AWS Compute Blog
Using Amazon MQ as an event source for AWS Lambda
This blog is about using ActiveMQ brokers as an event source. For information on using RabbitMQ brokers, read Using Amazon MQ for RabbitMQ as an event source for Lambda.
Amazon MQ is a managed, highly available message broker for Apache ActiveMQ. The service manages the provisioning, setup, and maintenance of ActiveMQ. Now, with Amazon MQ as an event source for AWS Lambda, you can process messages from the service. This allows you to integrate Amazon MQ with downstream serverless workflows.
ActiveMQ is a popular open source message broker that uses open standard APIs and protocols. You can move from any message broker that uses these standards to Amazon MQ. With Amazon MQ, you can deploy production-ready broker configurations in minutes, and migrate existing messaging services to the AWS Cloud. Often, this does not require you to rewrite any code, and in many cases you only need to update the application endpoints.
In this blog post, I explain how to set up an Amazon MQ broker and networking configuration. I also show how to create a Lambda function that is invoked by messages from Amazon MQ queues.
Overview
Using Amazon MQ as an event source operates in a similar way to using Amazon SQS or Amazon Kinesis. In all cases, the Lambda service internally polls for new records or messages from the event source, and then synchronously invokes the target Lambda function. Lambda reads the messages in batches and provides these to your function as an event payload.
Lambda is a consumer application for your Amazon MQ queue. It processes records from one or more partitions and sends the payload to the target function. Lambda continues to process batches until there are no more messages in the topic.
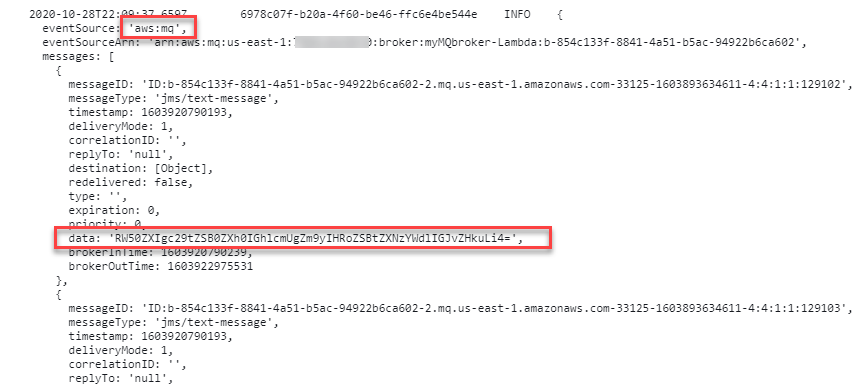
The Lambda function’s event payload contains an array of records in the messages attribute. Each array item contains envelope details of the message, together with the base64 encoded message in the data attribute:
How to configure Amazon MQ as an event source for Lambda
Amazon MQ is a highly available service, so it must be configured to run in a minimum of two Availability Zones in your preferred Region. You can also run a single broker in one Availability Zone for development and test purposes. In this walk through, I show how to run a production, public broker and then configure an event source mapping for a Lambda function.
There are four steps:
- Configure the Amazon MQ broker and security group.
- Create a queue on the broker.
- Set up AWS Secrets Manager.
- Build the Lambda function and associated permissions.
Configuring the Amazon MQ broker and security group
In this step, you create an Amazon MQ broker and then configure the broker’s security group to allow inbound access on ports 8162 and 61617.
- Navigate to the Amazon MQ console and choose Create brokers.
- In Step 1, keep the defaults and choose Next.
- In Configure settings, in the ActiveMQ Access panel, enter a user name and password for broker access.

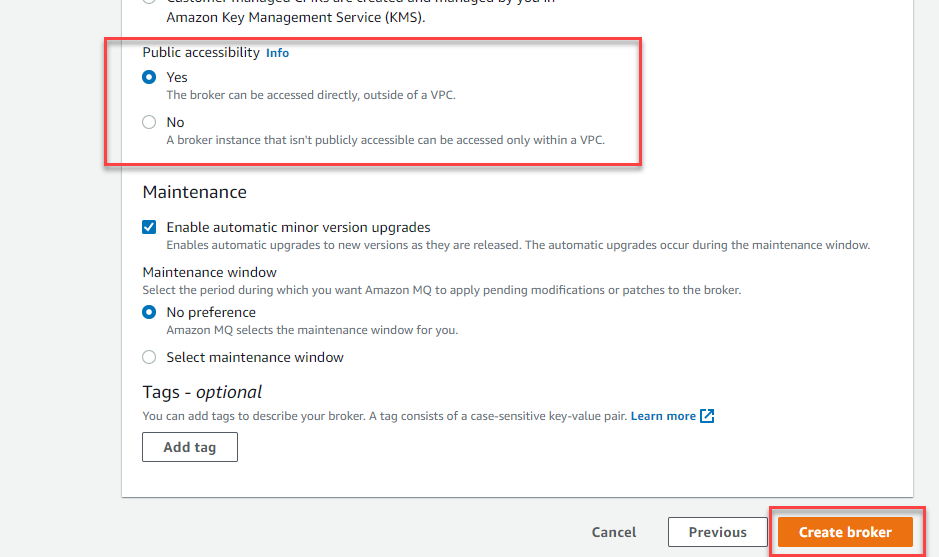
- Expand the Additional settings panel, keep the defaults, and ensure that Public accessibility is set to Yes. Choose Create broker.
- The creation process takes up to 15 minutes. From the Brokers list, select the broker name. In the Details panel, choose the Security group.

- On the Inbound rules tab, choose Edit inbound rules. Add rules to enable inbound TCP traffic on ports 61617 and 8162:

- Port 8162 is used to access the ActiveMQ Web Console to configure the broker settings.
- Port 61617 is used by the internal Lambda poller to connect with your broker, using the OpenWire endpoint. Note that the Lambda poller uses the same network configuration of the broker.
Create a queue on the broker
The Lambda service subscribes to a queue on the broker. In this step, you create a new queue:
- Navigate to the Amazon MQ console and choose the newly created broker. In the Connections panel, locate the URLs for the web console.
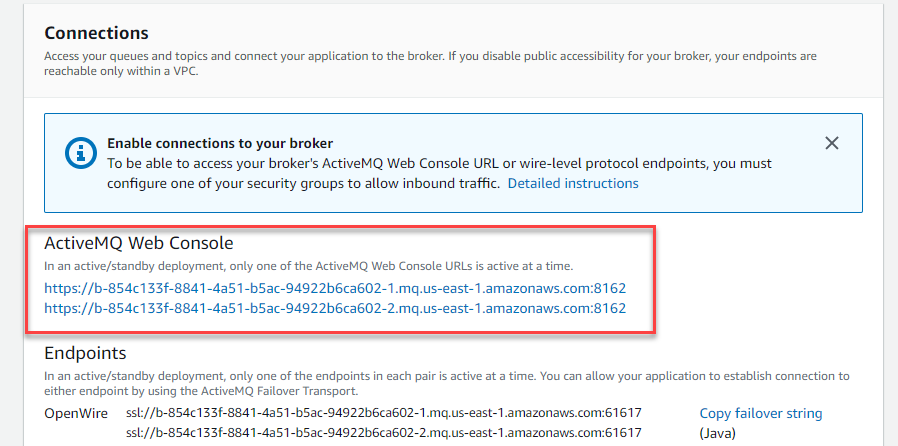
- Only one endpoint is active at a time. Select both and one resolves to the ActiveMQ Web Console application. Enter the user name and password that you configured earlier.

- In the top menu, select Queues. For Queue Name, enter myQueue and choose Create. The new queue appears in the Queues list.

Keep this webpage open, since you use this later for sending messages to the Lambda function.
Set up Secrets Manager
The Lambda service needs access to your Amazon MQ broker, using the user name and password you configured earlier. To avoid exposing secrets in plaintext in the Lambda function, it’s best practice to use a service like Secrets Manager. To create a secret, use the create-secret AWS CLI command. To do this, ensure you have the AWS CLI installed.
From a terminal window, enter this command, replacing the user name and password with your own values:
aws secretsmanager create-secret --name MQaccess --secret-string '{"username": "your-username", "password": "your-password"}'The command responds with the ARN of the stored secret:
Build the Lambda function and associated permissions
The Lambda function must have permission to access the Amazon MQ broker and stored secret. It must also be able to describe VPCs and security groups, and manage elastic network interfaces. These execution roles permissions are:
- mq:DescribeBroker
- secretsmanager:GetSecretValue
- ec2:CreateNetworkInterface
- ec2:DescribeNetworkInterfaces
- ec2:DescribeVpcs
- ec2:DeleteNetworkInterface
- ec2:DescribeSubnets
- ec2:DescribeSecurityGroups
If you are using an encrypted customer managed key, you must also add the kms:Decrypt permission.
To set up the Lambda function:
- Navigate to the Lambda console and choose Create Function.
- For function name, enter MQconsumer and choose Create Function.
- In the Permissions tab, choose the execution role to edit the permissions.

- Choose Attach policies then choose Create policy.
- Select the JSON tab and paste the following policy. Choose Review policy.
{ "Version": "2012-10-17", "Statement": [ { "Effect": "Allow", "Action": [ "mq:DescribeBroker", "secretsmanager:GetSecretValue", "ec2:CreateNetworkInterface", "ec2:DescribeNetworkInterfaces", "ec2:DescribeVpcs", "ec2:DeleteNetworkInterface", "ec2:DescribeSubnets", "ec2:DescribeSecurityGroups", "logs:CreateLogGroup", "logs:CreateLogStream", "logs:PutLogEvents" ], "Resource": "*" } ] } - For name, enter ‘AWSLambdaMQExecutionRole’. Choose Create policy.
- In the IAM Summary panel, choose Attach policies. Search for AWSLambdaMQExecutionRole and choose Attach policy.

- On the Lambda function page, in the Designer panel, choose Add trigger. Select MQ from the drop-down. Choose the broker name, enter ‘myQueue’ for Queue name, and choose the secret ARN. Choose Add.

- The status of the Amazon MQ trigger changes from Creating to Enabled after a couple of minutes. The trigger configuration confirms the settings.

Testing the event source mapping
- In the ActiveMQ Web Console, choose Active consumers to confirm that the Lambda service has been configured to consume events.

- In the main dashboard, choose Send To on the queue. For Number of messages to send, enter 10 and keep the other defaults. Enter a test message then choose Send.

- In the MQconsumer Lambda function, select the Monitoring tab and then choose View logs in CloudWatch. The log streams show that the Lambda function has been invoked by Amazon MQ.

A single Lambda function consumes messages from a single queue in an Amazon MQ broker. You control the rate of message processing using the Batch size property in the event source mapping. The Lambda service limits the concurrency to one execution environment per queue.
For example, in a queue with 100,000 messages and a batch size of 100 and function duration of 2000 ms, the Monitoring tab shows this behavior. The Concurrent executions graph remains at 1 as the internal Lambda poller fetches messages. It continues to invoke the Lambda function until the queue is empty.
Using AWS SAM
In AWS SAM templates, you can configure a Lambda function with an Amazon MQ event source mapping and the necessary permissions. For example:
Resources:
ProcessMSKfunction:
Type: AWS::Serverless::Function
Properties:
CodeUri: code/
Timeout: 3
Handler: app.lambdaHandler
Runtime: nodejs12.x
Events:
MQEvent:
Type: MQ
Properties:
Broker:
Fn::GetAtt: MyMqBroker.Arn
Queues:
- "MyQueue"
SourceAccessConfigurations:
- Type: BASIC_AUTH
URI:
Ref: MQBrokerUserSecret
Policies:
- Statement:
- Effect: Allow
Resource: '*'
Action:
- mq:DescribeBroker
- secretsmanager:GetSecretValue
- ec2:CreateNetworkInterface
- ec2:DescribeNetworkInterfaces
- ec2:DescribeVpcs
- ec2:DeleteNetworkInterface
- ec2:DescribeSubnets
- ec2:DescribeSecurityGroups
- logs:CreateLogGroup
- logs:CreateLogStream
- logs:PutLogEvents
Conclusion
Amazon MQ provide a fully managed, highly available message broker service for Apache ActiveMQ. Now Lambda supports Amazon MQ as an event source, you can invoke Lambda functions from messages in Amazon MQ queues to integrate into your downstream serverless workflows.
In this post, I give an overview of how to set up an Amazon MQ broker. I show how to configure the networking and create the event source mapping with Lambda. I also show how to set up a consumer Lambda function in the AWS Management Console, and refer to the equivalent AWS SAM syntax to simplify deployment.
To learn more about how to use this feature, read the documentation. For more serverless learning resources, visit https://serverlessland.com.