Integration & Automation
Top 5 posts published in 2021 on the AWS Infrastructure & Automation Blog
Interested in how people solve business problems using automation-related Amazon Web Services (AWS) services, such as AWS CloudFormation? That’s generally what authors write about here on the AWS Infrastructure & Automation Blog. Read on for highlights from the five most viewed posts published on this blog in 2021.
#5: Automate IAM credential reports at scale across AWS
by Ibukun Oyewumi and Jose Obando
“Automation is your best friend when it comes to compliance and auditing. Organizations must continually monitor and mitigate security risks to maintain regulatory and compliance requirements that involve AWS Identity and Access Management (IAM) practices.
“In this post, we demonstrate how to automate and consolidate IAM credential reports for your AWS accounts using a scalable infrastructure as code (IaC) automation created through AWS CloudFormation. With this process, you can generate and download credential reports that list all of your IAM users and the status of their credentials, including passwords, access keys, and multifactor-authentication devices…” Read this post.
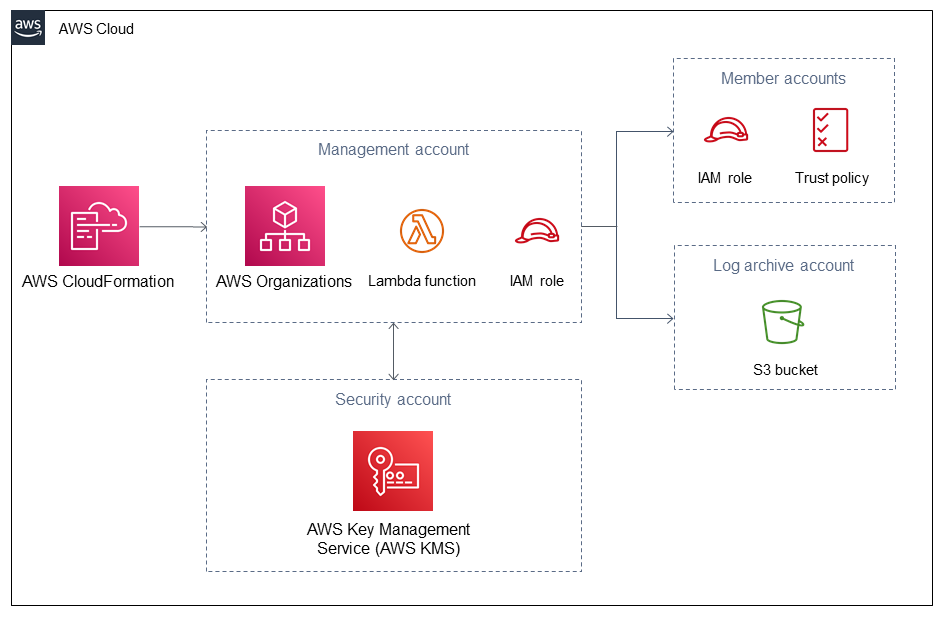
Figure 1. Architecture diagram showing the AWS resources that are deployed by implementing the steps in this #5 post
#4: Manage Amazon S3 Event Notifications using a Lambda function
by Philip Chen
“Is your Amazon Simple Storage Service (Amazon S3) bucket shared across multiple AWS CloudFormation stacks? If so, you most likely struggle with finding an efficient way to manage S3 Event Notifications.
“By default, when you configure a shared S3 bucket, updates to the event notification configuration can override preexisting notifications. This behavior exists because the notifications are managed centrally by the S3 bucket, not by the individual teams that manage the stacks.
“If you want to change the S3 bucket configuration to accommodate all notifications, you must engage with the team that manages the bucket. The problem with this is that individual teams that manage the stacks and own the individual services cannot configure their own notifications.
“To solve this, you can use an AWS Lambda function and custom AWS CloudFormation resources to bypass the centralized S3 notification configuration, allowing you to manage notifications for each service. With this approach, each service’s configuration can manage adding or removing notifications for various S3 actions without affecting the existing notifications configured by other services.
“In this post, I walk through the process of creating the stacks, Lambda function, and custom resources to help you manage S3 Event Notifications…” Read this post.

Figure 2. Architecture diagram showing the three stacks that you configure by implementing the steps in this #4 post
#3: Use Git pre-commit hooks to avoid AWS CloudFormation errors
by Troy Ameigh and Andrew Glenn
“Do you struggle with formatting AWS CloudFormation templates? Do you wonder if your Python and shell scripts are 100% neat and error-free? Do you spend time and mental energy fixing missing semicolons and trailing white space at the end of your files? If so, there’s a better way to avoid errors: Use GitHub pre-commit hooks.
“These hooks catch and sometimes even fix formatting issues and messy scripts before you commit changes to your Git repository.
“With the approach we propose, you configure pre-commit hooks for your project and commit your changes to the repo. Then Git inspects your files and returns a list of any issues that must be fixed. If Git flags issues, the commit fails. If not, your code is committed to the project.
“For example, here on the AWS Integration and Automation team, when we build AWS Quick Starts, we commonly use the following pre-commit hooks:
- cfn-lint: AWS CloudFormation linter. Validates general mappings, resources, parameters, and other components in both YAML and JSON-based CloudFormation templates.
- black: Formats your Python code.
- isort: Sorts your imports in alphabetical order.
- seed-isort-config: Sorts your third-party imports and integrates them into isort.
- flake8: Enforces style consistency in Python code.
- shellcheck: Checks shell scripts for accuracy.
- mixed-line-ending: Replaces or checks mixed line endings.
- trailing-whitespace: Trims trailing white space.
“In this post, we walk you through an exercise that helps you learn, first-hand, how pre-commit hooks work…” Read this post.
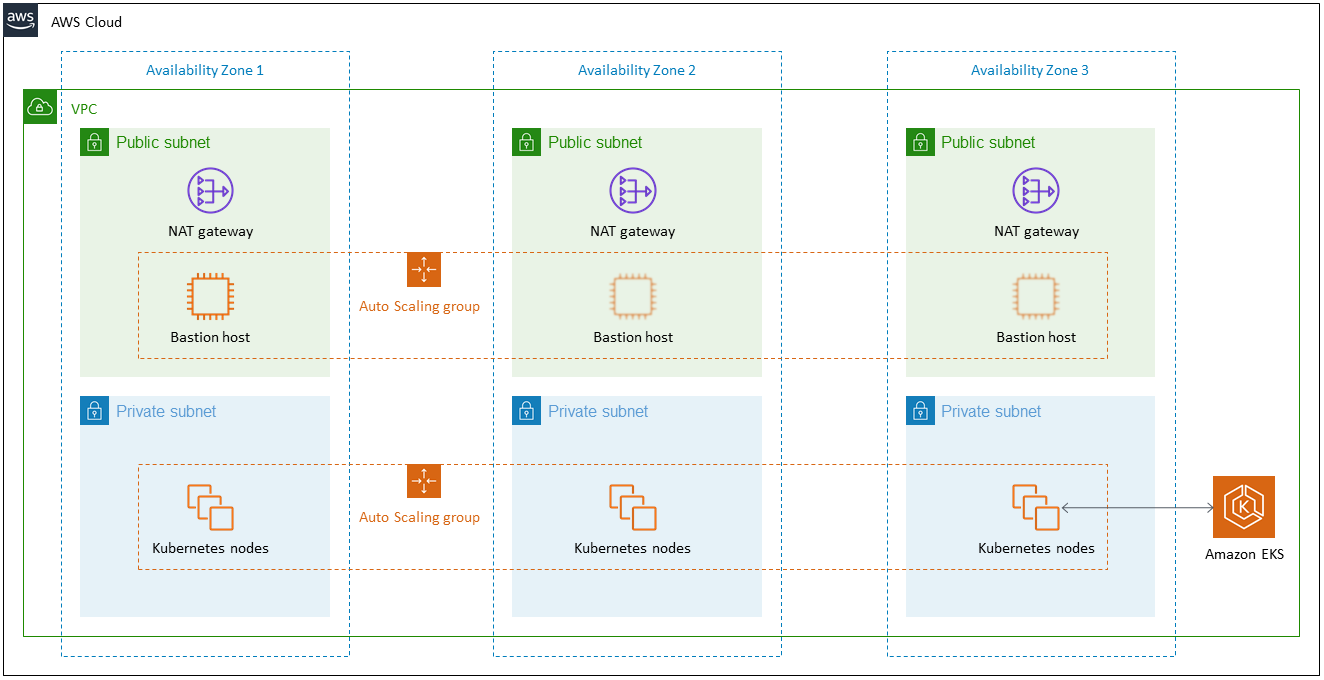
Figure 3. Architecture diagram for the test repo, the Amazon EKS Quick Start, used in the walkthrough for this #3 post
#2: Deploy an SPA with personalized subdomains using AWS CDK
by Paul Kukiel
“Customer-specific subdomains can improve your experience with a single-page application (SPA). Imagine an application at www.example.com. With customer subdomains, customer A can use the application at customerA.example.com, and, similarly, customer B can use the application at customerB.example.com. Despite these benefits, there are drawbacks, such as managing a Domain Name System (DNS) record for each subdomain, having multiple front-end deployments, and diverging code bases.
“In this post, I provide a serverless operation of hosting an SPA with personalized subdomains on the Amazon Web Services (AWS) Cloud. I also use the AWS Cloud Development Kit (AWS CDK) to show you how to deploy all of the required resources…” Read this post.
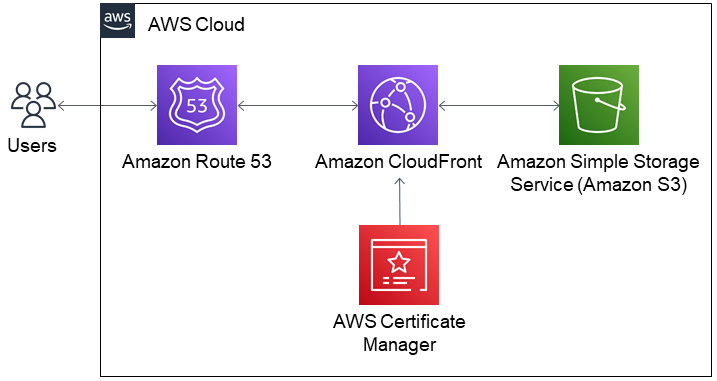
Figure 4. Architecture diagram showing the collection of AWS resources deployed in the walkthrough for this #2 post
#1: Use Python to manage third-party resources in AWS CloudFormation
by Jay McConnell
“In this post, I demonstrate how to use Python and the AWS CloudFormation registry to manage third-party resources, which are common components of modern cloud architectures. The benefits of using CloudFormation to manage third-party resources include reducing deployment complexity and enabling the inherent benefits of CloudFormation, such as rollback if a failure occurs.
“Using the CloudFormation Command Line Interface (CLI), I create a CloudFormation resource provider, which enables you to manage GitHub repositories and AWS resources from a single template…” Read this post.
What to do next
 |
Thank you, all of you who create the posts for this blog and all of you who read them. The Infrastructure & Automation Blog team look forward to sharing more about automation in the AWS Cloud in 2022.
Meanwhile, check out the ready-to-use automated reference deployments that AWS has made available. These automated reference deployments—AWS Quick Starts—are built by AWS solutions architects and AWS Partners to help you deploy popular technologies on AWS following AWS best practices. Instead of doing hundreds of manual steps that may take hours or weeks, you build your environment in just a few steps and start using it within minutes. If you try a Quick Start, please come back to this post and leave a comment to let me know how it went.
 Marcia Riefer Johnston
Marcia Riefer Johnston