AWS Partner Network (APN) Blog
Driving Continuous Security and Configuration Checks for Amazon EKS with Alcide Advisor
By Yaniv Peleg Ysabari, Head of Product Management at Alcide
By Paavan Mistry, Specialist Security Solutions Architect at AWS
 |
 |
 |
 |
As Kubernetes gradually becomes the leading open-source platform for automating deployment, scaling, and management of containerized applications, more and more Amazon Web Services (AWS) customers are using Kubernetes as their main container orchestration platform.
On AWS, you can easily adopt Kubernetes with a managed service like Amazon Elastic Container Service for Kubernetes (Amazon EKS), or alternatively provision and manage custom Kubernetes clusters with tools such as Kubernetes Operations (Kops).
In this post, we will go over some of the Kubernetes controls that we believe can greatly improve your application security, and specifically, accessing secrets, detecting Kubernetes vulnerabilities, and running specific checks related to Amazon EKS clusters.
We also explain how Alcide Advisor helps ensure your Amazon EKS cluster, nodes, and pods configuration are tuned to run according to security best practices and internal guidelines.
Alcide is an AWS Partner Network (APN) Advanced Technology Partner. As a network security leader, Alcide empowers DevSecOps with code-to-production continuous security, helping customers discover, manage, and enforce security policies for workloads running in Kubernetes.
Overview
Traditional application-level security aims to find issues before they expand, and involves practices such as code reviews, scans, and penetration tests. While these practices are still relevant, they are no longer sufficient in a Kubernetes environment.
Kubernetes provides the freedom to rapidly ship applications by minimizing deployment and service update cycles from weeks to days, and sometimes even hours. The velocity of application updates and deployment, however, requires a continuous security approach that involves integrating tools as early as possible in the deployment pipeline.
Alcide Advisor is an agentless service for Kubernetes audit and compliance that’s built to ensure a frictionless and secured DevSecOps flow by hardening the development stage before moving to production.
Alcide Advisor serves as a one-stop-shop to continuously discover, mitigate, and validate Amazon EKS cluster risks.
With Alcide Advisor, you can cover the following security checks:
- Kubernetes vulnerability scanning.
- Hunting misplaced secrets, or excessive secret access.
- Workload hardening from Pod Security to network policies.
- Istio security configuration and best practices.
- Ingress controllers for security best practices.
- Kubernetes API server access privileges.
- Kubernetes operators security best practices.
Flexible Deployment and Operation
Alcide Advisor can be easily deployed on your Amazon EKS clusters, or any other managed Kubernetes clusters. The deployment process is frictionless, takes less than five minutes, and does not require an agent.
Alcide Advisor can run in two modes:
- Monitor: Continuously scan your cluster to monitor for existing and new security risks.
- CI/CD: Natively integrated with your existing CI/CD automation workflows, such as AWS CodePipeline and Jenkins, to ensure new deployments are secured and don’t possess any new risks.
Discovering and Mitigating Risks
Alcide Advisor scan results display the latest scan on every monitored cluster. By default, a scan runs on every monitored cluster every 24 hours and can be configured as required.
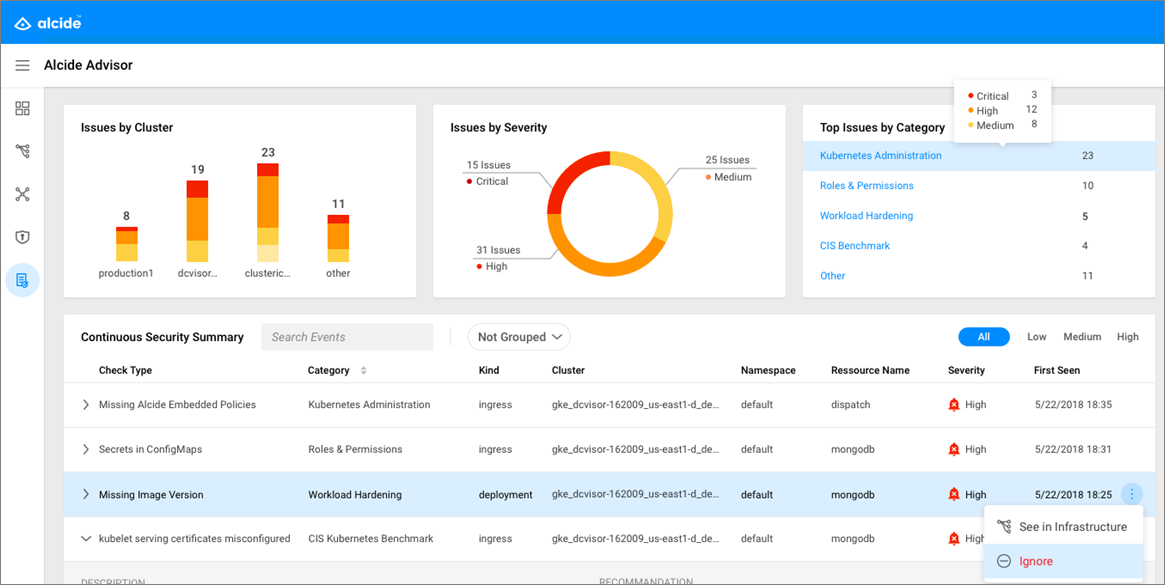
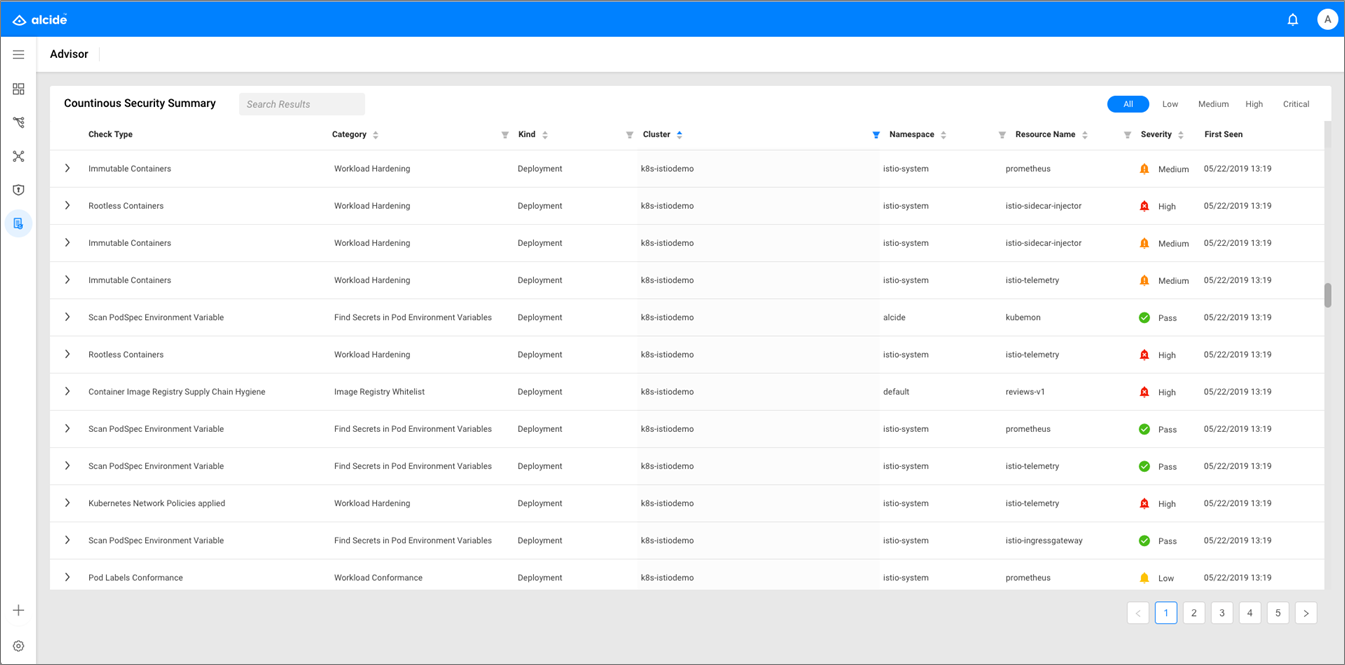
Each result includes a check type with a short description of the detected issue, category the specific check belongs to, cluster, namespace, and resource the issue was detected on, as well as its severity.
In addition, each result provides additional information such as a detailed description, recommended steps you can take to fix the issue based on security best practices, and links to external references with additional details.
On the Alcide dashboard, you can see the time that an issue was first detected through the First Seen table column, to better understand if the issue was already found in previous scans and was not yet fixed.
Figure 1 – Alcide Advisor continuous security summary dashboard.
You can sort and filter any of the table columns, search for specific results to prioritize mitigation actions, and group results by type, resource, or namespace.
Ongoing Checks Provided by Alcide Advisor
Let’s dive into three examples of the ongoing checks the Alcide Advisor provides.
Example 1: Hunting Misplaced Secrets, or Excessive Secret Access
The Kubernetes secret object is designed to store and manage sensitive information, such as passwords, OAuth tokens, and SSH keys. Placing this information in plain text or in the wild (such as config maps) makes it easily exposed to unauthorized users, and is a greater risk for your Kubernetes and cloud provider environments.
Alcide Advisor scans for any secrets, API keys, and passwords that may have been wrongfully misplaced in pod environment variables, as well as in config maps. In addition, it verifies the use of RBAC permissions that defines who can read secret objects.
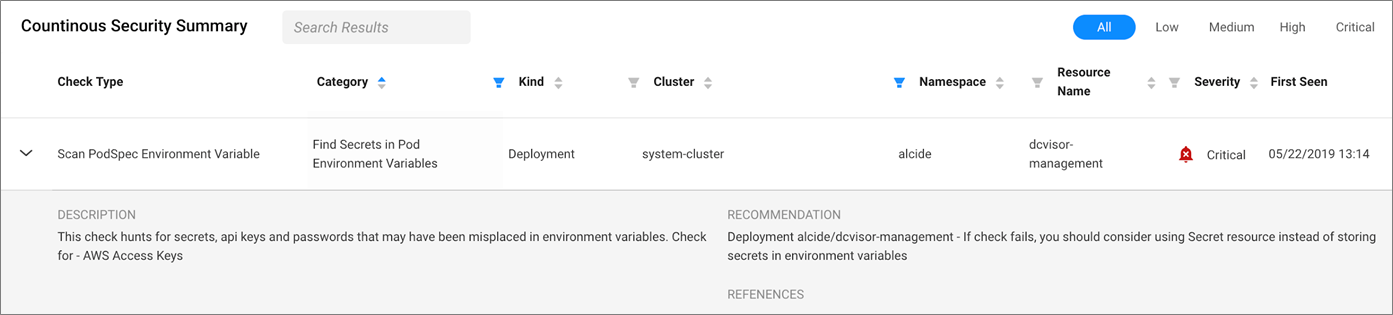
Figure 2 – Secrets found in Pod environment variables.
The information displayed in Figure 2 shows a critical alert stating that an AWS Access Key was found as plain text on the Pod environmental variable. To remediate this risk, DevOps should use the secret object to store this key and thus ensure it is properly secured.
Example 2: Kubernetes Vulnerabilities Scan
While Kubernetes drastically simplifies the orchestration of your most sensitive containerized environments, it’s not bulletproof to critical security vulnerabilities that require quick detection and response.
An example of a serious vulnerability that was recently found is the privilege escalation vulnerability, tracked as CVE-2018-1002105. This vulnerability allows users, through a specially crafted request, to establish a connection through the Kubernetes API server and send arbitrary requests over the same connection directly to that backend. It was authenticated with the Kubernetes API server’s TLS credentials that were used to establish the backend connection.
Alcide Advisor scans your cluster for known vulnerabilities on the master API server and worker node components, including container runtime. This has great benefit for teams using Kops on AWS, as it signals when an upgrade is required.
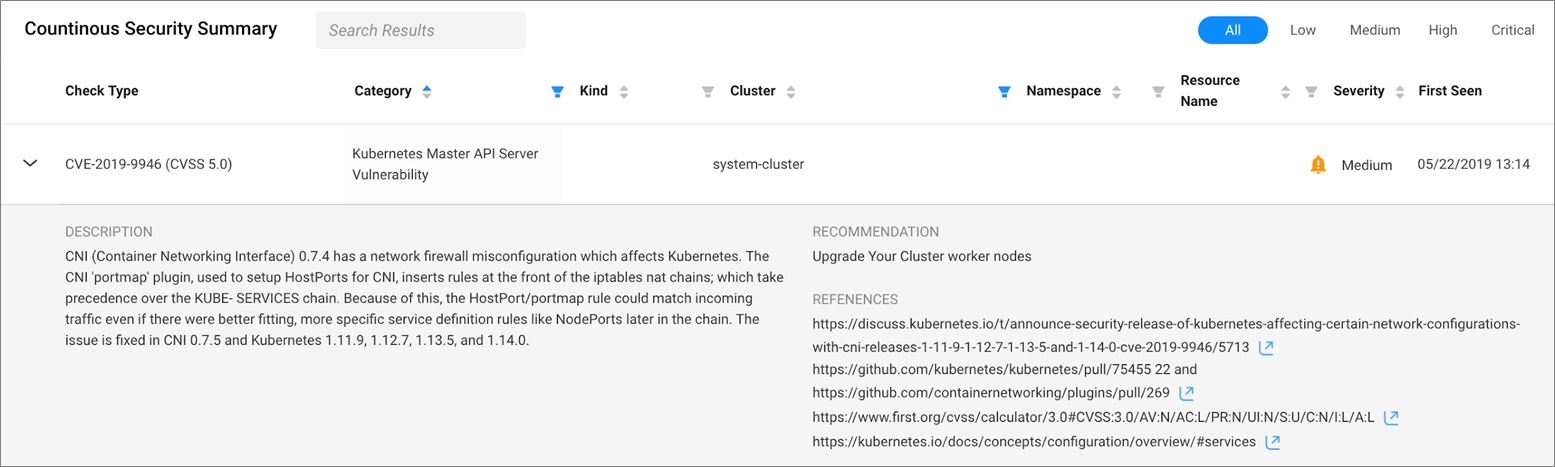
Figure 3 – Continuous security alert on Kubernetes master API server vulnerability.
The alert you see in Figure 3 states that your current Kubernetes API version is exposed to a critical known CVE. Alongside with reference for further reading, the recommendation is to upgrade the Kubernetes cluster to the newest available version.
Example 3: Amazon EKS Cluster Checks
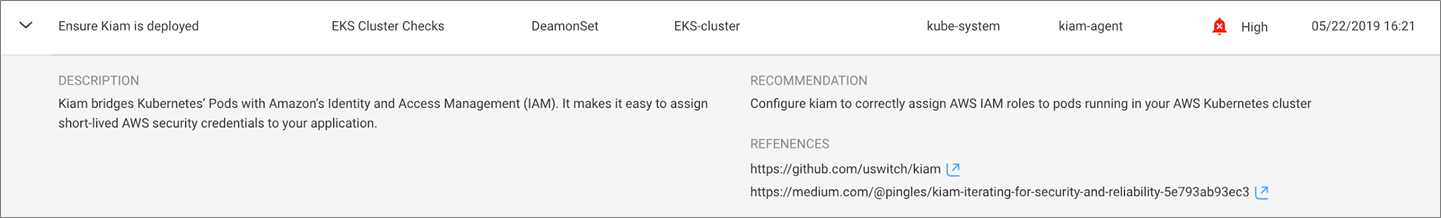
Alcide Advisor provides a set of checks related to Amazon EKS clusters. For example, kiam bridges Kubernetes Pods with AWS Identity and Access Management (IAM) and makes it easy to assign short-lived AWS security credentials to your application.
Kiam runs as an agent on each node in your Kubernetes cluster to allow cluster users to associate IAM roles to Pods. Alcide Advisor scans Amazon EKS clusters and checks for kiam deployment, as you can see in Figure 4 below.
Figure 4 – Configurating kiam to assign IAM modes to pods running in Kubernetes cluster.
App-Formation
The App-formation feature allows you to create a baseline profile on a specific cluster, and get scan results only on issues that deviate from the baseline. This helps DevOps focus on relevant issues and assets that require attention.
App-formation supports the following use cases of:
- Integration with CI/CD pipeline.
- Scalable review of many clusters against a blue print profile.
- Re-run against same cluster and alert on changes compared to baseline profile.
VIDEO: Alcide Advisor App Formation (1:10)
Here’s how to create a baseline profile for your Amazon EKS cluster, and run a scan against that baseline.
Getting Started with Alcide Advisor
To install the Alcide Advisor scanner component, follow the steps below:
- Sign up for a Free Trial.
- Log in to Alcide using the credentials you’ve received.
- Run through the onboarding wizard and configure the cluster you wish to run Advisor scan on.
- In Steps 1-5, you’ll name the Amazon EKS cluster you want to add, and then connect it to a logical entity representing the AWS account it’s running on.
- In Step 6, start by downloading the Alcide CLI tool and run commands 1-3, 5.
Once installed, Alcide Advisor automatically starts scanning your Amazon EKS cluster and provides an immediate scan report. This outlines your cluster’s configuration issues, with actionable recommendations for every scan result.
From this point on, unless configured differently, Alcide Advisor will automatically scan that Amazon EKS cluster every 24 hours.
Alcide Advisor provides many other checks to help you create a secured Amazon EKS deployment and meet security best practices. This includes Cluster Ingress Controllers and Kubernetes Operators Security best practices, Istio security configuration, workload labeling and annotations scheme conformance, Kubernetes dashboard permissions, and more.
Figure 5 – Report of all risks and misconfiguration issues found.
The end result is that you get a report with a summary of the Amazon EKS cluster’s compliance and security status, as well as a detailed list of identified compliance and security issues, with description and recommendation for a quick remediation.
Summary
The inherent complexities for running cloud-native applications such as Kubernetes, especially in a multi-cluster environment, are growing. Alcide Advisor creates a snapshot of your cluster’s security and compliance posture with actionable recommendations to ensure no security drifts are detected only in runtime.
In this post, we demonstrated how Alcide Advisor provides Kubernetes security and compliance check in all levels by answering questions like “Are all of my clusters compliant with the security policies?” and “Am I pulling software from authorized image registries?”
Alcide Advisor also allows DevOps and security teams to discover misplaced secrets or secret access, identify Kubernetes vulnerabilities and perform Amazon EKS cluster checks. These teams can then benefit from continuous, always-on, dynamic analysis of their deployments.
Get Alcide Advisor for free by signing up for a 30-day trial.
You can also download the Solution Brief, and watch the on-demand webinar: Providing Continuous Kubernetes Security through Your CI/CD Pipeline >>
.
 |
 |
Alcide – APN Partner Spotlight
Alcide is an APN Advanced Technology Partner. They empower DevSecOps with code-to-production continuous security, to discover, manage, and enforce security policies for workloads running in Kubernetes.
Contact Alcide | Solution Overview
*Already worked with Alcide? Rate this Partner
*To review an APN Partner, you must be an AWS customer that has worked with them directly on a project.