AWS Cloud Operations Blog
Govern your applications centrally using AppRegistry and Application Manager
The customers I work with often handle multiple applications in their cloud environments. In general, an application includes multiple AWS resources deployed via AWS CloudFormation stacks, APIs, or other infrastructure as code tools. My customers often ask me about efficient mechanisms for managing the resources and governing the security policies of their resources in an Application context. An application context includes a group of resources related to computing, networking, and storage resources. Furthermore, customers want to define metadata specific to the application, including information regarding application teams, finance, and security.
This post will show you a mechanism for grouping the resources using AWS Service Catalog AppRegistry with AWS Resource Groups and getting additional operational insights into the applications through AWS Systems Manager Application Manager.
AppRegistry provides a place to collect your AWS CloudFormation stacks and associate your customer-defined attribute groups (metadata) that describe your AWS applications. Automate stack updates and metadata changes by calling AppRegistry from within your continuous integration/continuous delivery (CI/CD) processes. The IT and business stakeholders can always receive the latest information, such as organizational ownership, data sensitivity, and the cost center of the applications by querying the attribute groups.
Application Manager, a capability of AWS Systems Manager, helps DevOps engineers investigate and remediate their AWS resource issues in the context of their applications and clusters. Application Manager aggregates operations information from multiple AWS services and Systems Manager capabilities to a single AWS Management Console.
To try out the steps in this blog post, you will utilize the provided AWS CloudFormation Stack to deploy a sample application, register it with AppRegistry, and configure additional security policies and monitoring metrics. You will see how these applications are discovered automatically in Application Manager and receive additional application insights.
Here’s a quick review of some of the terms I will use:
- An application is a logical group of AWS resources that you want to operate as a unit.
- Metrics are the fundamental concept in Amazon CloudWatch. A metric represents a time-ordered set of data points published to CloudWatch.
- OpsCenter, a capability of AWS Systems Manager, provides a central location where operations engineers and IT professionals can view, investigate, and resolve operational work items (OpsItems) related to AWS resources.
- AWS Config continuously tracks the configuration changes occurring among your resources. It checks whether these changes violate any of the conditions in your rules.
Things to consider
Below are a few things to keep in mind before diving deep into the solution:
- You must have an AWS account to deploy this solution.
- Enable OpsCenter in the AWS Region where you are deploying this solution.
- Enable AWS Config service in the Region where you are operating. If you are working on AWS Control Tower Managed environment, then AWS Config is enabled as part of account enrollment.
- Create an EC2 key pair if needed. This is utilized with LAMP stack that you deploy as part of this solution.
- You will be deploying a sample single instance LAMP stack for quick validation. Refer to Application frameworks to deploy highly scalable and durable stacks.
- The CloudWatch alarm thresholds are configured very low for this blog in order to demonstrate functionality. You may update the CloudWatch alarm to increase the thresholds as required.
Solution overview
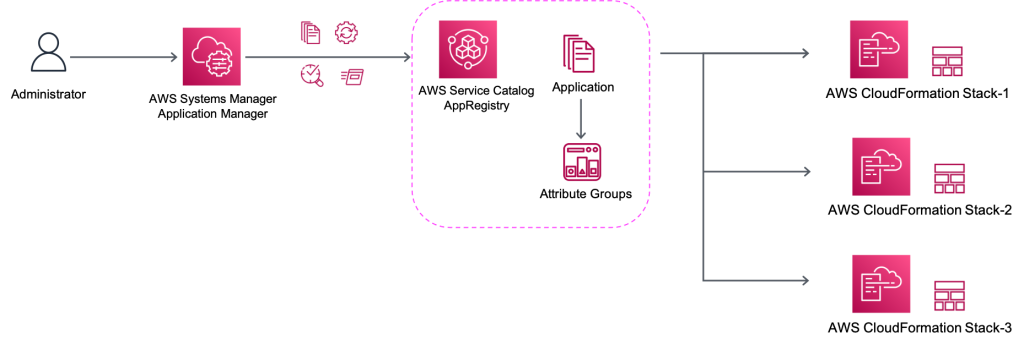
The following diagram illustrates the workflow of how to utilize Application Manager to enable governance policies and conduct operational tasks in the context created by AppRegistry Application.
- Launch the CloudFormation stack provided as part of this blog. The stack deploys:
- A Virtual Private Cloud to provide an isolated environment for the application
- A LAMP stack to simulate a web application.
- Amazon CloudWatch alarms configured for this application’s resources.
- Additional AWS Config rules to watch for the application’s compliance status.
- Upon successful completion of the stack, you will see Applications in the Application Manager automatically.
- You will manually trigger actions that would result in generating CloudWatch alarms and OpsItems.
- You will investigate the outstanding non-compliances and operational insights by using Application Manager.
How it works
We launch a stack that creates a new VPC, deploy a LAMP stack which includes set of open source software used for web application development, and configures CloudWatch metrics to report high traffic. Then we will walk through the solution components and finally use run books to remediate non-compliances reported.
Step 1: Launch Resources and register with AppRegistry
- Login to your AWS Management Console.
- Choose Launch stack. (The stack is deployed in
us-east-1region by default. Update the region if needed) - Choose Next.
- Under the Specify stack details screen select the below Parameters:
- RegionAZ1Name: Select Availability Zone 1 from the list.
- RegionAZ2Name: Select another Availability Zone 2 from the list.
- EC2KeyPair: Select from the available list of EC2 key pairs.
- BastionSSHCIDR: Type in a CIDR to allow SSH access to the bastion. You could get your IP address using https://www.whatsmyip.org/, and add ‘/32’ in addition (example: xx.yy.xx.yy/32).
- SupportContact: Key in an email address, the same email will also be the configured SNS Subscription.
- Adjust the remaining fields as needed. For this blog post, you can leave the remaining defaults.
- Choose Next, Next.
- In the Review screen, under Capabilities, check the boxes:
- I acknowledge that AWS CloudFormation might create IAM resources with custom names. and
- I acknowledge that AWS CloudFormation might require the following capability: CAPABILITY_AUTO_EXPAND.
- Choose Create Stack.
- Wait for the stack status to change to CREATE_COMPLETE. This may take 5-10 minutes.
- While you wait for the stack status change, you should receive an SNS Subscription email. Confirm the subscription.
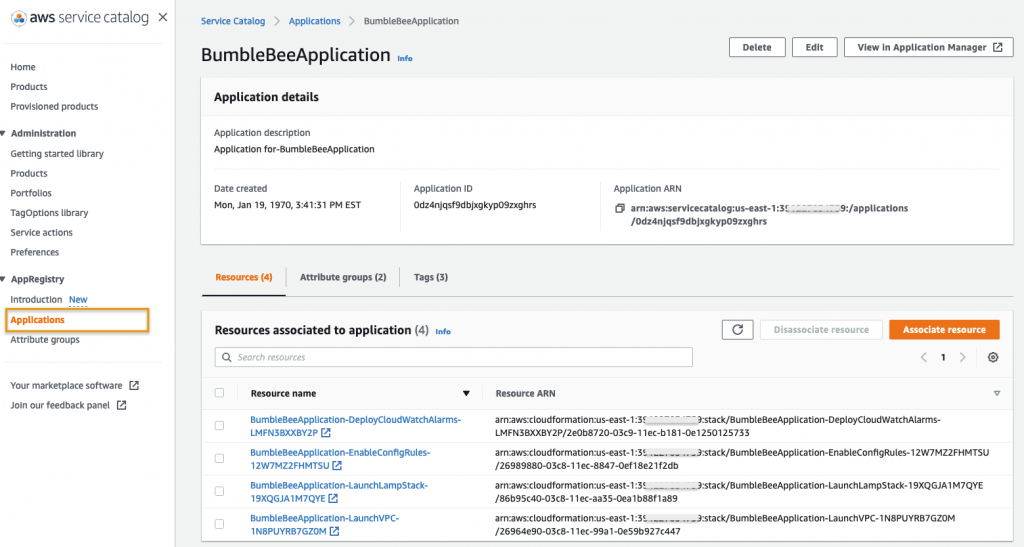
Step 2: Verify the new AppRegistry Application
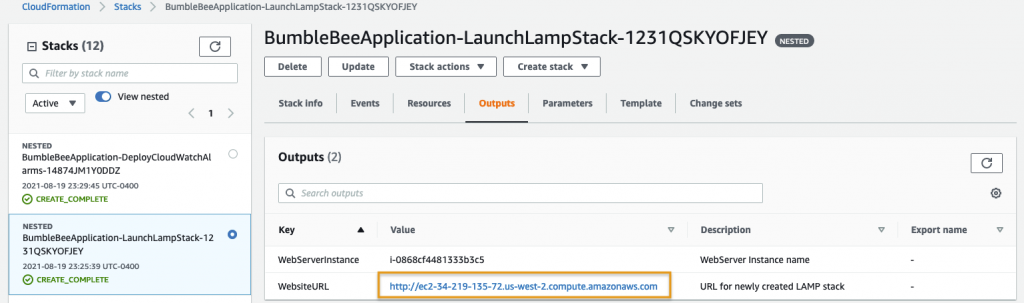
- Choose the Outputs tab of the CloudFormation stack deployed in step-1.
- Choose the value of ApplicationSCURL in order to open the new Application that was just created.
- Alternatively, choose Service Catalog, AppRegistry, Applications, and the
Application Nameto access the application. - Under the Resources tab, you should see 4 resources.
- Under the Attribute groups tab, you should see 2 resources.
- Under the Tags tab, you should see 3 key:value pairs.
Step 3: Access the AppRegistry Application in Systems Manager Application Manager
- In the AWS Service Catalog Application page, choose View in Application Manager in the top right corner.

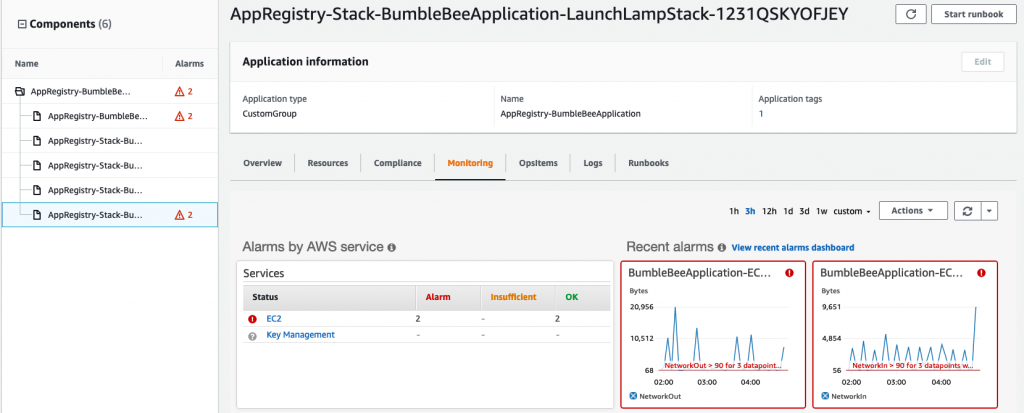
- The Overview gives details related to active CloudWatch Alarms and operation Items as shown below.
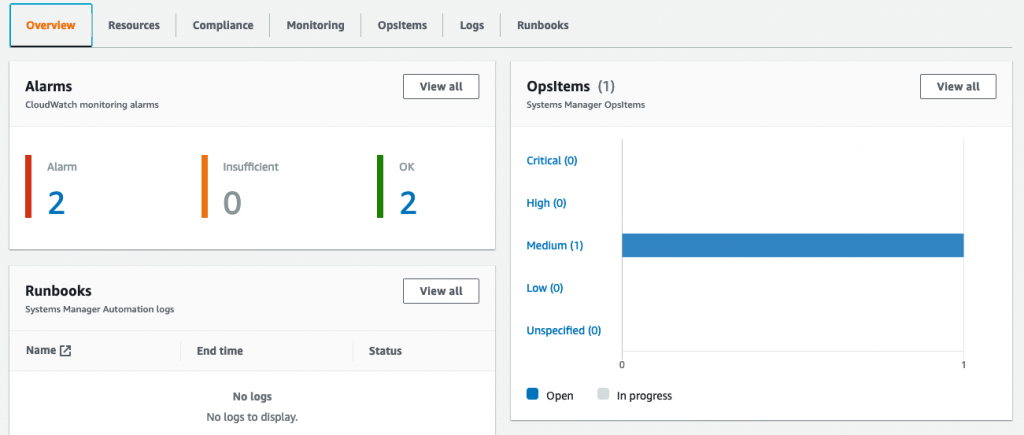
- Choose the Resources tab to view a list of all resources associated with this application.

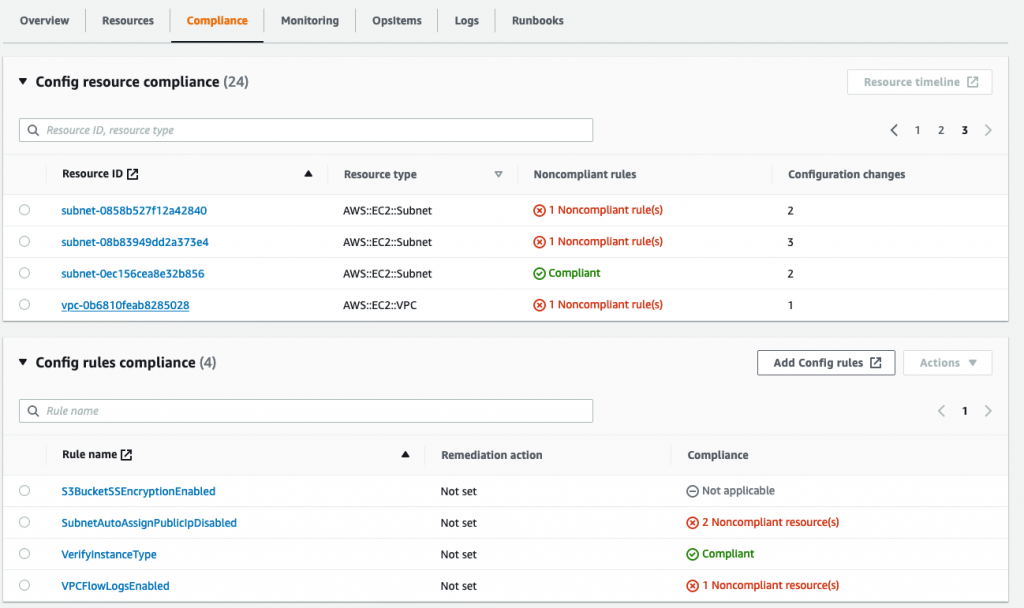
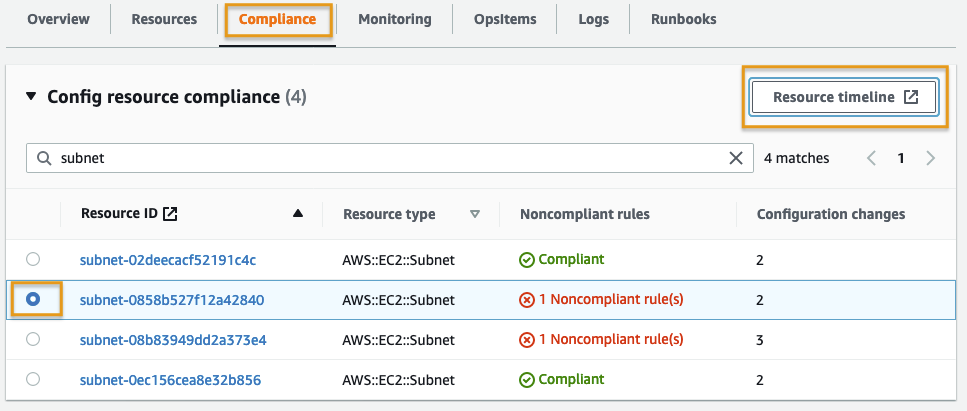
- Choose the Compliance tab to view the AWS Config resource compliance of the application resources. Optionally select a Resource ID and choose Resource timeline to view the resource status history.
- Scroll down to the AWS Config rules compliance section to view the config rules applicable to the application.
- Choose the Monitoring tab and on the left panel select the Component that starts with AppRegistry-Stack-BumbleBeeApplication-LaunchLampStack.
Step 4: Run some network traffic to generate an Ops Item
- Navigate to CloudFormation Console and choose the Stack that starts with
<Your-stack-name>-LaunchLampStack-. - Choose the Outputs tab and value of WebsiteURL to open the PHP site you created using LAMP stack.
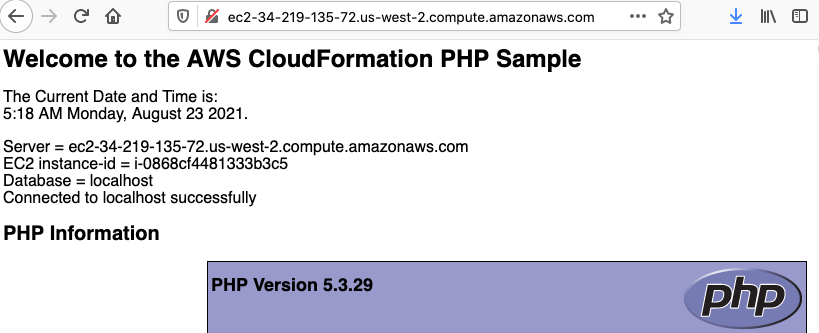
- This will open a webpage as shown below. Refresh the webpage 3-4 times to generate traffic in order to turn on CloudWatch alarm.
- Navigate to Systems Manager, Application Manager, AppRegistry applications and
<Application-name> - You will now see OpsItems reported on the Overview page.
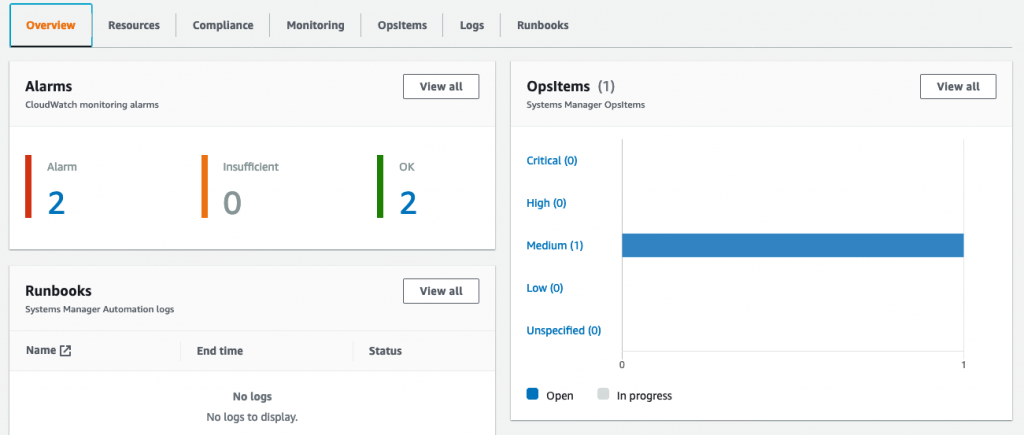
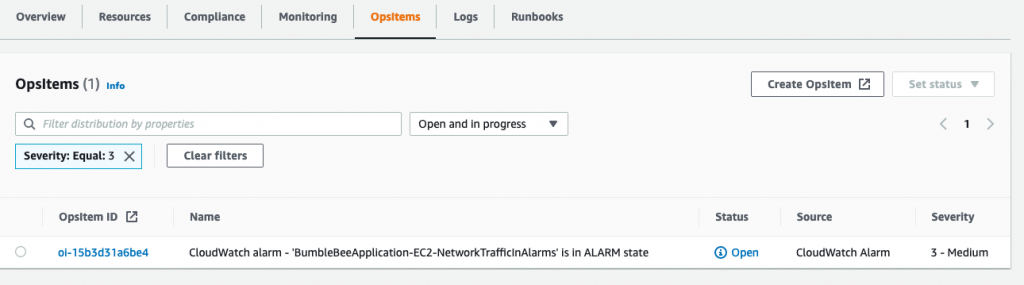
- Choose the OpsItems tab to view all open OpsItems for the application.
Step 5: Verify Resource timeline of a Noncompliant resource
- Choose the Compliance tab on the Application page
- Under config resource compliance, search for
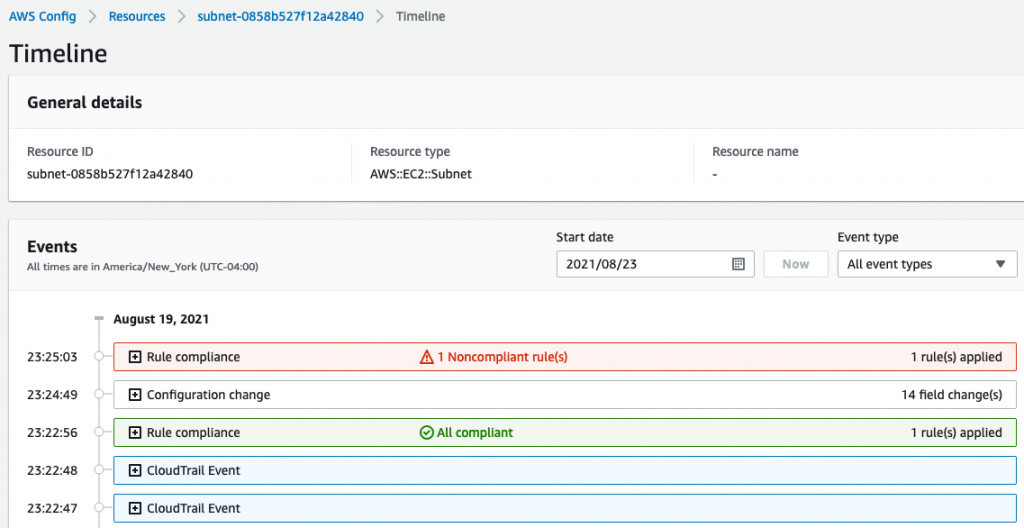
Subnetin order to list all subnets associated with the application. - Select any Resource ID marker as Noncompliant, and choose Resource timeline.
- You will be redirected to the resource timeline window in the AWS Config console.
Congratulations! You successfully created and deployed an application in AWS Service Catalog AppRegistry with multiple stacks comprised of multiple AWS resources. You also extended the application to the AWS Systems Manager Application Registry in order to centrally view and govern the application resources by gaining additional insights into the compliance and operations statuses.
Cleanup
The solution deployed as part of this blog was for demonstration. We recommend uninstalling this solution and updating as required for your business needs. Leaving the stack installed could result in additional notifications and accumulate the cost for EC2, DB instance, and other components deployed as part of this solution. Follow the steps below to uninstall the solution.
- Update the OpsItems and change the status to Resolved.
- Delete the CloudFormation template deployed in step-1.
Conclusion
This post showed you how to group multiple AWS resources as an Application using AWS Service Catalog AppRegistry and centrally manage the resources, as well as govern the security policies in the context of an Application using AWS Systems Manager Application Manager integration. An application context includes a group of resources related to computing, networking, and storage resources. Moreover, customers can also define metadata specific to the application, including operational information, cost, and other dimensions.
Author

Kishore Vinjam is a partner solutions architect focusing on AWS Service Catalog, AWS Control Tower, and AWS Marketplace. He is passionate about working in cloud technologies, working with customers, and building solutions for them. When not working, he likes to spend time with his family, hike, and play volleyball and ping-pong.