AWS Security Blog
TLS 1.2 to become the minimum TLS protocol level for all AWS API endpoints
February 27, 2024: AWS has completed our global updates to deprecate support for TLS 1.0 and TLS 1.1 versions on our AWS service API endpoints across each of our AWS Regions and Availability Zones.
January 17, 2024: Over 96% of AWS service API endpoints have ended support for TLS versions 1.0 and 1.1. Over the next six weeks, the remaining services will complete updates to their TLS configuration to require a minimum of TLS version 1.2. We will update this post again when the changes are globally complete across AWS Regions and Availability Zones.
September 28, 2023: AWS GovCloud (US) is complete, which means that AWS now enforces use of TLS 1.2+ across all AWS GovCloud (US) public API endpoints.
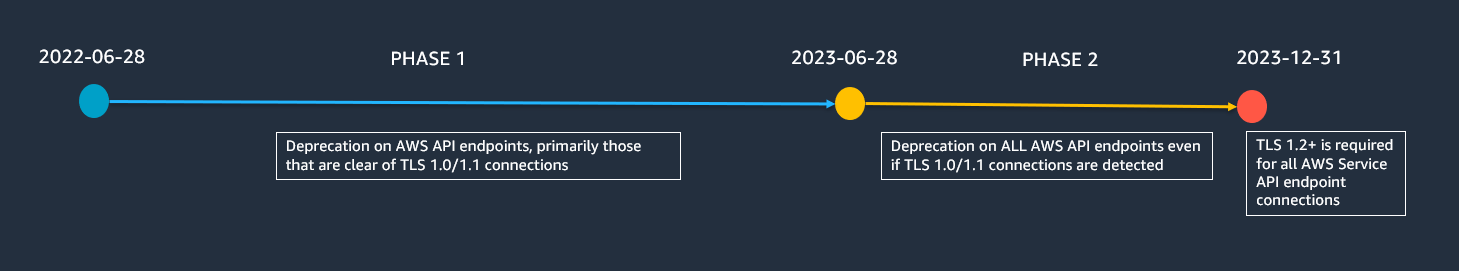
June 1, 2023: This blog post has been updated to add a timeline to clarify the key dates. To avoid a disruption to your AWS workloads, you must update all of your TLS 1.0/ 1.1 software clients no later than 06/28/23.
May 23, 2023: This post was revised to indicate that we are continuing to gradually update AWS API endpoints to TLS 1.2 minimum policies between now and December 31, 2023. We have also added a reference to our new blog post announcing efforts to enable TLS 1.3.
April 25, 2023: We’ve updated this blog post to include more security learning resources.
April 5, 2023: This post was updated with new references to add the newly recorded Our AWS Supports You | Updating Your Clients to TLS 1.2 session, we added an option for S3 customers to use the Amazon S3 server-access logs to analyze if they are at risk, and lastly we added a link to the AWS Pricing page for further information on associated costs that may be incurred to identify your use of outdated TLS.
At Amazon Web Services (AWS), we continuously innovate to deliver you a cloud computing environment that works to help meet the requirements of the most security-sensitive organizations. To respond to evolving technology and regulatory standards for Transport Layer Security (TLS), we will be updating the TLS configuration for all AWS service API endpoints to a minimum of version TLS 1.2. This update means you will need to use of TLS versions 1.2 or higher for your connections, with a continued gradual rollout that will complete by December 31, 2023. In this post, we will tell you how to check your TLS version, and what to do to prepare.
We have continued AWS support for TLS versions 1.0 and 1.1 to maintain backward compatibility for customers that have older or difficult to update clients, such as embedded devices. Furthermore, we have active mitigations in place that help protect your data for the issues identified in these older versions. Now is the right time to retire TLS 1.0 and 1.1, because increasing numbers of customers have requested this change to help simplify part of their regulatory compliance, and there are fewer and fewer customers using these older versions.
If you are one of the more than 99% of AWS customers who are already using TLS 1.2 or later, you will not be impacted by this change. You are almost certainly already using TLS 1.2 or later if your client software application was built after 2014 using an AWS Software Development Kit (AWS SDK), AWS Command Line Interface (AWS CLI), Java Development Kit (JDK) 8 or later, or another modern development environment. If you are using earlier application versions, or have not updated your development environment since before 2014, you will likely need to update.
If you are one of the customers still using TLS 1.0 or 1.1, then you must update your client software to use TLS 1.2 or later to maintain your ability to connect. It is important to understand that you already have control over the TLS version used when connecting. When connecting to AWS API endpoints, your client software negotiates its preferred TLS version, and AWS uses the highest mutually agreed upon version.
To minimize the availability impact of requiring TLS 1.2, AWS is continuing to rollout the changes on an endpoint-by-endpoint basis. Before making these potentially breaking changes, we monitor for connections that are still using TLS 1.0 or TLS 1.1. If you are one of the AWS customers who may be impacted, we will notify you on your AWS Health Dashboard, and by email. After June 28, 2023, AWS will update our API endpoint configuration to remove TLS 1.0 and TLS 1.1, even if you still have connections using these versions.
We have a video presentation available on this project from AWS re:Inforce 2022 called ‘Uplifting AWS service API data protection to TLS 1.2+:
What should you do to prepare for this update?
To minimize your risk, you can self-identify if you have any connections using TLS 1.0 or 1.1. If you find any connections using TLS 1.0 or 1.1, you should update your client software to use TLS 1.2 or later.
AWS CloudTrail records are especially useful to identify if you are using the outdated TLS versions. You can now search for the TLS version used for your connections by using the recently added tlsDetails field. The tlsDetails structure in each CloudTrail record contains the TLS version, cipher suite, and the client-provided host name used in the service API call, which is typically the fully qualified domain name (FQDN) of the service endpoint. You can then use the data in the records to help you pinpoint your client software that is responsible for the TLS 1.0 or 1.1 call, and update it accordingly. Over half of AWS services currently provide the TLS information in the CloudTrail tlsDetails field, and we are continuing to roll this out for the remaining services in the coming months.
We recommend you use one of the following options for running your CloudTrail TLS queries. Please note that these options may incur cost, please refer to the relevant service’s pricing via the AWS Pricing page.
- AWS CloudTrail Lake: You can follow the steps, and use the sample TLS query, in the blog post Using AWS CloudTrail Lake to identify older TLS connections. There is also a built-in sample CloudTrail TLS query available in the AWS CloudTrail Lake console.
- Amazon CloudWatch Log Insights: There are two built-in CloudWatch Log Insights sample CloudTrail TLS queries that you can use, as shown in Figure 2.

Figure 2: Available sample TLS queries for CloudWatch Log Insights
- Amazon Athena: You can query AWS CloudTrail logs in Amazon Athena, and in November 2022 we added support for querying the TLS values in your CloudTrail logs.
- Amazon S3 server-access logs are an option for Amazon S3 customers to view detailed requests to your S3 buckets, including data connections such as GetObject.
In addition to using CloudTrail data, you can also identify the TLS version used by your connections by performing code, network, or log analysis as described in the blog post TLS 1.2 will be required for all AWS FIPS endpoints. Note that while this post refers to the FIPS API endpoints, the information about querying for TLS versions is applicable to all API endpoints.
Will I be notified if I am using TLS 1.0 or TLS 1.1?
If we detect that you are using TLS 1.0 or 1.1, you will be notified on your AWS Health Dashboard, and you will receive email notifications. However, you will not receive a notification for connections you make anonymously to AWS shared resources, such as a public Amazon Simple Storage Service (Amazon S3) bucket, because we cannot identify anonymous connections. Furthermore, while we will make every effort to identify and notify every customer, there is a possibility that we may not detect infrequent connections, such as those that occur less than monthly.
How do I update my client to use TLS 1.2 or TLS 1.3?
If you are using an AWS Software Developer Kit (AWS SDK) or the AWS Command Line Interface (AWS CLI), follow the detailed guidance about how to examine your client software code and properly configure the TLS version used in the blog post TLS 1.2 to become the minimum for FIPS endpoints. There is also information provided on identifying and updating the TLS version in your client in our AWS re:Inforce 2022 presentation Uplifting AWS service API data protection to TLS 1.2+ (DPP202).
We encourage you to be proactive in order to avoid an impact to availability. Also, we recommend that you test configuration changes in a staging environment before you introduce them into production workloads.
What is the most common use of TLS 1.0 or TLS 1.1?
The most common use of TLS 1.0 or 1.1 are .NET Framework versions earlier than 4.6.2. If you use the .NET Framework, please confirm you are using version 4.6.2 or later. For information about how to update and configure the .NET Framework to support TLS 1.2, see How to enable TLS 1.2 on clients in the .NET Configuration Manager documentation or this re:post article.
What is Transport Layer Security (TLS)?
Transport Layer Security (TLS) is a cryptographic protocol that secures internet communications. Your client software can be set to use TLS version 1.0, 1.1, 1.2, or 1.3, or a subset of these, when connecting to service endpoints. You should ensure that your client software supports TLS 1.2 or later. You can visit our May 23, 2023 blog post on our efforts to add TLS 1.3.
Is there more assistance available to help verify or update my client software?
This video, Our AWS Supports You: Updating Your Clients to TLS 1.2 session, provides additional detail about this upcoming change, provides a walkthrough of AWS CloudTrail Lake, and shares guidance on how to update your software clients.
If you have any questions or issues, you can start a new thread on the AWS re:Post community, or you can contact AWS Support or your Technical Account Manager (TAM).
Additionally, you can use AWS IQ to find, securely collaborate with, and pay AWS certified third-party experts for on-demand assistance to update your TLS client components. To find out how to submit a request, get responses from experts, and choose the expert with the right skills and experience, see the AWS IQ page. Sign in to the AWS Management Console and select Get Started with AWS IQ to start a request.
If you own an Amazon Simple Storage Service (Amazon S3) bucket that your customers use to access content using TLS 1.0 or TLS 1.1, you may follow this AWS Knowledge Base guidance on “How do I allow access to my Amazon S3 buckets to customers who do not use TLS 1.2 or higher?“. Please note that you can also enforce use of TLS 1.2 or higher for all connections to your S3 buckets as per this AWS Knowledge Base guidance.
If you have feedback about this post, submit comments in the Comments section below.
Want more AWS Security how-to content, news, and feature announcements? Follow us on Twitter.