Containers
Category: Security, Identity, & Compliance
A quick path to Amazon EKS single sign-on using AWS SSO
With the rapid growth of software as a service (SaaS) and cloud adoption, identity is the new security perimeter. AWS Identity and Access Management (IAM) and Kubernetes role-based access control (RBAC) provide the tools to build a strong least-privilege security posture. Single sign-on (SSO) uses federation with a central identity provider (IdP) to improve security by allowing […]
Using IAM database authentication with workloads running on Amazon EKS
Amazon Elastic Kubernetes Service (Amazon EKS) is a managed service that you can use to run Kubernetes on AWS without needing to install, operate, and maintain your own Kubernetes control plane or nodes. When running containerized workloads on Amazon EKS, it is common to store the stateful parts of the application outside of the Kubernetes […]
Container scanning updates in Amazon ECR private registries using Amazon Inspector
We announced a new Amazon Inspector last week at re:Invent 2021 with improved vulnerability management for cloud workloads. Amazon Inspector is a service used by organizations of all sizes to automate security assessment and management at scale. For Amazon Elastic Container Registry (Amazon ECR) private registry customers, this announcement brings updates, enhancements, and integrations to […]
How to use Application Load Balancer and Amazon Cognito to authenticate users for your Kubernetes web apps
This post describes how to use Amazon Cognito to authenticate users for web apps running in an Amazon Elastic Kubernetes Services (Amazon EKS) cluster. Behind any identity management system resides a complex network of systems meant to keep data and services secure. These systems handle functions such as directory services, access management, identity authentication, and […]
Managing ROSA subscriptions at scale
One aspect of operating applications at scale is managing software in a manner that provides control as well as caters for self service and agility. As the modernization of applications and overall business processes takes place, agility requirements drive the need for teams to have access to the tools they require. How does a large-scale […]
Automating image compliance for Amazon ECS and Amazon EKS using Amazon Elastic Container Registry (ECR) and AWS Security Hub
Introduction As containers move to cloud native production environments, DevOps and security teams increasingly look to deploy DevSecOps pipelines that provide automated real-time visibility into container activity, restrict container access to host and network resources and detect and prevent exploits and attacks on running containers. In this blog post, we implement a solution that demonstrates […]
Authenticating with Docker Hub for AWS Container Services
Docker Hub has recently updated its terms of service to introduce rate limits for container image pulls. While these limits don’t apply to accounts under a Pro or Team plan, anonymous users are limited to 100 pulls per 6 hours per IP address, and authenticated free accounts are limited to 200 pulls per 6 hours. […]
Results of the 2020 AWS Container Security Survey
In 2019 we carried out the first AWS Container Security Survey and now we have the results of this year’s survey for you available. As in 2019, we conducted an anonymous survey throughout 2020 amongst container users on AWS. From the 655 people who visited the survey, 295 started it and 156 completed it (completion […]
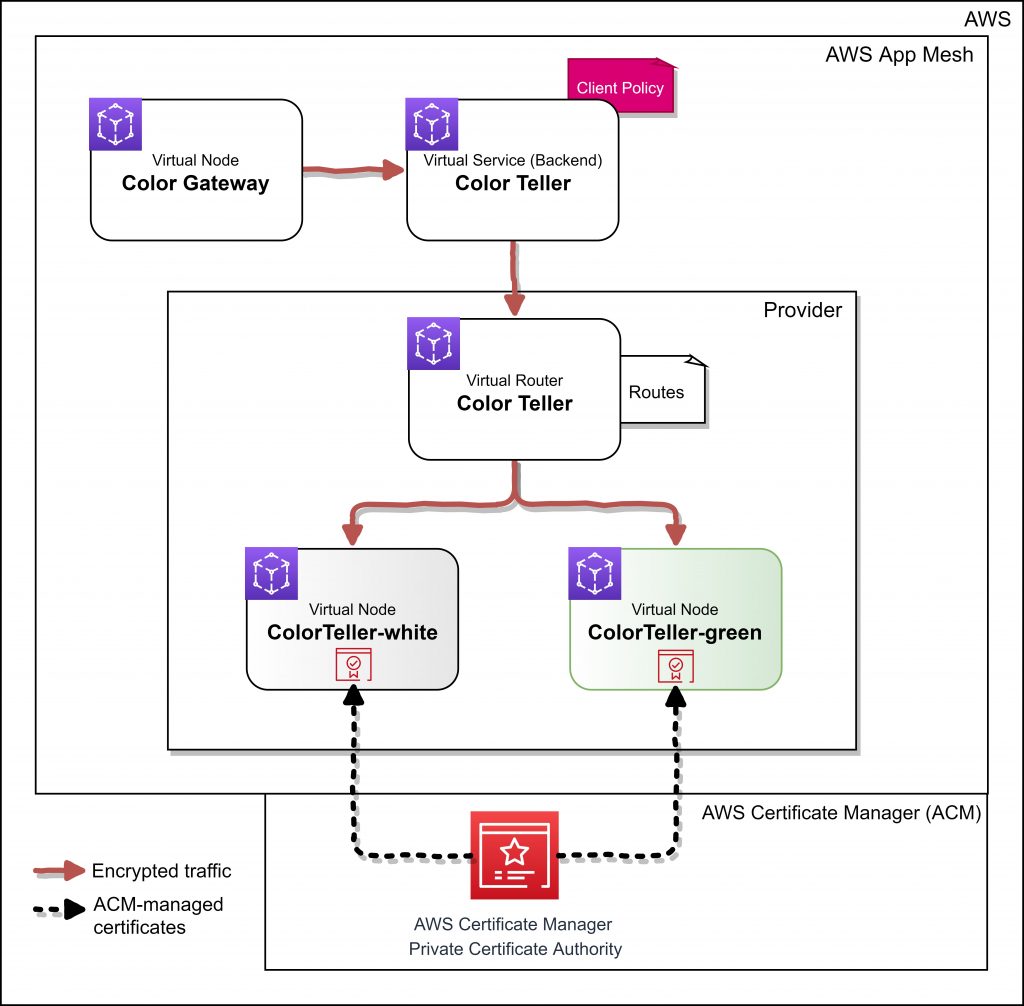
Enable traffic encryption between services in AWS App Mesh using AWS Certificate Manager or customer-provided certificates
NOTICE: October 04, 2024 – This post no longer reflects the best guidance for configuring a service mesh with Amazon ECS and Amazon EKS, and its examples no longer work as shown. For workloads running on Amazon ECS, please refer to newer content on Amazon ECS Service Connect, and for workloads running on Amazon EKS, […]
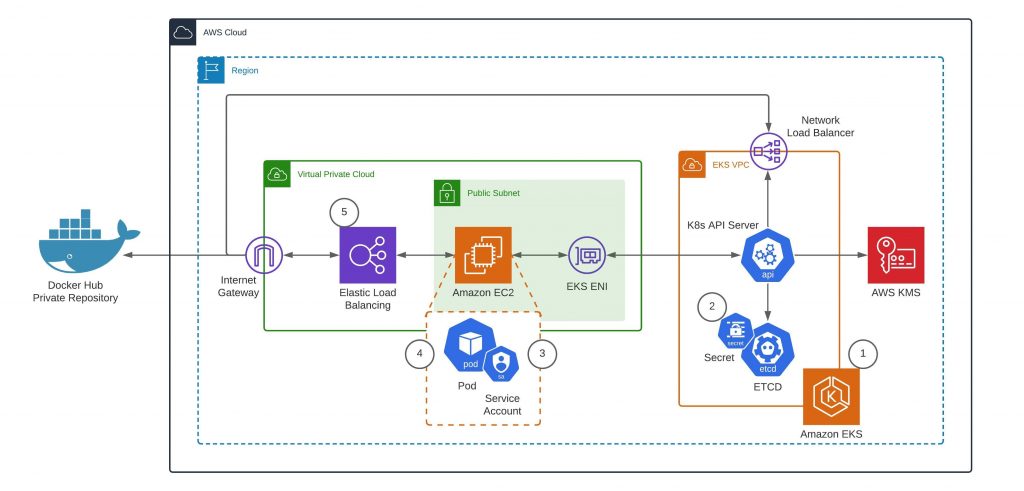
Using EKS encryption provider support for defense-in-depth
Gyuho Lee, Rashmi Dwaraka, and Michael Hausenblas When we announced that we plan to natively support the AWS Encryption Provider in Amazon EKS, the feedback we got from you was pretty clear: can we have it yesterday? Now we’re launching EKS support for the encryption provider, a vital defense-in-depth security feature. That is, you can […]