which define who can assume a role) and attaching permissions to roles. Additionally, […]