AWS News Blog
New – Encryption at Rest for Amazon Aurora
|
|
Updated on February 17th, 2026 – Encryption at rest is now enabled by default for all new Aurora clusters. You can benefit from enhanced security and simplified compliance at no cost and without any configuration effort.
—
We launched Amazon Aurora a little over a year ago (see my post, Amazon Aurora – New Cost-Effective MySQL-Compatible Database Engine for Amazon RDS, to learn more). Customer adoption of Amazon Aurora has been strong and it is now the fastest-growing AWS service! We recently made Amazon Aurora available in the Asia Pacific (Tokyo) region for our customers in Japan and the surrounding area (it was already available in the US East (N. Virginia), US West (Oregon), and Europe (Ireland) regions).
Encryption at Rest
Encryption is an important part of any data protection strategy. Today we are making it easier for you to encrypt the data that you store in Amazon Aurora (this is often known as “encryption at rest”). As is the case with the other encryption options for RDS, you simply choose a key (either AWS-managed or customer-managed) from AWS Key Management Service (AWS KMS) when you create the database instance:
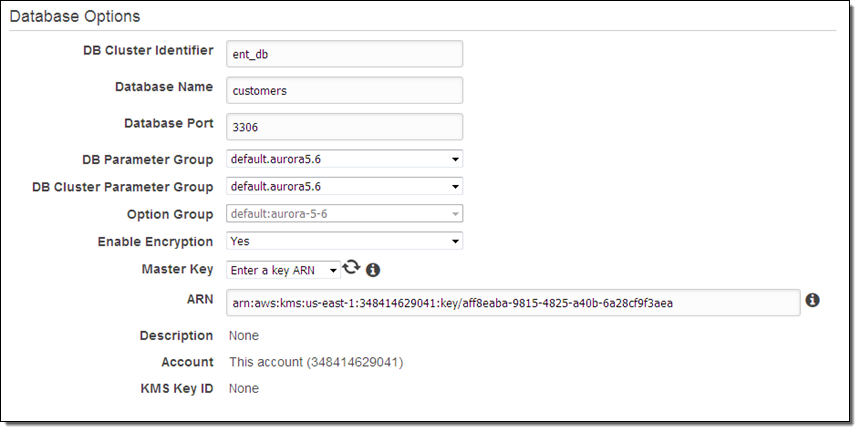
Encryption (AES-256) applies to the data in the database, logs, backups, snapshots, and read replicas. You must specify encryption when you create the database instance; you cannot enable or disable it for a running instance. Read about Encrypting Amazon RDS Resources to learn more.
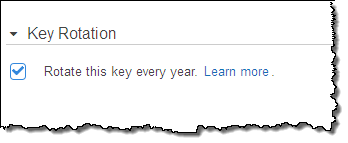
If you choose to create your own key, you can request annual rotation:
You can also enable AWS CloudTrail logging for your AWS account. This will allow you to track all of the calls made to KMS (including all Encrypt and Decrypt operations) for auditing purposes. To learn how do to this, read Logging AWS KMS API Calls Using AWS CloudTrail.
— Jeff;
PS – Before you ask, Amazon Aurora uses AES-256 to encrypt data in transit.
