The Internet of Things on AWS – Official Blog
Tag: AWS IoT best practices
Simplify multi-account device provisioning and certificate authority registration when using AWS IoT Core
Customers often manage multiple AWS accounts to separate their development, staging, and production environments. When deploying IoT workloads on AWS IoT Core, customers usually use unique X.509 certificates for identifying devices and certificate authorities (CAs) for validating the signature of device certificates during provisioning. In this blog, we will demonstrate how to use the newly […]
Automating workflows for AWS IoT Greengrass V2 components
Introduction AWS IoT Greengrass V2 Development Kit Command-Line Interface (GDK CLI) was announced at AWS re:Invent 2021. With GDK CLI you can easily create AWS IoT Greengrass V2 components, flexibly define recipes, and publish these components to AWS IoT Greengrass V2. However, every time there is a change to the AWS Greengrass V2 component recipe, […]
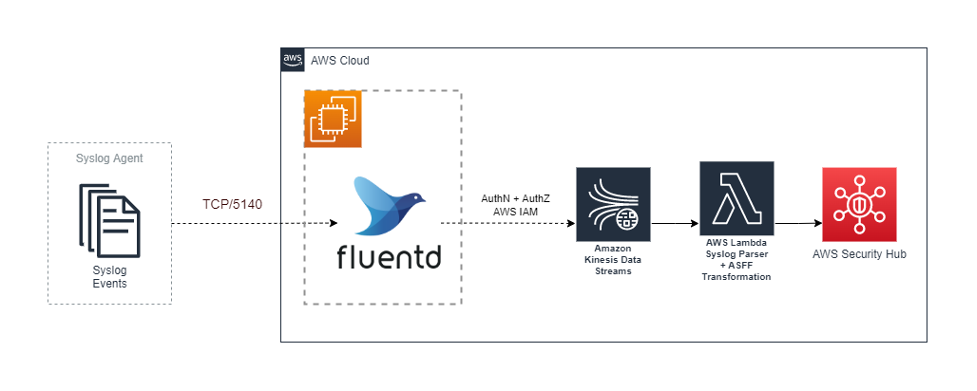
Implement security monitoring across OT, IIoT and cloud with AWS Security Hub
Introduction Industrial digital transformation can increase competitiveness and optimize processes and profitability through the use of big data, IoT, machine-to-machine communication, and machine learning. Continuous digitalization and progressive interconnectivity of the production environment is important to capturing value from industrial IoT (IIoT) solutions. While this new and expanding “physical meets digital” connectivity enables great rewards, […]
Assessing OT and IIoT cybersecurity risk
This blog is co-authored by Ryan Dsouza, AWS and John Cusimano, Deloitte Introduction Innovative and forward-looking oil and gas, electrical generation and distribution, aviation, maritime, rail, utilities, and manufacturing companies who use Operational Technology (OT) to run their businesses are adopting the cloud in many forms as a result of their digital transformation initiatives. Data […]
7 patterns for IoT data ingestion and visualization- How to decide what works best for your use case
Introduction Whether you are just starting with your Internet of Things (IoT) journey, or already have millions of connected IoT devices, you might be looking for ways to maximize the value extracted from your IoT data. IoT devices data can contain a wealth of information within its reported telemetry data, metadata, state, and commands and […]
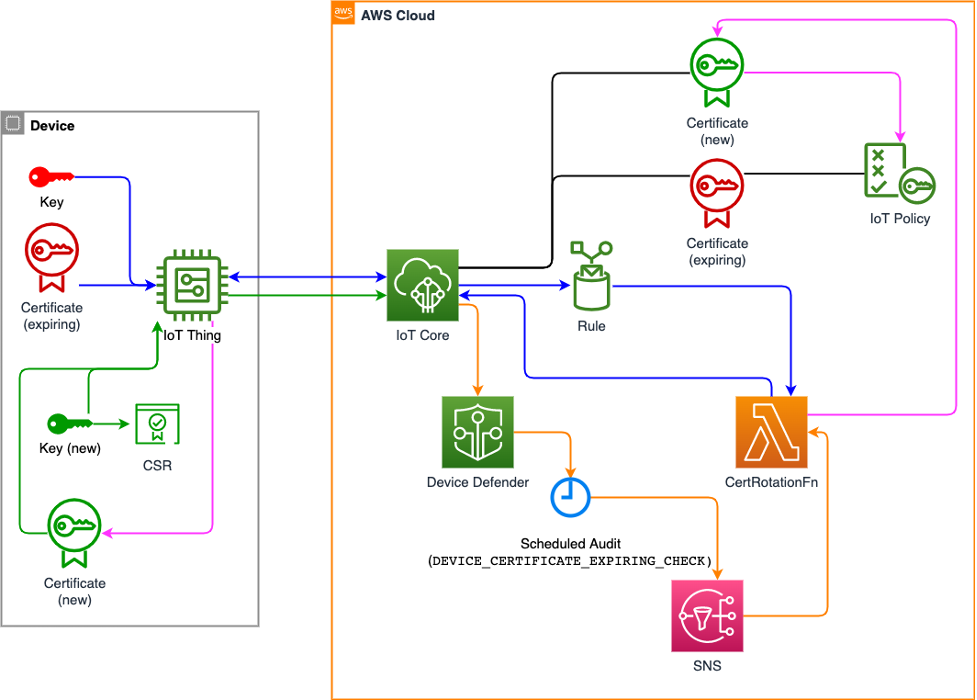
How to manage IoT device certificate rotation using AWS IoT
Introduction The Internet of Things (IoT) is transforming business operations and customer experiences across a variety of industries. This unlimited opportunity enables business transformation, but if not implemented correctly, it also brings security, risk, and privacy concerns, compromising your data and brand. In industrial facilities, OT (Operational Technology) environments are leveraging more IT solutions to improve […]
How to detect anomalies in device metrics and improve your security posture using AWS IoT Device Defender custom metrics
Introduction IoT applications and devices can be diverse and are used across industries such as utilities, agriculture, manufacturing, mining, and consumer electronics. With the exponential growth of IoT devices and the increasing threat landscape, it also means that IoT security needs to be accounted for and designed into the solution from the ground up. AWS […]
What actions customers can take to protect, detect, and respond to Log4j vulnerabilities in Operational Technology (OT) and Industrial Internet of Things (IIoT) environments
In this post we will provide guidance to help industrial customers respond to the recently disclosed Log4j vulnerability. This post covers how to identify if you are susceptible to the issue, and then how to address the vulnerability in OT and IIoT environments. The Log4j vulnerability (CVE-2021-44228, CVE-2021-45046) is a critical vulnerability (CVSS 3.1 base […]
How to implement zero trust IoT solutions with AWS IoT
Introduction Zero trust is often misunderstood. It’s not a product but a security model and associated set of architectural principles and patterns. One of the main challenges customers face is determining how zero-trust principles can be applied to Internet of Things (IoT) and how to get started with incorporating zero trust with Amazon Web Services […]
Build an AWS IoT Well-Architected environment with the IoT Lens
There are an estimated 31 billion IoT devices in 2020, and this is expected to increase to 75 billion by 2025 according to Security Today. You may be starting on your IoT journey or have hundreds of thousands of devices connected and want to improve your architecture and reduce your cost. To guide you through […]