AWS Security Blog
Tag: AWS WAF
How to analyze AWS WAF logs using Amazon Elasticsearch Service
September 9, 2021: Amazon Elasticsearch Service has been renamed to Amazon OpenSearch Service. See details. Log analysis is essential for understanding the effectiveness of any security solution. It can be valuable for day-to-day troubleshooting and also for your long-term understanding of how your security environment is performing. AWS WAF is a web application firewall that […]
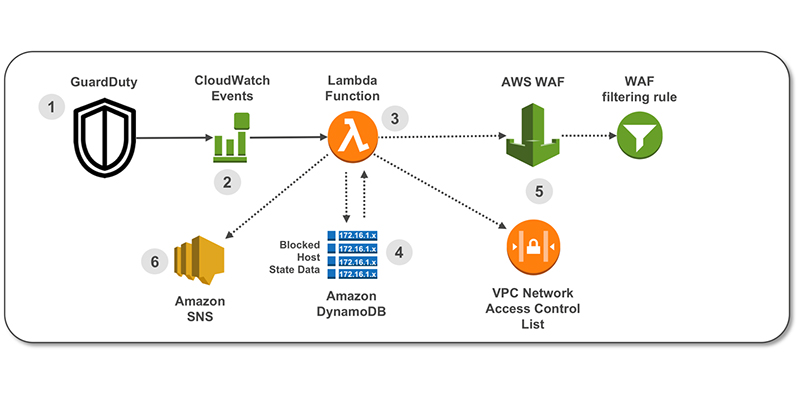
How to use Amazon GuardDuty and AWS Web Application Firewall to automatically block suspicious hosts
April 25, 2023: We’ve updated this blog post to include more security learning resources. When you’re implementing security measures across your AWS resources, you should use a holistic approach that incorporates controls across multiple areas. In the Cloud Adoption Framework (CAF) Security perspective whitepaper, we define these controls across four categories. Directive controls. Establish the […]
The Top 10 Most Downloaded AWS Security and Compliance Documents in 2017
July 24, 2020: The number 9 item in this list, the Auditing Security Checklist, has been replaced by a Cloud Audit Academy course. The following list includes the ten most downloaded AWS security and compliance documents in 2017. Using this list, you can learn about what other AWS customers found most interesting about security and […]
Now Available: New Digital Training to Help You Learn About AWS Cloud Security
Cloud security with scalability and innovation: at AWS, this is our top priority. To help you securely architect cloud solutions, AWS Training and Certification recently added new free digital training about security, including a new course about Amazon GuardDuty, a new managed threat-detection service. These introductory courses, built by AWS experts, are suitable for users and decision makers […]
Now You Can Use AWS Shield Advanced to Help Protect Your Amazon EC2 Instances and Network Load Balancers
Starting today, AWS Shield Advanced can help protect your Amazon EC2 instances and Network Load Balancers against infrastructure-layer Distributed Denial of Service (DDoS) attacks. Enable AWS Shield Advanced on an AWS Elastic IP address and attach the address to an internet-facing EC2 instance or Network Load Balancer. AWS Shield Advanced automatically detects the type of AWS resource behind the […]
New Security Whitepaper Now Available: Use AWS WAF to Mitigate OWASP’s Top 10 Web Application Vulnerabilities
Today, we released a new security whitepaper: Use AWS WAF to Mitigate OWASP’s Top 10 Web Application Vulnerabilities. This whitepaper describes how you can use AWS WAF, a web application firewall, to address the top application security flaws as named by the Open Web Application Security Project (OWASP). Using AWS WAF, you can write rules to […]
How to Help Protect Dynamic Web Applications Against DDoS Attacks by Using Amazon CloudFront and Amazon Route 53
Using a content delivery network (CDN) such as Amazon CloudFront to cache and serve static text and images or downloadable objects such as media files and documents is a common strategy to improve webpage load times, reduce network bandwidth costs, lessen the load on web servers, and mitigate distributed denial of service (DDoS) attacks. AWS […]
The Most Viewed AWS Security Blog Posts in 2016
September 9, 2021: Amazon Elasticsearch Service has been renamed to Amazon OpenSearch Service. See details. The following 10 posts were the most viewed AWS Security Blog posts that we published during 2016. You can use this list as a guide to catch up on your blog reading or even read a post again that you […]
Updated Whitepaper Available: AWS Best Practices for DDoS Resiliency
AWS is committed to providing you high availability, security, and resiliency in the face of bad actors on the Internet. As part of this commitment, AWS provides tools, best practices, and AWS services that you can use to build distributed denial of services (DDoS)–resilient applications. We recently released the 2016 version of the AWS Best […]
How to Use AWS CloudFormation to Automate Your AWS WAF Configuration with Example Rules and Match Conditions
Note from July 4, 2017: The solution in this post has been integrated into AWS WAF Security Automations, and AWS maintains up-to-date solution code in the companion GitHub repository. AWS WAF is a web application firewall that integrates closely with Amazon CloudFront (AWS’s content delivery network [CDN]). AWS WAF gives you control to allow or block […]