AWS Security Blog
Category: Technical How-to
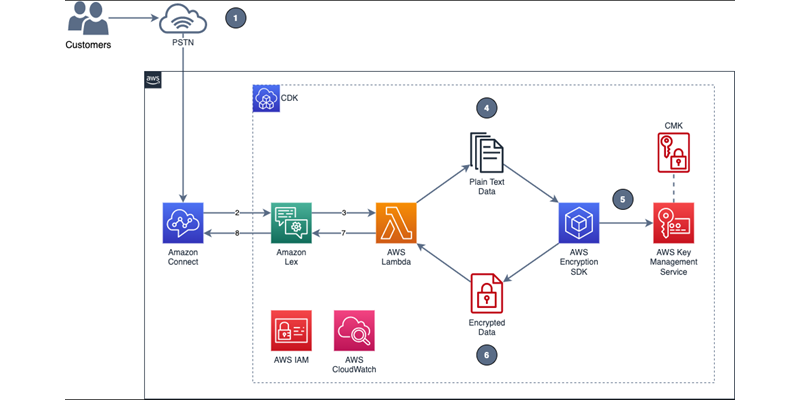
How to encrypt sensitive caller voice input in Amazon Lex
In the telecommunications industry, sensitive authentication and user data are typically received through mobile voice and keypads, and companies are responsible for protecting the data obtained through these channels. The increasing use of voice-driven interactive voice response (IVR) has resulted in a need to provide solutions that can protect user data that is gathered from […]
How to revoke federated users’ active AWS sessions
February 6, 2023: Updates added to explain an additional detail regarding the sourceIdentity field. In addition to using the sourceIdentity field to reference the user through various roles they have assumed, you may also construct your IAM trust policies to enforce acceptable sourceIdentity values or ensure any value for sourceIdentity is set. When you use […]
How to query and visualize Macie sensitive data discovery results with Athena and QuickSight
February 21, 2023: We’ve updated the CREATE TABLE DDL to add the new originType field introduced as part of the Automated Sensitive Data Discovery feature of Macie. Amazon Macie is a fully managed data security service that uses machine learning and pattern matching to help you discover and protect sensitive data in Amazon Simple Storage Service (Amazon S3). With […]
Prepare for consolidated controls view and consolidated control findings in AWS Security Hub
March 29, 2023: The post had been updated to notify customers that the Automated Security Response on AWS v2.0.0 now supports consolidated control findings. Currently, AWS Security Hub identifies controls and generates control findings in the context of security standards. Security Hub is aiming to release two new features in the first quarter of 2023 […]
How to use Amazon Verified Permissions for authorization
Applications with multiple users and shared data require permissions management. The permissions describe what each user of an application is permitted to do. Permissions are defined as allow or deny decisions for resources in the application. To manage permissions, developers often combine attribute-based access control (ABAC) and role-based access control (RBAC) models with custom code […]
How to secure your SaaS tenant data in DynamoDB with ABAC and client-side encryption
If you’re a SaaS vendor, you may need to store and process personal and sensitive data for large numbers of customers across different geographies. When processing sensitive data at scale, you have an increased responsibility to secure this data end-to-end. Client-side encryption of data, such as your customers’ contact information, provides an additional mechanism that […]
How to investigate and take action on security issues in Amazon EKS clusters with Amazon Detective – Part 2
March 15, 2023: We’ve updated this post to incorporate a section to investigate VPC flow logs. In part 1 of this of this two-part series, How to detect security issues in Amazon EKS cluster using Amazon GuardDuty, we walked through a real-world observed security issue in an Amazon Elastic Kubernetes Service (Amazon EKS) cluster and […]
How to use Amazon Macie to preview sensitive data in S3 buckets
February 13, 2024: We’ve updated this post to show you how to configure Macie to assume an IAM role when you configure Macie to preview sensitive data in findings. Security teams use Amazon Macie to discover and protect sensitive data, such as names, payment card data, and AWS credentials, in Amazon Simple Storage Service (Amazon […]
Use Amazon Macie for automatic, continual, and cost-effective discovery of sensitive data in S3
Customers have an increasing need to collect, store, and process data within their AWS environments for application modernization, reporting, and predictive analytics. AWS Well-Architected security pillar, general data privacy and compliance regulations require that you appropriately identify and secure sensitive information. Knowing where your data is allows you to implement the appropriate security controls which […]
Get the best out of Amazon Verified Permissions by using fine-grained authorization methods
With the release of Amazon Verified Permissions, developers of custom applications can implement access control logic based on caller and resource information; group membership, hierarchy, and relationship; and session context, such as device posture, location, time, or method of authentication. With Amazon Verified Permissions, you can focus on building simple authorization policies and your applications—instead […]