AWS Security Blog
Category: How-To
How to Manage Secrets for Amazon EC2 Container Service–Based Applications by Using Amazon S3 and Docker
Docker enables you to package, ship, and run applications as containers. This approach provides a comprehensive abstraction layer that allows developers to “containerize” or “package” any application and have it run on any infrastructure. Docker containers are analogous to shipping containers in that they provide a standard and consistent way of shipping almost anything. One […]
How to Use the REST API to Encrypt S3 Objects by Using AWS KMS
August 4, 2023: This blog post is out of date, and is in the process of being updated. AWS Key Management Service (AWS KMS) allows you to use keys under your control to encrypt data at rest stored in Amazon S3. The two primary methods for implementing this encryption are server-side encryption (SSE) and client-side […]
How to Automatically Tag Amazon EC2 Resources in Response to API Events
Note: As of March 28, 2017, Amazon EC2 supports tagging on creation, enforced tag usage, AWS Identity and Access Management (IAM) resource-level permissions, and enforced volume encryption. See New – Tag EC2 Instances & EBS Volumes on Creation on the AWS Blog for more information. Access to manage Amazon EC2 instances can be controlled using […]
How to Configure Your EC2 Instances to Automatically Join a Microsoft Active Directory Domain
Seamlessly joining Windows EC2 instances in AWS to a Microsoft Active Directory domain is a common scenario, especially for enterprises building a hybrid cloud architecture. With AWS Directory Service, you can target an Active Directory domain managed on-premises or within AWS. How to Connect Your On-Premises Active Directory to AWS Using AD Connector takes you […]
How to Control Access to Your Amazon Elasticsearch Service Domain
September 9, 2021: Amazon Elasticsearch Service has been renamed to Amazon OpenSearch Service. See details. With the recent release of Amazon Elasticsearch Service (Amazon ES), you now can build applications without setting up and maintaining your own search cluster on Amazon EC2. One of the key benefits of using Amazon ES is that you can […]
How to Optimize and Visualize Your Security Groups
September 9, 2021: Amazon Elasticsearch Service has been renamed to Amazon OpenSearch Service. See details. May 3, 2017: We published a related blog post also written by Guy Denney, How to Visualize and Refine Your Network’s Security by Adding Security Group IDs to Your VPC Flow Logs. Many organizations start their journey with AWS by experimenting […]
How to Import IP Address Reputation Lists to Automatically Update AWS WAF IP Blacklists
Note from July 3, 2017: The solution in this post has been integrated into AWS WAF Security Automations, and AWS maintains up-to-date solution code in the companion GitHub repository. You can use AWS WAF (a web application firewall) to help protect your web applications from exploits that originate from groups of IP addresses that are known […]
How to Set Up Federated Single Sign-On to AWS Using Google Apps
March 10, 2020: This blog post is out of date. Please refer to this post for updated info: How to set up federated single sign-on to AWS using Google Workspace The AWS Security Blog has covered a variety of solutions for federating single sign-on (SSO) to the AWS Management Console. For example, How to Connect […]
How to Enable Windows Integrated Authentication for RDS for SQL Server Using On-Premises Active Directory
On March 23, 2016, AWS announced that Amazon Relational Database Service for SQL Server (RDS for SQL Server) now supports authentication to AWS Directory Service for Microsoft Active Directory (Enterprise Edition), also known as Microsoft AD. On April 7, 2016, AWS launched a new console feature for Microsoft AD that makes it easy for you […]
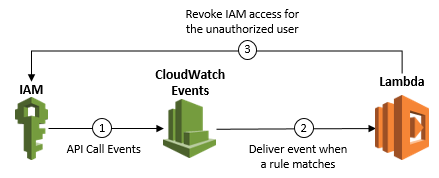
How to Detect and Automatically Revoke Unintended IAM Access with Amazon CloudWatch Events
Update on October 24, 2018: Note that if you do not author the Lambda function correctly, this setup can create an infinite loop (in this case, a rule that is fired repeatedly, which can impact your AWS resources and cause higher than expected charges to your account). The example Lambda function I provide in Step […]