AWS Security Blog
Category: Security, Identity, & Compliance
AWS achieves ISO 22301:2019 certification
We’re excited to announce that Amazon Web Services (AWS) has successfully achieved ISO 22301:2019 certification without audit findings. ISO 22301:2019 is a rigorous third-party independent assessment of the international standard for Business Continuity Management (BCM). Published by the International Organization for Standardization (ISO), ISO 22301:2019 is designed to help organizations prevent, prepare for, respond to, […]
Get more out of service control policies in a multi-account environment
September 19, 2025: This post was updated to reflect that AWS Organizations now offers full IAM policy language support for service control policies (SCPs). Details of this new feature are outlined in this post. Many of our customers use AWS Organizations to manage multiple Amazon Web Services (AWS) accounts. There are many benefits to using […]
A sneak peek at the data protection and privacy sessions for AWS re:Inforce 2022
June 15, 2022: This post had been updated with reference to a blog post of Identity and access management added. Register now with discount code SALUZwmdkJJ to get $150 off your full conference pass to AWS re:Inforce. For a limited time only and while supplies last. Today we want to tell you about some of […]
Correlate IAM Access Analyzer findings with Amazon Macie
In this blog post, you’ll learn how to detect when unintended access has been granted to sensitive data in Amazon Simple Storage Service (Amazon S3) buckets in your Amazon Web Services (AWS) accounts. It’s critical for your enterprise to understand where sensitive data is stored in your organization and how and why it is shared. […]
AWS CSA Consensus Assessment Initiative Questionnaire version 4 now available
Amazon Web Services (AWS) has published an updated version of the AWS Cloud Security Alliance (CSA) Consensus Assessment Initiative Questionnaire (CAIQ). The questionnaire has been completed using the current CSA CAIQ standard, v4.0.2 (06.07.2021 update), and is now available for download. The CSA is a not-for-profit organization dedicated to “defining and raising awareness of best […]
Join me in Boston this July for AWS re:Inforce 2022
I’d like to personally invite you to attend the Amazon Web Services (AWS) security conference, AWS re:Inforce 2022, in Boston, MA on July 26–27. This event offers interactive educational content to address your security, compliance, privacy, and identity management needs. Join security experts, customers, leaders, and partners from around the world who are committed to […]
When and where to use IAM permissions boundaries
Customers often ask for guidance on permissions boundaries in AWS Identity and Access Management (IAM) and when, where, and how to use them. A permissions boundary is an IAM feature that helps your centralized cloud IAM teams to safely empower your application developers to create new IAM roles and policies in Amazon Web Services (AWS). […]
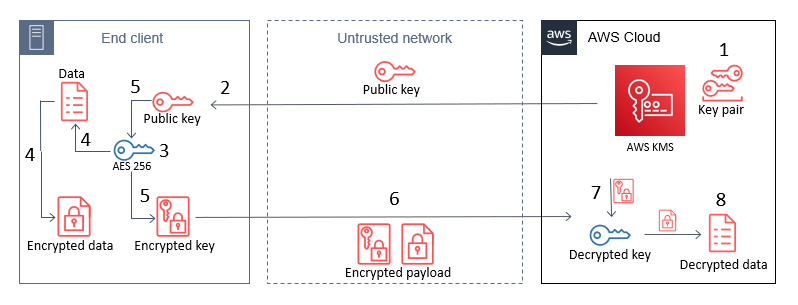
How to use AWS KMS RSA keys for offline encryption
October 28, 2022: This blog post has been updated to reflect that CBC has changed to CTR, as well as a few more modifications. This blog post discusses how you can use AWS Key Management Service (AWS KMS) RSA public keys on end clients or devices and encrypt data, then subsequently decrypt data by using […]
How to use regional SAML endpoints for failover
August 10, 2022: This blog post has been updated to reflect the new name of AWS Single Sign-On (SSO) – AWS IAM Identity Center. Read more about the name change here. Many Amazon Web Services (AWS) customers choose to use federation with SAML 2.0 in order to use their existing identity provider (IdP) and avoid […]
Spring 2022 SOC 2 Type I Privacy report now available
Your privacy considerations are at the core of our compliance work at Amazon Web Services (AWS), and we are focused on the protection of your content while using AWS services. Our Spring 2022 SOC 2 Type I Privacy report is now available, which provides customers with a third-party attestation of our system and the suitability […]