AWS News Blog
New – Encrypted EBS Boot Volumes
Encryption is an important part of any data protection strategy. Over the past year or two, we have introduced many features that are designed to simplify the task of storing your cloud-based information in encrypted form. Many of these features make use of the AWS Key Management Service (KMS); here are some of the more recent announcements on that topic:
- Encryption at Rest for Amazon Aurora.
- Encrypted Storage Volumes for Amazon WorkSpaces.
- S3 SSE-KMS Encryption for AWS CloudTrail.
- S3 Encryption Integrated with Amazon EMR.
- KMS Encryption for Amazon RDS.
- Encryption for Elastic Transcoder.
- EBS Data Volume Encryption.
To learn more, check out the AWS Services That Offer Encryption Integrated with AWS KMS.
Many customers tell me that they appreciate the fact that AWS makes it very easy for them to encrypt their data. They enable it as needed, and rely on AWS for the heavy lifting.
Encrypted EBS Boot Volumes
Today we are launching encryption for EBS boot volumes. This feature builds on a recent release that allowed you to copy an EBS snapshot while also applying encryption.
You can now create Amazon Machine Images (AMIs) that make use of encrypted EBS boot volumes and use the AMIs to launch EC2 instances. The stored data is encrypted, as is the data transfer path between the EBS volume and the EC2 instance. The data is decrypted on the instance on an as-needed basis, then stored only in memory.
This feature will aid your security, compliance, and auditing efforts by allowing you to verify that all of the data that you store on EBS is encrypted, whether it is stored on a boot volume or on a data volume. Further, because this feature makes use of KMS, you can track and audit all uses of the encryption keys.
Each EBS backed AMI contains references to one or more snapshots of EBS volumes. The first reference is to an image of the boot volume. The others (if present) are to snapshots of data volumes. When you launch the AMI, an EBS volume is created from each snapshot. Because EBS already supports encryption of data volumes (and by implication the snapshots associated with the volumes), you can now create a single AMI with a fully-encrypted set of volumes. You can, if you like, use individual Customer Master Keys in KMS for each volume.
Creating an Encrypted EBS Boot Volume
The process of creating an encrypted EBS boot volume begins with an existing AMI (either Linux or Windows). If you own the AMI, or if it is both public and free you can use it directly. Otherwise, you will need to launch the AMI, create an image from it, and then use that image to create the encrypted EBS boot volume (this applies, for example, to Windows AMIs). The resulting encrypted AMI will be private; you cannot share it with another AWS account.
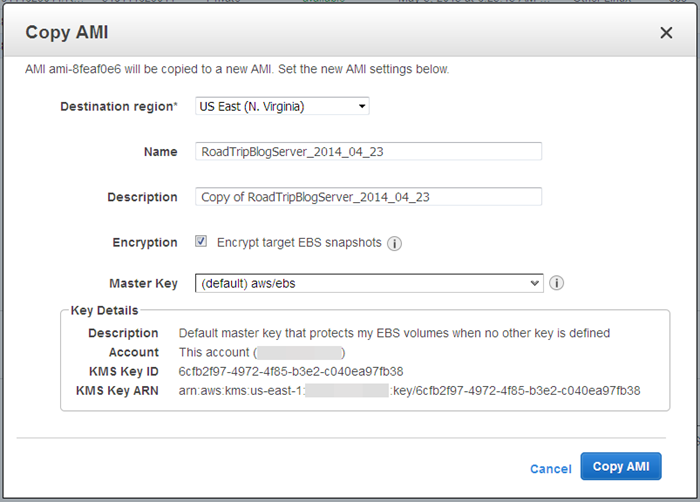
With the AMI and the encrypted snapshot in hand, you simply create a new AMI using the AWS copy-image command as follows:
$ aws ec2 copy-image -r source_region -s source_ami_id \
[-n ami_name] [-d ami_description] [-c token] \
[--encrypted] [--kmsKeyID keyid]If you request encryption with --encrypted and do not supply the --kmsKeyID parameter, the default EBS Customer Master Key (CMK) for your account will be used.
For example, here is how you would make a copy of the Amazon Linux AMI:
$ aws ec2 copy-image --source-region us-west-2 --source-image-id ami-60b6c60a \
--region us-east-1 --name "JeffProdAMI" --encrypted \
--kms-key-id arn:aws:kms:us-west-2:012345678910:alias/Jeff-Master-KeyYou can also create an AMI with an encrypted boot volume from the EC2 Console:
Using an Encrypted EBS Boot Volume
After you create your new AMI, you can use it to launch new instances as usual. You don’t need to make any other changes to your code or your operational practices.
Available Now
This new feature is available now in all AWS regions except China (Beijing) and you can start using it today at no additional charge.
— Jeff;
PS – The EBS team is hiring! Check out the EBS Careers page for more info.