AWS Security Blog
Tag: Security
Defending LLM applications against Unicode character smuggling
When interacting with AI applications, even seemingly innocent elements—such as Unicode characters—can have significant implications for security and data integrity. At Amazon Web Services (AWS), we continuously evaluate and address emerging threats across aspects of AI systems. In this blog post, we explore Unicode tag blocks, a specific range of characters spanning from U+E0000 to […]
Optimize security operations with AWS Security Incident Response
Security threats demand swift action, which is why AWS Security Incident Response delivers AWS-native protection that can immediately strengthen your security posture. This comprehensive solution combines automated triage and evaluation logic with your security perimeter metadata to identify critical issues, seamlessly bringing in human expertise when needed. When Security Incident Response is integrated with Amazon […]
Multi-Region keys: A new approach to key replication in AWS Payment Cryptography
In our previous blog post (Part 1 of our key replication series), Automatically replicate your card payment keys across AWS Regions, we explored an event-driven, serverless architecture using AWS PrivateLink to securely replicate card payment keys across AWS Regions. That solution demonstrated how to build a custom replication framework for payment cryptography keys. Based on […]
Amazon disrupts watering hole campaign by Russia’s APT29
Amazon’s threat intelligence team has identified and disrupted a watering hole campaign conducted by APT29 (also known as Midnight Blizzard), a threat actor associated with Russia’s Foreign Intelligence Service (SVR). Our investigation uncovered an opportunistic watering hole campaign using compromised websites to redirect visitors to malicious infrastructure designed to trick users into authorizing attacker-controlled devices […]
Secure file sharing solutions in AWS: A security and cost analysis guide: Part 2
As introduced in Part 1 of this series, implementing secure file sharing solutions in AWS requires a comprehensive understanding of your organization’s needs and constraints. Before selecting a specific solution, organizations must evaluate five fundamental areas: access patterns and scale, technical requirements, security and compliance, operational requirements, and business constraints. These areas cover everything from […]
Secure file sharing solutions in AWS: A security and cost analysis guide, Part 1
Securely share sensitive data with time-limited, nonce-enhanced presigned URLs that prevent replay attacks, minimizing exposure risks through granular access controls and rigorous monitoring.
AWS Security Incident Response: The customer’s journey to accelerating the incident response lifecycle
August 1, 2024: This post was republished to remove incorrect references to AWS WAF and Shield. Organizations face mounting challenges in building and maintaining effective security incident response programs. Studies from IBM and Morning Consult show security teams face two major challenges: over 50 percent of security alerts go unaddressed because of resource constraints and alert […]
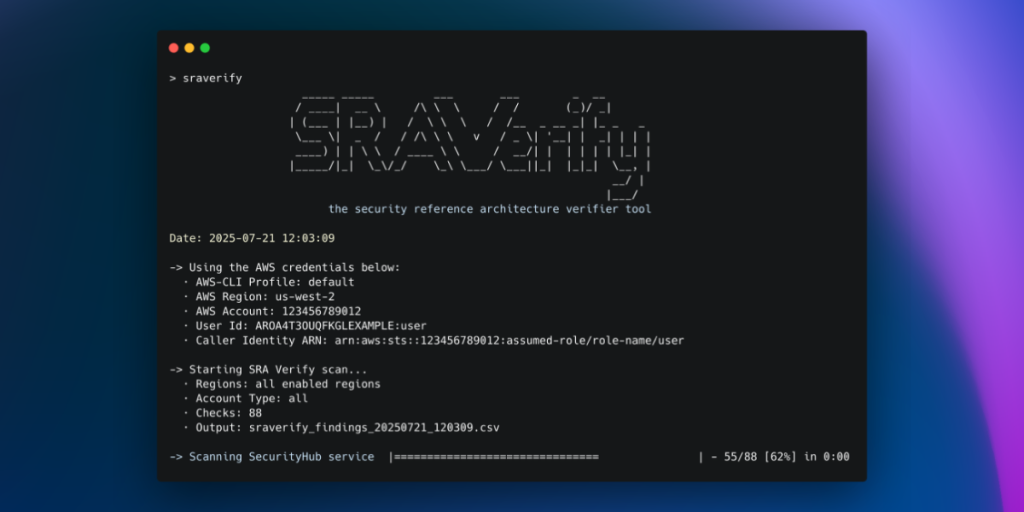
Introducing SRA Verify – an AWS Security Reference Architecture assessment tool
The AWS Security Reference Architecture (AWS SRA) provides prescriptive guidance for deploying AWS security services in a multi-account environment. However, validating that your implementation aligns with these best practices can be challenging and time-consuming. Today, we’re announcing the open source release of SRA Verify, a security assessment tool that helps you assess your organization’s alignment […]
Secure your Express application APIs in minutes with Amazon Verified Permissions
June 23, 2025: We updated @verifiedpermissions/authorization-clients to @verifiedpermissions/authorization-clients-js to correctly reflect the name of the package on npm. Today, Amazon Verified Permissions announced the release of @verifiedpermissions/authorization-clients-js, an open source package that developers can use to implement external fine-grained authorization for Express.js web application APIs in minutes when using Verified Permissions. Express is a minimal […]
Improve your security posture using Amazon threat intelligence on AWS Network Firewall
Today, customers use AWS Network Firewall to safeguard their workloads against common security threats. However, they often have to rely on third-party threat feeds and scanners that have limited visibility in AWS workloads to protect against active threats. A self-managed approach to cloud security through traditional threat intelligence feeds and custom rules can result in […]