AWS Marketplace
Effective cloud remediation for Security Hub findings with Tamnoon.io
Fix AWS Security Hub issues using Tamnoon’s Cloud Assisted Remediation
Overview
Customers often encounter breaches in their cloud environments due to misconfigurations and end-user errors. Gartner predicts that, through 2025, over 99 percent of cloud breaches will stem from preventable misconfigurations and end-user mistakes.
Monitoring and remediating these cloud misconfigurations and vulnerabilities is crucial for maintaining a well-secured cloud environment. In line with the shared responsibility model, customers are responsible for addressing such alerts and findings. Some of our customers have reported that 70–80 percent of security analysts’ time is consumed by triaging findings from services like AWS Security Hub , planning remediation efforts and performing the actual remediation and/or automation activities.
AWS Security Hub offers customers a unified view of their security status within Amazon Web Services (AWS), allowing them to align their environment with security standards and best practices. Once enabled, Security Hub seamlessly aggregates data from various AWS security services. For instance, it integrates intrusion detection insights from Amazon GuardDuty and results from vulnerability scans conducted by Amazon Inspector. Furthermore, it provides findings related to Amazon Simple Storage Service (Amazon S3) bucket policies from Amazon Macie, identifies publicly accessible and cross-account resources via AWS Identity and Access Management (IAM) Access Analyzer, and pinpoints resources that lack AWS WAF coverage, all managed through AWS Firewall Manager.
Tamnoon.io offers a solution that combines human expertise and AI with the goal of helping teams quickly and safely remediate cloud risks. With Tamnoon.io, SecOps and DevOps teams fix more risks in less time, while limiting the negative impact that configuration changes may cause to their environments.
In this blog post, we show you how you can efficiently scale the remediation process using Tamnoon.io, to prioritize alerts and findings, conduct impact analysis of findings, and fix misconfigurations with minimal production impact.
Prerequisites
Before getting started, following steps have been completed:
- AWS Security Hub enabled with NIST 800-53 rev 5 config conformance pack, for the all AWS accounts that will be monitored by Tamnoon.io
- Enable AWS Config rules that align with the security controls and standards monitored by AWS Security Hub.
- Subscribe to Tamnoon from AWS Marketplace
Solution overview
In this section, we show you how to onboard AWS accounts monitored by Security Hub for compliance with NIST 800-53 rev 5 and how you can remediate the related findings with Tamnoon’s Assisted Cloud Remediation solution. You can enable NIST 800-53 Rev 5 config conformance pack. Please refer to these tutorials for more details. (AWS Security Hub supports NIST SP 800-53 r5)
To take advantage of the Tamnoon platform for assisted remediation of Security Hub findings, we perform these steps –
- Click Onboard Security Hub to Tamnoon Platform
- Create IAM Role for Tamnoon to fetch Security Hub findings. Follow steps 4-13 listed here.
- Tamnoon will update the fetch policy in Tamnoon AWS account
- Tamnoon Lambda fetcher will assume the AWS Security hub fetch role in the customer environment
- Tamnoon will trigger / invoke getFindings API call in the customer security hub account
- Tamnoon load the tasks from the Tamnoon database (Internal repository)
- Customer triggers task remediation from AWS Systems Manager Agent
The following reference architecture shows the AWS services and the steps of this solution.

Figure1: Overall architecture depicting how Tamnoon integrates with AWS security Hub to remediate findings
Solution walkthrough: Fix Security Hub issues with minimal production impact using Tamnoon’s Assisted Cloud Remediation
Tamnoon automates the remediation of unencrypted Amazon Elastic Block Store (Amazon EBS) volumes. This critical function aids in fulfilling the NIST 800-53 requirement for data-at-rest encryption. Specifically, it addresses the EC2.3 control in NIST 800-53 rev 5 requirements, monitored by Security Hub, which mandates the encryption of attached Amazon EBS volumes at rest.
Related NIST800-53 rev 5 requirements are: CA-9(1),CM-3(6), SC-13, SC-28, SC-28(1), SC-7(10), and SI-7(6).
The following diagram shows a high level Tamnoon’s Assisted Cloud Remediation process.

Figure 2: Tamnoon Assisted Cloud Remediation Process
To address security issues, the first step is to set up monitoring using cloud-native tools like AWS Security Hub and Amazon GuardDuty, or third-party cloud security solutions. Once issues are detected, follow a robust process to fix them promptly. Key recommended steps for a remediation process include:
1. Prioritization and ongoing assessment
Upon identifying a security issue in AWS, the initial step is to prioritize or triage the issue. This process involves evaluating various factors such as the location of the issue, the sensitivity of the data involved, the organization’s prioritization criteria for different types of problems, and the ownership of the affected assets. Assessing these elements is crucial in determining the urgency and sequence for addressing each identified security issue in AWS.
Consider this scenario: Security Hub has flagged a list of unencrypted EBS volumes.
Encrypting Amazon EBS volumes is a crucial measure, adding a robust layer of data protection by safeguarding information against unauthorized access to the underlying storage. To effectively manage this, create a task in Tamnoon to prioritize these volumes. This prioritization is based on a thorough analysis incorporating factors such as asset classification, ownership, identification of critical assets (crown jewels), and a risk assessment of the alerts. This analysis is efficiently executed by the Tamnoon Prioritization Engine, ensuring a focused and strategic approach to enhancing your AWS security posture.
Tamnoon Remediation Tasks –
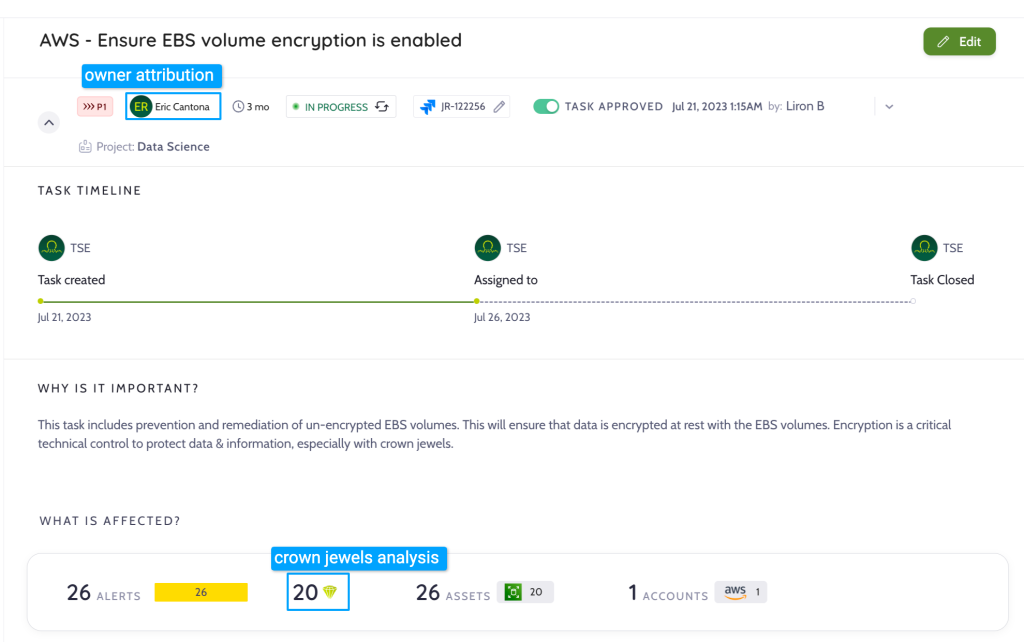
Figure 3: Remediation Task in Tamnoon
List of prioritized alerts of unencrypted Volumes included and assigned to the task – using Tamnoon’s proprietary Human-Centric AI prioritization process

Figure 4: List of AWS Security Hub Alerts – included in Tamnoon Task
2. Remediation impact analysis
After security issues have been identified and evaluated, the next step is to create a detailed plan to address them. An important part of this process is performing a comprehensive analysis of how remediating the issues will impact the environment. Investigation playbooks can greatly improve efficiency when analyzing large systems and log files to determine potential problems from remediating an alert.
In this phase, we analyze and build an execution plan based on the operational impact:
- Check if the EBS volume is attached to any EC2 instances. If it is not attached, proceed to the next step.
- Verify the EBS volume is not referenced or in-use by any critical services or applications. Look at tags, volume name, and other identifiers to determine if the volume is still required.
- Check if the EBS volume is part of an Auto Scaling group or referenced in a launch configuration/template. Deleting volumes that are part of Auto Scaling groups can cause issues.
- If the EBS volume is detached, not referenced anywhere, and not part of an Auto Scaling group, it is likely safe to delete.
- Before deleting, you may want to create a snapshot as a backup in case the volume is needed later.
Tamnoon builds a well-defined execution plan that addresses each scenario by performing logs analysis AI based investigation that is curated by CloudPro expert
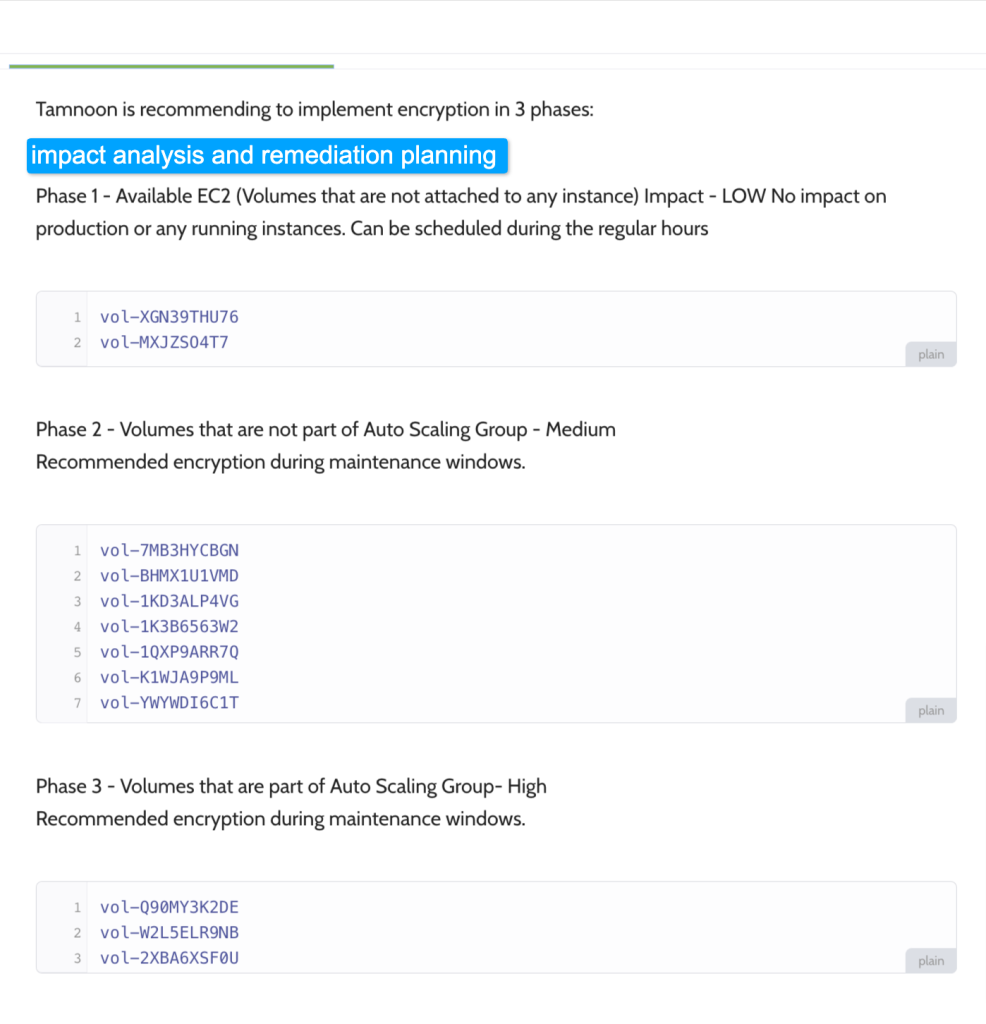
Figure 5: List of volumes and impact investigation results as part of Tamnoon task
3. Execution and remediation
The execution phase puts your plan into action. Automation playbooks from Tamnoon can streamline this process and accelerate resolving any problems.
The EBS volume encryption playbook outlines automatically remediating unencrypted EBS volumes. Encrypting EBS volumes adds another layer of data protection by safeguarding your data from unauthorized access to the underlying storage. You can leverage Amazon EBS encryption to boost data security for your cloud-deployed applications and meet encryption-at-rest compliance requirements.
Refer to Tamnoon’s Public Playbooks repository to learn more about EBS volume encryption and the remediation workflow. To learn more about EBS volume encryption and the remediation process, refer to the Tamnoon Public Playbooks repository.
4. Preventive measures
While resolving current security vulnerabilities is crucial, taking proactive steps to prevent future incidents is equally important. If team members continue deploying misconfigured resources, you will face the same problems repeatedly. To prevent this, it’s vital to establish ongoing prevention processes leveraging AWS’s native security controls and automation playbooks.
Tamnoon’s service automatically enables encryption for Amazon EBS volumes across all Regions and accounts. This means whenever a new EC2 instance launches in an enabled account, the EBS volume created for that instance will encrypt by default. This prevents unencrypted volumes from being created inadvertently.

Figure 6: Prevention for unencrypted EBS volumes – script for execution
Cleanup
As part of EBS volume encryption process and investigation that Tamnoon will perform for all the volumes – as a side effect we will be identifying all the volumes that are not attached to instances as well as respective snapshots. As part of this effort, several resources can be deleted from the account to reduce unnecessary spend. To avoid unwanted charges in your AWS and Tamnoon account, clean up the resources created in this demonstration. You can stop or delete the AWS security Hub
Conclusion
In this blog post, we explore the integration of Tamnoon with AWS Security Hub, illustrating a streamlined approach to structured remediation. This integration facilitates a comprehensive process, including prioritization, impact analysis, execution, and prevention, empowering Security Analysts to efficiently concentrate on the most critical security issues.
To find out more about Tamnoon products, visit AWS Marketplace. To learn more about EBS volume encryption and the remediation process, refer to the Tamnoon Public Playbooks repository.