AWS DevOps & Developer Productivity Blog
Integrating SonarCloud with AWS CodePipeline using AWS CodeBuild
In most development processes, common challenges include the quality of released code and the efficiency of the code review process. There are multiple tools providing insights into code quality which can easily be integrated into the daily routine of the development team. One such tool is SonarCloud, a code analysis as a service provided by SonarQube. This tool provides a defined process to enforce code control on three levels—syntax, code standards, and structure—before the code reaches the testing stage can address these challenges and help the developer release high-quality code every time.
In this blog post, we will demonstrate how SonarCloud can be integrated with AWS CodePipeline using AWS CodeBuild.
AWS CodePipeline is a fully managed continuous delivery service that helps you automate your release pipelines for fast and reliable application and infrastructure updates. CodePipeline automates the build, test, and deploy phases of your release process every time there is a code change, based on the release model you define. This enables you to rapidly and reliably deliver features and updates. You can easily integrate AWS CodePipeline with third-party services such as GitHub or with your own custom plugin.
AWS CodeBuild is a fully managed build service that compiles source code, runs tests, and produces software packages that are ready to deploy.
Prerequisites:
- GitHub account credential to login to SonarCloud. We assume you have fair understanding of SonarCloud.
- AWS Account and console access. We assume you have sample project to integrate either in GitHub or AWS CodeCommit repository.
- For more information on CodeBuild, refer getting started documentation.
High level architecture
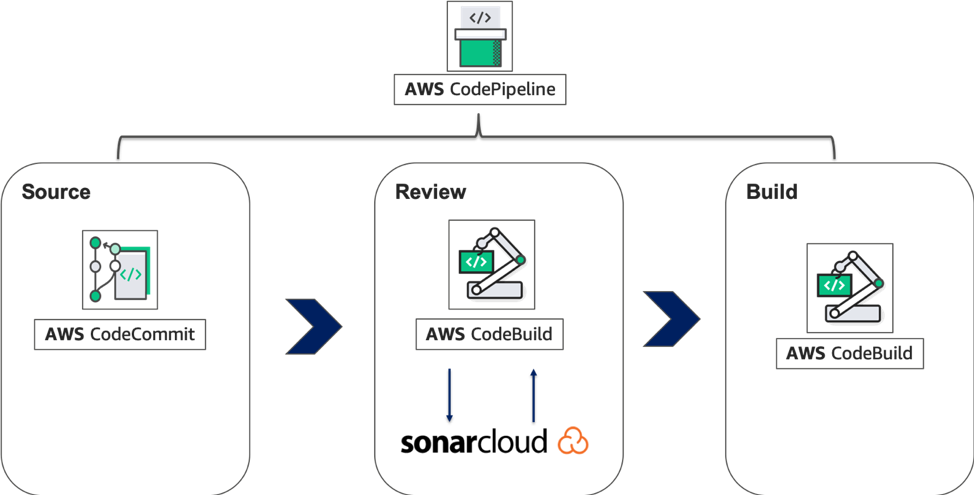
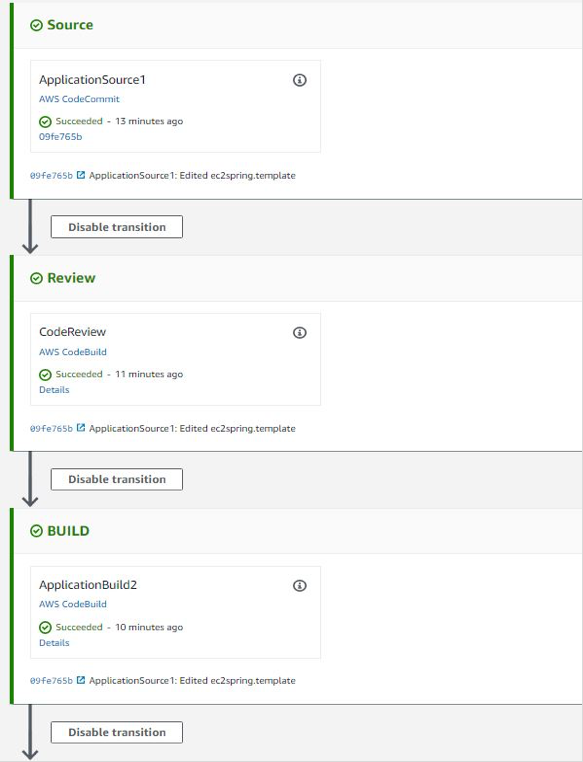
Here, we are going to use a simple three stage CodePipeline setup to demonstrate the integration with Sonarcloud. For source stage, we will use a sample project stored in AWS CodeCommit. For review stage, we will use AWS CodeBuild project to integrate with SonarCloud and perform code quality check. For final build stage, we will use another AWS CodeBuild project and push the built artifact to S3 bucket.
Connect your repository with SonarCloud
First, connect your repository with SonarCloud by following these steps:
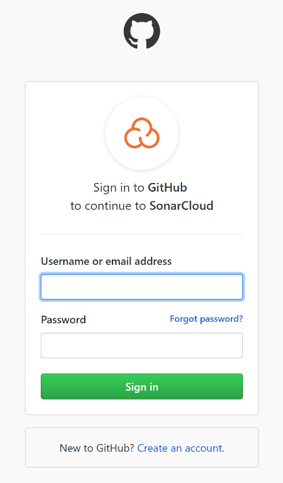
- Sign in to GitHub through the SonarCloud site using your GitHub credentials, as shown in the following screenshot.
 2. Choose Create a new project in the SonarCloud portal, as shown in the following screenshot.
2. Choose Create a new project in the SonarCloud portal, as shown in the following screenshot.

3. Choose Choose an organization in GitHub, as shown in the following screenshot.
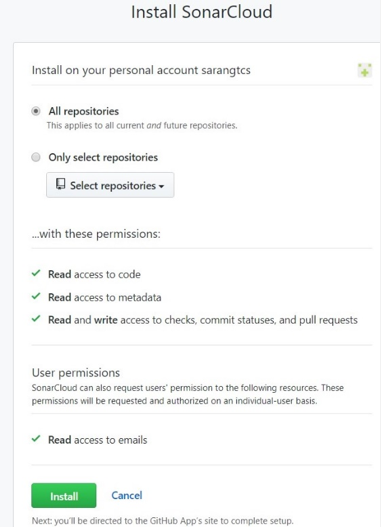
 4. Choose Install after selecting the required repositories, as shown in the following screenshot.
4. Choose Install after selecting the required repositories, as shown in the following screenshot.
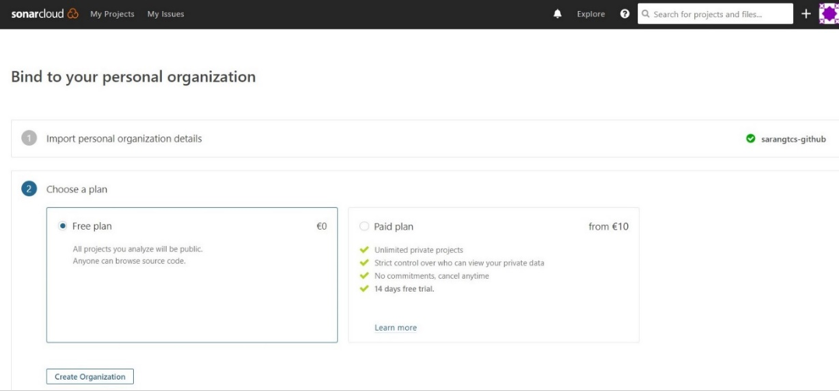
5. Your GitHub repository is now synchronized with SonarCloud. The GitHub repository in this example has a Java project. Bind the GitHub branch and choose Create Organization, as shown in the following screenshot.
6. To generate a token, to go User > My Account > Security. Your existing tokens are listed here, each with a Revoke button. Enter a new Token name and Click Generate. Store it for the succeeding steps.

7. Select Analyze new project.

8. Select Set up manually. Add a new Project key and click Set up.

Note: We will use the Project key, Organization and token in the next step to configure CodeBuild.
Configure SecretManager
We will use AWS Secret Manager to store the sonar login credentials. By using Secrets Manager we can provide controlled access to the credentials from CodeBuild.
1. Visit AWS Secret Manager console to setup the sonar login credentials.
2. Select Store a new secret. And choose Other types of secret
3. Enter secret keys and values as shown below. Enter the values based on your Organization, project and token.
4. Enter the secret name. In this case, we will use “prod/sonar” and save with default settings.

Configuring AWS CodeBuild
A buildspec.yml file is a collection of build commands and related settings in YAML format that CodeBuild uses to run a build. To understand buildspec.yml file specification, refer to the Build Specification Reference for CodeBuild.
Create a CodeBuild Project name, such as CodeReview, for integrating with SonarCloud.
For CodeBuild Environment, use AWS managed image with Ubuntu Operating System and Standard runtime with image “aws/codebuild/standard:3.0”
The buildspec.yml file in CodeBuild is structured as follows:
version: 0.2 env: secrets-manager: LOGIN: prod/sonar:sonartoken HOST: prod/sonar:HOST Organization: prod/sonar:Organization Project: prod/sonar:Project phases: install: runtime-versions: java: openjdk8 pre_build: commands: - apt-get update - apt-get install -y jq - wget http://www-eu.apache.org/dist/maven/maven-3/3.5.4/binaries/apache-maven-3.5.4-bin.tar.gz - tar xzf apache-maven-3.5.4-bin.tar.gz - ln -s apache-maven-3.5.4 maven - wget https://binaries.sonarsource.com/Distribution/sonar-scanner-cli/sonar-scanner-cli-3.3.0.1492-linux.zip - unzip ./sonar-scanner-cli-3.3.0.1492-linux.zip - export PATH=$PATH:/sonar-scanner-3.3.0.1492-linux/bin/ build: commands: - mvn test - mvn sonar:sonar -Dsonar.login=$LOGIN -Dsonar.host.url=$HOST -Dsonar.projectKey=$Project -Dsonar.organization=$Organization - sleep 5 - curl https://sonarcloud.io/api/qualitygates/project_status?projectKey=$Project >result.json - cat result.json - if [ $(jq -r '.projectStatus.status' result.json) = ERROR ] ; then $CODEBUILD_BUILD_SUCCEEDING -eq 0 ;fi
Note: In the pre-build phase, we have downloaded and unzipped the SonarQube Scanner CLI package. The SonarCloud CLI is used to interact with the SonarCloud service. You can also look for the latest SonarCloud CLI release. And in the build phase, we have added a command to execute SonarCloud check and get a response from the project’s quality gate.
2. The Code Review status of the project can be also be verified in the SonarCloud dashboard, as shown in the following screenshot.

Note: Quality Gate is a feature in SonarCloud that can be configured to ensure coding standards are met and regulated across projects. You can set threshold measures on your projects like code coverage, technical debt measure, number of blocker/critical issues, security rating/unit test pass rate, and more. The last step calls the Quality Gate API to check if the code is satisfying all the conditions set in Quality Gate.
Quality Gate can return four possible responses:
- ERROR: The project fails the Quality Gate.
- WARN: The project has some irregularities but is ok to be passed on to production.
- OK: The project successfully passes the Quality Gate.
- None: The Quality Gate is not attached to project.
AWS CodeBuild provides several environment variables that you can use in your build commands. CODEBUILD_BUILD_SUCCEEDING is a variable used to indicate whether the current build is succeeding. Setting the value to 0 indicates the build status as failure and 1 indicates the build as success.
Using the Quality Gate ERROR response, set the CODEBUILD_BUILD_SUCCEEDING variable to failure. Accordingly, the CodeBuild status can be used to provide response for the pipeline to proceed or to stop.
Set up CodePipeline to verify the SonarCloud integration.
Switch to your CodePipeline console to create a pipeline for your repository.
You can integrate SonarCloud in any stage in CodePipeline. In this example, we created a Review stage after the CodePipeline Source stage with CodeBuild used as an action provider, as shown in the following screenshot. Here, we have used a project from our CodeCommit repository to analyze it on SonarCloud. You should be able to link your projects from either GitHub, S3 or CodeCommit as appropriate using CodePipeline.
Clean Up
- Visit CodePipeline console, select the created pipeline. Select the Edit and click Delete.
- Visit CodeBuild console, select the created project. Select the Action and click Delete.
- Visit Secrets Manager console, select the created secret. Select the Action and click Delete.
Conclusion
This blog demonstrated how to integrate SonarCloud with CodePipeline using CodeBuild. With this solution, you can automate static code analysis every time you have a check-in in your source code tool. Hopefully this blog post will help you integrate SonarCloud for better code quality before release. Feel free to leave suggestions or approaches on integration in the comments.
About the Authors

Raji Krishnamoorthy is a AWS Cloud architect working for Tata Consultancy Services.
She carries close to 16 years of experience in Microsoft .Net, SharePoint, AWS and other cloud technologies. Currently, she is leading the Public Cloud Industry Transformation Group with Tata Consultancy Services.

Neelam Jain is a AWS Solution Architect working for Tata Consultancy Services. She has expertise on Java and AWS DevOps technologies. Currently, she is playing the role of a Senior Developer in Public Cloud CoE group with Tata Consultancy Services.