Networking & Content Delivery
Simplify SD-WAN connectivity with AWS Transit Gateway Connect
SD-WANs, or Software Defined Wide Area Networks, have long been used to connect data centers and branch offices over the public internet. Today, those networks must also extend to the cloud. However, traditional SD-WAN infrastructure is not always well suited for this task—significantly increasing complexity and operational burden. At the same time, many AWS customers are using AWS Transit Gateway at the network edge to connect their global network to the AWS backbone. With the launch of AWS Transit Gateway Connect, there is now a native way to connect your SD-WAN infrastructure with AWS. This makes it easy to extend your SD-WAN into AWS without having to set up IPsec VPNs between SD-WAN network virtual appliances and Transit Gateway. Transit Gateway Connect is a new attachment type that supports Generic Routing Encapsulation (GRE) for higher bandwidth performance compared to a VPN connection. Transit Gateway Connect supports Border Gateway Protocol (BGP) for dynamic routing, and removes the need to configure static routes. This simplifies network design and reduces the associated operational costs. In addition, integration with Transit Gateway Network Manager provides advanced visibility through global network topology, attachment level performance metrics, and telemetry data.
To understand how this feature works, let’s review some of the new terms and concepts introduced in Transit Gateway Connect:
-
Connect attachment: this is a new Transit Gateway attachment type that uses a transport Transit Gateway attachment (existing VPC or AWS Direct Connect attachment as transport) for the third-party appliance to connect to Transit Gateway. Generic Routing Encapsulation (GRE) tunneling protocol and Border Gateway Protocol (BGP) are used over the Connect attachment.
-
Connect VPC: this is a central VPC that contains EC2 instances running third-party virtual appliances. These instances link to Transit Gateway using a Connect attachment type.
-
Transport attachment: this is an existing Transit Gateway attachment type (VPC or AWS Direct Connect attachment) that is used as the underlying transport by the Connect attachment.
-
Third-Party appliances: a third-party virtual router/gateway appliance running on an EC2 instance, in a Connect VPC that is using VPC attachments as the transport.
Benefits of Transit Gateway Connect
-
Native integration: You can now natively connect your network to AWS Transit Gateways without having to configure complex IPsec VPN connections. Dynamic routing capability further simplifies route management across hybrid cloud environments.
-
Higher bandwidth interconnects between SD-WAN and AWS cloud: You no longer need to manage and operate multiple IPsec VPN connections between your third-party appliances and Transit Gateway to support higher bandwidth. Transit Gateway Connect does this by using GRE tunnels that are scaled horizontally to provide higher bandwidth within a single Connect attachment. This increases total bandwidth to 20 Gbps per Connect attachment.
-
Increased visibility: Integration with Transit Gateway Network Manager gives you increased levels of visibility into your network health. It shows you performance metrics and telemetry data, not only from virtual appliance instances in AWS, but also from branch appliances sitting behind them. Now you can truly monitor your end-to-end network, across AWS and on-premises.
-
End-to-End Management: You can perform end-to-end management of your global network with a single orchestration platform. Transit Gateway Connect does this through deeper integration with APN Partner SD-WAN orchestration platforms and gives you the ability to update Transit Gateway route tables, resulting in more intelligent routing decisions.
-
Security and Compliance: You can use private IP addresses on your third-party virtual appliances by using Transit Gateway Connect to establish connectivity and reachability to resources located in AWS Virtual Private Clouds (VPC), decreasing the need for internet routable public IPs.
Architecture
A high-level architecture of Transit Gateway Connect using VPC attachments is shown in the following: Figure 1 (a&b), reference architectures.
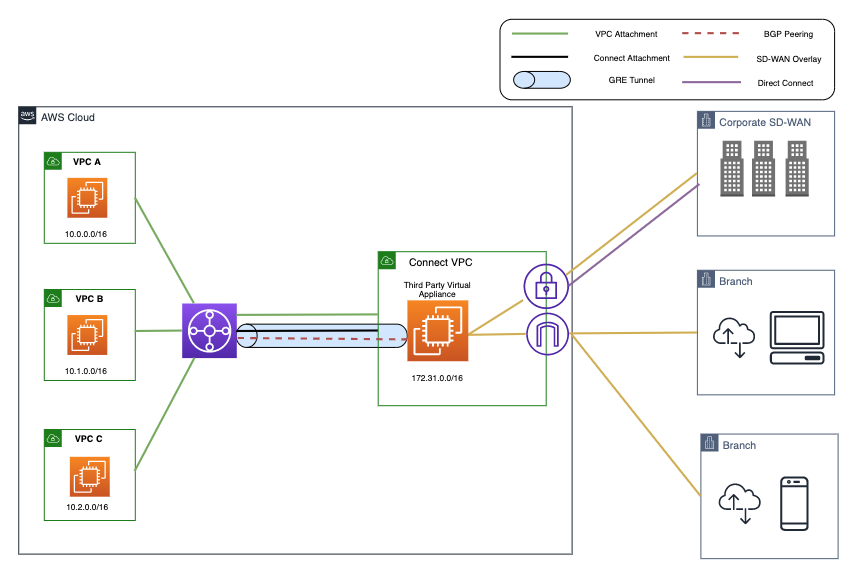
Figure 1(a), Transit Gateway Connect – High Level Architecture – Virtual Appliance
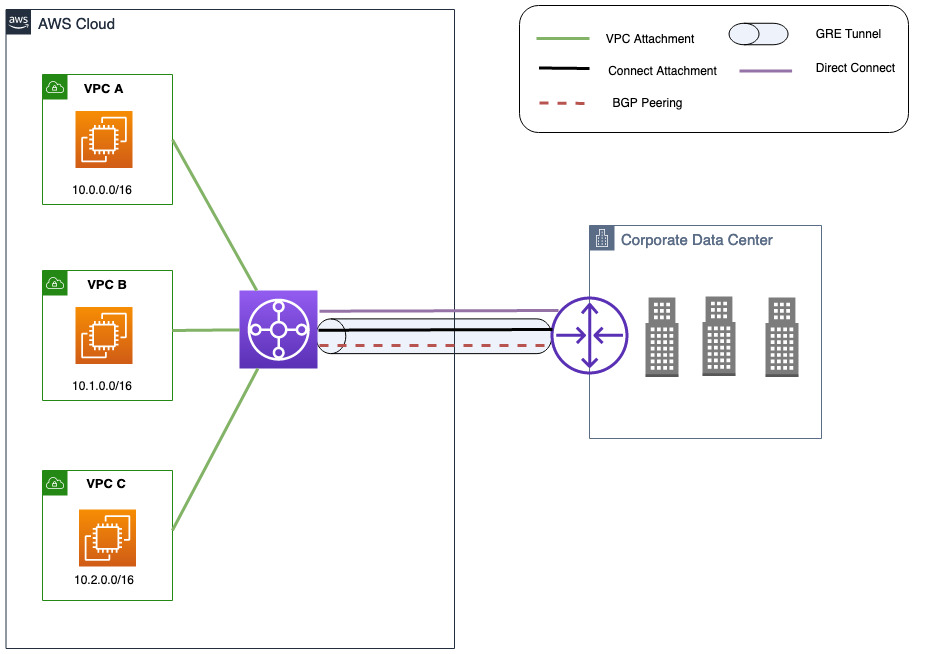
Figure 1(b), Transit Gateway Connect – High Level Architecture – AWS Direct Connect
Transit Gateway Connect can also be used as a third-party branch or customer gateway appliance running in an on-premises network that uses AWS Direct Connect as transport. This is shown in the following: Figure 1(b), Transit Gateway Connect – AWS Direct Connect Attachment. Here you see how BGP peering has been established with Transit Gateway over a GRE tunnel, using a Connect attachment. This attachment is also responsible for exchanging traffic with Transit Gateway over an encapsulation channel.
With this new Connect attachment type, GRE packets from third-party appliances are routed based on the associated route table of the Connect attachment. A GRE tunnel is established between Transit Gateway and the third-party appliance. You can then establish BGP peering with the Transit Gateway within the GRE tunnel to securely exchange routing information.
Transit Gateway Connect – getting started
In this example we will review the process using the AWS Management Console. The Command Line Interface (AWS CLI) and AWS Cloud Development Kit (AWS CDK) can also be used to create a Transit Gateway Connect attachments. A diagram of the overall architecture we will walk through can be seen in the preceding Figure 1(a), Transit Gateway Connect – High Level Architecture – Virtual Appliance.
-
Modify or create a new Transit Gateway to allocate a CIDR block. An IP address within this CIDR block is allocated for the Transit Gateway side of the Connect peer and configured as GRE outer IP address.

- Create a Transit Gateway attachment with attachment type as VPC. This will be our Transport attachment. No changes needed if you are modifying an existing Transit Gateway.

- Select a Connect attachment type to your Transit Gateway using the VPC attachment as the Transport attachment.

- Create a Connect peer (GRE tunnel) specifying the GRE and BGP parameters. In this example, we are using iBGP. (If you want to use eBGP, you can specify a different Peer ASN.) Note: you must use eBGP multi-hop.

- Create a route in the appropriate VPC/Subnet route table for the third-party virtual appliances to connect with the Transit Gateway side Connect peer IP (GRE tunnel IP).

- In order to complete the Connect peer configuration (GRE tunnel and BGP peering) on the third-party virtual appliance, configure the GRE tunnel and verify you can ping the BGP peer IP address of Transit Gateway sourcing from the virtual appliance’s BGP peer IP address within the GRE tunnel. You can then establish BGP session to exchange routes with Transit Gateway. (Note: The GRE outer IP address of Transit Gateway does not respond to ICMP.)

- (Optional) To help achieve high availability, you can have your second third-party virtual appliance in a different Availability Zone and follow step 3 to create another Connect Peer.
- By following these steps, you create high availability design that was shown in the following: Figure 2. High availability over Transit Gateway Connect.
 Figure 2. High availability over Transit Gateway Connect
Figure 2. High availability over Transit Gateway Connect
Things to know
-
You can create a new Connect attachment on an existing Transit Gateway.
-
Third-party appliances can be located on-premises or run as a virtual appliance in the VPC. The appliance must be configured with a GRE tunnel in order to send and receive traffic from Transit Gateway using Connect attachments. The appliance must be configured with BGP for dynamic route updates and health checks. If the appliance is located on-premises, an AWS Direct Connect connection is required.
-
Connect attachments do not support static routes. BGP is a minimum requirement for Transit Gateway Connect.
-
Transit Gateway Connect supports a maximum bandwidth of 5 Gbps per GRE tunnel. Bandwidth above 5 Gbps is achieved by advertising the same prefixes across multiple Connect peer (GRE tunnel) for the same Connect attachment.
-
A maximum of four Connect peers are supported for each Connect attachment at the time of launch.
-
Transit Gateway Connect supports IPv6 and dynamic route advertisements via Multiprotocol Extensions for BGP (MBGP or MP-BGP).
-
There are hourly attachment charges for each Connect attachment. See Transit Gateway Connect Pricing for more details.
Featured APN Partners
AWS Partner Network (APN) help customers simplify and automate provisioning of Transit Gateway Connect. At this launch, AWS Transit Gateway Connect integrates with a number of industry-leading partners, including:
| 128 Technology | Partner Profile | Contact |
| Alkira, Inc. | Partner Profile | Contact |
| Arista Networks | Partner Profile | Contact |
| Aruba, a Hewlett Packard Enterprise company (HPE) | Partner Profile | Contact |
| Aryaka | Partner Profile | Contact |
| Aviatrix | Partner Profile | Contact |
| Cisco Systems (Cisco Cloud ACI, Cisco SD-WAN) | Partner Profile | Contact |
| Citrix | Partner Profile | Contact |
| Fortinet | Partner Profile | Contact |
| Palo Alto Networks (CloudGenix, VM-Series Virtual Firewall) | Partner Profile | Contact |
| Silver Peak, a Hewlett Packard Enterprise company (HPE) | Partner Profile | Contact |
| Sophos | Partner Profile | Contact |
| Versa Networks. | Partner Profile | Contact |
One can integrate to AWS Transit Gateway Connect by supporting GRE and BGP protocol in their network appliance and performing testing of appliance’s connectivity in the AWS environment. APN partners are welcome to reach out to their AWS Partner team for support with integration and related opportunities.
Conclusion
Transit Gateway Connect offers a native way to integrate your SD-WAN infrastructure into AWS. It helps you extend your SD-WAN into AWS without having to set up or manage IPsec VPNs between SD-WAN network virtual appliances and AWS Transit Gateway—reducing the complexity of integration, overall cost as well as significantly reducing operational overhead. To learn more and get started, please visit the Transit Gateway Connect frequently asked questions and documentation.
About the authors


