AWS Partner Network (APN) Blog
Automate Istio-Enabled Amazon EKS Cluster Deployment with Tetrate’s EKS Blueprints Add-On
By Petr McAllister, Solutions Architect – Tetrate
By Mikhail Shapirov, Principal Partner Solutions Architect – AWS
 |
| Tetrate |
 |
Istio and Envoy have become key technologies in the modern application stack, especially for enterprises adopting Zero Trust security standards for microservices applications.
Tetrate is an AWS Partner that was started by Istio and Envoy founders and maintainers to reimagine application networking, and part of the nuts and bolts of that mission is operationalizing service mesh configuration, deployment, and management.
Using standardized tooling from Amazon Web Services (AWS) and Tetrate, it’s easier than ever to fully integrate Amazon Elastic Kubernetes Service (Amazon EKS) and Istio into modern, declarative infrastructure-as-code (IaC) deployment processes.
In this post, we’ll show how to use EKS Blueprints with Tetrate’s Istio add-on to stand up fully bootstrapped clusters in a declarative way that works seamlessly with modern GitOps tools and processes.
Standardize Automation with EKS Blueprints
From its experience working with enterprise customers across industries, Tetrate sees organizations commonly divide the process of setting up new Kubernetes clusters into the following manageably-sized chunks:
- Provision node hosts.
- Configure operating system (OS) and networking on those nodes.
- Install Kubernetes on each node.
- Join the nodes to the cluster.
- Deploy applications.
- In parallel, the infrastructure team may deploy additional components.
Every organization approaches these operations a little differently, especially when it comes to automation tooling. Often, different teams in the same organization have—by necessity—developed their own bespoke set of tools and processes. Unfortunately, the operational friction from this lack of common tooling harms agility and reliability.
The Amazon EKS ecosystem has popular tools such as eksctl and AWS CloudFormation that go a long way towards providing a standard automation kit.
Announced in April 2022, EKS Blueprints, coupled with the wide and expanding range of EKS add-ons, go even farther to facilitate an open, cross-platform ecosystem for extensible automation that covers popular open source and commercial products, including service mesh deployments.
Tetrate’s EKS Add-On for Istio with Tetrate Istio Distro
To contribute Tetrate’s Istio service mesh expertise to the Amazon EKS ecosystem, Tetrate has developed an EKS Blueprint add-on you can use to deploy Istio to newly-created or existing clusters, addressing both Day 1 and Day 2 concerns.
Tetrate’s Istio add-on is built using Tetrate Istio Distro (TID), an open-source project that aims to make adopting, managing, and updating Istio safe and easy. TID offers a vetted, upstream distribution of Istio—a hardened image of Istio that is simpler to install, manage, and upgrade.
TID is tested and optimized for EKS and Amazon EKS Anywhere by Tetrate, providing vetted builds of Istio and a command line interface (CLI) that facilitates acquiring, installing, and configuring multiple TID versions. Tetrate Istio Distro also offers FIPS 140-2 verified Istio builds for FedRAMP environments.
How it Works
Tetrate’s Istio add-on, based on the open-source EKS Blueprints for Terraform project, is available on GitHub and contains example code you can use to get started.
In the following tutorial, we’ll show how to use Tetrate’s Istio add-on to deploy an EKS cluster that’s fully bootstrapped with Tetrate Istio Distro binaries.
Step 1 – Clone the repository:
Step 2 – Move to the demo directory and initialize Terraform. The following output is shortened for brevity (you may see warnings about experimental features):
Step 3 – Create a Terraform execution plan. This step lets you preview the changes that Terraform plans to make to your infrastructure. The following output is also shortened for brevity:
Step 4 – Deploy the infrastructure with “terraform apply.” This step will:
- Reiterate the values presented during “terraform plan” for review.
- Prompt you for confirmation to apply the plan to your infrastructure.
- Apply the plan to your infrastructure.
This step may take up to 30-45 minutes to complete, after which you’ll be presented with the kubectl command to access the cluster.
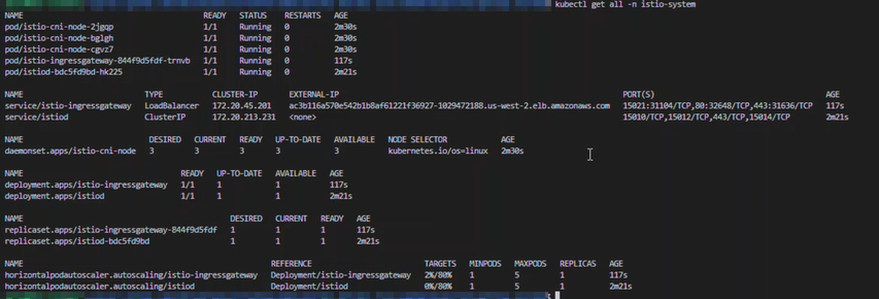
Step 5 – Validate the deployment. Executing kubectl get all -n istio-system should show you the newly-deployed Istio resources, similar to the following screenshot:
Figure 1 – Deployment validation screenshot.
As you can see, in a few short, repeatable steps we were able to deploy a fully-functional, Istio-enabled EKS cluster.
The EKS Blueprints with Istio add-on can be added to a CI/CD pipeline which, when using a declarative GitOps tool such as ArgoCD, enables a complete GitOps approach to EKS and Istio deployment.
Advantages of EKS Blueprints with Tetrate’s Istio Add-On
There are a number of advantages to using EKS Blueprints and Tetrate’s Istio add-on:
- A single command kicks off a repeatable, predictable process to fully deploy Kubernetes with Istio, configured the same way every time.
- Using Terraform lets you participate in its large ecosystem.
- Using Tetrate Istio Distro ensures hardened, tested, and verified Istio binaries with available support.
Bridge Cloud and Datacenter Applications with Tetrate Service Bridge
Tetrate Service Bridge (TSB) is a service mesh management plane that provides central management of networking, security, and observability for your entire application fleet—across Kubernetes clusters, virtual machines (VMs) and bare metal servers, and across clouds and on-premises deployments.
At its core, Tetrate Service Bridge manages multiple instances of Istio and Envoy, coordinating their configuration to apply security and traffic policies consistently across all of your application environments.
TSB is also a “bridge” between your organization—its people, teams, and applications—and your compute infrastructure, making it easy to assign consistent policies and access rights so your teams can safely control application resources.
Modernize Security with Built-in Zero Trust Architecture
Protect your applications and support compliance efforts with TSB’s Zero Trust architecture.
Multi-Tenancy
Group resources into a logical hierarchy that cuts across underlying physical infrastructure, allowing security policy to encompass whole applications and lines of business beyond just individual VMs or pods. Isolation between applications mitigates shared-fate outages and the impact of noisy neighbors.
User Access Policy
Import your corporate identity provider (LDAP or Active Directory, for example) and map your organization’s users and groups to resource permissions. Isolate access along organizational boundaries for compliance and prevent teams from stepping on each other’s toes.
Runtime Access Policy
Transparently configure runtime security policies like mTLS and end-user authentication along application and tenancy boundaries.
Service Identity
Gain finer control over network security than IP or network-based access policies. Decouple policies from the underlying network to make them portable across environments. Control service-to-service access, limiting the surface area for a potential pivot by an intruder.
Cascading Hierarchical Policy
Apply policy up and down your resource hierarchy. Give security teams the power to transparently implement cross-application policies like mTLS, plus view and audit the entire infrastructure, while tailoring controls for application developers to the unique requirements of the business. Provide security guardrails for developers, who can then focus on business value instead of security concerns.
Auditability
Audit every resource at the push of a button with detailed, fine-grained data about who changed what and when.
Increase Business Agility and Continuity with Global Connectivity
Easily control traffic flow to and between services across your entire application infrastructure with centralized management and global enforcement.
Application Edge and Ingress Gateways
Use tiered application gateways to intelligently route traffic to its final destination. Load balance across clusters with the multi-tenant first-tier application edge gateway. Provide ownership-based traffic isolation with dedicated application ingress gateways to specific workloads.
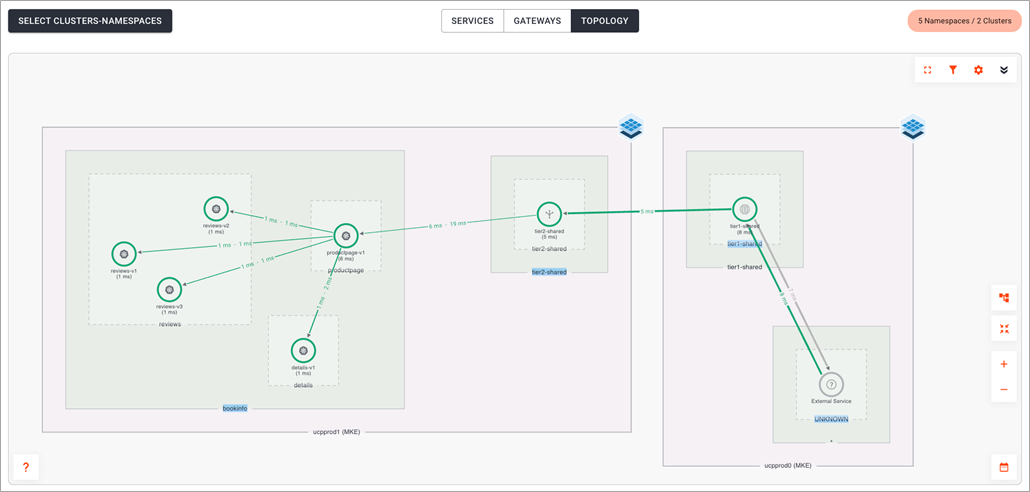
Topography-Aware Routing, Seamless Failover, Global Visibility
Gain fine-grained control over application connectivity with intelligent, per-request routing based on a global application topography. Keep traffic as local as possible, but shift automatically to other clusters when needed for availability. Gain real-time insight into application health, connectivity, and controls.
Multi-Cluster Routing
Make multi-cluster management easy and service more requests with higher availability. Decouple routing configuration from underlying infrastructure to route across clusters as simply as within them.
API Gateway Capabilities, Everywhere
Add API gateway functionality wherever you need it—not just at a single gateway. Give application teams API-based control with OpenAPI spec annotations to configure traffic flow. Avoid hairpin traffic common to traditional API gateway topologies.
Take advantage of these capabilities available in every Envoy instance:
- Authn/z
- Rate limiting
- Fault tolerance via timeouts, retries, and circuit breakers
- CORS policy configuration
- WAF policy
- Request transformation via WASM
Traffic Splitting and Migrations
Keep your applications available, even while migrating to the cloud or moving from monoliths to microservices. Define how traffic flows to different versions in different parts of your infrastructure. Use TSB’s built-in observability capabilities to gain confidence in application updates before a full release—or easily roll back to a known-good state before customers notice a problem.
See Everything with Global Observability
Gain consistent observability data from all of your applications transparently, without relying on application teams to build in instrumentation.
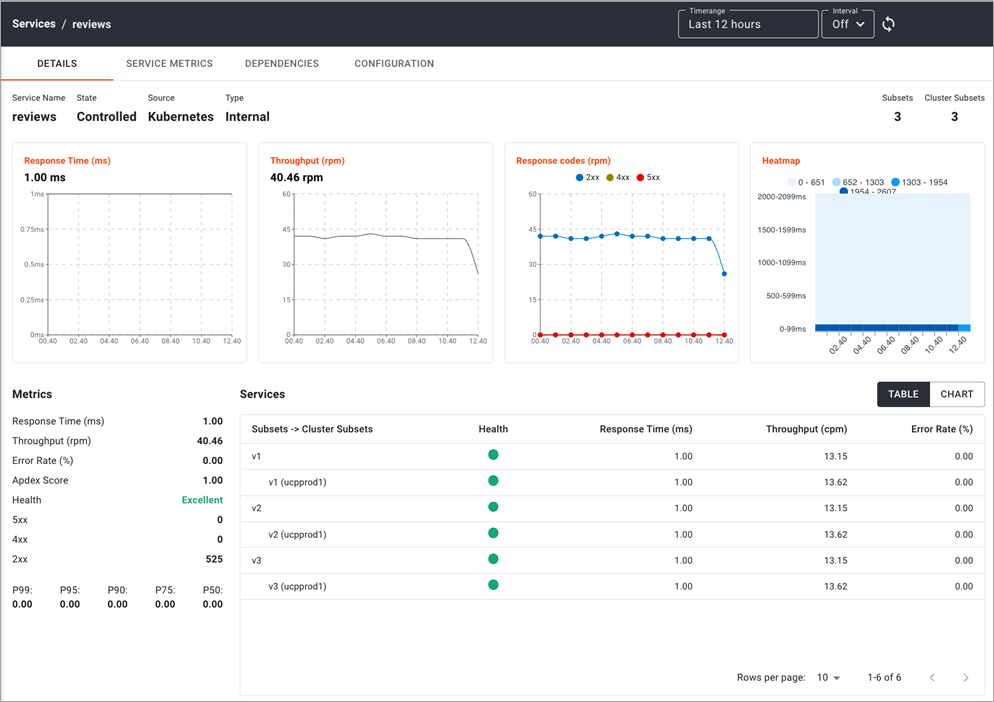
Out of the box, Istio provides per-cluster operational (RED: rate, error, duration) metrics, logging, and distributed tracing. Tetrate Service Bridge consolidates this observability data from across your infrastructure to form a single, coherent picture.
Global Service Registry and Topology
Understand your entire application environment with consolidated metrics from every cluster in a single view.
Figure 2 – Global service topology.
Global Service Metrics
Get the big picture with global service metrics—or drill down into service-centric views to see behavior in individual clusters and even specific instances of a service.
Figure 3 – Global service metrics.
Tetrate is Available on AWS Marketplace
Tetrate’s mission is to help enterprises manage the complexity of modern microservices applications. A key part of that mission is operationalizing the process of deploying application infrastructure in an automated, repeatable way.
The introduction of Amazon EKS Blueprints with add-ons goes a long way toward transforming cluster provisioning and deployment into modern, declarative infrastructure as code deployment processes.
- Tetrate Istio Distro (TID) makes adopting, managing, and updating Istio safe and easy, especially for organizations operating in federal regulatory environments that demand FIPS-verified software components.
- Tetrate Service Bridge (TSB) helps enterprises manage application connectivity for both traditional and microservices workloads across clusters, regions, and data centers. TID is free and open source, with optional enterprise support available from Tetrate.
Both TID and TSB are available on AWS Marketplace, and Tetrate collaborates closely with AWS to deliver a seamless product procurement and implementation process.
Tetrate – AWS Partner Spotlight
Tetrate is an AWS Partner that bridges your applications wherever they are with the only compute-agnostic, zero-trust service mesh fabric built for multi-cluster and multi-cloud.