AWS Compute Blog
Category: Security, Identity, & Compliance
Getting Started with AWS Nitro Enclaves on Microsoft Windows
This post is written by Scott Malkie, Specialist Solutions Architect, EC2 AWS Nitro Enclaves, introduced in October 2020, are isolated compute environments. They leverage the power of the AWS Nitro System to provide isolation and attestation for sensitive data processing. Customers use Nitro Enclaves to isolate their data processing workloads, even from users with root […]
Evaluating access control methods to secure Amazon API Gateway APIs
This post is written by Bryant Bost, Cloud Application Architect. There is not a one-size-fits-all approach to access control for Amazon API Gateway. Properties of your application such as API type, identity provider, client access patterns, privacy requirements, and others influence the design of your access control solution. Understanding the types of access control available […]
Building an image searching solution with the AWS CDK
This post discusses a fully serverless architecture for searching images based on their contents. It shows how this architecture is decoupled and stateless by using S3 events, SQS messages, an EventBridge bus, and Amazon Aurora Serverless.
Operating Lambda: Building a solid security foundation – Part 1
This post explains the Lambda execution environment and how the service protects customer data. It covers important steps you should take to prevent data leakage between invocations and provides additional security resources to review.
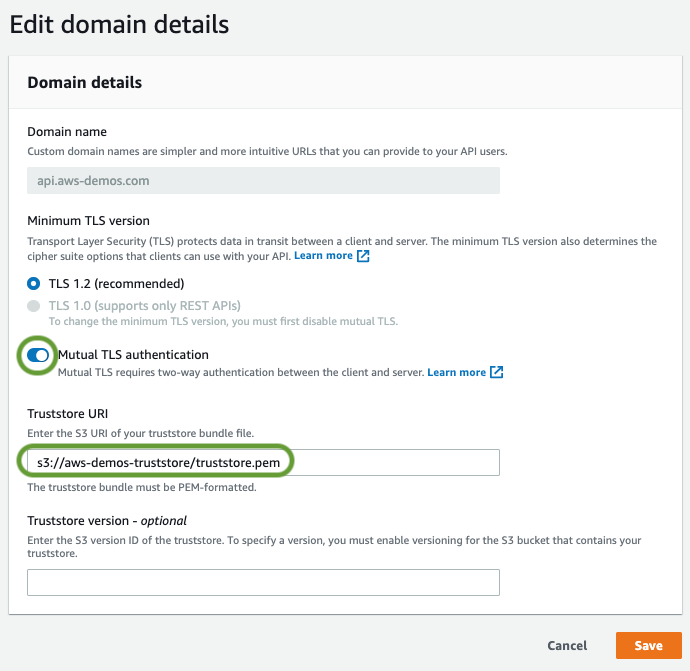
Automating mutual TLS setup for Amazon API Gateway
Mutual TLS (mTLS) for API Gateway is now generally available at no additional cost. This post shows how to automate mutual TLS for Amazon API Gateway HTTP APIs using the AWS Certificate Manager Private Certificate Authority as a private CA. Using infrastructure as code (IaC) enables you to develop, deploy, and scale cloud applications, often with greater speed, less risk, and reduced cost.
Creating a cross-region Active Directory domain with AWS Launch Wizard for Microsoft Active Directory
AWS Launch Wizard is a console-based service to quickly and easily size, configure, and deploy third party applications, such as Microsoft SQL Server Always On and HANA based SAP systems, on AWS without the need to identify and provision individual AWS resources. AWS Launch Wizard offers an easy way to deploy enterprise applications and optimize […]
Introducing IAM and Lambda authorizers for Amazon API Gateway HTTP APIs
Amazon API Gateway HTTP APIs enable you to create RESTful APIs with lower latency and lower cost than API Gateway REST APIs. The API Gateway team is continuing work to improve and migrate popular REST API features to HTTP APIs. We are adding two of the most requested features, AWS Identity and Access Management (IAM) […]
Introducing mutual TLS authentication for Amazon API Gateway
Mutual TLS (mTLS) for API Gateway is generally available today at no additional cost. It’s available in all AWS commercial Regions, AWS GovCloud (US) Regions, and China Regions. It supports configuration via the API Gateway console, AWS CLI, SDKs, and AWS CloudFormation.
Troubleshooting Amazon API Gateway with enhanced observability variables
Amazon API Gateway is often used for managing access to serverless applications. Additionally, it can help developers reduce code and increase security with features like AWS WAF integration and authorizers at the API level. Because more is handled by API Gateway, developers tell us they would like to see more data points on the individual […]
Building a serverless document scanner using Amazon Textract and AWS Amplify
This guide demonstrates creating and deploying a production ready document scanning application. It allows users to manage projects, upload images, and generate a PDF from detected text. The sample can be used as a template for building expense tracking applications, handling forms and legal documents, or for digitizing books and notes. The frontend application is […]