AWS Partner Network (APN) Blog
Automate Security and Monitoring with Amazon EKS Blueprints, Terraform, and Sysdig
By Manuel Boira, Strategic Alliances Solutions Architect – Sysdig
By Frank Carta, Sr. Container Specialist – AWS
 |
| Sysdig |
 |
Many companies report the biggest challenge when adopting Kubernetes is a lack of in-house skills (48% according to the Kubernetes and cloud-native report, 2022). In this same report, difficulty training users (29%) is also perceived as an obstacle.
Infrastructure as code (IaC) blueprints can mitigate these gaps by accelerating hands-on experience, providing a reproducible foundation to configure, provision, and destroy clusters easily.
Sysdig, in collaboration with Amazon Web Services (AWS), launched a Sysdig add-on for Amazon Elastic Kubernetes Service (Amazon EKS), and Sysdig EKS Blueprints to enable organizations to confidently deploy instrumented Kubernetes clusters using Terraform. The blueprints provision clusters that are monitored and secured from the day zero.
In this post, we will talk about Kubernetes adoption difficulties and how to use the blueprints to reduce those gaps. We’ll also learn some interesting facts about Kubernetes, IaC, and best practices along the way.
Sysdig is an AWS Partner and AWS Marketplace Seller with Competencies in Containers, Security, DevOps, and Cloud Operations. Sysdig delivers cloud and container security fueled by runtime insights, providing real-time visibility into AWS workloads with automated remediation.
Taming Kubernetes is Challenging
According to TheNewStack, security and monitoring are the top challenges reported by practitioners.
From a security perspective, Kubernetes clusters generate a new range of potential risks, especially in production where workloads expose their vulnerabilities to the world. This becomes even more complicated if we mention the majority of containers are ephemeral and live less than five minutes, according to research conducted by Sysdig.
This complexity starts earlier at the left side of the lifecycle when developers have to choose libraries with scalability and distribution in mind, not to mention the big bunch of artifacts involved when moving across the CI/CD stage.
Figure 1 – Kubernetes top challenges faced by users (TheNewStack).
Security First
Sysdig recommends reading the Amazon EKS Best Practices Guides and blog posts covering containers and Kubernetes security best practices, and specifically the Amazon EKS security best practices checklist.
Security best practices are built on top of operations best practices. One of the broadly accepted best practices when it comes to Kubernetes, cloud, and DevOps is to follow a GitOps approach. In fact, both the Center for Internet Security (CIS) and National Security Agency (NSA) recommend following Kubernetes hardening guidelines right from day zero.
This post attempts to take you two steps closer to a “hardened Kubernetes” with regard to monitoring and security using simple automation powered by Terraform.
IaC and GitOps Enforce Security
Security, infrastructure as code, and Kubernetes are a perfect match, according to Sysdig.
GitOps practices enable traceability, facilitate rollbacks, and disaster recovery. A well-implemented GitOps model makes it easier to reduce the attack surface, enforces least privilege, and helps prevent issues with secrets and outdated software, among other things.
A Git approach also enforces consistency and prevents mistakes via review, quality assurance, and linting. It provides the substratum for automations and other “things as code” such as policy as code. The practice of GitOps enables an organization to shift left security to detect vulnerabilities, threats, and misconfigurations long before they are propagated in real environments.
Complexity, Learning, and Experimentation
As we mentioned at the beginning of this post, adopting Kubernetes can be a long trip, especially for new practitioners and organizations that are at the first half of the cloud journey.
With the Sysdig add-ons and EKS Blueprints, anyone can provision Amazon EKS clusters and start operating with Sysdig in a matter of minutes. That’s valuable when it comes to evaluating, learning and researching.
The EKS Blueprints were designed to accelerate the adoption and reduce the learning curve in a sensible manner, but it’s important to note that blueprints alone should not be solely relied upon for building production-ready EKS clusters.
An EKS Blueprints roadmap can be checked in the Terraform EKS Blueprints GitHub pages.
Amazon EKS, Terraform, and Sysdig
Managed Kubernetes services like Amazon EKS mitigate part of the complexity by removing the need to manage the Kubernetes control plane. Sysdig takes care of security and monitoring across nodes, clusters, and containers by embedding “security cameras” to provide observability and security.
The add-ons framework provided by AWS facilitates a modular approach to configure and deploy operative tools like Sysdig, making it easier (and faster) to understand Amazon EKS and how to manage it.
Generally speaking, there are multiple use cases where blueprints provide value. For example, DevSecOps teams can leverage them to provide a modular foundation to other teams so they can customize and provision EKS clusters secured by default for their applications. Engineers who want to adopt Kubernetes can leverage blueprints as a guide through the best practices to reduce the learning curve.
Anyone who wants to learn cloud security can start working with EKS and Sysdig in a matter of minutes.
How to Use Sysdig Blueprints
The repository terraform-eks-blueprints contains the EKS Blueprints that are ready to be used. The only prerequisites are a Sysdig account (you can register for a free 30-day trial), an AWS account, and a console with the AWS and the Terraform command line interfaces (CLIs) installed and configured.
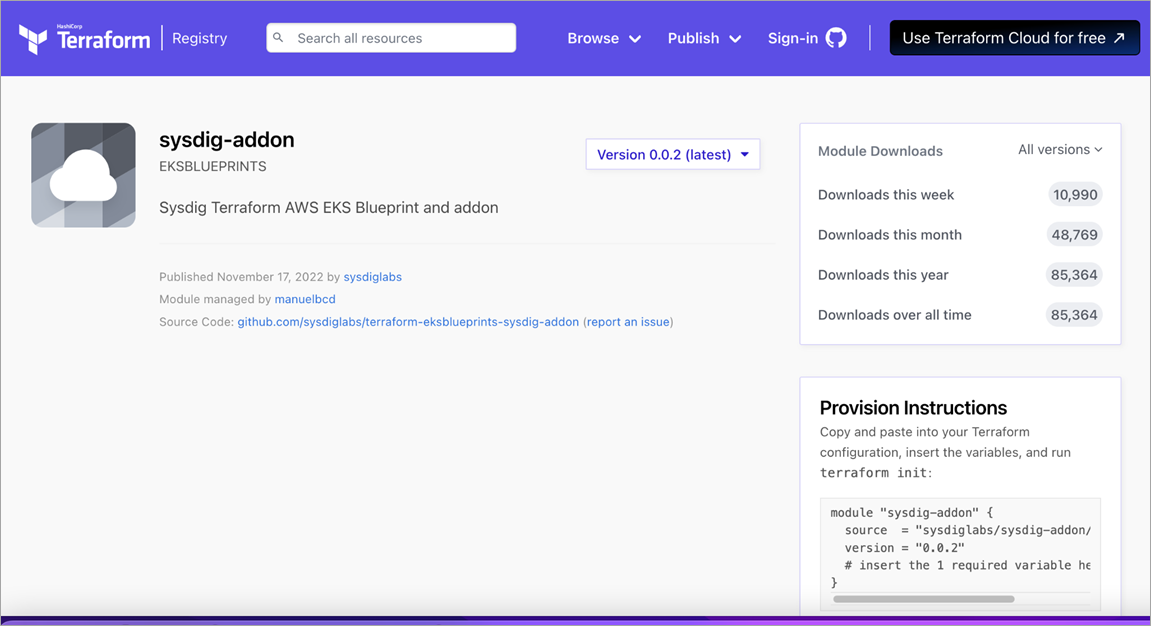
Figure 2 – Sysdig add-on published in Terraform Registry.
Building Blocks
The getting-started blueprint provides the basic foundation to provision a secured EKS cluster with the Sysdig instrumentation pre-installed by default. You can customize and extend the blueprint easily by adding new modules and setting flags in blueprint/main.tf.
Security Lab for Training and Learning
Try the lab-security and configure it with just three basic parameters, and then launch the script. Detected runtime threats and vulnerabilities will start populating your Sysdig user interface (UI) and allow you to learn, play, break, and dig deeper.
Figure 3 – Sysdig Secure user interface.
Monitoring Metrics and Alerts as Code
Try the monitor-alerts blueprint and configure notification channels, set metrics, configure boundaries and alerts—everything defined as code.
Steps to Test the Automation
Choose the blueprint you want to work with, rename terraform.tfvars.example to terraform.tfvars and configure the following parameters:
- Access key: Settings > Agent Installation
- Sysdig region: us1, us2, us3, us4, eu1, au1, custom
- Cluster name of your preference
- aws_region where you are going to deploy the EKS cluster
Now, you can launch the Terraform script with the classic “terraform init – plan – apply” commands.
From Source to Run with Sysdig
Once your Amazon EKS clusters are defined as code, you can leverage all of the services Sysdig brings to secure and monitor your workloads.
Security
- IaC scan to identify misconfigurations and enable drift control. Follow these steps to integrate Sysdig with your Git repository.
- Vulnerability management to scan images in your CI/CD pipeline, registries, admission controller, and at runtime.
- Kubernetes Security Posture Management (KSPM) to manage the defense and compliance of EKS clusters.
- Runtime threat detection to detect and respond to threats, exploits, and malicious activity in containers, hosts, and EKS.
- Forensics analysis (security RCA) to investigate security incidents as well as forward events to SOAR and SIEM platforms.
- Rapid response to quickly take action to address live issues or security events.
Monitoring
- Kubernetes monitoring to observe EKS health and performance and avoid potential problems.
- Cloud infrastructure monitoring to maximize the performance of AWS services.
- Managed Prometheus service to monitor cloud-native applications and services.
- Cloud-native cost advisor to right-size environments and drive cost efficiency.
- Custom metrics to increase visibility into applications and infrastructure
Conclusion
Companies are adopting Kubernetes to boost their ability to deploy and scale with agility, but there are new needs and risks and Sysdig helps organizations to run Kubernetes with confidence.
Using the Sysdig add-on together with Amazon EKS Terraform blueprints, you can reduce the learning curve and train yourself in the adoption of IaC strategies for your infrastructure. The assets deployed with these blueprints will be secured and monitored from day zero.
Please note that while EKS Blueprints is maintained by AWS contributors, it’s still an open-source project and does not come with support like official AWS services. Adopters should be aware of this difference and ensure when using EKS Blueprints to build in the appropriate safeguards and practices when using in production.
You can also learn more about Sysdig in AWS Marketplace.
Sysdig – AWS Partner Spotlight
Sysdig is an AWS Partner that delivers cloud and container security fueled by runtime insights, providing real-time visibility into AWS workloads with automated remediation.