AWS Security Blog
Tag: Containers
Amazon Elastic Kubernetes Service gets independent affirmation of its zero operator access design
Today, we’re excited to announce the independent affirmation of our Amazon Elastic Kubernetes Service (Amazon EKS) zero operator access posture. Because security is our top priority at Amazon Web Services (AWS), we designed an operational architecture to meet the data privacy posture our regulated and most stringent customers want in a managed Kubernetes service, giving […]
Manage authorization within a containerized workload using Amazon Verified Permissions
Containerization offers organizations significant benefits such as portability, scalability, and efficient resource utilization. However, managing access control and authorization for containerized workloads across diverse environments—from on-premises to multi-cloud setups—can be challenging. This blog post explores four architectural patterns that use Amazon Verified Permissions for application authorization in Kubernetes environments. Verified Permissions is a scalable permissions management and fine-grained […]
Making sense of secrets management on Amazon EKS for regulated institutions
Amazon Web Services (AWS) customers operating in a regulated industry, such as the financial services industry (FSI) or healthcare, are required to meet their regulatory and compliance obligations, such as the Payment Card Industry Data Security Standard (PCI DSS) or Health Insurance Portability and Accountability Act (HIPPA). AWS offers regulated customers tools, guidance and third-party audit reports […]
How to create a pipeline for hardening Amazon EKS nodes and automate updates
July 16, 2024: We updated the code in this post and some of the CloudFormation parameters. Amazon Elastic Kubernetes Service (Amazon EKS) offers a powerful, Kubernetes-certified service to build, secure, operate, and maintain Kubernetes clusters on Amazon Web Services (AWS). It integrates seamlessly with key AWS services such as Amazon CloudWatch, Amazon EC2 Auto Scaling, […]
How to use AWS Secrets Manager and ABAC for enhanced secrets management in Amazon EKS
In this post, we show you how to apply attribute-based access control (ABAC) while you store and manage your Amazon Elastic Kubernetes Services (Amazon EKS) workload secrets in AWS Secrets Manager, and then retrieve them by integrating Secrets Manager with Amazon EKS using External Secrets Operator to define more fine-grained and dynamic AWS Identity and […]
Best Practices to help secure your container image build pipeline by using AWS Signer
AWS Signer is a fully managed code-signing service to help ensure the trust and integrity of your code. It helps you verify that the code comes from a trusted source and that an unauthorized party has not accessed it. AWS Signer manages code signing certificates and public and private keys, which can reduce the overhead […]
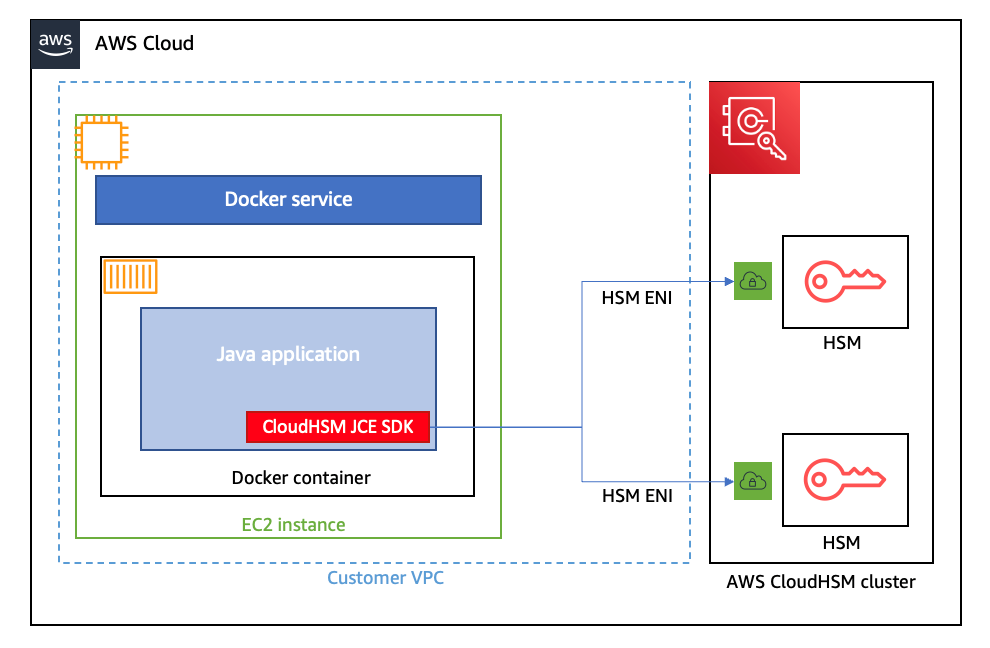
How to run AWS CloudHSM workloads in container environments
January 25, 2023: We updated this post to reflect the fact that CloudHSM SDK3 does not support serverless environments and we strongly recommend deploying SDK5. AWS CloudHSM provides hardware security modules (HSMs) in the AWS Cloud. With CloudHSM, you can generate and use your own encryption keys in the AWS Cloud, and manage your keys […]
How to investigate and take action on security issues in Amazon EKS clusters with Amazon Detective – Part 2
March 15, 2023: We’ve updated this post to incorporate a section to investigate VPC flow logs. In part 1 of this of this two-part series, How to detect security issues in Amazon EKS cluster using Amazon GuardDuty, we walked through a real-world observed security issue in an Amazon Elastic Kubernetes Service (Amazon EKS) cluster and […]
How to detect security issues in Amazon EKS clusters using Amazon GuardDuty – Part 1
In this two-part blog post, we’ll discuss how to detect and investigate security issues in an Amazon Elastic Kubernetes Service (Amazon EKS) cluster with Amazon GuardDuty and Amazon Detective. Amazon Elastic Kubernetes Service (Amazon EKS) is a managed service that you can use to run and scale container workloads by using Kubernetes in the AWS […]
Use Amazon Inspector to manage your build and deploy pipelines for containerized applications
Amazon Inspector is an automated vulnerability management service that continually scans Amazon Web Services (AWS) workloads for software vulnerabilities and unintended network exposure. Amazon Inspector currently supports vulnerability reporting for Amazon Elastic Compute Cloud (Amazon EC2) instances and container images stored in Amazon Elastic Container Registry (Amazon ECR). With the emergence of Docker in 2013, […]