AWS Startups Blog
Lacework’s Three Keys for Effective AWS Security
Guest post from Lacework, sponsors of AWS Security Week at the San Francisco Loft from July 30 – August 2.
If you’ve ever considered running a workload on AWS, then you probably have some familiarity with the “shared responsibility model.” This is AWS’s framework for how security should be handled and states that AWS will take care of the things that make up the cloud, but you are responsible for the stuff running in the cloud.
While AWS provides numerous tools and features to implement security for resources running in the cloud, you still need to understand how to maintain security over your own users, data, and assets if you want to truly be able to maintain rigor in your security and compliance operations. That’s the part of shared responsibility that companies need to own and build discipline around.
To do this, users must construct an approach that is comprehensive in terms of awareness, but also maintains the type of flexibility that cloud users rely on to function in an agile way. That means first knowing WHAT is going on in their environment, but then also having a way to measure the severity of those activities. The approach mandates an understanding of the continuous state of three aspects of security that we’ve found critical to operating workloads in AWS:
● Compliance, and how to ensure you are aware of all changes and updates to your configuration that could affect your adherence to regulations and established best practices such as the CIS benchmark for AWS
● AWS account security, which is critical to monitoring the activities of your AWS accounts. This includes continuous awareness of users and the resources they are accessing, and other activity like API calls made to data sources, so you can quickly detect any anomalous activity; and
● Host intrusion detection, so you can immediately discover instances of forced intrusions and other anomalies in the behaviors of your cloud events that warrant critical alerts.
Smart organizations recognize that being mindful of what’s happening is just one step. Security teams must have continuous awareness of cloud events and understand who has access (and what they have access to), the configurations and settings of cloud resources, and the connections among and between applications and data conductors like APIs.
The notion of really seeing every event happening within the cloud may appear challenging, but with the right tools and skill sets, organizations can gain control over their cloud environment through the lens of these three aspects.
Compliance is critical…and manageable
The management of compliance has usually been done in a checklist fashion. Standards and governance frameworks state controls that the IT infrastructure must adhere to, and a security or compliance team does the work to ensure that those requirements are correspondingly met.
It seems easy enough in a static environment, but in the cloud it demands a different approach. In highly dynamic cloud environments, accounts and resources configuration change continuously and workloads are brought up and down frequently. This agility is what gives the cloud its advantages, but it also means that the compliance process demands more frequent controls and an automated approach.
Meeting those requirements means that you have awareness of your cloud configurations and settings and recognize when you are in or out of compliance with the controls in the compliance “checklist.” Since configurations change dynamically in order to allow for user groups or connections to new data sources, there’s really no constant state of the environment.
In order to remain compliant with standards like SOC, PCI, HIPAA, and other frameworks, an organization needs continuous awareness of every event that might affect configurations within the cloud. These changes are happening at the application, ID, workload, and host layers of the cloud; within the shared responsibility model, these are the responsibility of the user, and they’re critical because this is where user and organizational data is being accessed.
Organizations can start by ensuring they meet the demands outlined in the CIS Foundations Benchmark best practices. These are guidelines from the Center for Internet Security (CIS) about how to apply configurations to the different layers within the AWS infrastructure. Combined with a continuous monitoring tool that delivers insights into configuration changes and anomalous activity, a security team can identify where issues exist, so they can immediately be fixed.

Lacework uses a continuous auditing process done at the velocity and pace of the cloud and produces interactive reports with detailed information on issues that could render an organization out of compliance at risk.
If auditors determine your cloud isn’t compliant with standards like PCI, SOC-2, or other compliance frameworks that are related to your business, you could lose your ability to operate. Most organizations understand this but still don’t have an organized approach to awareness. Automating the continuous activity in your cloud will provide a framework that can enable you to operate in compliance and securely.
Analysis of AWS CloudTrail events
AWS CloudTrail is an AWS service that collects important data about the activities of your AWS Accounts. CloudTrail logs provide an overview of changes and updates and provide essential insight into how your AWS environment is functioning.
First, we need to frame what’s really needed when it comes to CloudTrail and how organizations use it. Many are happy to search through their logs to do a manual forensic analysis of where and how issues happened. There’s nothing wrong with that, and while it may help you get smarter about your own infrastructure, it’s all after-the-fact data. It won’t do much to reduce threats.
Organizations can only meet risk head-on through on-going analysis of CloudTrail logs. Lacework applies visibility, insight, and analysis capabilities to CloudTrail logs so users get both a continuous and automated view into their environment, but can also act on account anomalies that detect issues that are critically relevant to AWS Account security.
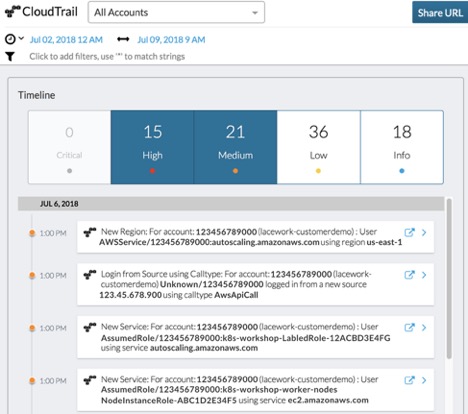
Integrating with AWS CloudTrail and analyzing CloudTrail data means that Lacework can detect anomalies within AWS accounts, including:
● Unusual changes across AWS resources. This can be done in regions and/or accounts and can identify when new S3 buckets are launched and when there are changes within those resources.
● Suspicious changes to users, roles, and any other type of access to apps and resources. This includes changes to security groups and when multi-factor authentication (MFA) is bypassed. Lacework employee machine learning to understand the normalized behaviors of users, accounts, services, and API calls, and alerts when there is an anomaly. Additionally, it is always monitoring defined, high-value events like S3 bucket creation and security group changes.
● All changes to AWS infrastructure services. Amazon GuardDuty uses CloudTrail and AWS Config to provide configuration snapshots, but it’s important to also identify and capture changes to access master keys, route table modifications, and anything related to network interfaces and services. High-risk anomalies are presented with insights so that the security team can rapidly investigate and fix potential incidents.
Intrusion detection
Here’s where the rubber of the shared responsibility model meets the road of your AWS infrastructure. You can only really know what’s happening if it’s identified at the point at which the information is collected. That requires an agent to be operating within an organization’s workloads or containers, so insights can be determined at the host-based level rather than the network level.
A host-based intrusion detection system (IDS) like that provided within Lacework uses anomaly detection algorithms and machine learning to analyze every application and user behavior inside a workload. The coverage includes all issues on SSH, parent hierarchy, user privilege change, process communication, machine communication, internal and external data transfers, and other cloud events.
Irrespective of whether it was an intentional, but ill-advised change, or the result of an attack attempt, configuration changes open the cloud environment to potential bad actors and threats. Intrusion detection done at the host-level, like with Lacework, detects anomalies across all layers, leaving no hidden space at the application and data layer for bad actors to hide.
Those in the security field know the feeling of being inundated with alerts. Like the little boy who cried “wolf,” alert fatigue can inure us to severe threats and what their implications are. This is why Lacework addresses issues with behavior baselining. Rather than looking at every machine, user, and application individually, our approach is to cluster these together based on historical behavior analysis, and alert when behavior is abnormal. The result is that, rather than being alerted multiple times for activities on multiple machines that all operate according to the same behaviors, we can alert you on the few issues that deviate from the norm.
Security never stops
AWS users are aware of the advantages of operating their workloads in the cloud, and the freedom from having to manage and monitor physical resources. But they are realistic, too. With the structural flexibility comes a new approach to securing data and workloads.
Understanding and managing your responsibilities for your AWS accounts can seem like a massive undertaking, but careful attention to the three key security elements outlined here will help create a framework for your security approach.
Creating a discipline based on cloud security best practices, coupled with the right supporting tools that automate aspects of cloud security can empower your organization to effectively identify and address threats. The ability to do that through continuous awareness means that issues can be dealt with upon discovery, with greater odds of thwarting attacks and strengthening the overall security of your AWS environment.