AWS Security Blog
Tag: IAM
How to secure API Gateway HTTP endpoints with JWT authorizer
This blog post demonstrates how you can secure Amazon API Gateway HTTP endpoints with JSON web token (JWT) authorizers. Amazon API Gateway helps developers create, publish, and maintain secure APIs at any scale, helping manage thousands of API calls. There are no minimum fees, and you only pay for the API calls you receive. Based […]
Security practices in AWS multi-tenant SaaS environments
Securing software-as-a-service (SaaS) applications is a top priority for all application architects and developers. Doing so in an environment shared by multiple tenants can be even more challenging. Identity frameworks and concepts can take time to understand, and forming tenant isolation in these environments requires deep understanding of different tools and services. While security is […]
IAM Access Analyzer makes it easier to implement least privilege permissions by generating IAM policies based on access activity
In 2019, AWS Identity and Access Management (IAM) Access Analyzer was launched to help you remove unintended public and cross account access by analyzing your existing permissions. In March 2021, IAM Access Analyzer added policy validation to help you set secure and functional permissions during policy authoring. Now, IAM Access Analyzer takes that a step […]
Guidelines for protecting your AWS account while using programmatic access
One of the most important things you can do as a customer to ensure the security of your resources is to maintain careful control over who has access to them. This is especially true if any of your AWS users have programmatic access. Programmatic access allows you to invoke actions on your AWS resources either […]
How to quickly find and update your access keys, password, and MFA setting using the AWS Management Console
August 10, 2022: This blog post has been updated to reflect the new name of AWS Single Sign-On (SSO) – AWS IAM Identity Center. Read more about the name change here. You can now more quickly view and update all your security credentials from one place using the “My Security Credentials” page in the AWS […]
How to automate SAML federation to multiple AWS accounts from Microsoft Azure Active Directory
September 12, 2022: This blog post has been updated to reflect the new name of AWS Single Sign-On (SSO) – AWS IAM Identity Center. Read more about the name change here. December 2, 2019: Since the author wrote this post, AWS Single Sign On (AWS IAM Identity Center) has launched native features that simplify using […]
Automate analyzing your permissions using IAM access advisor APIs
As an administrator that grants access to AWS, you might want to enable your developers to get started with AWS quickly by granting them broad access. However, as your developers gain experience and your applications stabilize, you want to limit permissions to only what they need. To do this, access advisor will determine the permissions […]
Recovering from a rough Monday morning: An Amazon GuardDuty threat detection and remediation scenario
Amazon GuardDuty is a managed threat detection service that continuously monitors for malicious or unauthorized behavior to help you protect your AWS accounts and workloads. Given the many log types that Amazon GuardDuty analyzes (Amazon Virtual Private Cloud (VPC) Flow Logs, AWS CloudTrail, and DNS logs), you never know what it might discover in your […]
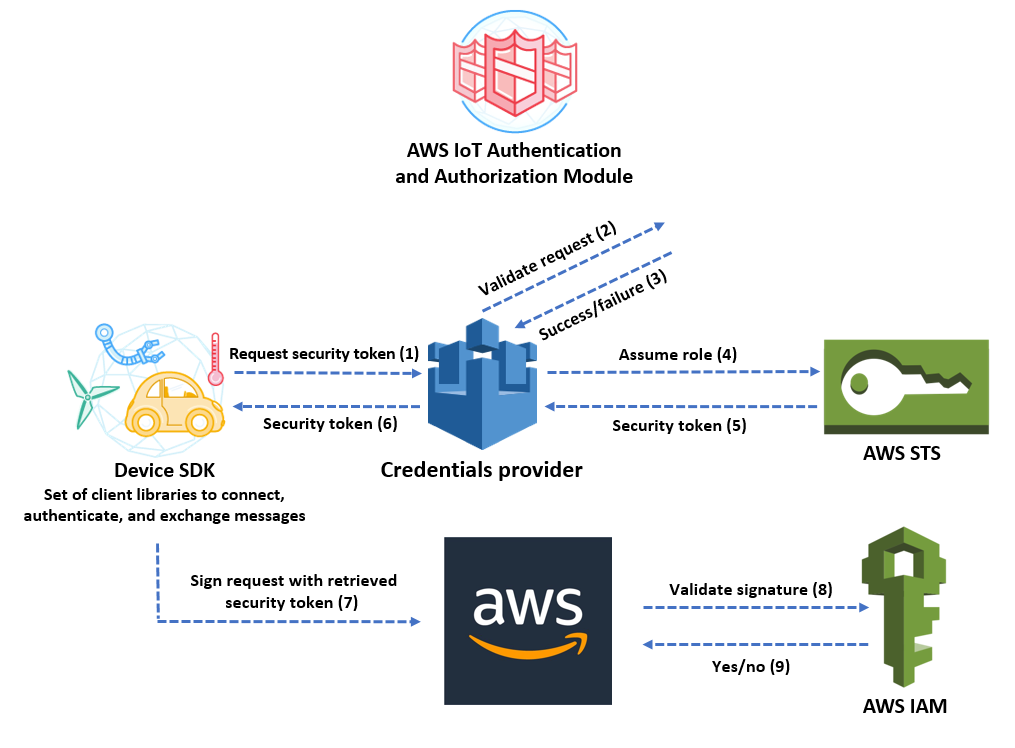
How to Eliminate the Need for Hardcoded AWS Credentials in Devices by Using the AWS IoT Credentials Provider
January 12, 2023: This post was updated to remove some instructions that are no longer needed on recent versions of Mac OSX and when run would result in an error. August 31, 2021: AWS IoT Core Credential Provider enables customers to request temporary, limited-privilege security tokens that are valid up to 12 hours and use […]
How to Use Service Control Policies in AWS Organizations
January 20, 2020: Based on customer feedback, we rephrased the fourth goal in the “An example structure with nested OUs and SCPs” section to try to improve clarity. With AWS Organizations, you can centrally manage policies across multiple AWS accounts without having to use custom scripts and manual processes. For example, you can apply service […]