AWS Partner Network (APN) Blog
Simplicity and Security Through Centralized Application Delivery and F5 Networks
 |
 |
 |
 |
By Greg Coward, Solution Architect at F5 Networks
As a solution architect focusing on public clouds, I spend a fair amount of time with customers and partners discussing various topics such as “lift and shift” and “hybrid deployments.”
Whether shifting existing applications or developing cloud-native solutions, there are tremendous benefits with regards to scalability and availability gained from the Amazon Web Services (AWS) Cloud. There are also challenges encountered when extending your applications to the cloud.
In a typical organization, NetOps needs to ensure the infrastructure used to support application delivery is configured with consideration towards performance, scalability, and availability. Likewise, SecOps needs to ensure that applications, regardless of where they are deployed, are done so in a consistent and secure manner.
Meanwhile, the application owner or DevOps is looking for a simple way to deploy their applications while adhering to corporate policy. These challenges only increase as the corporate footprint expands outside the datacenter walls.
In this post, I’ll walk through a typical application deployment utilizing the F5 BIG-IP Cloud Edition to provide a centralized point of control for provisioning, configuring, and managing F5 BIG-IP application delivery controllers.
F5 is an AWS Partner Network (APN) Advanced Technology Partner with AWS Competencies in both Networking and Security.
F5 BIG-IP Cloud Edition
F5 BIG-IP Cloud Edition is currently available for VMware and AWS environments and consists of multiple components, including F5 BIG-IQ Centralized Management, F5 BIG-IQ Data Collection, and F5 Per-App Virtual Edition (VE).
- BIG-IQ Centralized Management: The BIG-IQ (among other services) centralizes the configuration, deployment, and management of Service Scaling Groups (SSGs). Additionally, BIG-IQ provides the tenant portal and hosts the visibility/analytics dashboard.
- BIG-IQ Data Collection Device (DCD): The DCD handles data collection, processing, and storage.
- BIG-IP Per-App VEs: Per-App VEs are deployed into SSGs and provide advanced traffic management and web application firewall security on a per-app basis.
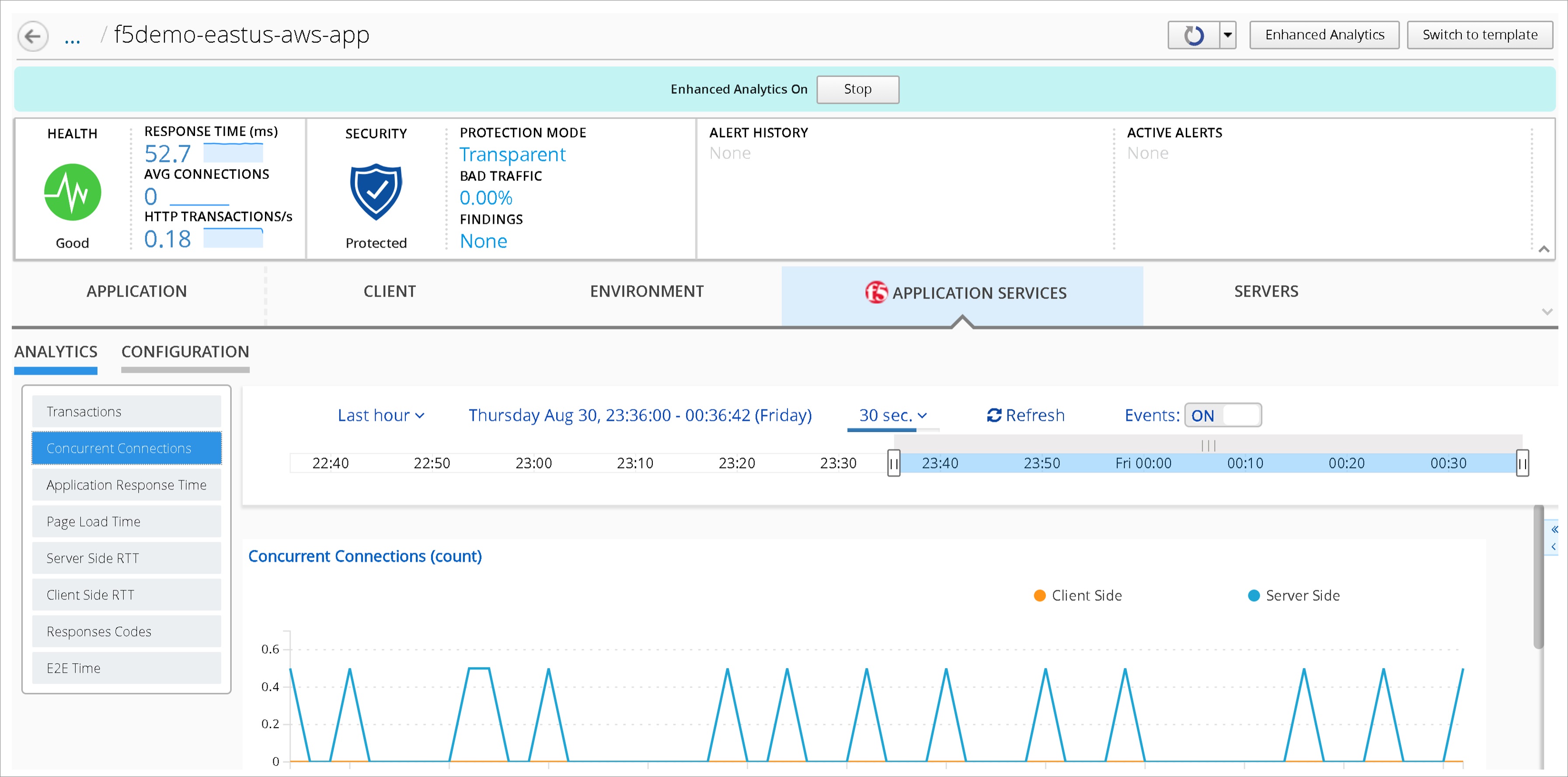
These components combine to provide the ability to apply secure and consistent traffic policies across all applications, regardless of where they reside. By utilizing SSGs, I get the scalability and availability I need to right-size my BIG-IP VEs and deliver services efficiently. Additionally, as illustrated in Figure 1, F5 BIG-IP Cloud Edition provides enhanced visibility and analytics for all my applications regardless of where they are deployed.
Figure 1 – BIG-IQ Centralized Management provides enhanced infrastructure and application analytics.
BIG-IQ utilizes Role-Based Access Control (RBAC) to provide separation of responsibilities. DevOps and application owners utilize self-service templates to securely deploy their applications onto SSGs, which are created and managed by infrastructure owners.
This allows the app owner to focus on their application, and NetOps/SecOps have the peace of mind knowing that applications are deployed in a consistent and secure manner.
Deployment Process Overview
Let’s take a closer look at a typical (albeit simplified) deployment scenario. I have a copy of my application deployed on-premises, as well as one in my AWS account. To improve availability and address the needs of an expanding market, I will extend my application’s footprint to an additional AWS region, as shown in Figure 2.
Figure 2 – Hybrid application environment.
Both deployments—AWS and on-premises—are hosted on SSGs deployed from and managed by BIG-IQ.
F5 BIG-IP DNS, hosted on AWS and on-premises, is used to provide Global Server Load Balancing (GSLB). Additionally, I have established an IPSec VPN tunnel between the datacenter and Virtual Private Clouds (VPCs) to enable secure deployment and management of AWS-hosted resources.
For the remainder of this post, in the role of NetOps/SecOps, I will deploy an additional SSG in the EU London region of my AWS account. Afterwards, as an application owner, I will use a pre-configured application template to publish a copy of the application.
Deploying Service Scaling Groups
In this step, I utilize the BIG-IQ centralized management interface to configure and deploy an SSG consisting of per-app BIG-IP VEs.
Aside from the similar names, SSGs and Auto Scaling Groups are closely related. When you deploy an SSG to AWS, BIG-IQ provisions an Auto Scaling Group of BIG-IPs.
By deploying out of BIG-IQ, I have a single pane of glass for managing all application instances regardless of where they reside, as well as providing a holistic view of my application with enhanced reporting and analytics.
Configure SSG Components
There are three components I configure to enable SSG provisioning on AWS:
- Device Template
- Cloud Provider
- Cloud Environment
- License Pool (optional)
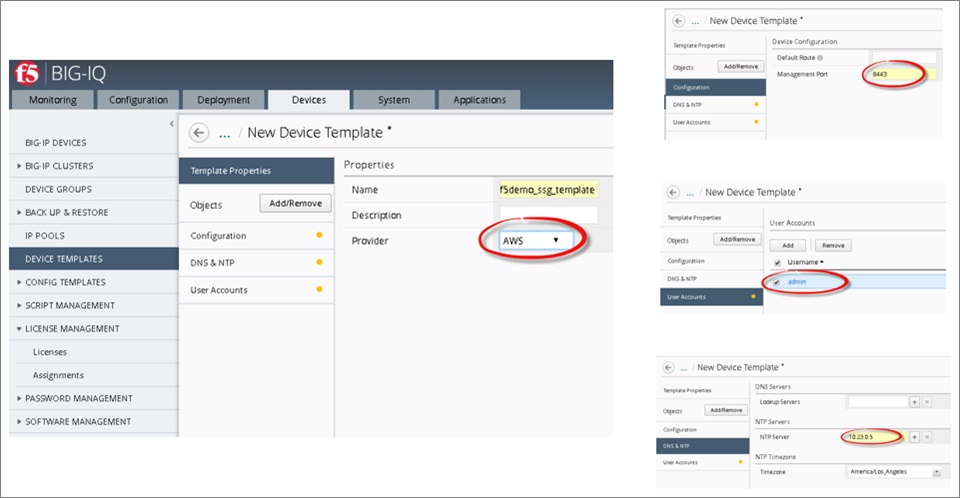
Device Template
I need to provide a few pieces of information, as shown in Figure 3, that are specific to my deployment environment. This includes management port, admin password, and more. Since I will be deploying these devices to AWS, there will be less information required.
Figure 3 – Device templates are used for configuring service scaling groups.
Cloud Provider
The cloud provider in Figure 4 securely stores the AWS credentials I provide for remote configuration and management. I select the appropriate provider, enter my access key ID, and secret access key.
Figure 4 – Cloud providers supply credentials for interacting with AWS infrastructure.
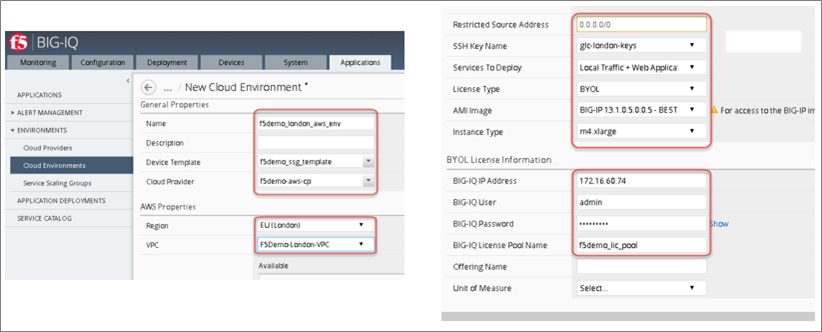
Cloud Environment
The cloud environment stores resource information related to the AWS instance, including associating my previously-created device template and cloud provider. Once selected, AWS pre-populates several of the remaining fields with information gathered from my account.
I have elected to use the BYOL image available in the selected region, as shown in Figure 5. Rather than licensing individual BIG-IPs, I’ll use a pool of licenses with my BIG-IQ to automate the BIG-IP licensing process. This way, licenses are provisioned/de-provisioned as needed.
Figure 5 – Cloud environments configure desired instance settings for SSG deployment.
Deploy SSG onto AWS
Now that I have the appropriate pieces in place, it’s simply a matter of navigating to the Service Scaling Groups tab and selecting Create. I select my desired scaling policy and alert thresholds, as shown in Figure 6. These settings can be modified after deployment.
Figure 6 – Deploying a new Service Scaling Group.
After the SSG has been successfully deployed, I should see the resources (Auto Scaling Groups, compute instances, etc.) created in my AWS account, as well as noted on my BIG-IQ dashboard as shown in Figure 7.
Figure 7 – Service Scaling Group deployed into AWS environment.
Deploying the Application Configuration
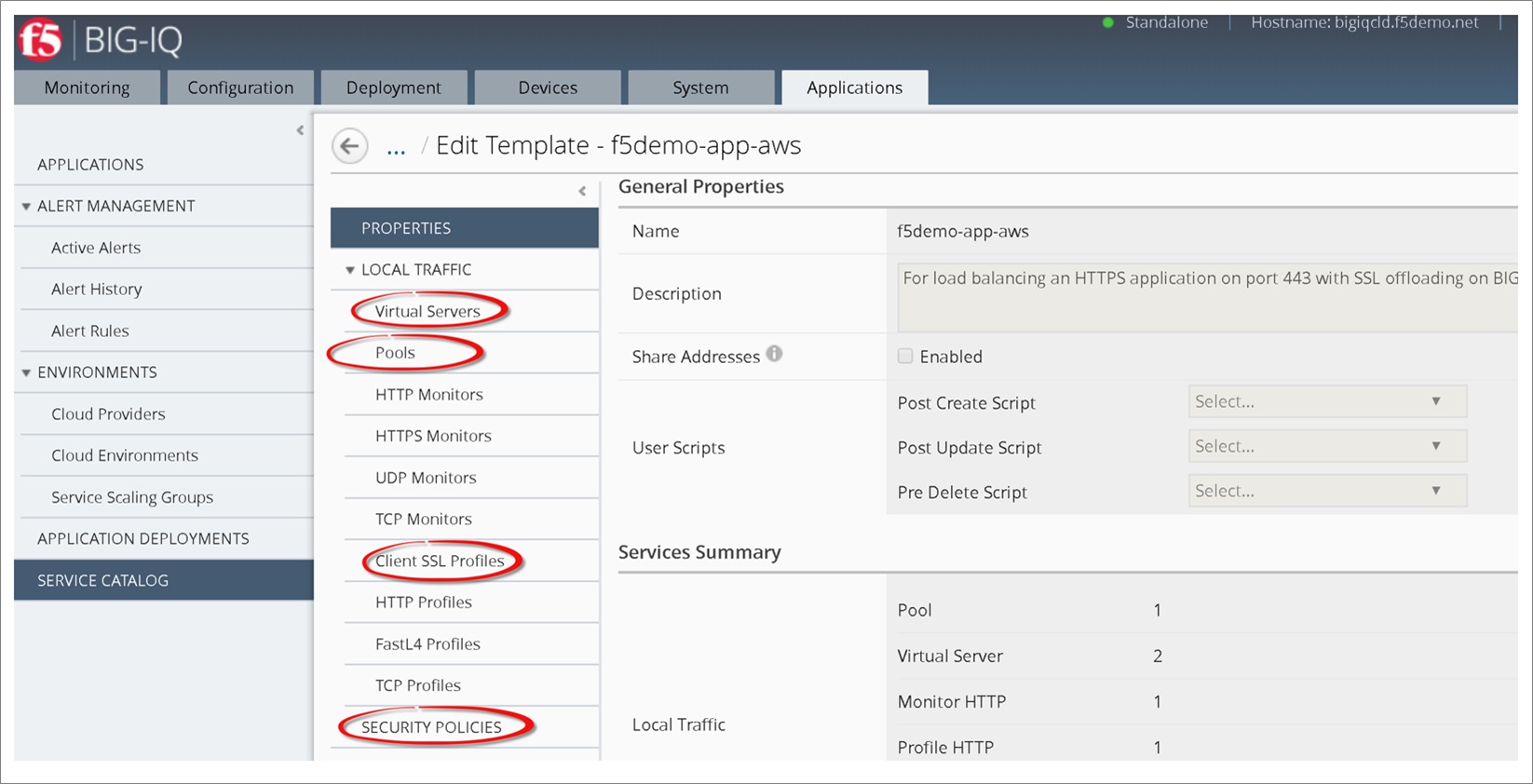
Now that we have the SSG deployed, there’s one last task for NetOps/SecOps before it can be turned over to the application owner.
Application templates provide the application owner self-service application publishing. The template contains all the information required—virtual servers, pool members, WAF policies—to configure the BIG-IP VEs.
The template in Figure 8 can be created and published by NetOps/SecOps and assigned to application owners.
Figure 8 – Application templates configure SSGs with application-specific traffic management services.
Deploy the Application
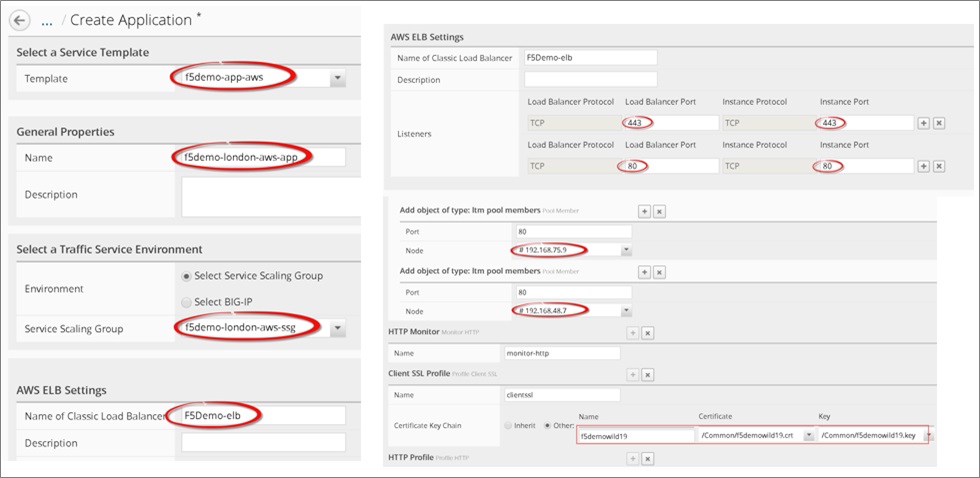
Now that I have an application template available to me, it’s time to publish my AWS-hosted application. I navigate to the Applications tab and select Create. As the application owner, there’s just a small amount of information required to publish my application.
On this page, shown in Figure 9, I will accept/select various application-specific settings, such as ports, certificates, pool members, and the SSG where I will deploy my application. Additionally, I will need to provide the name of an Elastic Load Balancing resource in my subscription. BIG-IQ uses this to load balance application requests across the SSG.
Figure 9 – Deploying a new application into the Service Scaling Group.
Now that we have completed the deployment, I have a third copy of the application deployed in the AWS EU London region.
Figure 10 – New application deployed.
Summary
Managing hybrid cloud deployments can be challenging. As enterprises continue to expand to the AWS Cloud, the need for centralized traffic management becomes even more critical.
Additionally, as the pace of application development increases, DevOps and application owners need a secure and reliable platform on which to deploy their apps. Fortunately, the F5 BIG-IQ Cloud Edition provides a central point of control for all your applications, regardless of where they live.net
Next Steps
Learn more about F5’s products and services, including F5 BIG-IQ Cloud Edition. We also offer evaluation versions if you’re interested in trying out the BIG-IP or BIG-IQ in their own environments.
The content and opinions in this blog are those of the third party author and AWS is not responsible for the content or accuracy of this post.
.
 |
 |
F5 Networks – APN Partner Spotlight
F5 is an AWS Competency Partner. They provide an advanced monitoring solution for cloud apps and modern infrastructure that aggregates metrics across distributed services to alert you on service-wide issues and trends in real-time—versus host-specific errors well after the fact—addressing critical application and infrastructure.
Contact F5 | Practice Overview | Buy on Marketplace
*Already worked with F5? Rate this Partner
*To review an APN Partner, you must be an AWS customer that has worked with them directly on a project.