AWS Business Intelligence Blog
Simplify business intelligence identity management with Amazon Quick Suite and AWS IAM Identity Center
 |
All your trusted BI capabilities of Amazon Quick Sight now come with powerful new AI features that integrate chat agents, deep research, and automation in one seamless experience with Amazon Quick! Learn more » |
March 2026: This post was reviewed and updated for accuracy.
Amazon Quick Suite is now an AWS IAM Identity Center enabled application. This capability allows administrators that subscribe to Quick Suite to use IAM Identity Center to enable their users to login using their existing credentials.
Quick Sight as a part of Quick Suite is a scalable, serverless, machine learning (ML)-powered business intelligence (BI) solution that makes it simple to connect to your data, create interactive dashboards, get access to ML-enabled insights, enable natural language querying of your data, and share visuals and dashboards with tens of thousands of internal and external users, either within Quick Sight itself or embedded into another application.
IAM Identity Center helps you securely create or connect your workforce identities and manage their access centrally across AWS accounts and applications. IAM Identity Center is the recommended approach for workforce authentication and authorization on AWS for organizations of varying size and type. With IAM Identity Center, you can create and manage user identities in AWS, or connect your existing identity source, including Microsoft Active Directory, Okta, Ping Identity, JumpCloud, Google Workspace, and Azure Active Directory (Azure AD).
With this release, administrators can create a new Quick Suite account and select IAM Identity Center to configure Quick Suite with their organization’s identity provider or with the IAM Identity Center identity store without requiring additional single sign-on configuration in Quick Suite. They can use a supported identity provider’s groups to assign Quick Sight roles within Quick Suite (administrator, author and reader) to users. Amazon Quick Suite users can seamlessly sign-in to Quick Suite with their organization’s identity provider from the AWS access portal or directly from Quick Suite and share assets with users and groups.
In this post, we show how to simplify your BI identity management with Quick Suite and IAM Identity Center.
Use case overview
AnyCompany Inc. is a fictitious organization in the healthcare space. They have an application for hospitals across different regions of the country that manages business operations. AnyCompany has thousands of healthcare employees accessing the application portal. Being in the healthcare and life sciences industry, AnyCompany handles sensitive data and centrally securing user access is critical to meet business and compliance requirements. AnyCompany already configured Okta with IAM Identity Center. This configuration enables identity and access management for IAM Identity Center enabled applications. This post will go through the steps for AnyCompany to sign up to Quick Suite with IAM Identity Center.
Solution Overview
When enabled with an external identity provider like Okta, signing up to Quick Suite with IAM Identity Center enables the following sign-in flows:
- Quick Suite service provider (SP) initiated sign-in
The user loads the Quick Suite application URL and is automatically redirected to the sign-in page of the configured IdP. Upon successful authentication, the user is redirected to Quick Suite. The following diagram illustrates this flow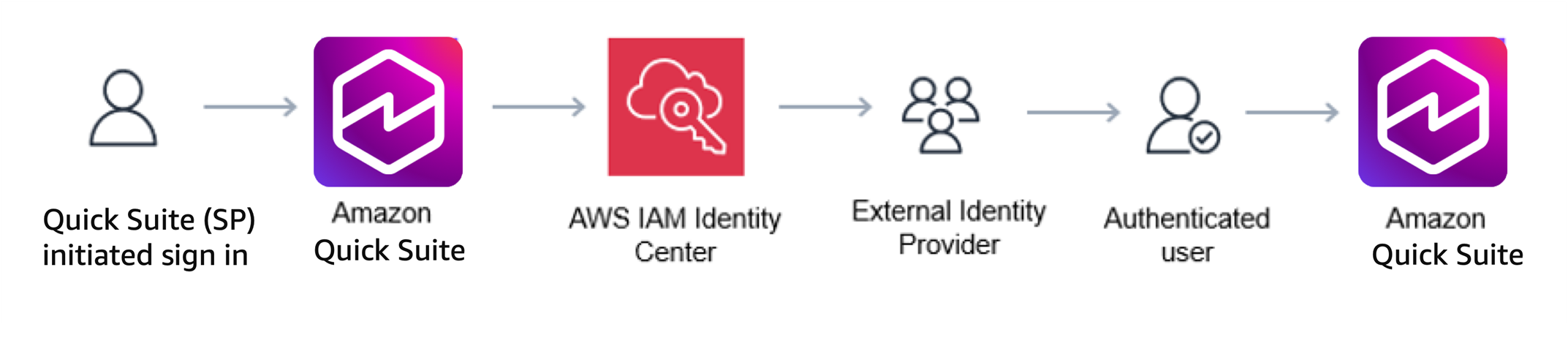
- AWS access portal SP initiated sign in
The user loads the AWS access portal URL and is automatically redirected to the sign-in page of the configured IdP. After authentication, the user chooses the Quick Suite application tile in the AWS access portal and is redirected to Quick Suite. The following diagram illustrates this flow.

- External IdP initiated sign-in
The user navigates to the application portal hosted by the IdP and is authenticated. They select the IAM Identity Center AWS access portal. The AWS access portal loads and shows enabled applications like Quick Suite. The user chooses the Quick Suite application tile, and is automatically redirected to Quick Suite.

Prerequisites
To complete this walkthrough, you must have the following:
- Organizations and IAM Identity Center enabled.
- Okta configured as an IdP in IAM Identity Center. For instructions, refer to Okta.
- An AWS account for Quick Suite in the same organization as IAM Identity Center. This account should not currently be subscribed to Quick Suite.
- The administrator needs AWS Identity and Access Management(IAM) administrator access or Quick Suite and IAM Identity Center permissions. For more information, refer to IAM policy examples for Amazon Quick Suite
Subscribe to Quick Suite with IAM Identity Center
To subscribe to Quick Suite, complete the following steps:
- Sign in to your AWS account and open Quick Suite from the AWS Management Console. You can find it under Analytics or by searching for
Quick Suite.
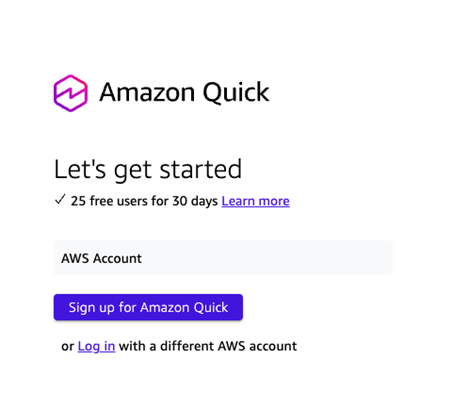
- Choose Sign up for Quick Suite.
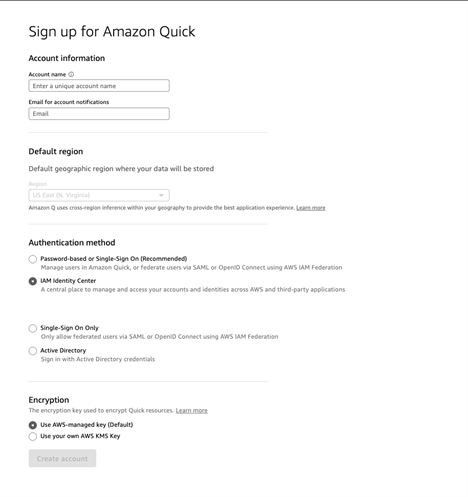
- Enter a notification email address for the Quick Suite account owner or group. This email address receives service and usage notifications.
- Select the identity option that you want to subscribe with. For this post, we select Use AWS IAM Identity Center.
- Enter an account name. Choose Configure.
- Next, you assign groups in IAM Identity Center to roles in Quick Suite (admin, author and reader.) This step enables your users to access the Quick Suite application. If you are using an external identity provider, the groups that you plan to use to assign users to roles in Quick Suite need to be assigned to the IAM Identity Center application. For more details on how to do this with Okta, refer to this step from the prerequisite configuration of Okta and IAM Identity Center. If you cannot find a group from your external identity provider from Quick Suite, the group likely hasn’t yet been assigned to the IAM Identity Center application in your external identity provider. If you are not using an external identity provider, your IAM Identity Center groups are ready to use in Quick Suite. A common way to create groups for role group assignation is to create a group of users for each role:
QuickSuiteAdmins,QuickSuiteAuthorsandQuickSuiteReaders. In Okta, you can create rules based on attributes in your external identity provider to automatically add users to those groups. - Search for a group from IAM Identity Center for each Quick Suite role. Note that you can add additional groups after your sign up is complete from the Manage Users page in the Quick Suite administration console. From this page, click on Manage role groups.
- Select an IAM role to control Quick Suite access to your AWS resources. For more information, see Accessing AWS resources.
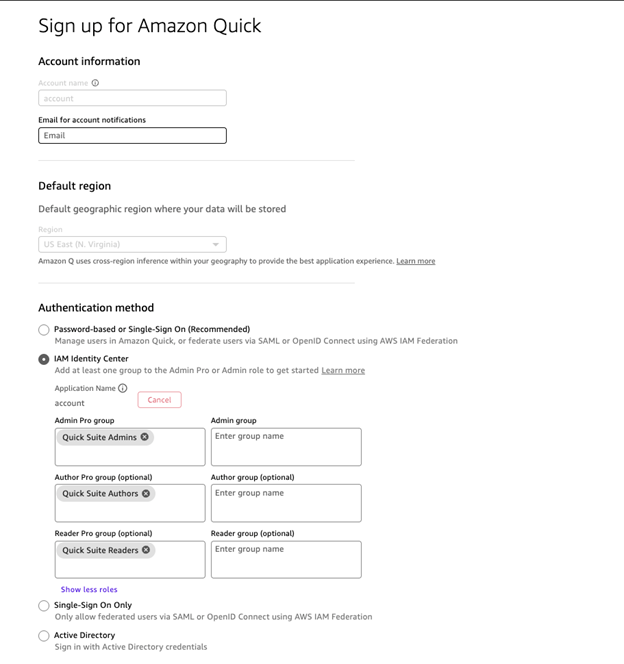
- You can optionally select the Pixel-Perfect Reports add-on.

- Review the choices that you made, then choose Finish.
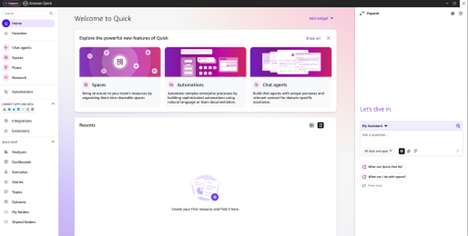
- Choose Go to Amazon Quick Suite.
Validate user sign-in to Quick Suite
Now you can validate that users are able to sign-in to Quick Suite using both the IdP-initiated flow and SP-initiated flow.
Verify IdP initiated flow:
Complete the following steps to test the IdP-initiated flow:
- Navigate to the Okta console and log in with a user who is a member of one of the groups that you assigned to be Quick Suite Admins, Authors or Readers.

Once logged in on the dashboard, users will be able to see the assigned Identity Center application.
- Choose the AWS IAM Identity Center application from the list of applications available.

This will bring you to the IAM Identity Center landing page with a list of applications.
- Choose the QuickSight application from the list to navigate to Quick Suite.

- This will automatically log you into Quick Suite.
Validate the SP-initiated flow:
To validate the SP-initiated flow, complete the following steps:
- Navigate to https://quicksight.aws.amazon.com
- On the landing page, enter the account name used during Quick Suite sign up, then choose Next.
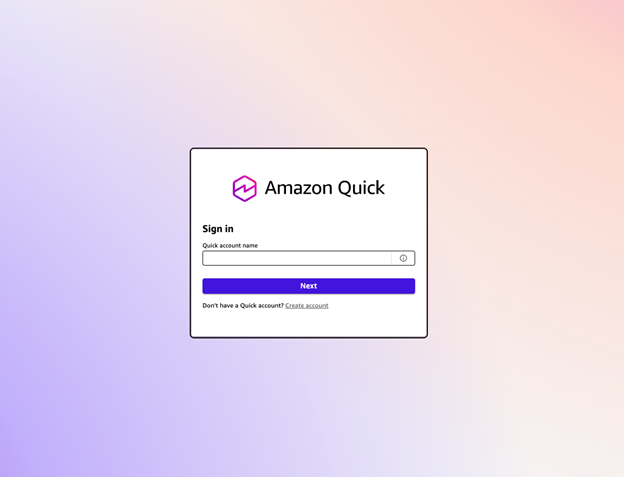
This will automatically redirect you to Okta sign-in page
- Enter your Okta credentials to login.

Upon successful authentication, you will be redirected to Quick Suite.

Conclusion
This post provided step-by-step instructions to sign up for Quick Suite with IAM Identity Center and assign groups to roles in Quick Suite. Quick Suite automatically detects the IAM Identity Center instance in the account’s organization and doesn’t require additional single sign-on configuration in Quick Suite. Amazon Quick Suite users can seamlessly sign-in to Quick Suite with their organization’s identity provider from the AWS access portal or directly from Quick Suite and share assets with users and groups. For more details, see Configure your Amazon Quick Suite account with IAM Identity Center.
For additional discussions and help getting answers to your questions, check out the Quick Suite Community.
About the authors
 Camille Taylor is a Sr Technical Product Manager focused on Quick Suite Administration and Identity Management at AWS. She has been a consultant advising Fortune 500 companies on how to derive value from their data and scale adoption of their business intelligence investments across industries. Earlier in her career, she worked in financial services consumer product valuations and analytics. In her spare time, she likes to cycle, run and engage with the latest analytical consumer tech.
Camille Taylor is a Sr Technical Product Manager focused on Quick Suite Administration and Identity Management at AWS. She has been a consultant advising Fortune 500 companies on how to derive value from their data and scale adoption of their business intelligence investments across industries. Earlier in her career, she worked in financial services consumer product valuations and analytics. In her spare time, she likes to cycle, run and engage with the latest analytical consumer tech.
 Srikanth Baheti is a Specialized World Wide Principal Solutions Architect for Amazon Quick Suite. He started his career as a consultant and worked for multiple private and government organizations. Later he worked for PerkinElmer Health and Sciences & eResearch Technology Inc, where he was responsible for designing and developing high traffic web applications, highly scalable and maintainable data pipelines for reporting platforms using AWS services and Serverless computing.
Srikanth Baheti is a Specialized World Wide Principal Solutions Architect for Amazon Quick Suite. He started his career as a consultant and worked for multiple private and government organizations. Later he worked for PerkinElmer Health and Sciences & eResearch Technology Inc, where he was responsible for designing and developing high traffic web applications, highly scalable and maintainable data pipelines for reporting platforms using AWS services and Serverless computing.
 Raji Sivasubramaniam is a Sr. Solutions Architect at AWS, focusing on Analytics. Raji is specialized in architecting end-to-end Enterprise Data Management, Business Intelligence and Analytics solutions for Fortune 500 and Fortune 100 companies across the globe. She has in-depth experience in integrated healthcare data and analytics with wide variety of healthcare datasets including managed market, physician targeting and patient analytics.
Raji Sivasubramaniam is a Sr. Solutions Architect at AWS, focusing on Analytics. Raji is specialized in architecting end-to-end Enterprise Data Management, Business Intelligence and Analytics solutions for Fortune 500 and Fortune 100 companies across the globe. She has in-depth experience in integrated healthcare data and analytics with wide variety of healthcare datasets including managed market, physician targeting and patient analytics.
 Sumit Dhuwalia is a Technical Account Manager at AWS focused on helping ISV customers build, deploy, and run secure, resilient, and cost-effective workloads on AWS. He has a background in analytics consulting and has helped several Fortune 500 companies across industries implement solutions spanning the entire data lifecycle, from data governance / management to advanced analytics using machine learning. Outside of work, he keeps himself busy with all things finance and reading non-fiction.
Sumit Dhuwalia is a Technical Account Manager at AWS focused on helping ISV customers build, deploy, and run secure, resilient, and cost-effective workloads on AWS. He has a background in analytics consulting and has helped several Fortune 500 companies across industries implement solutions spanning the entire data lifecycle, from data governance / management to advanced analytics using machine learning. Outside of work, he keeps himself busy with all things finance and reading non-fiction.
 Ron Cully is a Principal Product Manager at AWS where he has spent over 7 years in identity leading work on AWS IAM Identity Center, and previously on AWS Directory Service. Ron has over 25 years of industry experience in product and program management of networking and directory related products. He is passionate about delivering secure, reliable solutions that help make it easier for customers to have trustworthy experiences while taking advantage of cloud computing.
Ron Cully is a Principal Product Manager at AWS where he has spent over 7 years in identity leading work on AWS IAM Identity Center, and previously on AWS Directory Service. Ron has over 25 years of industry experience in product and program management of networking and directory related products. He is passionate about delivering secure, reliable solutions that help make it easier for customers to have trustworthy experiences while taking advantage of cloud computing.
 Praney Mahajan is a Senior Technical Account Manager at AWS who partners with key enterprise customers as their strategic advisor. He is passionate about bridging technical solutions with business outcomes, with expertise in database, analytics, cost optimization, and operational efficiency to help customers achieve sustainable growth through innovative cloud solutions. He enjoys going on long drives with his family and playing cricket in his free time.
Praney Mahajan is a Senior Technical Account Manager at AWS who partners with key enterprise customers as their strategic advisor. He is passionate about bridging technical solutions with business outcomes, with expertise in database, analytics, cost optimization, and operational efficiency to help customers achieve sustainable growth through innovative cloud solutions. He enjoys going on long drives with his family and playing cricket in his free time.