Desktop and Application Streaming
Integrating Microsoft Azure MFA Server with Amazon WorkSpaces
Important note: Microsoft Azure MFA Server has been a popular Multi-Factor Authentication(MFA) solution. If you are still using Azure MFA Server, this blog post provides instructions on integrating it with WorkSpaces. As of July 1, 2019, Microsoft no longer offers MFA Server for new deployments. Azure Multi-Factor Authentication customers must deploy a Network Policy Server (NPS) to enable multi-factor authentication for Amazon WorkSpaces with Azure AD. Depending on the types of Tokens in use, the configuration for NPS and your AWS Directory may differ. To configure Azure MFA and Microsoft Network Policy Service for multi-factor authentication with Amazon WorkSpaces, read Use Azure MFA and Microsoft Network Policy Server (NPS) for multi-factor authentication with Amazon WorkSpaces on the AWS Desktop and Application Streaming blog.
Overview
Amazon WorkSpaces is a managed, secure cloud desktop service. You can use Amazon WorkSpaces to provision Windows and Linux desktops in just a few minutes and quickly scale to provide thousands of desktops to workers across the globe.
Multifactor Authentication (MFA) is a security system that requires more than one method of authentication from independent categories of credentials to verify the user’s identity for a login or other transaction. Microsoft Azure MFA Server is a popular MFA solution and this Blog Post provides instructions on integrating it with WorkSpaces. This post will setup Phone Call factor authentication for use with WorkSpaces.
Prerequisites
The solution utilizes one or more MFA Servers which proxies MFA credentials between an AWS Directory Service and Azure MFA service. The Microsoft Azure Multi-Factor Authentication Server software should be installed on a domain-joined Windows Server. The software setup should be performed by a Domain Administrator or Enterprise Administrator in order to allow registration with Active Directory.
Instructions for downloading and installing the Azure MFA server software can be found at https://docs.microsoft.com/en-us/azure/active-directory/authentication/howto-mfaserver-deploy
In this post, we will deploy the Microsoft MFA Server software on an Amazon Elastic Compute Cloud (EC2) instance in an AWS Virtual Private Cloud (VPC). Note the hardware and software compatibility requirements in the above MFA Server setup guide and launch an appropriate EC2 instance to house it. Visit the following page for a tutorial on launching a Windows EC2 instance: https://docs.aws.amazon.com/AWSEC2/latest/WindowsGuide/EC2_GetStarted.html
The WorkSpaces client leverages the WorkSpaces Authentication Gateway (AG) to securely authenticate against Active Directory and RADIUS. We will be using the AWS Directory Service, Active Directory Connector (ADC), which proxies credentials between components to facilitate this process. For this post, it is assumed the ADC is already configured for Active Directory authentication. For details around configuring an AD Connector with Active Directory and Workspaces, visit the following pages:
AD Connector prerequisites: https://docs.aws.amazon.com/directoryservice/latest/admin-guide/prereq_connector.html
AD Connector / Workspaces setup: https://docs.aws.amazon.com/workspaces/latest/adminguide/launch-workspace-ad-connector.html
Architecture

Microsoft MFA Server Settings
Since this example uses AD Connector, the RADIUS clients are the two AD Connector devices represented by the IP addresses visible from the console view of the Directory Service. The MFA Server setup will require that you identify these IP addresses. In your WorkSpaces console, select Directories, then expand the view of the AD Connector. Make note of the IP Addresses and the security group.
Identifying the IP Addresses and security group of the AD Connector

(Note at this time your RADIUS status will not be ‘Completed’)
RADIUS Authentication
Proceed to the MFA Server interface. In the MFA Server Clients Tab
– Use port 1812 as pre-populated in the AD Connector setup
– Delete the reference to port 1645 since the AD Connector does not use it
– Add both IP Addresses from the AD Connector details and the Shared Secret

Target tab
Select Windows domain

Multi-Factor Auth Servers tab
Check the box identifying the MFA server. A best practice is to deploy multiple MFA servers for redundancy, although this example uses a single MFA server.

AD Connector settings
The following steps are used to integrate the AD Connector with the MFA Server:
1. In the WorkSpaces console, select Directories from the left menu
2. Select your AD Connector and choose Actions, then Update Details
3. Scroll down and expand the Multi-Factor Authentication section and update the details:
- Use the private IP address of the MFA server
- Port 1812
- PAP protocol
- The Server Timeout period can be adjusted to up to 55 seconds if there are issues with the authentication process due to latencies or other factors

Make note of the security group for the AD Connector, as well as that of the MFA server EC2 instance. Make sure the ADC and MFA Server instances can communicate over the assigned port (UDP 1812 in the example) by establishing inbound rules in the instance’s security group and Windows Firewall. You should also validate the outbound communication requirements specified by Microsoft in the setup instructions for the MFA Server.
- Identify the security group of the AD Connector by selecting it and expanding the dialog (ex: sg-0930000)
- In the security group for the MFA Server instance, add an inbound rule for Port: UDP 1812, with Source = [the security group of the AD Connector]
- Validate that the same source / port combinations are allowed by Windows Firewall of the server.
Usage
The user should visit the User Portal web site defined in the MFA Server Admin tool, and log in with their Active Directory credentials to invoke the Registration process. They will be able to enter their preferred telephone number, then receive the first call to verify their identity.
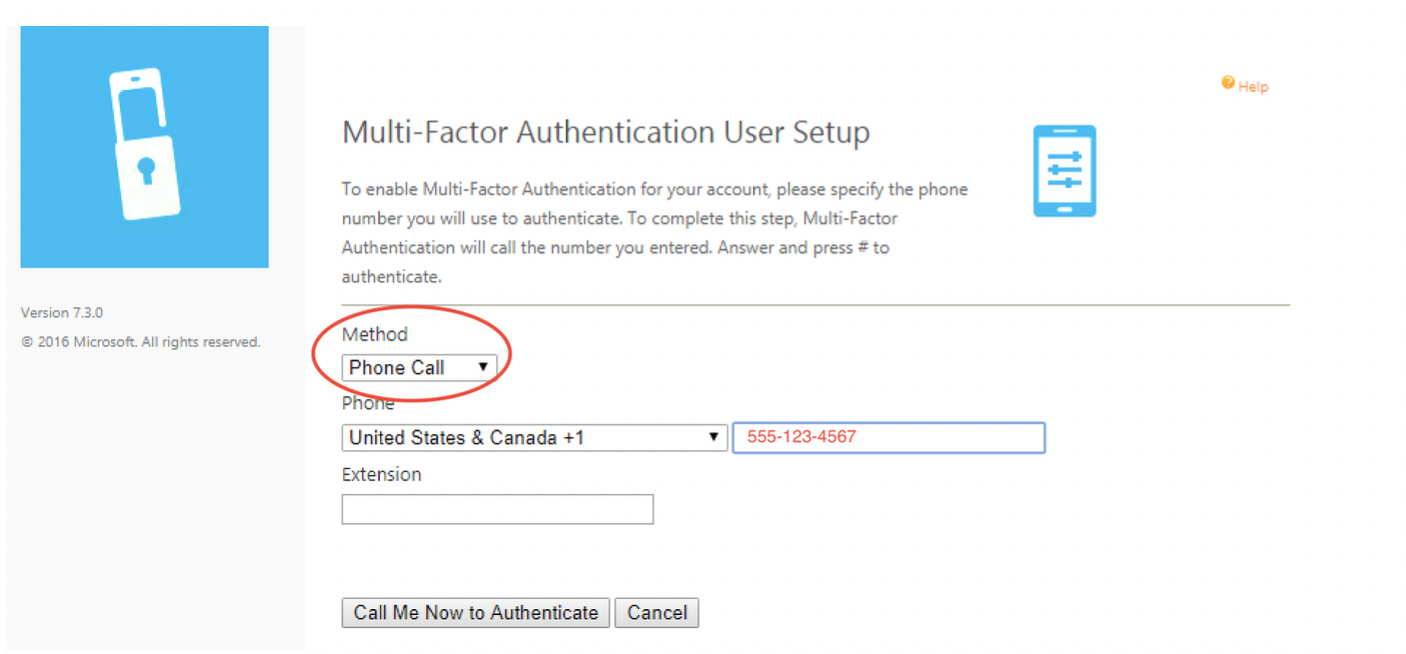
Once Registered into the MFA system, the user can now leverage it for use with the WorkSpaces client. They should enter their Active Directory Username and Password into the respective fields, then re-enter their Password into the MFA Code field. This example is validated for Phone Call Multi-Factor Authentication.

That’s it! Your users are now able to leverage Azure MFA Server with Phone Call factor for accessing Amazon WorkSpaces.