AWS Partner Network (APN) Blog
Risk-Based, Fine-Grained Authorization with Transmit Security and Amazon Verified Permissions
By Aliaksei Ivanou, Partner Solutions Architect, Security and Identity – AWS
By Danny Kadyshevich, Sr. Product Manager – Transmit Security
 |
| Transmit Security |
 |
Managing and securing account access can feel like navigating a complex landmine of risk. After all, you have millions of customer accounts, each with its own set of permissions and authorization requirements.
Updating these permissions to meet regulations and security requirements is a constant challenge, and hard-coded authorizations are especially difficult to manage. An access decision is not always a clear yes or no. This is where it becomes essential to have both fine-grained and risk-based authorization. Fine-grained authorization is needed to limit user access to least privilege, as required for a zero trust architecture.
Amazon Verified Permissions delivers a pre-built system that simplifies policy-based access control (PBAC) and is flexible enough to address the most advanced authorization requirements for custom applications. With granular policies, it’s highly effective for determining who has access to what.
But how do you know an account hasn’t been taken over or compromised? Is it really your customer who logged in to begin with? You can only answer these questions with risk-based authorization that is able to assess the full context of a request with respect to user activities in the current and previous sessions.
In this post, we explain how to take a risk score calculated by Transmit Security and use it as an input to an authorization decision made by Amazon Verified Permissions. Transmit Security is an AWS Partner that provides fraud detection and response and identity orchestration services to the largest enterprises in the world.
Innovative Risk-Based Authorization
Thanks to a collaborative effort, Transmit Security services now integrate with Amazon Verified Permissions to externalize authorization and monitor risk, triggering the right access decisions in real-time. Transmit Security Detection and Response Service collects and analyzes over 100 signals at all times to determine risk and trust across the full identity lifecycle.
The fraud orchestration layer of Detection and Response correlates the data and applies machine learning (ML) to evaluate telemetry and assess risk and trust access requests. The risk decision requires knowledge of the individual customer’s typical behavior and devices—as a baseline for comparison. If risk appears when a request should otherwise be authorized, the solution conditionally prompts the user to re-authenticate or verify their identity.
How it Works
The complexity of accounts today provides bad actors with a larger attack surface to gain unauthorized access to accounts and resources that are managed by these accounts. In order to close security gaps and verify the real account owner is the one trying to gain access, you need to apply two methods:
- Deterministic – answers the questions of:
- Who is the actor?
- Is the actor allowed to do what they are trying to do?
- Dynamic – adds additional user interaction risk and trust context:
- Even if a specific account is eligible to take certain actions, it’s possible for the account to be taken over. At this point, those deterministic checks must be strengthened with additional dynamic risk assessments that weigh the full context and analyze telemetry.
To make the best access decisions in real-time, you need both risk-based (dynamic) and fine-grained (deterministic) authorization. By joining forces, Amazon Web Services (AWS) and Transmit Security have created the next generation of risk-based, fine-grained authorization.
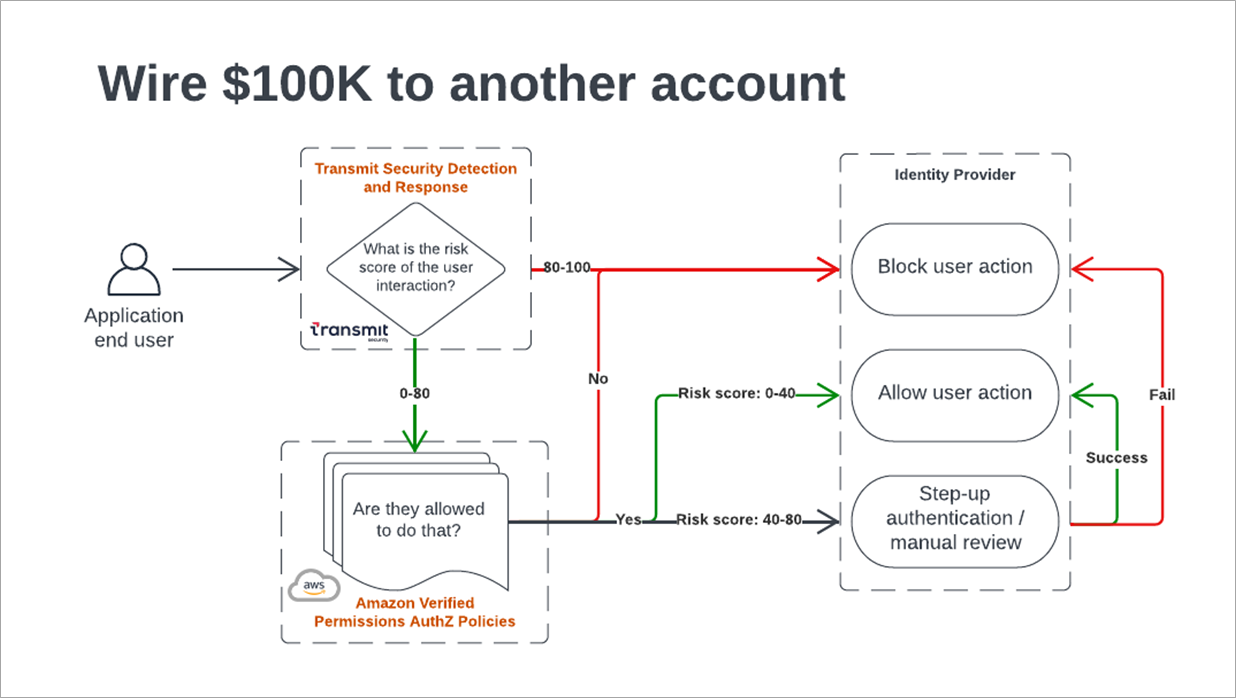
Figure 1 – User authorization decisioning.
AWS customers can use Amazon Verified Permissions for fine-grained permissions and authorization, and leverage Transmit Security to provide risk-based context and recommendations for each authorization request.
Transmit Security Detection and Response
Transmit Security Detection and Response Service leverages artificial intelligence (AI) models to process over 100 telemetry types using multiple detection methods. This enables real-time detection of behavior signals as well as risk, trust, fraud, bot, and behavior analysis with transparent, out-of-the-box decisioning logic that leverages:
- Account changes – new beneficiaries, multi-factor authentication (MFA) disabled
- App activity – financial transactions, password resets
- Authentication events – step up, verification
- Global risk signals – activity times and volume
- Network intelligence – IP address reputation, data center activity, residential proxy
- Device intelligence – fingerprinting, browser, and operating systems (OS) reputation
- Behavioral biometrics – mouse movement speed, typing velocity
By integrating Detection and Response into customer applications, telemetry can be collected throughout the entire end user journey—from account opening to login and in-account activities. At every critical moment in the app, the client can fetch a real-time risk score and recommendation (such as allow or deny) for the specific action (like login or transaction) to determine how to proceed.
The risk score is calculated by the detection engine based on risk reasons and signals observed, such as:
- Bot activity
- Emulated devices
- IP activity velocity
- Quick mouse movement
- Device takeover
- New user location
By combining the authorization policies evaluation results by Amazon Verified Permissions and the risk score returned by Transmit Security Detection and Response, security and compliance teams can confidently address the two critical questions to ensure their application accounts and assets are used in a safe and secure manner:
- Does the current user have the right to do what they want to do?
- Is the context of the user’s interaction with the service legitimate and normal?
Integration Overview
The following diagram presents an overview of the Amazon Verified Permissions and Detection and Response integration flow.
Figure 2 – Integration flow.
The high-level action flow is as follows:
- Upon every application user action, a JavaScript component running in the browser calls the triggerActionEvent API for fetching an actionToken used for retrieving the risk evaluation. In the background, the application continuously collects telemetry from the browser to provide a continuous risk evaluation.
- JavaScript application calls the backend service and passes the actionToken.
- Backend service calls the Detection and Response service to get a risk score.
- Backend service calls Amazon Verified Permissions (with the risk score) to determine if the user is authorized to access the resource.
- Request is authorized, the action is approved, and the content is returned to the end user.
Prerequisites
- Transmit Security
- Set up a Transmit Security Admin Portal tenant.
- Create a new application to get client credentials.
- Amazon Verified Permissions
- Create an Amazon Verified Permission policy store in your AWS account. Please refer to the documentation.
- Create authorization policies which are written in Cedar, an open-source language for defining permissions as policies.
Below are two policies related to the sample application:
It’s recommended to interpret the real-time risk score, which is provided on a scale of 0-100, as follows:
- Risk score is within the range of 0-40: User action is considered to have no-low risk and full user permission can be granted.
- Risk score is within the range of 40-80: User action is considered to have a medium risk and is highly recommended to limit the user for read-only activity.
- Risk score is within the range of 80-100: User action is considered to have a high risk and is highly recommended to restrict the user access to the account.
Telemetry collected on the browser may be blocked by ad blockers installed on end users’ devices resulting in software development kit (SDK) operation failures. This can be addressed by following any of the options listed in the Transmit Security guides.
Integration Sample App
You can see an integration sample app written in next.js (client and backend integrations).
Next, we will explain how to integrate Transmit Security Detection and Response Service with Amazon Verified Permissions.
Step 1: Transmit Security Detection and Response Client SDK Integration
Start monitoring end-user activity by loading and initializing the Transmit Security Detection and Response SDK across the application pages.
For a quick start, we have created the following sample code which is implemented in Next.js and consumes Detection and Response React.JS client SDK. For other implementations, see Detection and Response quick start guides.
- Call setAuthenticatedUser function after the user successfully authenticated in your app, as described in this article, or like this sample code (react client SDK integration).
- Call triggerActionEvent function with the relevant user action (such as ‘login’/’withdraw’) and receive the actionToken, as described in this article, or like this sample code.
Step 2: Add Action Token to Resource Access Request
Next, add the action token retrieved in the previous step to the relevant resource access request; see an example in GitHub.
Step 3: Fetch Detection and Response Risk Recommendation
Call the Recommendation API and extract the risk_score and action_id to be passed as parameters to the authorization request check.
Note that you can also decode the action_id from the actionToken, as done in this GitHub example.
Step 4: Amazon Verified Permissions SDK Backend Integration
Once you have completed the integration of the Detection and Response SDK into your application, you are ready to integrate with Amazon Verified Permissions to enforce business logic for checking authorization and risk score for every application request.
Please refer to this code snippet as an example. It sends the authorization context including the principal, action, resource, and context to the Amazon Verified Permissions isAuthorized API to evaluate authorization policies defined in the policy store.
You can find more information about Amazon Verified Permissions SDK and API in the documentation.
Step 5: Backend Response
If result.decision==’DENY’ then return error code 403 to the client due to missing permissions.
Audit and Investigate Context and Insights
The decisioning logic for the Transmit Security risk engine can be thought of as a funnel that distills raw data points into actionable recommendations.
Through this process, raw data points are collected on the client side and enriched with data from analytics and heuristics, as well as third-party data sources. It’s then compared against risk engine rules and any custom logic, such as custom rules or labels, to detect potential attacks and determine how to act on them.
This enables users to provide not the risk score per user action, and the raw data and enriched signals used to calculate the risk score in real-time using the Transmit Security user interface (UI) or APIs. Risk score is accompanied by contextualized information that explains the top reasons behind the final risk score, such as challenging a request due to impossible travel or allowing a request made with a trusted user device.
Within the UI, analysts can access more analytics to easily:
- Locate a specific user and see a real-time list of the user’s requests, along with their accompanying risk score and context.
- View the distribution of risk score over time to quickly spot large-scale attack campaigns.
- Filter for specific recommendation types or within specific moments of the user to drill down into application-wide patterns of suspicious behavior.
- See a breakdown of the top reasons for challenging and denying requests.
Figure 3 – Detection and Response recommendations dashboard.
Summary
With account takeover attacks on the rise, risk-based, fine-grained authorization is essential. The combination of Amazon Verified Permissions and Transmit Security Detection and Response allows developers to:
- Externalize authorizations to improve security, centralize policy administration, promote consistency in authorization decisions, and quickly adapt to changing security requirements or risk.
- Provide seamless access by removing friction for trusted customers.
- Stop risky requests and affirm zero trust with real-time risk-based authorization.
- Arm security teams with the activity logs to investigate risky behavior and anomalies.
Security and fraud teams can now extend their safeguards by ensuring users have the necessary permissions and the customer is truly the one who is requesting access.
Learn more about Transmit Security Detection and Response Service and Amazon Verified Permissions to start experimenting with this powerful integration.
Sample code, software libraries, command line tools, proofs of concept, templates, or other related technology are provided as AWS content or third-party content under the AWS Customer Agreement, or the relevant written agreement between you and AWS (whichever applies). You should not use this AWS content or third-party content in your production accounts, or on production or other critical data. You are responsible for testing, securing, and optimizing the AWS content or third-party content, such as sample code, as appropriate for production grade use based on your specific quality control practices and standards. Deploying AWS content or third-party content may incur AWS charges for creating or using AWS chargeable resources, such as running Amazon EC2 instances or using Amazon S3 storage.
Transmit Security – AWS Partner Spotlight
Transmit Security is an AWS Partner that provides fraud detection and response and identity orchestration services to the largest enterprises in the world.
Contact Transmit Security | Partner Overview | AWS Marketplace