AWS Partner Network (APN) Blog
How to Bake Open Source Security into Your AWS CodeBuild Pipeline
By Michael Hollander, Product Manager at WhiteSource
 |
 |
 |
 |
Open source security has become a growing concern for organizations the more they are depended on for greater proportions of their company’s software products.
Open source components comprise between 60-80 percent of the codebase in 92 percent of modern applications. Given the scale of their usage and role in many products, open source creates a wide threat surface that can be attacked by hackers.
Managing open source vulnerabilities can be challenging, especially at scale in a fast-moving continuous integration (CI) pipeline. Developers and DevOps professionals depend on CI pipeline tools like AWS CodeBuild to help them develop and test software at a breakneck pace, pushing out new software with greater efficiency and flexibility.
In this post, I will demonstrate how you can integrate WhiteSource into your CodeBuild pipeline to fuse open source security into existing build processes without having to compromise on speed or agility.
WhiteSource Integrations for AWS Users
WhiteSource is an AWS Partner Network (APN) Advanced Technology Partner with the AWS DevOps Competency.
We help businesses track the open source components they are using, detect which ones have known vulnerabilities (including in their direct or transitive dependencies), and ensure vulnerable components aren’t added to products through the automated enforcement of policies.
The WhiteSource integration with CodeBuild allows developers to automate the scanning of any source repository using CodeBuild as part of their CI pipeline. For each scan, security and compliance issues are detected, and suggested remediation options are provided.
WhiteSource Unified Agent Background
WhiteSource’s Unified Agent is a stand-alone command line tool that supports the scanning of multiple package managers, build tools, source files, containerized environments and archives, and integrates with multiple CI/CD tools and repositories.
The Unified Agent enables organizations to simplify their maintenance processes and remain updated while using centralized and templated configurations. It also supports automatic security and compliance thresholds that can be defined and enforced automatically within the SDLC, integrating with build tools to ensure security and compliance.
WhiteSource’s Unified Agent supports more than 200 different programming languages and approximately 30 different package managers. It can be used across the SDLC for both local and remote projects.
Prerequisites
To make sure you can integrate your CodeBuild application with WhiteSource, your build project needs to be set up on a Linux environment.
You will also need to add a buildspec.yml file to your source code root directory. Alternatively, you can store your build commands as a build project configuration using the Buildspec editor in your project.
Note that you will need a licensed WhiteSource account in order to be able to use the Unified Agent and report scanning results back to your account.
Configuration
Step 1
Add the below pre-build phase to your Buildspec. This will fetch a WhiteSource Unified Agent script file to be run as part of your post-build phase.
curl -LJO https://github.com/whitesource/unified-agent-distribution/raw/master/standAlone/wss_agent.sh
Step 2
Add a post-build phase in order to scan your repository using the Unified Agent. In this phase, the script that was downloaded in the previous step will be run.
The script will download the latest version of the Unified Agent executable file along with its default configuration file to your CodeBuild server.
The following command will be used to run the Unified Agent:
bash wss_agent.sh -apiKey $WS_API_KEY -project my-project -d
You will need to provide basic command line arguments to the Unified Agent in order to map the scan to your WhiteSource account into a new or existing project.
- -apiKey: This is the API key for your WhiteSource account. The dynamic value of the key can be obtained by following the instructions of Step 4.
- -project: This should be the name of your project. WhiteSource will create a new project in your WhiteSource organization using this name.
The example below shows a complete Buildspec file containing both pre-build as well as post-build commands required to be able to run the WhiteSource integration.
Full example:
Step 3
Go to your CodeBuild services from the AWS Developer Tools section. Click Create Build Project, or choose an existing project to run WhiteSource on.
Step 4
Next, you will need to add your WhiteSource Organization API key to allow CodeBuild to send results to your specific WhiteSource account. You can obtain the key by navigating to the Integrate page within the WhiteSource application.
There are two ways to map the WhiteSource API key to the “WS_API_KEY” value:
- If you are using the AWS Systems Manager Parameter Store for storing secrets, then this is the preferred way:
- Enter your Parameter Store and click Create Parameter.
- Enter “WS_API_KEY” within the parameter name field and make sure the type is set to String.
- Within the Value field, enter your WhiteSource API key. You can now click Create Parameter.
- Make sure a CodeBuild Service Role is created so that CodeBuild can interact with the relevant Parameter Store.
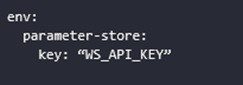
- Lastly, make sure to add an environment key of type parameter-store to the beginning of the Buildspec file:
- If you are not using AWS Systems Manager Parameter Store, you can set up an environment variable through CodeBuild. In order to do so, follow these steps:
- From your build project, click Edit > Environment.
- Then, in the Additional Configuration section, click Add Environment Variable and enter “WS_API_KEY” as the variable name and your WhiteSource API key as the value.
- Make sure the type is set to Plaintext. You can now click Update Environment to save these changes.
Step 5
You can now start a new build in order to activate a WhiteSource scan. Your WhiteSource service will be updated with the details of your project, and a build of your project will be placed inside the Amazon Simple Storage Service (Amazon S3) bucket you have selected in your project’s settings.
You can review the scanning results in your WhiteSource organization under the relevant project.
Tips and Tricks for the Road Ahead
When scanning a multi-module Maven or Gradle project, you can choose to aggregate the project’s modules into a single WhiteSource project. By default, a WhiteSource project will be created for each module.
You can use the ‘-maven.aggregateModules’ or ‘-gradle.aggregateModules’ parameter in this case. Here’s an example:
bash wss_agent.sh -apiKey $ws_api_key -project my-project -d . -maven.aggregateModules true
For more details, see this list of available Unified Agent command-line parameters.
You can also store the Unified Agent configuration file in a remote location. Just pass the -c parameter and provide the remote location of your configuration file. Here’s an example:
bash wss_agent.sh -apiKey $ws_api_key -project my-project -d . -c http://user:password@example.com:8080/wss_unified_agent.config
To learn more, see this list of available Unified Agent usage examples.
Benefits of WhiteSource
WhiteSource makes it easy for companies to manage their open source usage, relying on automated tracking and enforcement to ensure policies are maintained throughout the SDLC.
Here are some of the top benefits you’ll see when using WhiteSource:
- Set policies for what is allowed (security status, licenses, etc.) and what is not, failing the build, if necessary, to ensure that no vulnerable or risky open source components are incorporated into the product.
- The most comprehensive database of open source components and vulnerabilities available, going beyond the National Vulnerability Database to include resources from a wide variety of security advisories and issue trackers.
- Zero false positives with accurate identification of open source components.
- Smarter prioritization for remediations based on the effectiveness of vulnerable components, depending on their actual impact on the security of your product.
Summary
Along with the many benefits of using open source components as building blocks for our software products, open source usage also requires integrating a new set of processes and tools into the software development process to ensure security and compliance.
While it does present a challenge, managing your open source security can be easy. When you put the right solutions in place, you can automatically gain visibility and control over your open source usage.
WhiteSource’s Unified Agent allows you to seamlessly integrate WhiteSource into your SDLC, so that every time you run your build you’ll get a comprehensive overview of your open source usage, along with any existing security or license compliance risks.
Combining WhiteSource and AWS CodeBuild helps you keep up with the speedy pace of building and releasing software, while ensuring that your app is safe from vulnerable or problematic open source components.
Additional AWS Integrations from WhiteSource
WhiteSource works to secure your code throughout the SDLC with integrations for a range of AWS infrastructure services.
WhiteSource for Containers helps teams achieve visibility and policy enforcement within their Amazon Elastic Container Registry (ECR) and Amazon Elastic Kubernetes Services (Amazon EKS), identifying all open source components in your containers and providing the same level of security assurance from start to finish even when your containers are in production.
Our integration for AWS Lambda allows your developers to secure your serverless operations no matter how diffuse they may be.
Next Steps
- Find out more about the WhiteSource Unified Agent.
- Get more information about the WhiteSource CodeBuild integration.
- Check if your programming language is supported by WhiteSource.
- Start your free trial with WhiteSource.
The content and opinions in this blog are those of the third party author and AWS is not responsible for the content or accuracy of this post.
.
WhiteSource – APN Partner Spotlight
WhiteSource is an AWS DevOps Competency Partner that allows you to gain full visibility and control over your open source usage. It runs silently in the background, detecting all open source components in the code, including transitive dependencies, every time a build is run or a commit has been performed.
Contact WhiteSource | Solution Overview | AWS Marketplace
*Already worked with WhiteSource? Rate this Partner
*To review an APN Partner, you must be an AWS customer that has worked with them directly on a project.
