AWS Security Blog
Tag: authorization
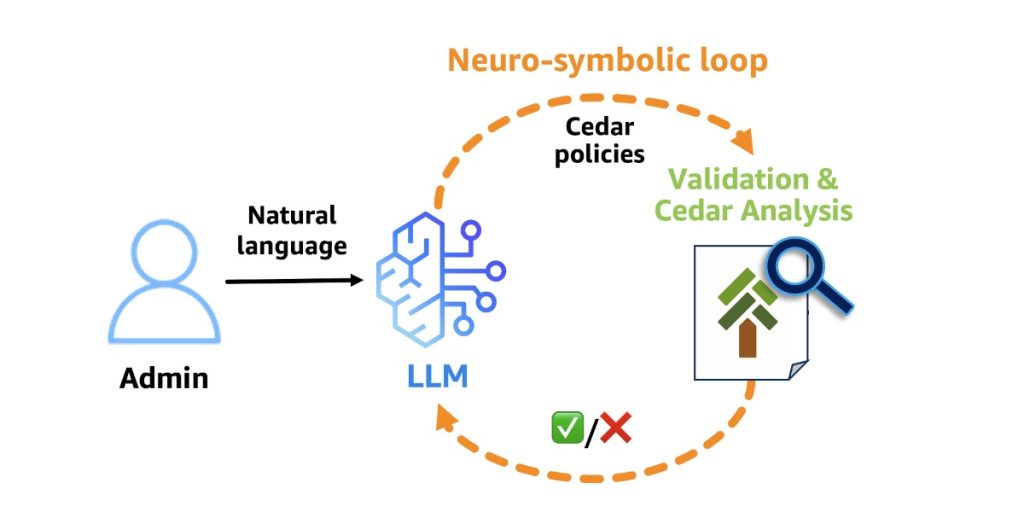
Why Policy in Amazon Bedrock AgentCore chose Cedar for securing agentic workflows
Agents have agency: they adapt and find multiple ways to solve problems. This autonomy creates a fundamental security challenge: the large language model (LLM) at the heart of the agent is non-deterministic, and its decisions can’t be predicted or guaranteed in advance. It can hallucinate harmful actions with complete confidence. It’s vulnerable to prompt injection […]
Secure your Express application APIs in minutes with Amazon Verified Permissions
June 23, 2025: We updated @verifiedpermissions/authorization-clients to @verifiedpermissions/authorization-clients-js to correctly reflect the name of the package on npm. Today, Amazon Verified Permissions announced the release of @verifiedpermissions/authorization-clients-js, an open source package that developers can use to implement external fine-grained authorization for Express.js web application APIs in minutes when using Verified Permissions. Express is a minimal […]
Connect your on-premises Kubernetes cluster to AWS APIs using IAM Roles Anywhere
February 26, 2025: We’ve updated this post to fix a typo in the code in Step 5 – Deploy your workload. Many customers want to seamlessly integrate their on-premises Kubernetes workloads with AWS services, implement hybrid workloads, or migrate to AWS. Previously, a common approach involved creating long-term access keys, which posed security risks and […]
Enhancing data privacy with layered authorization for Amazon Bedrock Agents
April 3, 2025: We’ve updated this post to reflect the new 2025 OWASP top 10 for LLM entries. Customers are finding several advantages to using generative AI within their applications. However, using generative AI adds new considerations when reviewing the threat model of an application, whether you’re using it to improve the customer experience for […]
Network perimeter security protections for generative AI
Generative AI–based applications have grown in popularity in the last couple of years. Applications built with large language models (LLMs) have the potential to increase the value companies bring to their customers. In this blog post, we dive deep into network perimeter protection for generative AI applications. We’ll walk through the different areas of network […]
AWS recognized as an Overall Leader in 2024 KuppingerCole Leadership Compass for Policy Based Access Management
Amazon Web Services (AWS) was recognized by KuppingerCole Analysts AG as an Overall Leader in the firm’s Leadership Compass report for Policy Based Access Management. The Leadership Compass report reveals Amazon Verified Permissions as an Overall Leader (as shown in Figure 1), a Product Leader for functional strength, and an Innovation Leader for open source […]
How to implement cryptographic modules to secure private keys used with IAM Roles Anywhere
AWS Identity and Access Management (IAM) Roles Anywhere enables workloads that run outside of Amazon Web Services (AWS), such as servers, containers, and applications, to use X.509 digital certificates to obtain temporary AWS credentials and access AWS resources, the same way that you use IAM roles for workloads on AWS. Now, IAM Roles Anywhere allows […]
How to monitor and query IAM resources at scale – Part 2
In this post, we continue with our recommendations for using AWS Identity and Access Management (IAM) APIs. In part 1 of this two-part series, we described how you could create IAM resources and use them soon after for authorization decisions. We also described options for monitoring and responding to IAM resource changes for entire accounts. […]
How to monitor and query IAM resources at scale – Part 1
March 7, 2023: We’ve fixed a typo in the blog post. In this two-part blog post, we’ll provide recommendations for using AWS Identity and Access Management (IAM) APIs, and we’ll share useful details on how IAM works so that you can use it more effectively. For example, you might be creating new IAM resources such as roles […]
Extend AWS IAM roles to workloads outside of AWS with IAM Roles Anywhere
AWS Identity and Access Management (IAM) has now made it easier for you to use IAM roles for your workloads that are running outside of AWS, with the release of IAM Roles Anywhere. This feature extends the capabilities of IAM roles to workloads outside of AWS. You can use IAM Roles Anywhere to provide a […]