AWS Developer Tools Blog
Category: Visual Studio
AWS Toolkit for Visual Studio adds support for Arm64 Visual Studio
We are thrilled to announce that the AWS Toolkit for Visual Studio is now generally available on the Arm64 version of Visual Studio (aka “Arm64 Visual Studio”). This release enables a Visual Studio user on a native Windows Arm64 device or on a device emulating Windows Arm64 on a M class Apple device to leverage […]
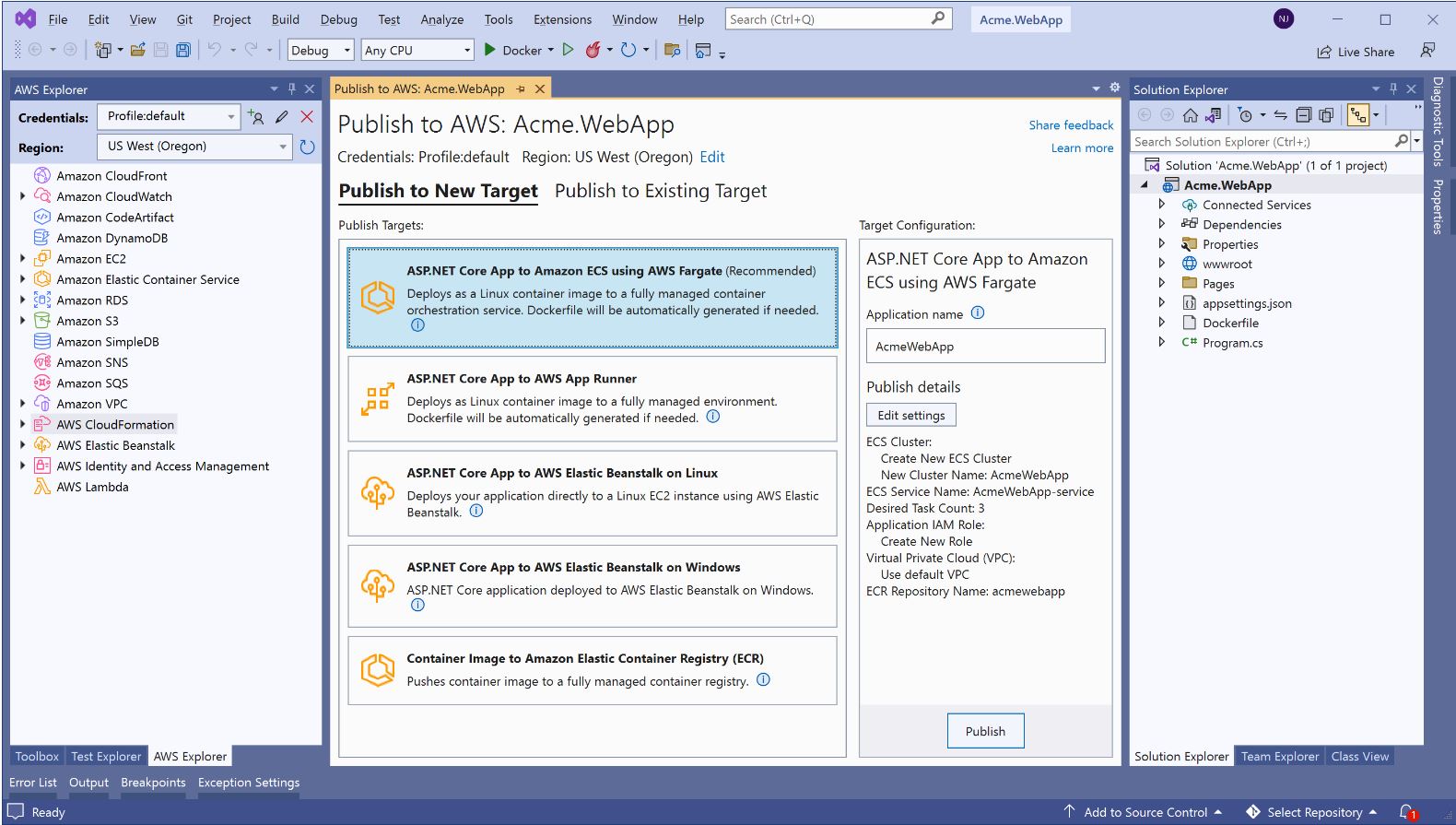
AWS announces a streamlined deployment experience for .NET applications
We are happy to announce the general availability of a new deployment experience in both the Visual Studio and the .NET CLI. This follows the preview announcement from last year. The new deployment experience focuses on the type of application you want to deploy instead of individual AWS services by providing intelligent compute recommendations. You […]
Tips & Tricks: Debugging your C# CDK project in Visual Studio
NOTE: This post assumes the reader has some familiarity with the AWS Cloud Development Kit (CDK). To get started with the AWS CDK, please visit the AWS CDK Developer Guide and follow the AWS CDK for .NET workshop. The AWS CDK is an an open-source Infrastructure-as-Code (IaC) framework that allows developers to model and provision […]
Run Blazor-based .NET Web applications on AWS Serverless
Blazor WebAssembly is a new client-side web development framework that lets developers to use C# to create application front end. Blazor can run client-side C# code directly in the browser, using WebAssembly. Blazor WebAssembly runs on .NET Core and it is an open source and cross-platform web framework for building single-page application using .NET and […]
AWS Toolkit for Visual Studio now supports Visual Studio 2019
A new release of the AWS Toolkit for Visual Studio has been published to Visual Studio marketplace. This new release adds support for Visual Studio 2019. Visual Studio 2019 is currently in preview, however, Microsoft has announced the general availability (GA) release date to be April 2, 2019. The AWS Toolkit for Visual Studio provides […]
General Availability of the AWS Toolkit for Visual Studio 2017
We’re pleased to announce that the AWS Toolkit for Visual Studio is now generally available (GA) for Visual Studio 2017. You can install it from the Visual Studio Gallery. The GA version is 1.12.1.0. Unlike with previous versions of the toolkit, we are using the Visual Studio Gallery to distribute new versions that target Visual Studio […]
Using AWS CodeCommit with Visual Studio Team Explorer
We recently announced support for new features in the AWS Toolkit for Visual Studio that make working with AWS CodeCommit repositories easy and convenient from within Visual Studio Team Explorer. In this post, we take a look at getting started with setting up credentials, and then how to create and clone repositories from within Team […]
Code Analyzers Added to AWS SDK for .NET
One of the most exciting Microsoft Visual Studio 2015 features is the ability to have static analysis run on your code as you write it. This allows you to flag code that is syntactically correct but will cause errors when run. We have added static analyzers to the latest AWS SDK NuGet packages for each […]
AWS Lambda Support in Visual Studio
Today we released version 1.9.0 of the AWS Toolkit for Visual Studio with support for AWS Lambda. AWS Lambda is a new compute service in preview that runs your code in response to events and automatically manages the compute resources for you, making it easy to build applications that respond quickly to new information. Lambda […]
New AWS Elastic Beanstalk Deployment Wizard
Today, we released version 1.8 of the AWS Toolkit for Visual Studio. For this release, we revamped our wizard to deploy your ASP.NET Applications. Our goal was to make deployment easier as well as take advantage of some of the new features AWS Elastic Beanstalk has added. What happened to the AWS CloudFormation deployments? Unlike […]