AWS Compute Blog
Category: Serverless
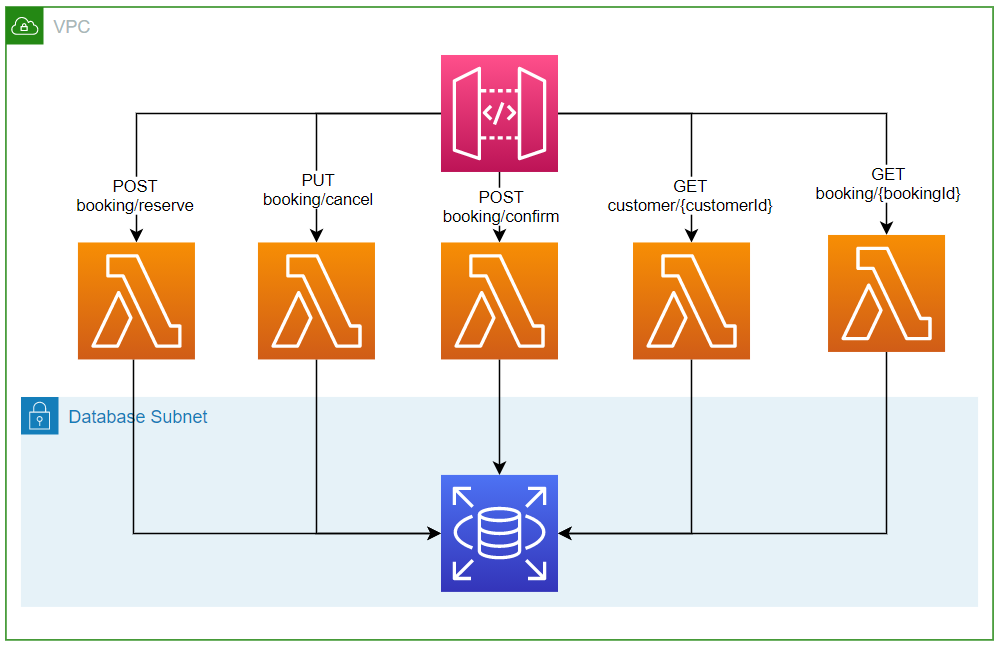
Migrating a monolithic .NET REST API to AWS Lambda
This blog post shows the required considerations for migrating a .NET Core REST API to AWS Lambda. You can now start to look at your existing code base and make an informed decision whether Lambda is for you. With the right abstractions and configuration, you can migrate a .NET Core API to Lambda compute with copy and paste.
Introducing the .NET 6 runtime for AWS Lambda
We are excited to add support for .NET 6 to Lambda. It’s fast to get started or migrate existing functions to .NET 6, with many new features in .NET 6 to take advantage of. Read the Lambda Developer Guide for more getting started information.
Building TypeScript projects with AWS SAM CLI
This post written by Dan Fox, Principal Specialist Solutions Architect and Roman Boiko, Senior Specialist Solutions Architect The AWS Serverless Application Model (AWS SAM) CLI provides developers with a local tool for managing serverless applications on AWS. This command line tool allows developers to initialize and configure applications, build and test locally, and deploy to […]
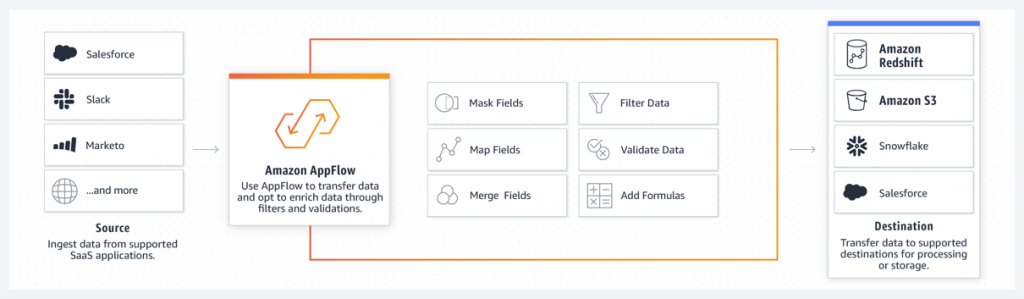
Building custom connectors using the Amazon AppFlow Custom Connector SDK
This blog post shows how to extend the Amazon AppFlow service to move data between SaaS endpoints and custom APIs. You can now build custom connectors using the Amazon AppFlow Custom Connector SDK.
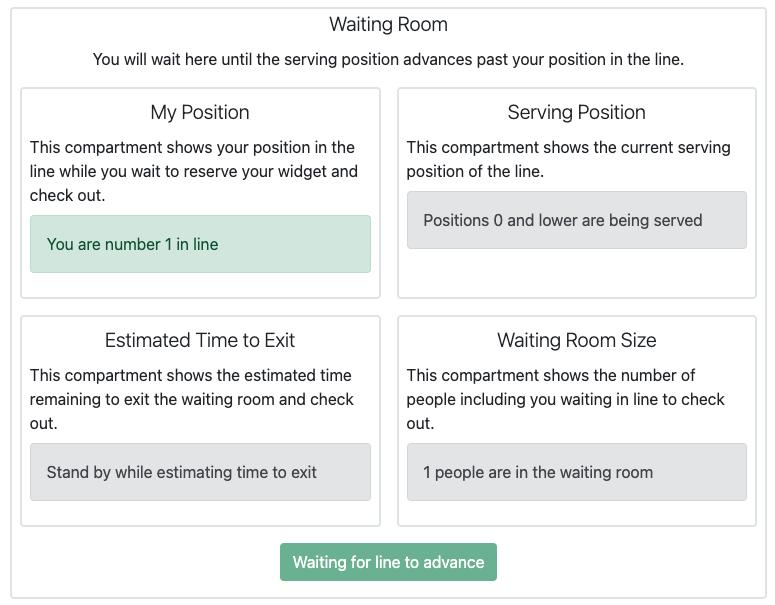
Introducing AWS Virtual Waiting Room
The AWS Virtual Waiting Room solution is available today at no additional cost, provided as open source under the Apache 2 license. It supports customized integration with any front-end application via a variety of integration techniques.
Capturing client events using Amazon API Gateway and Amazon EventBridge
This post shows how to send client events to an API and EventBridge to enable new customer experiences. The example covers enabling new experiences by creating a way for software clients to send events with minimal custom code.
Mocking service integrations with AWS Step Functions Local
This post is written by Sam Dengler, Principal Specialist Solutions Architect, and Dhiraj Mahapatro, Senior Specialist Solutions Architect. AWS Step Functions now supports over 200 AWS Service integrations via AWS SDK Integration. Developers want to build and test control flow logic for workflows using branching logic, error handling, and retries. This allows for precise workflow execution with deterministic […]
Using the circuit breaker pattern with AWS Step Functions and Amazon DynamoDB
This post is written by Anitha Deenadayalan, Developer Specialist SA, DevAx Modern applications use microservices as an architectural and organizational approach to software development, where the application comprises small independent services that communicate over well-defined APIs. When multiple microservices collaborate to handle requests, one or more services may become unavailable or exhibit a high latency. […]
Migrating AWS Lambda functions to Arm-based AWS Graviton2 processors
AWS Lambda now allows you to configure new and existing functions to run on Arm-based AWS Graviton2 processors in addition to x86-based functions. Using this processor architecture option allows you to get up to 34% better price performance. This blog post highlights some considerations when moving from x86 to arm64 as the migration process is […]
Introducing AWS Lambda batching controls for message broker services
This post is written by Mithun Mallick, Senior Specialist Solutions Architect. AWS Lambda now supports configuring a maximum batch window for instance-based message broker services to fine tune when Lambda invocations occur. This feature gives you an additional control on batching behavior when processing data. It applies to Amazon Managed Streaming for Apache Kafka (Amazon […]