AWS Security Blog
Category: How-To
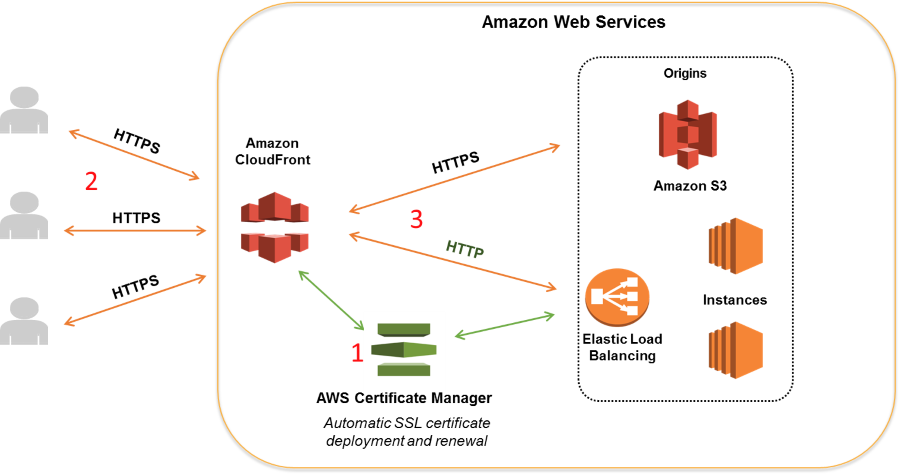
How to Help Achieve Mobile App Transport Security (ATS) Compliance by Using Amazon CloudFront and AWS Certificate Manager
Web and application users and organizations have expressed a growing desire to conduct most of their HTTP communication securely by using HTTPS. At its 2016 Worldwide Developers Conference, Apple announced that starting in January 2017, apps submitted to its App Store will be required to support App Transport Security (ATS). ATS requires all connections to […]
How to Create a Custom AMI with Encrypted Amazon EBS Snapshots and Share It with Other Accounts and Regions
August 31, 2021: AWS KMS is replacing the term customer master key (CMK) with AWS KMS key and KMS key. The concept has not changed. To prevent breaking changes, AWS KMS is keeping some variations of this term. More info. An Amazon Machine Image (AMI) provides the information required to launch an instance (a virtual […]
How to Use Amazon CloudWatch Events to Monitor Application Health
Amazon CloudWatch Events enables you to react selectively to events in the cloud as well as in your applications. Specifically, you can create CloudWatch Events rules that match event patterns, and take actions in response to those patterns. CloudWatch Events lets you process both AWS-provided events and custom events (those that you create and inject […]
How to Remove Single Points of Failure by Using a High-Availability Partition Group in Your AWS CloudHSM Environment
A hardware security module (HSM) is a hardware device designed with the security of your data and cryptographic key material in mind. It is tamper-resistant hardware that prevents unauthorized users from attempting to pry open the device, plug any extra devices in to access data or keys such as subtokens, or damage the outside housing. […]
How to Audit Cross-Account Roles Using AWS CloudTrail and Amazon CloudWatch Events
You can use AWS Identity and Access Management (IAM) roles to grant access to resources in your AWS account, another AWS account you own, or a third-party account. For example, you may have an AWS account used for production resources and a separate AWS account for development resources. Throughout this post, I will refer to […]
How to Use AWS CloudFormation to Automate Your AWS WAF Configuration with Example Rules and Match Conditions
Note from July 4, 2017: The solution in this post has been integrated into AWS WAF Security Automations, and AWS maintains up-to-date solution code in the companion GitHub repository. AWS WAF is a web application firewall that integrates closely with Amazon CloudFront (AWS’s content delivery network [CDN]). AWS WAF gives you control to allow or block […]
How to Use SAML to Automatically Direct Federated Users to a Specific AWS Management Console Page
Identity federation enables your enterprise users (such as Active Directory users) to access the AWS Management Console via single sign-on (SSO) by using their existing credentials. In Security Assertion Markup Language (SAML) 2.0, RelayState is an optional parameter that identifies a specified destination URL your users will access after signing in with SSO. When using […]
How to Prevent Uploads of Unencrypted Objects to Amazon S3
There are many use cases to prevent uploads of unencrypted objects to an Amazon S3 bucket, but the underlying objective is to protect the confidentiality and integrity of the objects stored in that bucket. AWS provides several services that help make this process easier, such as AWS Identity and Access Management (IAM) and AWS Key […]
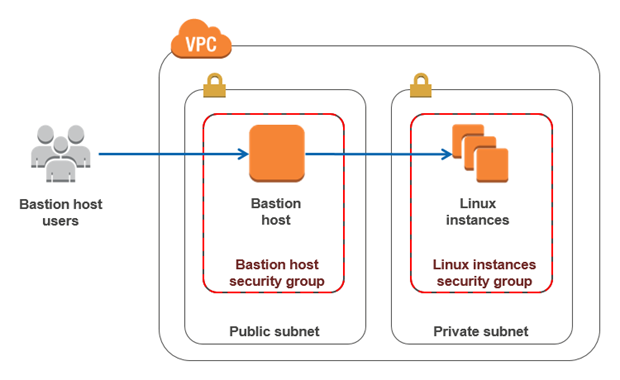
How to Record SSH Sessions Established Through a Bastion Host
A bastion host is a server whose purpose is to provide access to a private network from an external network, such as the Internet. Because of its exposure to potential attack, a bastion host must minimize the chances of penetration. For example, you can use a bastion host to mitigate the risk of allowing SSH […]
How to Set Up DNS Resolution Between On-Premises Networks and AWS by Using Unbound
In previous AWS Security Blog posts, Drew Dennis covered two options for establishing DNS connectivity between your on-premises networks and your Amazon Virtual Private Cloud (Amazon VPC) environments. His first post explained how to use Simple AD to forward DNS requests originating from on-premises networks to an Amazon Route 53 private hosted zone. His second […]