AWS Security Blog
Category: Amazon EC2
Confidential computing: an AWS perspective
Customers around the globe—from governments and highly regulated industries to small businesses and start-ups—trust Amazon Web Services (AWS) with their most sensitive data and applications. At AWS, keeping our customers’ workloads secure and confidential, while helping them meet their privacy and data sovereignty requirements, is our highest priority. Our investments in security technologies and rigorous […]
Use EC2 Instance Connect to provide secure SSH access to EC2 instances with private IP addresses
In this post, I show you how to use Amazon EC2 Instance Connect to use Secure Shell (SSH) to securely access your Amazon Elastic Compute Cloud (Amazon EC2) instances running on private subnets within an Amazon Virtual Private Cloud (Amazon VPC). EC2 Instance Connect provides a simple and secure way to connect to your EC2 […]
Review last accessed information to identify unused EC2, IAM, and Lambda permissions and tighten access for your IAM roles
September 28, 2023: IAM is incrementally adding support for actions from more services. For a list of services that report action last accessed information, see IAM action last accessed information services and actions. AWS Identity and Access Management (IAM) helps customers analyze access and achieve least privilege. When you are working on new permissions for […]
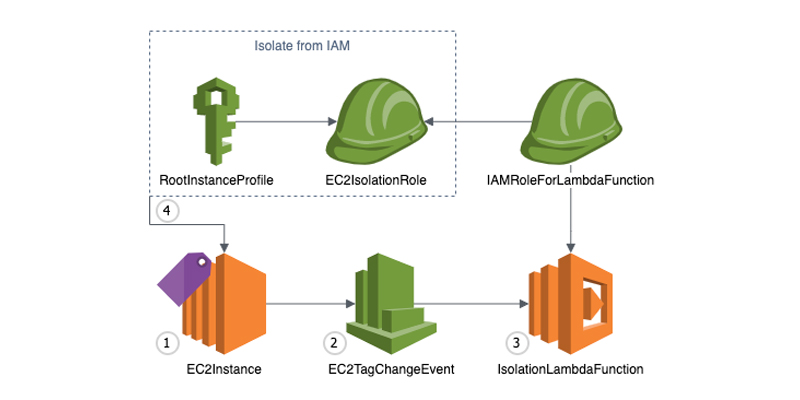
Automate Amazon EC2 instance isolation by using tags
Containment is a crucial part of an overall Incident Response Strategy, as this practice allows time for responders to perform forensics, eradication and recovery during an Incident. There are many different approaches to containment. In this post, we will be focusing on isolation—the ability to keep multiple targets separated so that each target only sees […]
Secure and automated domain membership management for EC2 instances with no internet access
In this blog post, I show you how to deploy an automated solution that helps you fully automate the Active Directory join and unjoin process for Amazon Elastic Compute Cloud (Amazon EC2) instances that don’t have internet access. Managing Active Directory domain membership for EC2 instances in Amazon Web Services (AWS) Cloud is a typical […]
Automate domain join for Amazon EC2 instances from multiple AWS accounts and Regions
As organizations scale up their Amazon Web Services (AWS) presence, they are faced with the challenge of administering user identities and controlling access across multiple accounts and Regions. As this presence grows, managing user access to cloud resources such as Amazon Elastic Compute Cloud (Amazon EC2) becomes increasingly complex. AWS Directory Service for Microsoft Active […]
How to automate incident response in the AWS Cloud for EC2 instances
One of the security epics core to the AWS Cloud Adoption Framework (AWS CAF) is a focus on incident response and preparedness to address unauthorized activity. Multiple methods exist in Amazon Web Services (AWS) for automating classic incident response techniques, and the AWS Security Incident Response Guide outlines many of these methods. This post demonstrates […]
How to configure an LDAPS endpoint for Simple AD
In this blog post, we show you how to configure an LDAPS (LDAP over SSL or TLS) encrypted endpoint for Simple AD so that you can extend Simple AD over untrusted networks. Our solution uses Network Load Balancer (NLB) as SSL/TLS termination. The data is then decrypted and sent to Simple AD. Network Load Balancer […]
Quickly build STIG-compliant Amazon Machine Images using Amazon EC2 Image Builder
In this post, we discuss how to implement the operating system security requirements defined by the Defence Information Systems Agency (DISA) Security Technical Implementation Guides (STIGs). As an Amazon Web Services (AWS) customer, you can use Amazon Machine Images (AMIs) published by AWS or APN partners. These AMIs, which are owned and published by AWS, […]
What is a cyber range and how do you build one on AWS?
In this post, we provide advice on how you can build a current cyber range using AWS services. Conducting security incident simulations is a valuable exercise for organizations. As described in the AWS Security Incident Response Guide, security incident response simulations (SIRS) are useful tools to improve how an organization handles security events. These simulations […]