AWS Compute Blog
Serverless Automated Cost Controls, Part1
This post courtesy of Shankar Ramachandran, Pubali Sen, and George Mao
In line with AWS’s continual efforts to reduce costs for customers, this series focuses on how customers can build serverless automated cost controls. This post provides an architecture blueprint and a sample implementation to prevent budget overruns.
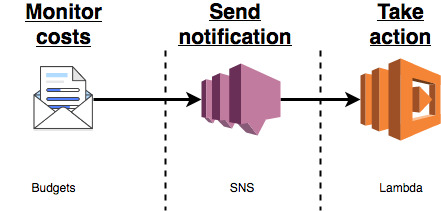
This solution uses the following AWS products:
- AWS Budgets – An AWS Cost Management tool that helps customers define and track budgets for AWS costs, and forecast for up to three months.
- Amazon SNS – An AWS service that makes it easy to set up, operate, and send notifications from the cloud.
- AWS Lambda – An AWS service that lets you run code without provisioning or managing servers.
You can fine-tune a budget for various parameters, for example filtering by service or tag. The Budgets tool lets you post notifications on an SNS topic. A Lambda function that subscribes to the SNS topic can act on the notification. Any programmatically implementable action can be taken.
The diagram below describes the architecture blueprint.
In this post, we describe how to use this blueprint with AWS Step Functions and IAM to effectively revoke the ability of a user to start new Amazon EC2 instances, after a budget amount is exceeded.
Freedom with guardrails
AWS lets you quickly spin up resources as you need them, deploying hundreds or even thousands of servers in minutes. This means you can quickly develop and roll out new applications. Teams can experiment and innovate more quickly and frequently. If an experiment fails, you can always de-provision those servers without risk.
This improved agility also brings in the need for effective cost controls. Your Finance and Accounting department must budget, monitor, and control the AWS spend. For example, this could be a budget per project. Further, Finance and Accounting must take appropriate actions if the budget for the project has been exceeded, for example. Call it “freedom with guardrails” – where Finance wants to give developers freedom, but with financial constraints.
Architecture
This section describes how to use the blueprint introduced earlier to implement a “freedom with guardrails” solution.
- The budget for “Project Beta” is set up in Budgets. In this example, we focus on EC2 usage and identify the instances that belong to this project by filtering on the tag Project with the value Beta. For more information, see Creating a Budget.
- The budget configuration also includes settings to send a notification on an SNS topic when the usage exceeds 100% of the budgeted amount. For more information, see Creating an Amazon SNS Topic for Budget Notifications.
- The master Lambda function receives the SNS notification.
- It triggers execution of a Step Functions state machine with the parameters for completing the configured action.
- The action Lambda function is triggered as a task in the state machine. The function interacts with IAM to effectively remove the user’s permissions to create an EC2 instance.
This decoupled modular design allows for extensibility. New actions (serially or in parallel) can be added by simply adding new steps.
Implementing the solution
All the instructions and code needed to implement the architecture have been posted on the Serverless Automated Cost Controls GitHub repo. We recommend that you try this first in a Dev/Test environment.
This implementation description can be broken down into two parts:
- Create a solution stack for serverless automated cost controls.
- Verify the solution by testing the EC2 fleet.
To tie this back to the “freedom with guardrails” scenario, the Finance department performs a one-time implementation of the solution stack. To simulate resources for Project Beta, the developers spin up the test EC2 fleet.
Prerequisites
There are two prerequisites:
- Make sure that you have the necessary IAM permissions. For more information, see the section titled “Required IAM permissions” in the README.
- Define and activate a cost allocation tag with the key Project. For more information, see Using Cost Allocation Tags. It can take up to 12 hours for the tags to propagate to Budgets.
Create resources
The solution stack includes creating the following resources:
- Three Lambda functions
- One Step Functions state machine
- One SNS topic
- One IAM group
- One IAM user
- IAM policies as needed
- One budget
Two of the Lambda functions were described in the previous section, to a) receive the SNS notification and b) trigger the Step Functions state machine. Another Lambda function is used to create the budget, as a custom AWS CloudFormation resource. The SNS topic connects Budgets with Lambda function A. Lambda function B is configured as a task in Step Functions. A budget for $2 is created which is filtered by Service: EC2 and Tag: Project, Beta. A test IAM group and user is created to enable you to validate this Cost Control Solution.
To create the serverless automated cost control solution stack, choose the button below. It takes few minutes to spin up the stack. You can monitor the progress in the CloudFormation console.
When you see the CREATE_COMPLETE status for the stack you had created, choose Outputs. Copy the following four values that you need later:
- TemplateURL
- UserName
- SignInURL
- Password
Verify the stack
The next step is to verify the serverless automated cost controls solution stack that you just created. To do this, spin up an EC2 fleet of t2.micro instances, representative of the resources needed for Project Beta, and tag them with Project, Beta.
- Browse to the SignInURL, and log in using the UserName and Password values copied on from the stack output.
- In the CloudFormation console, choose Create Stack.
- For Choose a template, select Choose an Amazon S3 template URL and paste the TemplateURL value from the preceding section. Choose Next.
- Give this stack a name, such as “testEc2FleetForProjectBeta”. Choose Next.
- On the Specify Details page, enter parameters such as the UserName and Password copied in the previous section. Choose Next.
- Ignore any errors related to listing IAM roles. The test user has a minimal set of permissions that is just sufficient to spin up this test stack (in line with security best practices).
- On the Options page, choose Next.
- On the Review page, choose Create. It takes a few minutes to spin up the stack, and you can monitor the progress in the CloudFormation console.
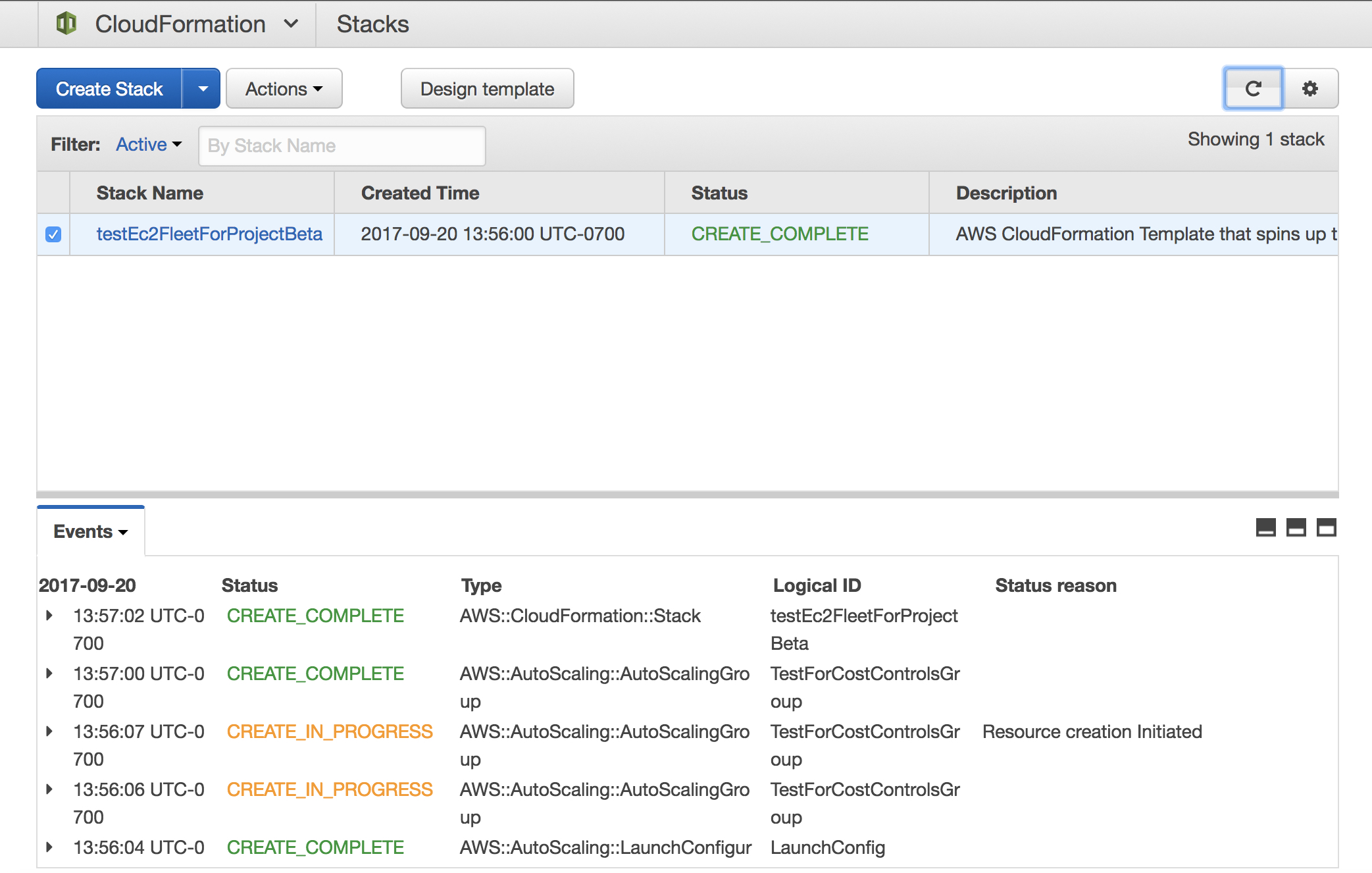
- When you see the status “CREATE_COMPLETE”, open the EC2 console to verify that four t2.micro instances have been spun up, with the tag of Project, Beta.
The hourly cost for these instances depends on the region in which they are running. On the average (irrespective of the region), you can expect the aggregate cost for this EC2 fleet to exceed the set $2 budget in 48 hours.
Verify the solution
The first step is to identify the test IAM group that was created in the previous section. The group should have “projectBeta” in the name, prepended with the CloudFormation stack name and appended with an alphanumeric string. Verify that the managed policy associated is: “EC2FullAccess”, which indicates that the users in this group have unrestricted access to EC2.
There are two stages of verification for this serverless automated cost controls solution: simulating a notification and waiting for a breach.
Simulated notification
Because it takes at least a few hours for the aggregate cost of the EC2 fleet to breach the set budget, you can verify the solution by simulating the notification from Budgets.
- Log in to the SNS console (using your regular AWS credentials).
- Publish a message on the SNS topic that has “budgetNotificationTopic” in the name. The complete name is appended by the CloudFormation stack identifier.

- Copy the following text as the body of the notification: “This is a mock notification”.
- Choose Publish.
- Open the IAM console to verify that the policy for the test group has been switched to “EC2ReadOnly”. This prevents users in this group from creating new instances.
- Verify that the test user created in the previous section cannot spin up new EC2 instances. You can log in as the test user and try creating a new EC2 instance (via the same CloudFormation stack or the EC2 console). You should get an error message indicating that you do not have the necessary permissions.
- If you are proceeding to stage 2 of the verification, then you must switch the permissions back to “EC2FullAccess” for the test group, which can be done in the IAM console.
Automatic notification
Within 48 hours, the aggregate cost of the EC2 fleet spun up in the earlier section breaches the budget rule and triggers an automatic notification. This results in the permissions getting switched out, just as in the simulated notification.
Clean up
Use the following steps to delete your resources and stop incurring costs.
- Open the CloudFormation console.
- Delete the EC2 fleet by deleting the appropriate stack (for example, delete the stack named “testEc2FleetForProjectBeta”).

- Next, delete the “costControlStack” stack.

Conclusion
Using Lambda in tandem with Budgets, you can build Serverless automated cost controls on AWS. Find all the resources (instructions, code) for implementing the solution discussed in this post on the Serverless Automated Cost Controls GitHub repo.
Stay tuned to this series for more tips about building serverless automated cost controls. In the next post, we discuss using smart lighting to influence developer behavior and describe a solution to encourage cost-aware development practices.
If you have questions or suggestions, please comment below.