AWS News Blog
Category: Amazon EC2
AWS Week in Review – June 13, 2022
This post is part of our Week in Review series. Check back each week for a quick roundup of interesting news and announcements from AWS! Last Week’s Launches I made a short trip to Austin, Texas last week in order to visit and learn from some customers. As is always the case, the days when […]
New – Amazon EC2 R6id Instances with NVMe Local Instance Storage of up to 7.6 TB
In November 2021, we launched the memory-optimized Amazon EC2 R6i instances, our sixth-generation x86-based offering powered by 3rd Generation Intel Xeon Scalable processors (code named Ice Lake). Today I am excited to announce a disk variant of the R6i instance: the Amazon EC2 R6id instances with non-volatile memory express (NVMe) SSD local instance storage. The […]
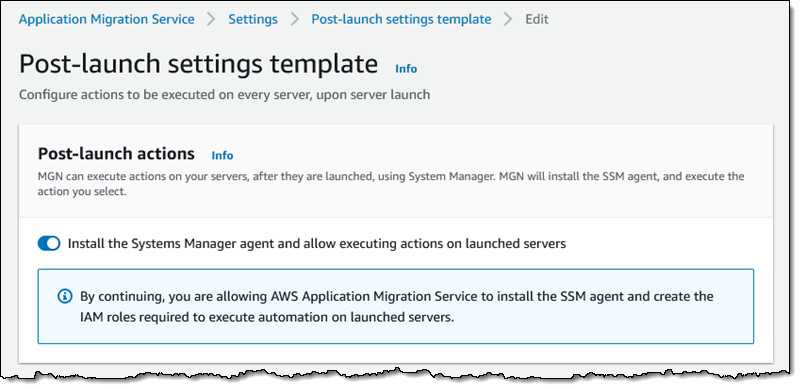
AWS MGN Update – Configure DR, Convert CentOS Linux to Rocky Linux, and Convert SUSE Linux Subscription
Just about a year ago, Channy showed you How to Use the New AWS Application Migration Server for Lift-and-Shift Migrations. In his post, he introduced AWS Application Migration Service (AWS MGN) and said: With AWS MGN, you can minimize time-intensive, error-prone manual processes by automatically replicating entire servers and converting your source servers from physical, […]
AWS Week In Review – May 30, 2022
Today, the US observes Memorial Day. South Korea also has a national Memorial Day, celebrated next week on June 6. In both countries, the day is set aside to remember those who sacrificed in service to their country. This time provides an opportunity to recognize and show our appreciation for the armed services and the important […]
New – Amazon EC2 M6id and C6id Instances with Up to 7.6 TB Local NVMe Storage
Last year, we launched the Amazon EC2 M6i instances and C6i instances, our sixth-generation offerings that include 3rd generation Intel Xeon Scalable processors. Today we are expanding Amazon EC2 M6id and C6id instances, backed by NVMe-based SSD block-level instance storage physically connected to the host server. These instances are powered by the Intel Xeon Scalable […]
New – Amazon EC2 C7g Instances, Powered by AWS Graviton3 Processors
I am excited to announce that Amazon Elastic Compute Cloud (Amazon EC2) C7g instances powered by the latest AWS Graviton3 processors that have been available in preview since re:Invent last year are now available for all. Let’s decompose the name C7g: the “C” instance family is designed for compute-intensive workloads. This is the 7th generation […]
AWS Week In Review – May 23, 2022
This post is part of our Week in Review series. Check back each week for a quick roundup of interesting news and announcements from AWS! This is the right place to quickly learn about recent AWS news from last week, in just about five minutes or less. This week, I have collected a couple of […]
Amazon EC2 Now Supports NitroTPM and UEFI Secure Boot
In computing, Trusted Platform Module (TPM) technology is designed to provide hardware-based, security-related functions. A TPM chip is a secure crypto-processor that is designed to carry out cryptographic operations. There are three key advantages of using TPM technology. First, you can generate, store, and control access to encryption keys outside of the operating system. Second, […]