AWS Security Blog
Tag: How-to guides
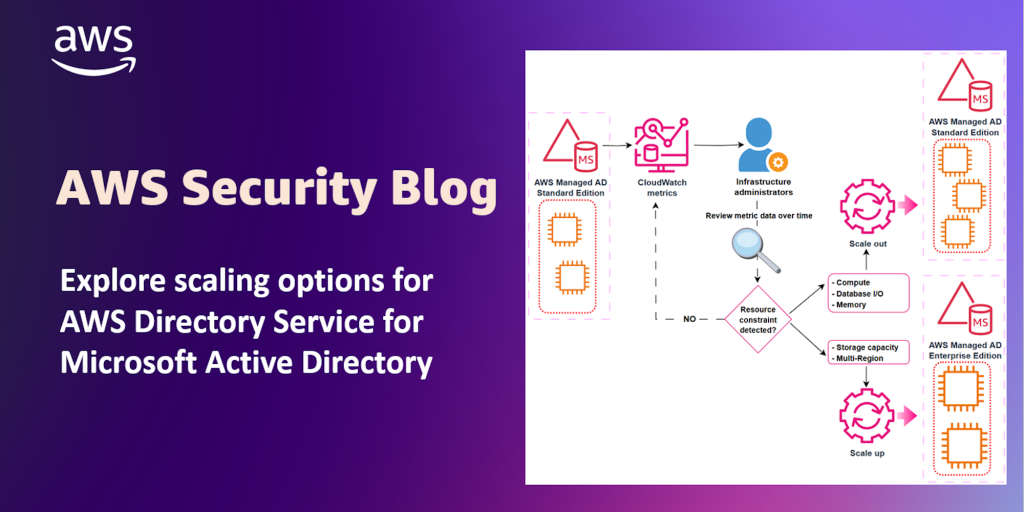
Explore scaling options for AWS Directory Service for Microsoft Active Directory
You can use AWS Directory Service for Microsoft Active Directory as your primary Active Directory Forest for hosting your users’ identities. Your IT teams can continue using existing skills and applications while your organization benefits from the enhanced security, reliability, and scalability of AWS managed services. You can also run AWS Managed Microsoft AD as […]
Writing IAM Policies: Grant Access to User-Specific Folders in an Amazon S3 Bucket
Mar 25, 2024: We have fixed the JSON code examples which caused errors by replacing the curly quotes with straight quotes. November 14, 2023: We’ve updated this post to use IAM Identity Center and follow updated IAM best practices. In this post, we discuss the concept of folders in Amazon Simple Storage Service (Amazon S3) […]
IAM Policies and Bucket Policies and ACLs! Oh, My! (Controlling Access to S3 Resources)
September 11, 2023: This post has been updated. Updated on July 6, 2023: This post has been updated to reflect the current guidance around the usage of S3 ACL and to include S3 Access Points and the Block Public Access for accounts and S3 buckets. Updated on April 27, 2023: Amazon S3 now automatically enables […]
Automate domain join for Amazon EC2 instances from multiple AWS accounts and Regions
As organizations scale up their Amazon Web Services (AWS) presence, they are faced with the challenge of administering user identities and controlling access across multiple accounts and Regions. As this presence grows, managing user access to cloud resources such as Amazon Elastic Compute Cloud (Amazon EC2) becomes increasingly complex. AWS Directory Service for Microsoft Active […]
Securing resource tags used for authorization using a service control policy in AWS Organizations
In this post, I explain how you can use attribute-based access controls (ABAC) in Amazon Web Services (AWS) to help provision simple, maintainable access controls to different projects, teams, and workloads as your organization grows. ABAC gives you access to granular permissions and employee-attribute based authorization. By using ABAC, you need fewer AWS Identity and […]
How to seamlessly domain join Amazon EC2 instances to a single AWS Managed Microsoft AD Directory from multiple accounts and VPCs
You can now share a single AWS Directory Service for Microsoft Active Directory (also known as an AWS Managed Microsoft AD) with multiple AWS accounts within an AWS Region. This capability makes it easier and more cost-effective for you to manage directory-aware workloads from a single directory across accounts and Amazon Virtual Private Clouds (Amazon […]
How to Use Service Control Policies in AWS Organizations
January 20, 2020: Based on customer feedback, we rephrased the fourth goal in the “An example structure with nested OUs and SCPs” section to try to improve clarity. With AWS Organizations, you can centrally manage policies across multiple AWS accounts without having to use custom scripts and manual processes. For example, you can apply service […]
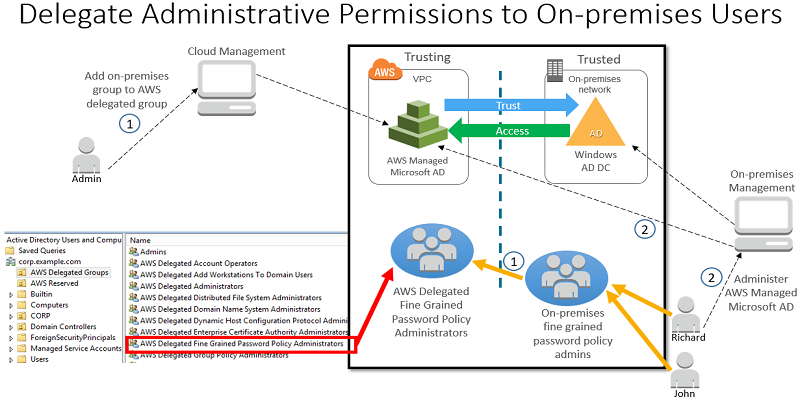
How to Delegate Administration of Your AWS Managed Microsoft AD Directory to Your On-Premises Active Directory Users
You can now enable your on-premises users administer your AWS Directory Service for Microsoft Active Directory, also known as AWS Managed Microsoft AD. Using an Active Directory (AD) trust and the new AWS delegated AD security groups, you can grant administrative permissions to your on-premises users by managing group membership in your on-premises AD directory. […]
Announcing New IAM Policy Simulator
Check out the new IAM policy simulator, a tool that enables you to test the effects of IAM access control policies before committing them into production, making it easier to verify and troubleshoot permissions. Learn more at the AWS Blog. – Kai
Guidelines for When to Use Accounts, Users, and Groups
I often get asked when to use different AWS accounts to enforce separation of duties versus using IAM users and groups within a single account. While the complete answer depends on what AWS services you use, the general guidelines in this post will point you in the right direction. As context for the guidelines, consider […]