AWS Security Blog
Use the New Visual Editor to Create and Modify Your AWS IAM Policies
Today, AWS Identity and Access Management (IAM) made it easier for you to create and modify your IAM policies by using a point-and-click visual editor in the IAM console. The new visual editor guides you through granting permissions for IAM policies without requiring you to write policies in JSON (although you can still author and edit policies in JSON, if you prefer). This update to the IAM console makes it easier to grant least privilege for the AWS service actions you select by listing all the supported resource types and request conditions you can specify. Policy summaries identify unrecognized services and actions and permissions errors when you import existing policies, and now you can use the visual editor to correct them. In this blog post, I give a brief overview of policy concepts and show you how to create a new policy by using the visual editor.
IAM policy concepts
You use IAM policies to define permissions for your IAM entities (groups, users, and roles). Policies are composed of one or more statements that include the following elements:
- Effect: Determines if a policy statement allows or explicitly denies access.
- Action: Defines AWS service actions in a policy (these typically map to individual AWS APIs.)
- Resource: Defines the AWS resources to which actions can apply. The defined resources must be supported by the actions defined in the Action element for permissions to be granted.
- Condition: Defines when a permission is allowed or denied. The conditions defined in a policy must be supported by the actions defined in the Action element for the permission to be granted.
To grant permissions, you attach policies to groups, users, or roles. Now that I have reviewed the elements of a policy, I will demonstrate how to create an IAM policy with the visual editor.
How to create an IAM policy with the visual editor
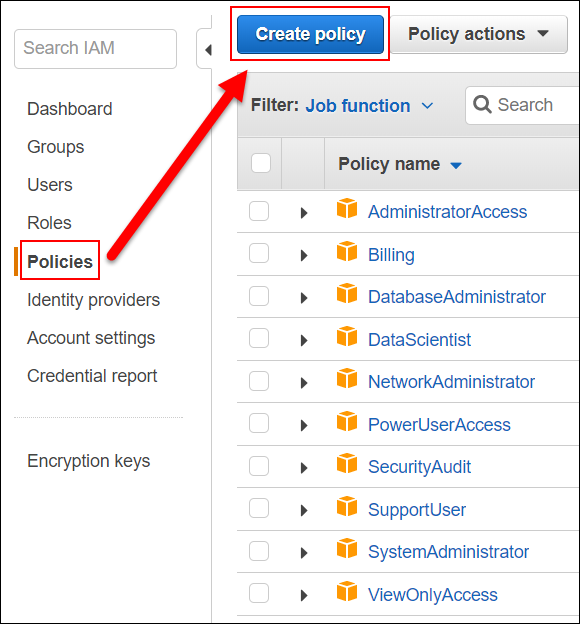
Let’s say my human resources (HR) recruiter, Casey, needs to review files located in an Amazon S3 bucket for all the product manager (PM) candidates our HR team has interviewed in 2017. To grant this access, I will create and attach a policy to Casey that grants list and limited read access to all folders that begin with PM_Candidate in the pmrecruiting2017 S3 bucket. To create this new policy, I navigate to the Policies page in the IAM console and choose Create policy. Note that I could also use the visual editor to modify existing policies by choosing Import existing policy; however, for Casey, I will create a new policy.
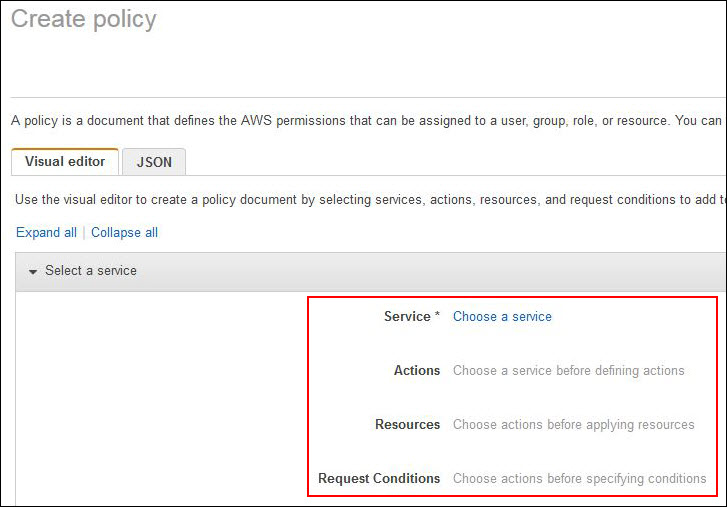
On the Visual editor tab, I see a section that includes Service, Actions, Resources, and Request Conditions.
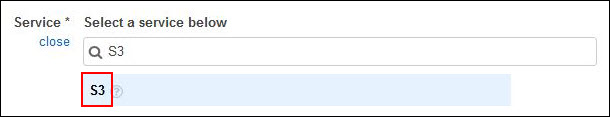
Select a service
To grant S3 permissions, I choose Select a service, type S3 in the search box, and choose S3 from the list.
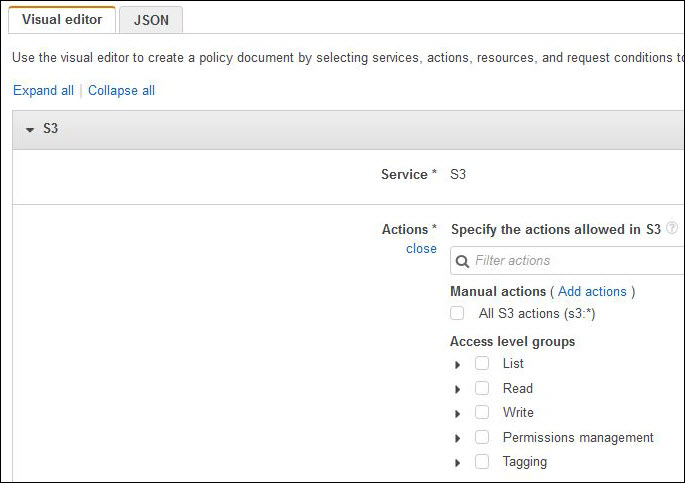
Select actions
After selecting S3, I can define actions for Casey by using one of four options:
- Filter actions in the service by using the search box.
- Type actions by choosing Add action next to Manual actions. For example, I can type List* to grant all S3 actions that begin with List*.
- Choose access levels from List, Read, Write, Permissions management, and Tagging.
- Select individual actions by expanding each access level.
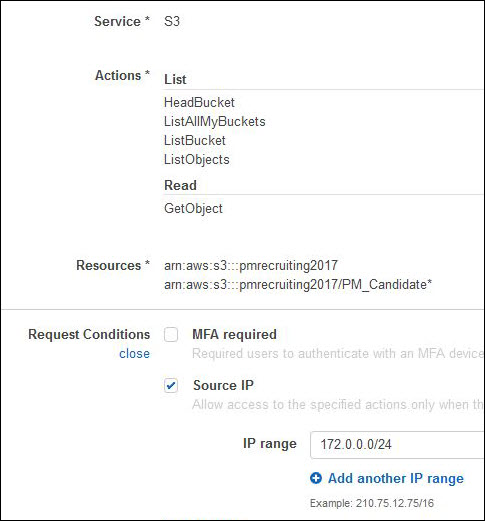
In the following screenshot, I choose options 3 and 4, and choose List and s3:GetObject from the Read access level.
We introduced access levels when we launched policy summaries earlier in 2017. Access levels give you a way to categorize actions and help you understand the permissions in a policy. The following table gives you a quick overview of access levels.
| Access level | Description | Example actions |
| List | Actions that allow you to see a list of resources | s3:ListBucket, s3:ListAllMyBuckets |
| Read | Actions that allow you to read the content in resources | s3:GetObject, s3:GetBucketTagging |
| Write | Actions that allow you to create, delete, or modify resources | s3:PutObject, s3:DeleteBucket |
| Permissions management | Actions that allow you to grant or modify permissions to resources | s3:PutBucketPolicy |
| Tagging | Actions that allow you to create, delete, or modify tags Note: Some services support authorization based on tags. |
s3:PutBucketTagging, s3:DeleteObjectVersionTagging |
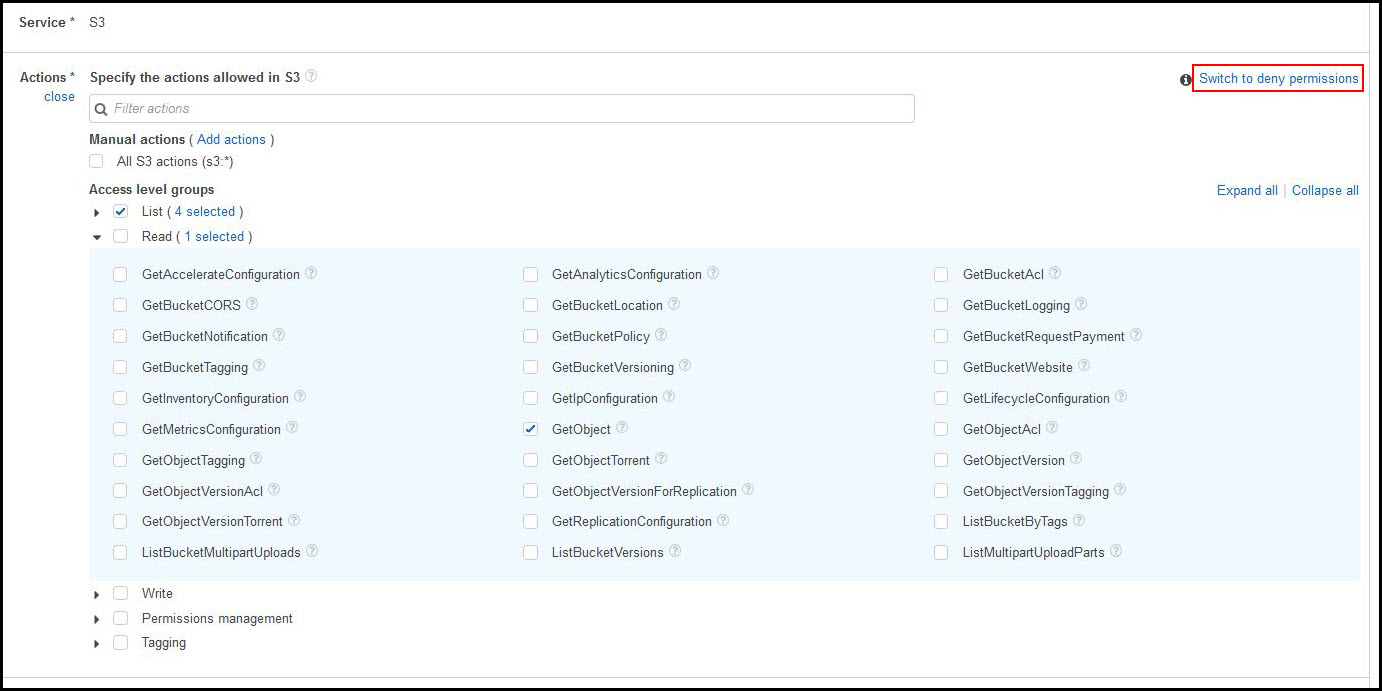
Note: By default, all actions you choose will be allowed. To deny actions, choose Switch to deny permissions in the upper right corner of the Actions section.
As shown in the preceding screenshot, if I choose the question mark icon next to GetObject, I can see the description and supported resources and conditions for this action, which can help me scope permissions.

The visual editor makes it easy to decide which actions I should select by providing in an integrated documentation panel the action description, supported resources or conditions, and any required actions for every AWS service action. Some AWS service actions have required actions, which are other AWS service actions that need to be granted in a policy for an action to run. For example, the AWS Directory Service action, ds:CreateDirectory, requires seven Amazon EC2 actions to be able to create a Directory Service directory.
Choose resources
In the Resources section, I can choose the resources on which actions can be taken. I choose Resources and see two ways that I can define or select resources:
- Define specific resources
- Select all resources
Specific is the default option, and only the applicable resources are presented based on the service and actions I chose previously. Because I want to grant Casey access to some objects in a specific bucket, I choose Specific and choose Add ARN under bucket.
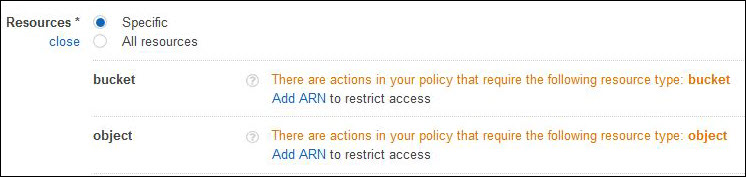
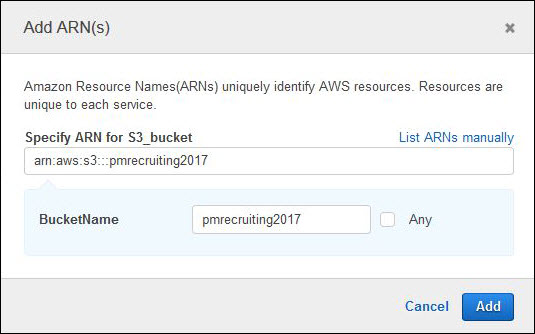
In the pop-up, I type the bucket name, pmrecruiting2017, and choose Add to specify the S3 bucket resource.
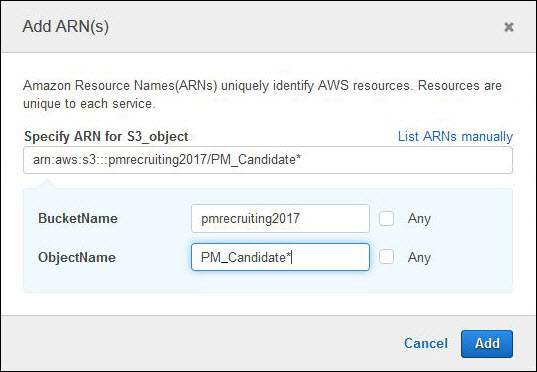
To specify the objects, I choose Add ARN under object and grant Casey access to all objects starting with PM_Candidate in the pmrecruiting2017 bucket. The visual editor helps you build your Amazon Resource Name (ARN) and validates that it is structured correctly. For AWS services that are AWS Region specific, the visual editor prompts for AWS Region and account number.
The visual editor displays all applicable resources in the Resources section based on the actions I choose. For Casey, I defined an S3 bucket and object in the Resources section. In this example, when the visual editor creates the policy, it creates three statements. The first statement includes all actions that require a wildcard (*) for the Resource element because this action does not support resource-level permissions. The second statement includes all S3 actions that support an S3 bucket. The third statement includes all actions that support an S3 object resource. The visual editor generates policy syntax for you based on supported permissions in AWS services.
Specify request conditions
For additional security, I specify a condition to restrict access to the S3 bucket from inside our internal network. To do this, I choose Specify request conditions in the Request Conditions section, and choose the Source IP check box. A condition is composed of a condition key, an operator, and a value. I choose aws:SourceIp for my Key so that I can control from where the S3 files can be accessed. By default, IpAddress is the Operator, and I set the Value to my internal network.

To add other conditions, choose Add condition and choose Save changes after choosing the key, operator, and value.
After specifying my request condition, I am now able to review all the elements of these S3 permissions.
Next, I can choose to grant permissions for another service by choosing Add new permissions (bottom left of preceding screenshot), or I can review and create this new policy. Because I have granted all the permissions Casey needs, I choose Review policy. I type a name and a description, and I review the policy summary before choosing Create policy.
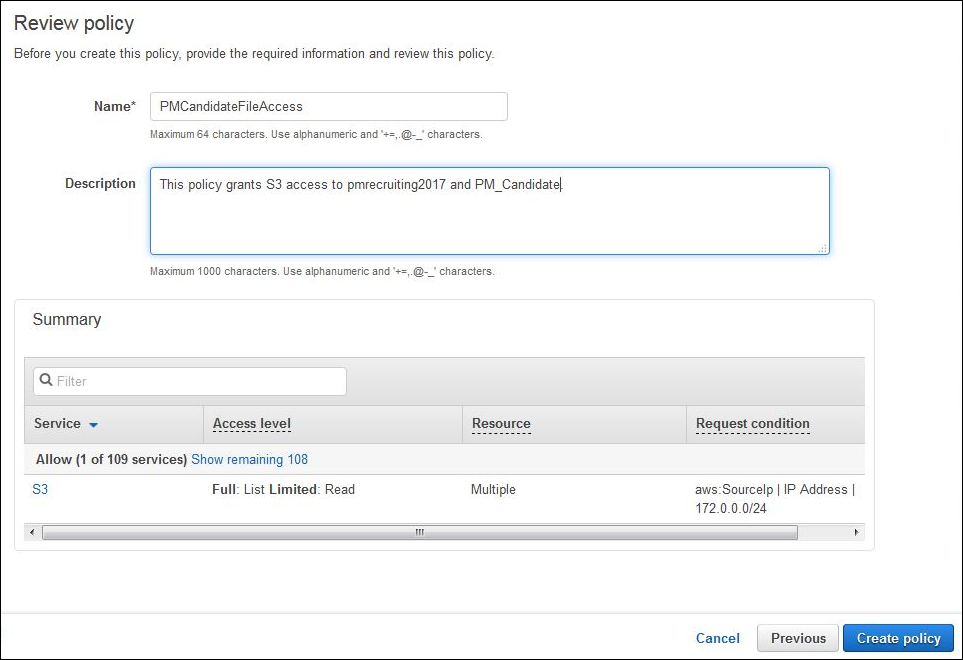
Now that I have created the policy, I attach it to Casey by choosing the Attached entities tab of the policy I just created. I choose Attach and choose Casey. I then choose Attach policy. Casey should now be able to access the interview files she needs to review.
Summary
The visual editor makes it easier to create and modify your IAM policies by guiding you through each element of the policy. The visual editor helps you define resources and request conditions so that you can grant least privilege and generate policies. To start using the visual editor, sign in to the IAM console, navigate to the Policies page, and choose Create policy.
If you have comments about this post, submit them in the “Comments” section below. If you have questions about or suggestions for this solution, start a new thread on the IAM forum.
– Joy
Want more AWS Security how-to content, news, and feature announcements? Follow us on Twitter.