AWS Cloud Operations Blog
Manage AWS Managed Microsoft AD resources with Session Manager port forwarding
Active Directory administrators are accustomed to managing domain resources using Remote Server Administrators Tools (RSAT) installed on either their workstations or a member server in the domain. When it comes to managing resources on a managed Active Directory service, such as the case with AWS Managed Microsoft AD, these tools must be available for administrators because domain resources still must be managed, unlike the infrastructure. Currently, one way to make these tools available is to add an EC2 instance to a domain and use a Remote Desktop Protocol (RDP) connection to that EC2 instance. Of course, the RSAT tools must also be installed on that instance.
Although effective, using RDP requires more management, such the need to manage inbound rules for port 3389. In some cases, having this port exposed to the internet might put your systems at risk. For example, they can be susceptible to brute force or dictionary attacks. In this blog post, I discuss another option: using the AWS Session Manager port forwarding feature to manage your domain resources. I show you, step by step, how to create an RDP connection to an EC2 instance and manage AWS Managed Active Directory using port forwarding. This option eliminates the need to open any inbound rules. It also integrates natively with AWS Identity and Access Management (IAM) and AWS CloudTrail, two services that enhance your security and audit posture.
Overview
Port forwarding provides the ability to forward traffic between your clients to open ports on your EC2 instance. After you configure port forwarding, you can connect to the local port and access the server application running inside the instance. The port forwarding feature in AWS Systems Manager Session Manager is controlled through IAM policies on API access and the AWS-StartPortForwardingSession document. These are two ways where you can control who in your organization is authorized to create tunnels to access your EC2 instances.
The following diagram shows how the Session Manager port forwarding feature creates a tunnel similar to an SSH tunnel,
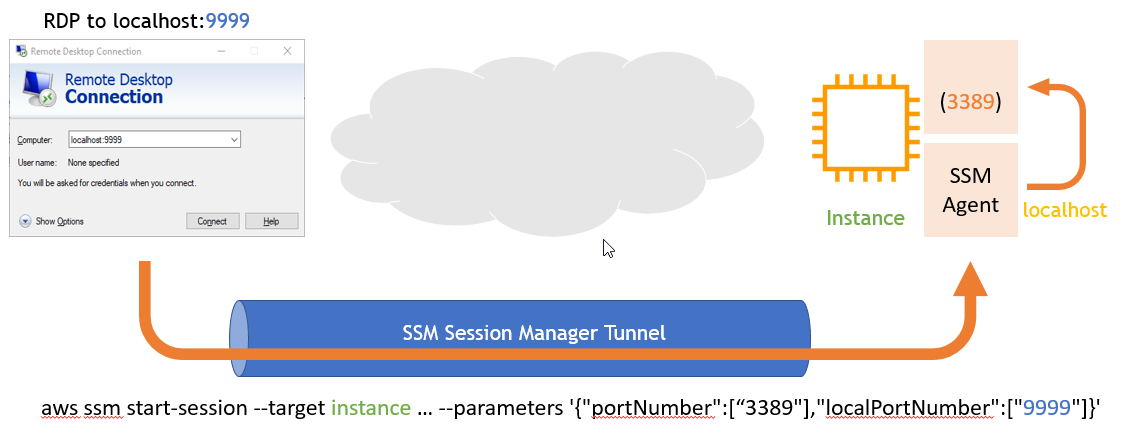
Figure 1: Creating a tunnel
When you use the port forwarding feature in Systems Manager Session Manager, you have the option to use an auditing service like AWS CloudTrail to provide a record of the connections made to your instances. You can also monitor the session using Amazon CloudWatch Events with Amazon Simple Notification Service to receive notifications when a user starts or ends session activity. There is no additional charge for accessing EC2 instances using AWS Session Manager port forwarding.
Tutorial prerequisites
Step 1: Create an instance
Create an instance in a private subnet and join it to the domain using seamless domain join. In the Amazon EC2 console, under Configure Instance Details, provide the following:
- The AWS Managed AD directory that the instance is part of.
- An IAM role. At a minimum, attach the followings policies:
- AmazonSSMManagedInstanceCore: This managed policy enables an instance to use Systems Manager core functionality.
- AmazonSSMDirectoryServiceAccess: This managed policy allows SSM Agent to access AWS Directory Service on your behalf for requests from the managed instance to join the domain.
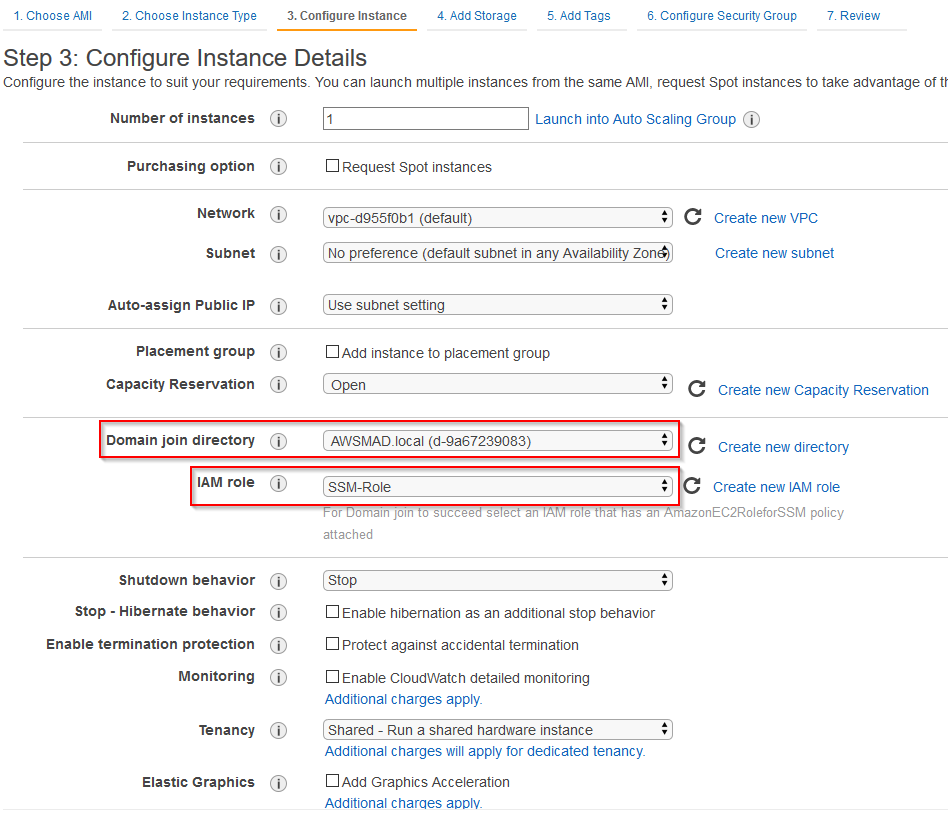
Figure 2: Amazon EC2 console page to specify domain join directory and IAM role
Step 2: Start an RDP session
Start an RDP session to the instance you just created. You must be member of Domain Admins group. In this example, I use the admin user created when I set up the AWS Managed AD.
Open a terminal and enter the following command to start a session to the instance:
aws ssm start-session --target <instance-id> --document-name AWS-StartPortForwardingSession --parameters "localPortNumber=9999,portNumber=3389"
You should see a message that indicates port 9999 has been opened for this session.
Using Microsoft Remote Desktop, open the Session Manager RDP remote desktop connection configured earlier for localhost:9999.
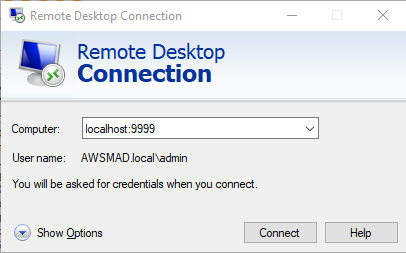
Figure 3: Remote Desktop Connection page
You should be now connected and able to work on remote instance over RDP.
To terminate the session, press Ctrl+C in the terminal.
Step 3: Install RSAT
Run PowerShell as an administrator to install RSAT.
- Run the following commands:
Install-WindowsFeature RSAT-AD-Tools,RSAT-AD-PowerShell,RSAT-ADDS,RSAT-AD-AdminCenter,RSAT-ADDS-Tools,RSAT-DNS-Server
To manage the domain from an instance in a private network, run dsa.msc from PowerShell to open Active Directory Users and Computers.
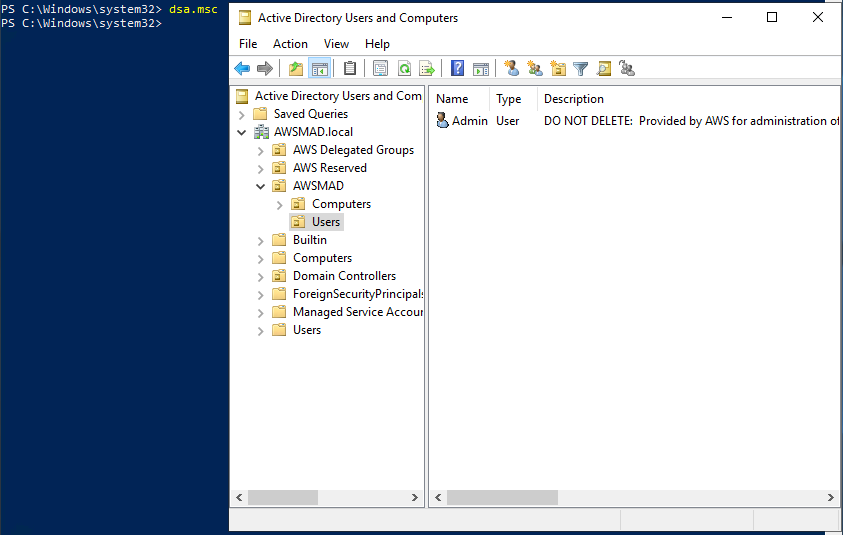
Figure 4: Active Directory Users and Computers
To manage DNS, run dnsmgmt.msc from PowerShell or Command Prompt and then connect to the AD domain name.
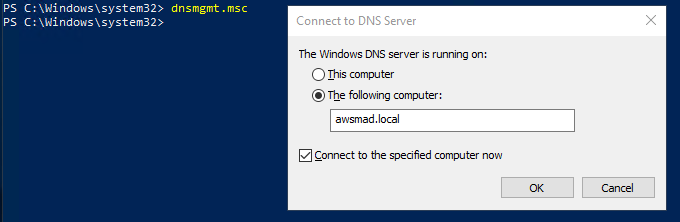
Figure 5: Connect to DNS Server dialog box
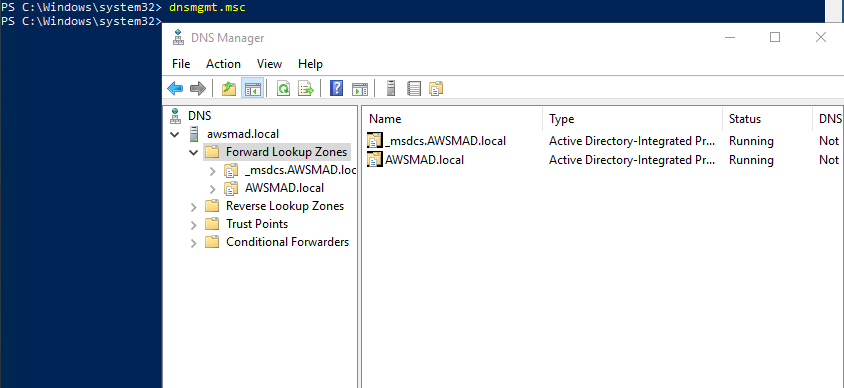
Figure 6: DNS Manager
Support for domain controllers
Session Manager connections to domain controllers are also supported. To initiate a connection with either the default Session Manager connection or the port forwarding feature discussed in this post, complete these steps:
- Create the ssm-user in your domain.
- Add the ssm-user to the domain groups that grant the user local access to the domain controller. One example is to add the user to the Domain Admins group.
IMPORTANT: Follow your organization’s security best practices when you grant the ssm-user access to the domain.
Conclusion
AWS Session Manager port forwarding to RDP provides a simplified and secure way to manage your domain resources.
The benefits include:
- Security: A more secure way to access your EC2 instance with no open inbound ports.
- Centralized access control to instances: Single place to grant and revoke access to instances using only IAM policies. This gives you the ability to control which individual users or groups in your organization can use Session Manager and which instances they can access.
- Auditing: AWS CloudTrail records information about Session Manager API calls made in your AWS account.
- Monitoring: You can monitor the session activity with Amazon CloudWatch Events and Amazon Simple Notification Service.
For more information, see Port Forwarding Using AWS System Manager Session Manager and the AWS Systems Manager Session Manager documentation.